

25,000+ students realised their study abroad dream with us. Take the first step today
Here’s your new year gift, one app for all your, study abroad needs, start your journey, track your progress, grow with the community and so much more.

Verification Code
An OTP has been sent to your registered mobile no. Please verify

Thanks for your comment !
Our team will review it before it's shown to our readers.

- Computer Science /
600+ Seminar Topics for CSE
- Updated on
- Nov 16, 2022

One of the most popular types of engineering , Computer Science Engineering (CSE) imparts extensive knowledge related to computing programs and hardware frameworks. Apart from equipping you with the fundamental principles of computer programming and networking through the diverse Computer Science Engineering syllabus , universities across the world also conduct seminars to familiarise you with the latest technological happenings. So, here is a blog that lists down some of the most important Seminar Topics for CSE!
This Blog Includes:
600+ popular seminar topics for cse 2023, mobile computing and its applications , rover mission using java technology, pill camera in medicine , postulates of human-computer interface, software testing, it in space, interconnection of computer networks, random number generators, hamming cut matching algorithm, cryptocurrency, smart textiles, voice morphing, wireless usb, zigbee technology, fog computing, crypto watermarking, ip address spoofing, list of seminar topics for computer science, technical seminar topics for cse with abstract, top universities for cse.
Popular Seminar Topics for CSE 2023 are listed below:
1. Screenless Display 2. Li-Fi Technology 3. Microprocessor and Microcontrollers 4. Silverlight 5. Green Computing 6. MANET 7. Facility Layout Design through Genetic Algorithm 8. Tamper Resistance 9. iSCSI 10. Wireless Networked Digital Devices 11. 3G-vs-WiFi Interferometric Modulator (IMOD) 12. Free Space Laser Communications 13. Virtual Instrumentation 14. Direct Memory Access 15. Smart Note Taker 16. Computational Intelligence in Wireless Sensor Networks 17. Fog Computing 18. Python Libraries for Data Science
19. Software Reuse 20. Google Project Loon 21. Object-Oriented Programming using Python/ Java/ C++ 22. Dynamic Synchronous Transfer Mode 23. Cellular Neural Network 24. Li-Fi and MiFi 25. Jini Technology 26. Quantum Information Technology 27. GSM 28. Delay Tolerant Networking 29. Brain Chips 30. Graphics Processing Unit (GPU) 31. Predictive Analysis 32. Cisco IOS Firewall 33. EyePhone 34. Keil C 35. Industrial Applications through Neural Networks 36. Helium Drives 37. Millipede 38. Holographic Memory 39. Autonomic Computing 40. Google Glass 41. Domain Name System(DSN) 42. VESIT Library – Android Application 43. Blockchain Technology 44. Dynamic Memory Allocation 45. TCP/ IP 46. Internet of Things 47. Internet Telephony Policy in India 48. Smart Cards 49. Night Vision Technology 50. Voice Portals 51. Smart Dust 52. DOS Attack 53. Futex 54. Pervasive Computing 55. Speed protocol processors 56. iTwin 57. Clockless Chip 58. Rain Technology Architecture 59. Code Division Duplexing 60. Biometrics in SECURE e-transaction 61. Network Topology 62. Augmented Reality vs Virtual Reality 63. DNA-Based Computing 64. Bio-metrics 65. Transactional Memory 66. Number Portability 67. VoiceXML 68. Prescription Eyeglasses 69. Lamp Technology
70. Eye Gaze Communication System 71. MRAMs and SMRs 72. Cyberbullying Detection 73. Facebook timeline 74. IDMA 75. Virtual LAN Technology 76. Global Wireless E-Voting 77. Smart Fabrics 78. Voice Morphing 79. Data Security in Local Network 80. Big Data Technology 81. Probability Statistics and Numerical Techniques 82. RAID 83. Ambiophonics 84. Digital Video Editing 85. Synchronous Optical Networking 86. Layer 3 Switching 87. InfiniBand 88. Steganography 89. Packet Sniffers 90. Cryptography Technology 91. System Software 92. Humanoid Robot 93. X-Vision 94. Firewalls 95. Introduction to the Internet Protocols 96. Bio-inspired Networking 97. BEOWULF Cluster 98. XML Encryption 99. Security Features of ATM 100. Design And Analysis Of Algorithms 101. OpenRAN 102. Advanced Driver Assistance System (ADAS) 103. Digital Scent Technology 104. Iris Scanning 105. Symbian Mobile Operating System 106. Motes 107. Google Chrome Laptop or Chrome Book 108. Mind-Reading Computer 109. Distributed Interactive Virtual Environment 110. Trustworthy Computing 111. Teleportation 112. Finger Reader 113. Linux Kernel 2.6 114. MemTable 115. Voice Browser 116. Alternative Models Of Computation 117. Diamond chip 118. Photonics Communications 119. System in Package 120. Neural Interfacing 121. Multiple Access Control Protocol 122. Synthetic Aperture Radar System 123. WhatsApp 124. 5g Wireless System 125. Touch screen 126. Wireless Fidelity 127. Wireless Video Service in CDMA Systems 128. 10 Gigabit Ethernet 129. Java Database Connectivity 130. Artificial Intelligence 131. Computer Intelligence Application 132. Airborne Internet
133. Fast Convergence Algorithms for Active Noise Controlling Vehicles 134. Survivable Networks Systems 135. Capacitive And Resistive Touch Systems 136. Electronic Payment Systems 137. Ipv6 – The Next Generation Protocol 138. Zigbee Technology 139. InfiniBand 140. Finger Vein Recognition 141. Integrated Voice and Data 142. Chameleon Chip 143. Spam Assassin 144. FireWire 145. Free Space Optics 146. Chatbot for Business Organization 147. Haptic Technology 148. DNS Tunneling 149. Example-Based Machine Translation 150. Holographic Versatile Disc 151. Brain Fingerprinting 152. Finger Sleeve 153. Computer Forensics 154. Wireless Application Protocol 155. Free-space optical 156. Digital Cinema 157. Hurd 158. Eye Movement-Based Human-Computer Interaction Techniques 159. Optical Packet Switching Network 160. Neural Networks And Their Applications 161. Palladium 162. Intel Centrino Mobile Technology 163. High-Performance DSP Architectures 164. Next-Generation Secure Computing Base 165. MiniDisc system 166. Multiprotocol Label Switching 167. Opera (web browser) 168. 3D Optical Storage 169. Touchless Touchscreen 170. SPCS 171. Cooperative Linux 172. Real-Time Application Interface 173. Driving Optical Network Evolution 174. Tempest and Echelon 175. Mobile Virtual Reality Service 176. Teradata 177. Word Sense Disambiguation 178. Yii Framework 179. Microsoft HoloLens 180. Project Oxygen 181. Voice Over Internet Protocol 182. Wibree 183. Handheld Computers 184. Sniffer for detecting lost mobile 185. Fiber Channel 186. Digital Audio Broadcasting 187. Mobile Phone Cloning 188. Near Field Communication NFC 189. IP Telephony 190. Transient Stability Assessment using Neural Networks 191. corDECT Wireless in Local Loop System 192. Gaming Consoles 193. Broad Band Over Power Line
194. Wine 195. Wardriving 196. Smart Skin for Machine Handling 197. XBOX 360 System 198. Unicode And Multilingual Computing 199. Aeronautical Communication 200. D-Blast 201. Swarm intelligence & Traffic Safety 202. 3D Human Sensing 203. Wireless Sensor Networks 204. Breaking the Memory Wall in MonetDB 205. Access gateways 206. Optical Networking and Dense Wavelength Division Multiplexing 207. Hyper-Threading technology 208. Intelligent RAM 209. Goal-line technology 210. Zigbee 211. Smart Textiles 212. Nanorobotics 213. Strata flash Memory 214. Digital Preservation 215. DNA Storage 216. Network Attached Storage 217. Dynamic Cache Management Technique 218. Enhancing LAN Using Cryptography and Other Modules 219. Conditional Access System 220. Reconfigurable computing 221. Thermography 222. Nano Cars Into The Robotics 223. Project Loon 224. DNA chips 225. Operating Systems with Asynchronous Chips 226. Prototype System Design for Telemedicine 227. Virtual Smart Phone 228. 3G vs WiFi 229. Sandbox (computer security) 230. Face Recognition Technology 231. Biometrics Based Authentication 232. Optical Computer 233. M-Commerce 234. Wireless Internet 235. E-Paper Technology 236. Web Scraping 237. Bluetooth-Based Smart Sensor Networks 238. Smart Dustbins for Smart Cities 239. Satellite Radio 240. Modular Computing 241. 3d Optical Data Storage 242. Robotic Surgery 243. Digital Jewelry 244. Home Networking 245. Flexpad 246. Web Clustering Engines 247. Public Key Infrastructure 248. Inverse Multiplexing 249. Wireless USB 250. Fiber-Distributed Data Interface 251. Elastic Quotas 252. Bionic Eye 253. Zenoss Core 254. Quadrics Interconnection Network 255. Unified Modeling Language (UML) 256. Compute Unified Device Architecture CUDA 257. Quantum Cryptography 258. Local Multipoint Distribution Service
259. Hi-Fi 260. HVAC 261. Mobile OS (operating systems) 262. Image Processing 263. Rover Technology 264. Cyborgs 265. Dashboard 266. High-Performance Computing with Accelerators 267. Anonymous Communication 268. Crusoe Processor 269. Seam Carving for Media Retargeting 270. Fluorescent Multi-layer Disc 271. Cloud Storage 272. Holograph Technology 273. TCPA / Palladium 274. Optical Burst Switching 275. Ubiquitous Networking 276. NFC and Future 277. Database Management Systems 278. Intel Core I7 Processor 279. Modems and ISDN 280. Optical Fibre Cable 281. Soft Computing 282. 64-Bit Computing 283. CloudDrops 284. Electronic paper 285. Spawning Networks 286. Money Pad, The Future Wallet 287. HALO 288. Gesture Recognition Technology 289. Ultra Mobile Broadband(UMB) 290. Computer System Architecture 291. PoCoMo 292. Compositional Adaptation 293. Computer Viruses 294. Location Independent Naming 295. Earth Simulator 296. Sky X Technology 297. 3D Internet 298. Param 10000 299. Nvidia Tegra 250 Developer Kit Hardware 300. Clayodor 301. Optical Mouse 302. Tripwire 303. Telepresence 304. Genetic Programming 305. Cyberterrorism 306. Asynchronous Chips 307. The Tiger SHARC processor 308. EyeRing 309. SATRACK 310. Daknet 311. Development of the Intenet 312. Utility Fog 313. Smart Voting System Support by using Face Recognition 314. Google App Engine 315. Terrestrial Trunked Radio 316. Parasitic Computing 317. Ethical Hacking
318. HPJava 319. Crypto Watermarking 320. Exterminator 321. Ovonic Unified Memory 322. Intelligent Software Agents 323. Swarm Intelligence 324. Quantum Computers 325. Generic Access Network 326. Cable Modems 327. IDC 328. Java Ring 329. DOS Attacks 330. Phishing 331. QoS in Cellular Networks Based on MPT 332. VoCable 333. The Callpaper Concept 334. Combating Link Spam 335. Tele-immersion 336. Intelligent Speed Adaptation 337. Compact peripheral component interconnect 338. Mobile Number Portability 339. 3D Television 340. Multi-Touch Interaction 341. Apple Talk 342. Secure ATM by Image Processing 343. Computerized Paper Evaluation using Neural Network 344. IMAX 345. Bluetooth Broadcasting 346. Biometrics and Fingerprint Payment Technology 347. SPECT 348. Gi-Fi 349. Real-Time Systems with Linux/RTAI 350. Multiple Domain Orientation 351. Invisible Eye 352. Virtual Retinal Display 353. 3D-Doctor 354. MobileNets 355. Bio-Molecular Computing 356. Semantic Digital Library 357. Cloud Computing 358. Semantic Web 359. Ribonucleic Acid (RNA) 360. Smart Pixel Arrays 361. Optical Satellite Communication 362. Surface Computer 363. Pill Camera 364. Self-Managing Computing 365. Light Tree 366. Phase Change Memory – PCM 367. Worldwide Interoperability for Microwave Access 368. Motion Capture 369. Planar Separators 370. CORBA Technology 371. Generic Framing Procedure
372. E Ball PC Technology 373. Bluetooth V2.1 374. Stereoscopic Imaging 375. Artificial Neural Network (ANN) 376. Big Data 377. Theory of Computation 378. CORBA 379. Ultra-Wideband 380. Speed Detection of moving vehicles with the help of speed cameras 381. zForce Touch Screen 382. iCloud 383. Sense-Response Applications 384. BitTorrent 385. Sensors on 3D Digitization 386. 4G Broadband 387. Serverless Computing 388. Parallel Computing In India 389. Rapid Prototyping 390. Compiler Design 391. Secure Shell 392. LED printer 393. Storage Area Networks 394. Aspect-oriented programming (AOP) 395. Dual Core Processor 396. LTE: Long-Term Evolution 397. Mobile IP 398. CGI Programming 399. Computer Memory Contingent on the Protein Bacterio-rhodopsin 400. Visible light communication 401. 5 Pen PC Technology 402. GSM Security And Encryption 403. Smart Mirror 404. PHANToM 405. High Altitude Aeronautical Platforms 406. Virtual Keyboard 407. Hadoop 408. Laser Communications 409. Middleware 410. Blue Gene 411. 4D Visualization 412. Facebook Thrift 413. Scrum Methodology 414. Green Cloud Computing 415. Blade Servers 416. Self Organizing Maps 417. Digital Rights Management 418. Google’s Bigtable 419. Hyper Transport Technology 420. Child Safety Wearable Device 421. Extended Mark-Up Language 422. Mobile Jammer 423. Design and Analysis of Algorithms 424. 3D password 425. Data Mining 426. Surround Systems 427. Blockchain Security 428. CyberSecurity 429. Blue Brain 430. Computer Graphics 431. HTAM 432. Graphic processing Unit 433. Human Posture Recognition System 434. Mind Reading System
435. Image Processing & Compression 436. Intrution Detection System 437. Migration From GSM Network To GPRS 438. Skinput Technology 439. Smart Quill 440. MPEG-7 441. xMax Technology 442. Bitcoin 443. Blue Tooth 444. Snapdragon Processors 445. Turbo Codes 446. Magnetic Random Access Memory 447. Sixth Sense Technology 448. Timing Attacks on Implementations 449. Performance Testing 450. Graph Separators 451. Finger Tracking In Real Time Human Computer Interaction 452. MPEG-4 Facial Animation 453. EDGE 454. Dynamic Virtual Private Network 455. Wearable Bio-Sensors 456. 4G Wireless System 457. Longhorn 458. Wireless LAN Security 459. Microsoft Palladium 460. A Plan For No Spam 461. RPR 462. Biometric Voting System 463. Unlicensed Mobile Access 464. Google File System 465. Pivot Vector Space Approach in Audio-Video Mixing 466. iPAD 467. Crusoe 468. Sensitive Skin 469. Storage Area Network 470. Orthogonal Frequency Division Multiplexing 471. Blue Eyes 472. E-Cash Payment System 473. Shingled Magnetic Recording 474. Google Chrome OS 475. Future of IoT 476. Intel MMX Technology 477. DRM Software Radio 478. Itanium Processor 479. Digital Subscriber Line 480. Symbian OS 481. Browser Security 482. Wolfram Alpha 483. Raspberry Pi 484. Neural Networks 485. Socket Programming 486. JOOMLA and CMS 487. Linux Virtual Server 488. Structured Cabling 489. Wine 490. Bluejacking 491. Strata flash Memory 492. Wi-Vi 493. CAPTCHA 494. Software Enginaugmeering 495. Data Structures 496. Mobile Ad-Hoc Networks Extensions to Zone Routing Protocol 497. BlackBerry Technology
498. Mobile TV 499. LWIP 500. Wearable Computers 501. Optical Free Space Communication 502. Software-Defined Radio 503. Resilient Packet Ring Technology 504. Computer Networks 505. Tracking and Positioning of Mobiles in Telecommunication 506. Plan 9 Operating System 507. Smart Memories 508. Real-Time Obstacle Avoidance 509. PON Topologies 510. Graphical Password Authentication 511. Smart Card ID 512. The Deep Web 513. Parallel Computing 514. Magnetoresistive Random Access Memory 515. Radio Frequency Light Sources 516. Refactoring 517. Confidential Data Storage and Deletion 518. Java Servlets 519. Privacy-Preserving Data Publishing 520. 3D Searching 521. Case-Based Reasoning System 522. Small Computer System Interface 523. IP Spoofing 524. Synchronous Optical Networking (SONET) 525. Multicast 526. GSM Based Vehicle Theft Control System 527. Measuring Universal Intelligence 528. Space Mouse 529. Rain Technology 530. AJAX 531. Cryptocurrency 532. Quantum Computing 533. Fibre optic 534. Extreme Programming (XP) 535. Cluster Computing 536. Location Dependent Query Processing 537. Femtocell 538. Computational Visual Attention Systems 539. Distributed Computing 540. Blu Ray Disc 541. Zettabyte FileSystem 542. Internet Protocol Television 543. Advanced Database System 544. Internet Access via Cable TV Network 545. Text Mining 546. Tsunami Warning System 547. WiGig – Wireless Gigabit 548. Slammer Worm 549. NRAM 550. Integer Fast Fourier Transform 551. Multiparty Nonrepudiation 552. Importance of real-time transport Protocol in VOIP 553. AC Performance Of Nanoelectronics 554. Wireless Body Area Network 555. Optical Switching 556. Web 2.0 557. NVIDIA Tesla Personal Supercomputer 558. Child Tracking System 559. Short Message Service (SMS) 560. Brain-Computer Interface 561. Smart Glasses 562. Infinite Dimensional Vector Space
563. Wisenet 564. Blue Gene Technology 565. Holographic Data Storage 566. One Touch Multi-banking Transaction ATM System 567. SyncML 568. Ethernet Passive Optical Network 569. Light emitting polymers 570. IMode 571. Tool Command Language 572. Virtual Private Network 573. Dynamic TCP Connection Elapsing 574. Buffer overflow attack: A potential problem and its Implications 575. RESTful Web Services 576. Windows DNA 577. Object Oriented Concepts 578. Focused Web Crawling for E-Learning Content 579. Gigabit Ethernet 580. Radio Network Controller 581. Implementation Of Zoom FFT 582. IDS 583. Virtual Campus 584. Instant Messaging 585. Speech Application Language Tags 586. On-line Analytical Processing (OLAP) 587. Haptics 588. NGSCB 589. Place Reminder 590. Deep Learning 591. Palm Vein Technology 592. Mobile WiMax 593. Bacterio-Rhodopsin Memory 594. iSphere 595. Laptop Computer 596. Y2K38 597. Adding Intelligence to the Internet 598. Hadoop Architecture 599. Multiterabit Networks 600. Discrete Mathematical Structures 601. Human-Computer Interface 602. Self Defending Networks 603. Generic Visual Perception Processor GVPP 604. Apache Cassandra 605. DVD Technology 606. GPS 607. Voice Quality 608. Freenet 609. Amorphous Computing and Swarm Intelligence 610. Third Generation 611. Smart card 612. Brain Gate 613. Optical packet switch architectures 614. Intrusion Tolerance 615. Pixie Dust 616. MPEG Video Compression 617. SAM 618. 3D Glasses 619. Digital Electronics 620. Mesh Radio 621. Hybridoma Technology 622. Cellular Communications 623. CorDECT 624. Fog Screen 625. Development of 5G Technology 626. VHDL 627. Fast And Secure Protocol
628. TeleKinect 629. Parallel Virtual Machine 630. Ambient Intelligence 631. iDEN 632. X- Internet 633. RD RAM 634. FRAM 635. Digital Light Processing 636. Green Cloud 637. Biological Computers 638. E-Ball Technology
Latest Seminar Topics for CSE 2023
Now that you are aware of some of the latest seminar topics for CSE, let us take a glance at some of the topics that will help you in preparing your presentation and simultaneously give you a brief overview of the reading material and key points to include!
Mobile Computing is a software technology that transfers media through wireless device data, voice, and video without having any fixed connection. The key elements that are involved in this process are mobile software, mobile hardware, and mobile chips.
Java technology today is good for general-purpose computing and GUIs. This technology enables the rovers to manoeuvre on the moon or outer space as per the commands given at the space stations. It is equipped with control systems working through diverse software programs.
With the technological advancements in the field of Medical Science, this has become one of the most popular seminar topics for CSE. It is an instrument with a tiny camera that resembles a vitamin pill and is used primarily throughout the endoscopy process. This capsule shape camera captures pictures of the digestive system and sends them to the recorder.
Human-Computer Interface is a manual intercommunication performed in designing, executing, and assessing processes of a computer system. This kind of technology is generally practised in all types of disciples where a computer installation is involved. The most well-known platform to perform this process is the Association for Computer Machinery (ACM).
Another addition to the list of seminar topics for CSE is Software Testing. It is a prominent technology employed for checking the quality and performance of a software application. The main purpose of this process is to check whether the developed application satisfies the testing parameters of the software. Also, it finds out the negative issues to secure the application becomes defect-free.
Information Technology is used for a wide range of applications in the field of Space Science and Technology. Extending from exploratory fly-bys to rocket launches, the prospects are immense and due to this, it is often included in the list of seminar topics for CSE.
A network or a group of computers helps in the transfer of information packets among network computers and their clients. This is transmitted from any source node to the target destination node.
With its applications spanning across areas like cryptography and security, Random Number Generators form an essential part of the seminar topics for CSE. Computers generate the numbers either through hardware-based analysis [termed as RNG] or do so by assessing external data like mouse clicking.
Hamming Cut Matching Algorithm is a set of programs that are meant to execute the functions of a firmware component and its associated algorithm. It reduces the comparison time for matching the iris code with a database so that we can apply iris verification in case of massive databases like the voting system.
Cryptocurrency is a digital currency secured by cryptography making it almost impossible to counterfeit. It is electronic money which hides the identification of the users.
Smart Textiles are fabrics that can sense and react to environmental stimuli, which may be mechanical, thermal, chemical, biological, and magnetic amongst others. They also automatically track the training progress and monitor the physical state.
Voice Morphing is the technique to alter one’s voice characteristics to another person’s. Voice Morphing Technology helps to transform or change the tone, and pitch or add distortions to the user’s voice.
It is a high-bandwidth wireless USB that connects peripherals like printers, sound cards, and video monitors.
Zigbee is a wireless technology that works on low-power wireless IoT networks and also is affordable. It can have a battery life of several years.
Fog Computing is a process by which multiple devices are allowed to communicate with each other using local networks. It improves efficiency, tightens security and reduces the data used while cloud processing and storage.
Crypto Watermarking is done to protect the content shared from plagiarizing and to authenticate the ownership and source of origin of the content. This also reduces the chances of tampering with data.
IP Address Spoofing is the process of creating Internet Protocol packets with a false source IP address, to trick other networks by entering as a legitimate entity.
Here is the list List of the seminar topics for computer science:
Here are some of the Technical Seminar Topics for CSE with Abstracts:
Be it Harvard University , Caltech , or MIT , Computer Science Engineering courses form part of the offerings of many world-renowned universities. Some of them have been given a rundown below:
The latest topics are considered to be the best ones for a seminar. Some of them are enlisted below: – 4G Wireless Systems – Global Positioning System – Brain-Computer Interface – Laser Satellite Strikers – Face Recognization Technology – Uses of Data – Multimedia Conferencing
Here is a list of the latest seminar topics that are important for seminars: – Laser Telemetric System – Chassis Frame – Ambient Backscatter – Network Security And Cryptography – Pulse Detonation Engine – Buck-Boost Converter – Solar Collector – 3D Television
Computer Science is a field that enables candidates to know about a range of topics such as Algorithms, Computational Complexity, Programming Language Design, Data Structures, Parallel and Distributed Computing, Programming Methodology, Information Retrieval, Computer Networks, Cyber Security and many more.
Given below are some topics for Computer Science that can help you out: – JAVA Programming – C++ Programming – Artificial Intelligence – Machine Learning – Web Scraping – Web Development – Edge Computing – Health Technology
Hence, there are scores of Seminar Topics for CSE that you can learn more about. Planning to pursue a master’s in Computer Science from a university abroad? Not sure how to proceed with it? Then reach out to our experts at Leverage Edu who will not only help you to find your dream university, and provide assistance in completing the formalities of the application but will also help you write an impressive SOP!
Team Leverage Edu
Leave a Reply Cancel reply
Save my name, email, and website in this browser for the next time I comment.
Contact no. *

Leaving already?
8 Universities with higher ROI than IITs and IIMs
Grab this one-time opportunity to download this ebook
Connect With Us
25,000+ students realised their study abroad dream with us. take the first step today..

Resend OTP in

Need help with?
Study abroad.
UK, Canada, US & More
IELTS, GRE, GMAT & More
Scholarship, Loans & Forex
Country Preference
New Zealand
Which English test are you planning to take?
Which academic test are you planning to take.
Not Sure yet
When are you planning to take the exam?
Already booked my exam slot
Within 2 Months
Want to learn about the test
Which Degree do you wish to pursue?
When do you want to start studying abroad.
September 2024
January 2025
What is your budget to study abroad?
How would you describe this article ?
Please rate this article
We would like to hear more.
- Interview Questions
- Group Discussion
- Electronics and Communication
- Electrical and Electronics
- Electronics and Instrumentation
- Computer Science
- Mechanical Engineering
- Civil Engineering
150+ Best Technical seminar topics for cse| Seminar topics for computer science
- Computer Science , Seminar Topics
If you’re looking for ideas for technical seminar topics for cse, you will find this article very useful as here you will find few potential options to consider.The field of computer science is always evolving, and keeping up with the latest advancements can be a challenge. Attending a technical seminar is a great way to stay up-to-date on the latest trends and technologies. Here are some great seminar topics for computer science students:
Table of Contents
Computer science seminar topics
Green computing.
Green computing is the practice of using computing resources in a way that is environmentally sustainable. This includes reducing the energy consumption of computers and other devices, as well as recycling or disposing of them properly. It also involves using green technologies, such as solar power, to power computing devices. Green computing is becoming increasingly important as the world becomes more reliant on technology. With the right practices in place, businesses and individuals can help to reduce their carbon footprint and make a positive impact on the environment.
A mobile ad hoc network (MANET) is a type of wireless network that does not rely on fixed infrastructure. MANETs are often used in situations where it is not possible or practical to deploy a traditional wired or wireless network. For example, MANETs can be used to provide connectivity in disaster areas or other remote locations. Technical seminar topics for cse students interested in MANETs may include topics such as routing protocols, security challenges, and energy-efficiency.
Wireless Networked Digital Devices
Wireless networking is one of the most popular topics in the field of computer science and engineering. In this seminar, you can explore the basics of wireless networking, including the different types of wireless networks and the devices that are used to connect to them. You can also discuss some of the challenges that wireless networks face, such as interference and security.
3G-vs-WiFi Interferometric Modulator (IMOD)
A 3G-vs-WiFi Interferometric Modulator (IMOD) is a device that can be used to modulate the interference between two wireless signals. It is a type of radio frequency (RF) interference Canceller. The IMOD can be used to improve the performance of wireless devices by reducing the amount of interference between the two signals.
Silverlight
Silverlight is a powerful development platform for creating engaging, interactive user experiences for web, desktop, and mobile applications. Silverlight is a cross-platform, cross-browser, and cross-device plugin for delivering the next generation of .NET based media experiences and rich interactive applications (RIAs) for the Web.
Free Space Laser Communications
Laser communications offer a number of advantages over traditional radio frequency (RF) communications, including higher bandwidth, increased security, and the ability to transmit data over longer distances. However, laser communications systems are also more expensive and require a clear line of sight between the transmitter and receiver.
In this seminar, you can discuss the basics of laser communications and explore some of the challenges associated with implementing these systems. You can also discuss some of the potential applications for free space laser communications, including high-speed data links and long-range communications.
Screenless Display
A screenless display is a display device that does not use a traditional video screen. Instead, images are projected directly onto the viewer’s retina, using a technology called retinal projection. This type of display has a number of advantages over traditional screens, including a higher resolution, a wider field of view, and a more immersive experience. Screenless displays are still in the early stages of development, but they have the potential to revolutionize the way we interact with computers and other digital devices.
Li-Fi Technology
Li-Fi is a new technology that uses light to transmit data. It is similar to Wi-Fi, but instead of using radio waves, it uses visible light. Li-Fi is much faster than Wi-Fi, and it is also more secure because it is less susceptible to interference. In addition, Li-Fi is more energy-efficient than Wi-Fi, making it a more sustainable option.
Smart Note Taker
The Smart Note Taker is a device that allows you to take notes and store them electronically. This can be extremely helpful for students who want to be able to take notes and have them stored in one place. The Smart Note Taker can also be used for business meetings or other events where taking notes is important. There are a variety of different models of the Smart Note Taker, so you can choose the one that best meets your needs.
Computational Intelligence in Wireless Sensor Networks
Wireless sensor networks are becoming increasingly popular as a means of gathering data about the world around us. However, these networks face a number of challenges, including the need for energy-efficient algorithms and the need to deal with incomplete and noisy data. Computational intelligence is a branch of artificial intelligence that is particularly well suited to these sorts of problems. This seminar will explore the use of computational intelligence in wireless sensor networks, with a focus on recent research developments.
Fog Computing
Fog computing is a distributed computing paradigm that provides data, compute, storage, and application services closer to the users and devices, at or near the edge of the network. Fog computing extends cloud computing and services by pushing them closer to the edge of the network, where devices (such as sensors and actuators) and people interact with the cloud. Fog computing can help to reduce the cost and complexity of deploying large-scale data services, and it can also help to improve the user experience by providing faster response times and lower latency.
Software Reuse
Software reuse is the process of using existing software components to create new software applications. It is a key principle of software engineering that can help software developers save time and money while creating high-quality software products. There are many benefits to software reuse, including increased software quality, reduced development time, and improved code maintainability. However, successful software reuse requires careful planning and execution. In the seminar, you can discuss the basics of software reuse and how to implement it effectively in your software development projects.
Google Project Loon
Google Project Loon is a research and development project by Google X that was created to bring Internet access to rural and remote areas. The project uses high-altitude balloons placed in the stratosphere at an altitude of about 32 km (20 mi) to create an aerial wireless network with up to 3G-like speeds. The balloons are equipped with solar panels, batteries, and transceivers that communicate with ground stations and relay Internet access to people in the coverage area.
Prescription Eyeglasses
Prescription eyeglasses are glasses that are prescribed by an optometrist or ophthalmologist to correct vision problems. They usually have a corrective lens on the front of the glasses that helps to focus light on the retina, which in turn improves vision. Prescription eyeglasses can also be used for cosmetic purposes, such as hiding a lazy eye.
Eye Gaze Communication System
An eye gaze communication system is a device that allows people to communicate using only their eyes. This technology is often used by people with severe physical disabilities who are unable to speak or use their hands. The system works by tracking the user’s eye movements and translating them into commands that can be used to control a computer or other devices. While this technology is still in its early stages, it has the potential to revolutionize the way people with disabilities communicate.
MRAMs and SMRs
Magnetic random-access memory (MRAM) is a type of non-volatile memory that uses magnetic fields to store data. Static magnetic random-access memory (SMR) is a type of MRAM that uses a static magnetic field to store data. SMRs are more resistant to power outages and data corruption than other types of MRAM, making them ideal for mission-critical applications.
Cyberbullying Detection
Cyberbullying is a growing problem among children and teenagers. It can take many forms, including online harassment, spreading rumors, and making threats. While it can be difficult to detect, there are some warning signs that parents and teachers can look for. These include sudden changes in behavior, withdrawal from social activities, and declining grades. If you suspect that your child is being cyberbullied, there are a number of steps you can take to help them. These include talking to them about it, reporting it to the proper authorities, and monitoring their online activity. Cyberbullying is a serious issue, but with awareness and action, it can be stopped.
Jini Technology
Jini technology is a distributed computing architecture that allows devices to connect and interact with each other over a network. Jini-enabled devices can be connected together to form an ad hoc network, which can be used to share data and resources. Jini technology is designed to be simple and easy to use, with a minimum of configuration required. Jini-enabled devices can be used to create everything from home automation systems to large-scale distributed systems.
Quantum Information Technology
Quantum information technology is an emerging field that uses the principles of quantum mechanics to process and store information. This technology has the potential to revolutionize computing, communication, and sensing. Currently, quantum information technology is in its early stages of development, but there are a number of potential applications that could have a major impact on society
. For example, quantum computers could be used to solve problems that are intractable for classical computers, such as factorizing large numbers or searching large databases. Quantum communication could enable secure communication that is impossible to eavesdrop on. And quantum sensors could be used to detect extremely weak signals, such as gravity waves or dark matter.
Facility Layout Design using Genetic Algorithm
Facility layout design is a critical component of many manufacturing and industrial operations. An effective layout can improve productivity and efficiency while reducing costs. Unfortunately, designing an optimal layout is a complex task that often requires significant trial and error.
Genetic algorithms offer a potential solution to this problem by using evolutionary techniques to generate near-optimal layouts. This approach has been shown to be effective in a variety of applications and industries. As a result, genetic algorithm-based facility layout design is a promising area of research with the potential to significantly impact many businesses and operations.
Tamper Resistance
Tamper resistance is a term used to describe the ability of a system or device to resist being tampered with. Tamper resistance can be achieved through a variety of means, including physical security measures, cryptographic protections, and software security.
Delay Tolerant Networking
Delay Tolerant Networking (DTN) is a new networking paradigm that is designed to cope with the challenges posed by highly dynamic and resource-constrained environments. DTN is characterized by intermittent connectivity, high link failure rates, and significant delays. Traditional networking protocols are not well suited for these conditions, and as a result, DTN has emerged as a new approach for networking in challenging environments.
DTN protocols are designed to deal with the challenges posed by intermittent connectivity and high link failure rates by using store-and-forward mechanisms. In addition, DTN protocols often make use of collaborative mechanisms, such as social networking, to route data around the network. DTN is an active area of research, and there are a number of different DTN protocols that have been proposed.
Helium Drives
Helium drives are a type of solid-state drive that use helium instead of air to keep the drive’s components cool. Helium is less dense than air, so it can help to reduce the amount of heat that builds up inside the drive. This can improve the drive’s performance and longevity. Helium drives are more expensive than traditional drives, but they offer a number of benefits.
Holographic Memory
Holographic memory is a new type of computer memory that uses light to store data. Unlike traditional computer memory, which stores data in bits, holographic memory can store data in multiple dimensions. This makes it much more efficient than traditional memory, and allows for higher data densities. Holographic memory is still in the early stages of development, but has the potential to revolutionize computing.
Autonomic Computing
Autonomic computing is a term coined by IBM in 2001 to describe a self-managing computer system. The idea is that a computer system can be designed to manage itself, without the need for human intervention. This would allow a computer system to automatically adjust to changing conditions, such as increasing traffic on a network, and make decisions that would optimize performance. Autonomic computing is still in the early stages of development, but has the potential to revolutionize the way we use computers.
Google Glass
Google Glass is a wearable computer with an optical head-mounted display (OHMD). It was developed by Google X, the company’s research and development arm. The device was first announced in April 2012, and was released to early adopters in the United States in May 2014. Google Glass is capable of displaying information in a smartphone-like format, and can also be used to take photos and videos, and to perform internet searches.
Blockchain Technology
Blockchain technology is a distributed database that allows for secure, transparent and tamper-proof transactions. This makes it ideal for a wide range of applications, from financial services to supply chain management. While the technology is still in its early stages, it has the potential to revolutionize the way we do business. For those interested in learning more about blockchain technology, they can include this in technical seminar topics for cse.
Internet of Things
The Internet of Things (IoT) is a network of physical devices, vehicles, home appliances, and other items embedded with electronics, software, sensors, and connectivity which enables these objects to connect and exchange data. The aim of IoT is to create an ecosystem of interconnected devices that can be controlled and monitored remotely. In a seminar cse students can explore the potential of IoT in various fields such as healthcare, transportation, smart cities, and manufacturing.
Brain Chips
Brain chips are a type of computer chip that can be implanted into the brain. These chips are designed to interface with the brain’s neurons and allow people to control devices with their thoughts. Brain chips are still in the early stages of development, but they hold great promise for people with disabilities. In the future, brain chips may also be used to improve cognitive abilities or to treat conditions like Alzheimer’s disease.
Graphics Processing Unit (GPU)
A graphics processing unit (GPU) is a specialized electronic circuit designed to rapidly manipulate and alter memory to accelerate the creation of images in a frame buffer intended for output to a display device. GPUs are used in embedded systems, mobile phones, personal computers, workstations, and game consoles.
Modern GPUs are very efficient at manipulating computer graphics and image processing, and their highly parallel structure makes them more effective than general-purpose CPUs for algorithms where the processing of large blocks of data is done in parallel. In a personal computer, a GPU can be present on a video card, or it can be embedded on the motherboard.
Smart Cards
A smart card is a type of credit card that contains a microprocessor. This microprocessor can be used to store information, such as your account number and balance. Smart cards are more secure than traditional credit cards, because the microprocessor makes it difficult for thieves to copy your information. In addition, smart cards can be used to store loyalty points or other rewards. If you’re looking for a new way to pay for your purchases, a smart card may be the right choice for you.
Night Vision Technology
Night vision technology is a type of technology that allows people to see in low-light or no-light conditions. This type of technology is often used by the military, law enforcement, and other professionals who need to be able to see in dark conditions. Night vision technology typically uses one or more of three different methods to allow people to see in the dark: image intensification, active illumination, and thermal imaging.
Voice Portals
Voice portals are a type of computer-based system that allows users to access information or perform tasks using voice commands. Voice portals are becoming increasingly popular as they offer a hands-free way to interact with technology. Many voice portals use artificial intelligence (AI) to understand user requests and provide accurate results. Some popular examples of voice portals include Siri, Google Assistant, and Alexa.
Smart Dust is a term used to describe tiny sensors that can be used to monitor everything from air quality to movement. These sensors are often powered by solar energy, making them environmentally friendly as well as efficient. Smart Dust has a wide range of potential applications, including tracking wildlife, monitoring traffic, and even spying on people. However, the technology is still in its early stages, and there are concerns about privacy and security.
A DOS attack is a type of cyber attack that is designed to overload a system with requests, making it unavailable to legitimate users. This can be done by flooding the system with traffic, or by sending it a large number of requests that it cannot handle. DOS attacks are often carried out by botnets, which are networks of infected computers that are controlled by a hacker.
Pervasive Computing
Pervasive computing is a term used to describe the trend of technology becoming increasingly embedded in our everyday lives. This can be seen in the rise of wearable devices, such as fitness trackers and smartwatches, as well as the proliferation of connected devices in the home, such as thermostats and security cameras. With the advent of 5G and the Internet of Things, this trend is only likely to continue, with an ever-increasing number of devices being connected to the internet. This has a number of implications for both individuals and businesses, and it is important to stay up-to-date on the latest developments in this field.
Speed protocol processors
Speed protocol processors are devices that are used to process data at high speeds. They are often used in telecommunications and networking applications. Technical seminar topics for cse often include speed protocol processors as a topic of discussion.
ITwin is a company that provides a service that allows users to securely access their files and data from any internet-connected device. The company’s flagship product is a USB drive that contains two parts: a “client” that is installed on the user’s computer, and a “server” that is stored in the cloud. When the user plugs the iTwin into their computer, the client connects to the server and allows the user to access their files as if they were on their own computer. The service also allows the user to share files with others, and to access their files from any internet-connected device.
Clockless Chip
A clockless chip is a type of microprocessor that does not use a clock signal to synchronize its operations. Clockless chips are also known as asynchronous or self-timed chips
Rain Technology Architecture
Rain technology architecture is a type of architecture that uses rainwater to provide a cooling effect. This can be done by using a roof system that collects and stores rainwater, or by using a facade system that allows rainwater to flow down the side of a building. This type of architecture is becoming increasingly popular as a way to reduce energy consumption and lower carbon emissions.
Code Division Duplexing
Code Division Duplexing is a duplexing technique used in communication systems. It allows two users to share the same frequency band by using different codes. CDD can be used in both frequency-division duplexing (FDD) and time-division duplexing (TDD) systems. In an FDD system, the two users are assigned different frequencies for uplink and downlink transmission. In a TDD system, the two users are assigned different time slots for uplink and downlink transmission. CDD can provide a higher data rate than FDD or TDD alone.
Augmented Reality vs Virtual Reality
Augmented reality (AR) and virtual reality (VR) are two of the most popular technical seminar topics for cse students. Both technologies have a lot to offer, but they are also very different. AR is a technology that overlays digital information on the real world, while VR creates a completely simulated environment. VR is often used for gaming and entertainment, while AR has a range of applications, from retail to education.
DNA Based Computing
DNA-based computing is a rapidly emerging field of research that uses DNA and other biomolecules to store and process information. This technology has the potential to revolutionize computing, as it offers a more efficient and scalable way to store and process data. In addition, DNA-based computing is well suited for certain types of applications, such as data mining and machine learning. As this technology continues to develop, it will likely have a major impact on the way we use computers.
Transactional Memory
Transactional memory is a programming technique that allows for easy management of concurrent access to shared data. It is especially useful in multicore and multithreaded environments, where it can help to prevent race conditions and other forms of data corruption. Transactional memory is a relatively new technology, but it is already being used in a variety of programming languages and applications.
A Voice XML
Voice XML is a markup language that allows developers to create voice-based applications. With Voice XML, developers can create applications that allow users to interact with a system using their voice. Voice XML applications can be used for a variety of purposes, such as voice-activated menus, voice-based search, and voice-based information services. Voice XML is an important tool for developers who want to create voice-based applications.
Virtual LAN Technology
Virtual LAN (VLAN) technology is a way to create multiple logical networks on a single physical network. VLANs are often used to segment a network into different subnets for security or performance reasons. Technical seminar topics for cse can include anything from the history of VLANs to the technical details of how they work. This makes VLANs an important topic for anyone interested in networking or computer science.
Global Wireless E-Voting
Global Wireless E-Voting is a technical seminar topic for cse students. It explains the process of conducting an election using wireless devices such as smartphones and tablets. The seminar will cover the advantages and disadvantages of this method of voting, as well as the potential security risks.
Smart Fabrics
Smart fabrics are fabrics that have been designed to incorporate technology into their construction. This can include anything from integrated sensors to heating and cooling elements. Smart fabrics are often used in military and industrial applications, but they are also finding their way into consumer products as well. Technical seminar topics for cse often explore the potential applications of smart fabrics and how they might be used in the future.
Voice Morphing
Voice morphing is the process of modifying a voice to sound like another person, or to modify the way your own voice sounds. This can be done for a variety of reasons, including entertainment, impersonation, and disguise. Voice morphing technology has come a long way in recent years, and it is now possible to create very realistic-sounding voice morphs.
Big Data Technology
Big data is a term that refers to the large volume of data that organizations generate on a daily basis. This data can come from a variety of sources, including social media, transactions, and sensor data. While big data has always been a part of our lives, it has only recently become possible to collect and analyze it on a large scale. This has led to a new field of data science, which is dedicated to understanding and extracting insights from big data
Ambiophonics
Ambiophonics is a method of sound reproduction that creates a more realistic and natural soundscape. It does this by using multiple speakers to create a three-dimensional sound field. This allows the listener to hear sounds as they would in real life, rather than from a single point in space. Ambiophonics can be used for both music and movies, and is becoming increasingly popular as a way to improve the sound quality of home theater systems.
Synchronous Optical Networking
Synchronous Optical Networking (SONET) is a standard for high-speed data transmission. It is used extensively in North America and Japan, and is slowly gaining popularity in Europe. SONET uses optical fiber to transmit data at speeds of up to 10 Gbps.
InfiniBand is a high-performance, scalable networking technology that is used in data centers and high-performance computing (HPC) environments. It offers low latency and high bandwidth, making it ideal for applications that require high levels of performance. InfiniBand is also designed to be scalable, so it can be used in small, medium, and large environments.
Packet Sniffers
A packet sniffer is a computer program or piece of hardware that can intercept and log traffic that passes through a network. Packet sniffers are often used by network administrators to troubleshoot network problems, but they can also be used by malicious actors to steal sensitive information. Technical seminar topics for cse usually include an overview of how packet sniffers work and how they can be used for both good and evil.
Cryptography Technology
Cryptography is the practice of secure communication in the presence of third parties. It is used in a variety of applications, including email, file sharing, and secure communications. Cryptography is a technical field, and there are a variety of seminar topics for cse students interested in learning more about it. These topics include the history of cryptography, the types of cryptography, and the applications of cryptography.
Humanoid Robot
A humanoid robot is a robot with a human-like appearance, typically including a head, two arms, and two legs. Humanoid robots are increasingly being developed for a variety of purposes, including assistance in the home, healthcare, and manufacturing. While many humanoid robots are still in the developmental stage, there are already a number of commercially available robots, such as the Honda ASIMO and the Boston Dynamics Atlas.
Humanoid robots are typically more expensive and complex than other types of robots, but they offer a number of advantages, including the ability to more easily interact with humans and navigate complex environments.
The X-Vision is a technical seminar for computer science students. It covers a wide range of topics, from the basics of computer programming to more advanced topics such as artificial intelligence and machine learning.
Bio-inspired Networking
Bio-inspired networking is a relatively new field of study that draws inspiration from biological systems to develop more efficient and effective networking solutions. The concepts of bio-inspired networking are being applied to a variety of different fields, including data networking, computer networking, and wireless networking.
By studying how biological systems communicate and interact, researchers are able to develop new protocols and algorithms that can be used to improve the efficiency of existing networks. Additionally, bio-inspired networking is being used to develop new types of networks that are more resilient to failure and better able to adapt to changing conditions.
BEOWULF Cluster
The BEOWULF Cluster is a type of computer cluster designed for high performance computing. It is named after the Old English epic poem Beowulf, which tells the story of a heroic warrior who defeats a monstrous creature. BEOWULF clusters are often used for scientific and engineering applications that require a lot of computing power, such as weather forecasting, climate modeling, and protein folding. Technical seminar topics for cse usually revolve around case studies of how certain organizations have utilized BEOWULF clusters to solve complex problems.
XML Encryption
XML encryption is a process of encoding data in XML format so that only authorized users can access it. This process is used to protect sensitive information from being accessed by unauthorized individuals. XML encryption is a relatively new technology, but it has already been adopted by a number of organizations as a way to protect their data.
Advanced Driver Assistance System (ADAS)
ADAS is a system that uses sensors and cameras to assist the driver in a variety of tasks, such as lane keeping, adaptive cruise control, and automated braking. The system is designed to make driving safer and more efficient by reducing the workload on the driver. ADAS is an important emerging technology, and its applications are expected to grow in the coming years.
Digital Scent Technology
Digital scent technology is a relatively new field that is constantly evolving. This type of technology allows for the creation of scents that can be stored in a digital format and then reproduced on demand. This technology has a wide range of potential applications, from creating customized perfumes to providing aromatherapy treatments. Digital scent technology is still in its early stages, but it has great potential to change the way we interact with scent.
Symbian Mobile Operating System
The Symbian mobile operating system was once one of the most popular platforms for smartphones. However, it has since been eclipsed by newer operating systems such as Android and iOS. Despite this, Symbian remains a popular choice for some users, particularly in emerging markets. If you’re interested in learning more about Symbian, this seminar topic is for you. In this cover the history of the platform, its key features, and its advantages and disadvantages compared to other mobile operating systems.
Mind-Reading Computer
A mind-reading computer is a computer that is able to interpret human thoughts and intentions. This technology is still in its early stages, but it has the potential to revolutionize the way we interact with computers. Currently, mind-reading computers are used mostly for research purposes, but they have also been used to help people with disabilities communicate. In the future, mind-reading computers could be used for a wide variety of applications, including personal assistants, security systems, and even lie detectors.
Distributed Interactive Virtual Environment
A distributed interactive virtual environment (DIVEn) is a type of virtual environment that is distributed across multiple computers. DIVEns are typically used for training, simulations, and gaming applications. Technical seminar topics for cse (computer science students) can include DIVEns and their applications.
Trustworthy Computing
Trustworthy Computing is a term coined by Microsoft to describe its commitment to building secure and reliable software. In practice, this means that Microsoft works to avoid security vulnerabilities in its products and services, and to quickly address any that do arise. Trustworthy Computing also includes efforts to protect user privacy and to ensure that users have control over their own data.
In order to achieve these goals, Microsoft employs a variety of technical and organizational measures. Technical measures include things like code signing, which verifies that code has not been tampered with, and sandboxing, which limits the damage that can be done by malicious code. Organizational measures include things like security audits and training for employees. By taking these measures, Microsoft seeks to ensure that its products and services are safe and reliable for users.
Teleportation
Teleportation is the theoretical transfer of matter or energy from one point to another without traversing the physical space between them. It is a common plot device in science fiction, and has been the subject of serious scientific research. While there is no known way to teleport matter, it is possible to teleport energy.
A MemTable is a data structure used by many database management systems (DBMS) to store recently committed data in memory. It is usually a hash table or a binary tree. When a transaction is committed, the data is first written to the MemTable before being written to disk. This allows for fast reads, as the data is already in memory. However, it also means that the data is lost if the system crashes before the data can be written to disk. For this reason, the data in a MemTable is often flushed to disk periodically.
Voice Browser
Voice browsers are software programs that enable users to access the World Wide Web using spoken commands. This technology is still in its early stages, but it has the potential to revolutionize the way we interact with the internet. Currently, most voice browsers are designed for use with mobile devices, such as smartphones. This allows users to surf the web hands-free, which can be especially useful for those with disabilities. In the future, voice browsers may become more widespread and sophisticated, offering features like voice-activated search and the ability to read web pages aloud.
Photonics Communications
Photonics Communications is a rapidly growing field that uses light to transmit information. This technology has a wide range of applications, from fiber optic cable to medical imaging. Photonics Communications is a relatively new field, and as such, there are many opportunities for research and development. Technical seminar topics for cse students may include an overview of the history and physics of photonics, as well as current and future applications.
Neural Interfacing
Neural interfacing is the process of connecting the nervous system to an external device. This can be done for a variety of reasons, including medical treatment, rehabilitation, and augmenting human abilities. Neural interfacing is a rapidly growing field, with new technologies being developed all the time. If you’re interested in neural interfacing, there are a number of resources available to learn more about the topic.
5g Wireless System
The 5G wireless system is the next generation of wireless technology. It is designed to provide higher speeds, lower latency, and more reliability than previous generations of wireless technology. 5G is still in the early stages of development, but it is already being tested in some areas. Technical seminar topics for cse students include an overview of the 5G wireless system, its potential applications, and the challenges involved in its deployment.
Wireless Fidelity
Wireless Fidelity, commonly known as Wi-Fi, is a wireless networking technology that allows devices to connect to the internet without the need for a physical connection. Wi-Fi is used in a variety of devices, including laptops, smartphones, and tablets. It has become increasingly popular in recent years as more and more devices are able to connect to the internet wirelessly. Technical seminar topics for cse students can include an overview of Wi-Fi technology, how it works, and its applications.
Artificial Intelligence
Artificial intelligence is a rapidly growing field with a wide range of applications. From self-driving cars to personal assistants, artificial intelligence is changing the way we live and work. CSE students can benefit from learning about artificial intelligence by understanding its potential applications and technical underpinnings.
Airborne Internet
Airborne Internet is a term used to describe the use of aircraft as platforms for providing Internet access. The concept is similar to that of using satellites to provide Internet access, but with the added benefit of being able to target specific areas with greater accuracy and without the need for expensive infrastructure. There are a number of companies working on developing this technology, and it has the potential to revolutionize the way we connect to the Internet.
Ipv6 – The Next Generation Protocol
IPv6 is the next generation of the Internet Protocol, designed to eventually replace IPv4. It has a number of advantages over IPv4, including a larger address space, better security, and improved efficiency. IPv6 is not backward compatible with IPv4, however, so a transition to the new protocol will require some changes to the way the Internet works.
Zigbee Technology
Zigbee is a wireless communication technology that allows devices to communicate with each other using low-power radio signals. Zigbee technology is used in a variety of applications, including home automation, security systems, and industrial control. Zigbee devices are often used in conjunction with other devices, such as sensors, to create a network of devices that can share data and perform tasks.
Finger Vein Recognition
Finger vein recognition is a type of biometric authentication that uses the unique patterns in a person’s finger veins to verify their identity. This technology is becoming increasingly popular in a variety of settings, from businesses to government agencies. Finger vein recognition is more accurate than traditional fingerprinting methods, and it is also more difficult to fake. If you are looking for a cutting-edge way to secure your information, finger vein recognition is a great option.
Chatbot for Business Organization
A chatbot is a computer program that simulates human conversation. Chatbots are used in business organizations to automate customer service or sales tasks. For example, a chatbot can help customers with questions about a product or service, or it can provide customer support. Chatbots can also be used to schedule appointments or make reservations.
Haptic Technology
Haptic technology is a branch of technology that deals with the sense of touch. It allows users to interact with digital information through the use of tactile feedback, or the sensation of touch. Haptic technology is used in a variety of applications, including gaming, virtual reality, and haptic interfaces.
DNS Tunneling
DNS tunneling is a technique used to encapsulate data in DNS queries and responses. This allows the data to be transported over an existing DNS infrastructure without being detected or blocked by firewalls. DNS tunneling can be used for a variety of purposes, including data exfiltration, command and control, and pivoting. DNS tunneling is a powerful tool that can be used for both good and evil. While it can be used to bypass firewalls and access blocked websites, it can also be used by attackers to steal sensitive data or take control of systems.
Brain Fingerprinting
Brain fingerprinting is a controversial technique that purports to be able to identify whether a person has knowledge of a particular event or not, based on their brainwaves. The technique is not widely accepted by the scientific community, and there is little empirical evidence to support its claims.
Computer Forensics
Computer forensics is the process of using investigative techniques to collect, analyze, and report on data that may be used as evidence in a legal case. This can include data stored on a computer, as well as data that has been deleted from a computer. Computer forensics is a relatively new field, and as such, there are many technical seminar topics for cse students that cover the topic in detail. These topics can include an overview of the field, as well as more specific topics such as data recovery, file analysis, and email forensics.
Intel Centrino Mobile Technology
Intel Centrino Mobile Technology is a platform that includes a processor, chipset, and wireless adapter designed to work together to provide the best possible mobile performance. The platform is designed for use in notebook computers and other mobile devices. It offers a number of benefits, including longer battery life, smaller form factor, and lower power consumption. Intel Centrino Mobile Technology is the perfect choice for mobile users who demand the best possible performance from their devices.
High Performance DSP Architectures
DSP architectures are critical for many applications including signal processing, communications, and audio/video processing. In this seminar topic, you can discuss various high performance DSP architectures and their applications. You can also explore the tradeoffs between different architecture choices.
Multiprotocol Label Switching
Multiprotocol Label Switching (MPLS) is a type of data-carrying technique for high-performance telecommunications networks. MPLS directs data from one network node to the next based on short path labels rather than long network addresses, avoiding complex lookups in a routing table. The labels identify virtual links between distant nodes rather than endpoints. MPLS can encapsulate packets of various network protocols, hence its name “multiprotocol”. In an MPLS network, data packets are assigned labels. Packet-forwarding decisions are made solely on the contents of this label, without the need to examine the packet header for routing information.
Cooperative Linux
Cooperative Linux is a free and open source software project that allows users to run Linux applications on Windows systems. It is based on the idea of co-operative multitasking, where each process is assigned a portion of the CPU time, and all processes are allowed to run concurrently. This makes it possible to run both Linux and Windows applications side-by-side, without the need for virtualization. Cooperative Linux is available for both 32-bit and 64-bit systems.
Real Time Application Interface
A real-time application interface (RAI) is a type of software that allows different applications to share data and resources in real time. This can be useful for a variety of purposes, such as allowing multiple applications to access the same database or allowing different applications to share data with each other. RAIs can be either proprietary or open source, and they can be used for a variety of different applications.
Tempest and Echelon
Tempest and Echelon are two of the most popular technical seminar topics for cse students. Tempest is a software engineering tool that automates the process of creating software prototypes. It is used to create high-fidelity prototypes of software applications. Echelon is a tool that helps developers to create efficient and scalable network applications. It is used to develop distributed systems.
Mobile Virtual Reality Service
Mobile virtual reality (VR) is a service that allows users to access VR content on their mobile devices. This includes both smartphone-based VR headsets and standalone VR headsets. Mobile VR has become increasingly popular in recent years, as it offers a more affordable and convenient VR experience than desktop VR. Technical seminar topics for cse students include an overview of mobile VR technology, its applications, and its potential future.
Word Sense Disambiguation
Word sense disambiguation is the process of determining which meaning of a word is being used in a particular context. This can be a difficult task for computers, as the same word can have multiple meanings depending on the context in which it is used. However, there are some techniques that can be used to help computers disambiguate words, such as looking at the surrounding words or using a database of known word meanings. Word sense disambiguation is an important task for natural language processing, as it can help computers to better understand the text they are processing.
Yii Framework
The Yii Framework is a high-performance PHP framework for developing Web applications. It is based on the Model-View-Controller (MVC) architectural pattern. The name “Yii” means “simple and evolutionary” in Chinese , and the goal of the Yii Framework is to make it easy for developers to create complex Web applications. The Yii Framework is popular among cse students, as it is a reliable and well-tested framework that is versatile and easy to use.
Microsoft HoloLens
Microsoft HoloLens is a headset that allows you to view and interact with holograms. HoloLens can be used for a variety of applications, including gaming, education, and business. HoloLens is a cutting-edge technology that is constantly evolving, making it an exciting and ever-changing field.
Handheld Computers
Handheld computers, also known as personal digital assistants (PDAs), are becoming increasingly popular. They offer many of the same features as a laptop computer, but are smaller and more portable. PDAs can be used for a variety of tasks, including keeping track of your schedule, storing contact information, and playing games. With the increasing popularity of PDAs, there is a growing market for PDA accessories, such as cases and chargers.
Sniffer for detecting lost mobiles
A sniffer is a type of software that can be used to detect lost mobiles. It works by scanning for and identifying wireless signals, then triangulating the position of the mobile based on the strength of the signal. This type of software can be very useful for finding lost or stolen phones, as well as for tracking down the source of interference.
Digital Audio Broadcasting
Digital Audio Broadcasting (DAB) is a digital radio technology used to broadcast radio programmes. It uses a wideband spectrum that allows for more channels to be broadcast than with analogue radio. DAB also provides higher quality sound than analogue radio, making it a popular choice for music lovers.
Mobile Phone Cloning
Mobile phone cloning is the process of copying the identity of one mobile phone to another. This can be done by copying the SIM card or by using software to copy the phone’s internal data. Cloning a phone allows someone to make calls and send texts as if they were the owner of the cloned phone. Cloned phones can be used to commit fraud or other crimes.
Near Field Communication NFC
Near Field Communication, or NFC, is a short-range wireless technology that allows devices to communicate with each other. NFC can be used for a variety of purposes, including making payments, sharing data, and connecting to devices. NFC is a relatively new technology, and as such, there is still much to learn about it. However, NFC is quickly becoming more popular, and is expected to have a major impact on the way we live and work.
IP Telephony
IP telephony, also known as VoIP (Voice over Internet Protocol), is a type of telecommunication that uses the Internet Protocol to place and receive telephone calls. IP telephony allows users to make and receive calls from any location with an Internet connection. In addition, IP telephony can offer a number of features and benefits that traditional telephone systems cannot, such as call forwarding, caller ID, and voicemail. IP telephony is a rapidly growing field, and many businesses are beginning to adopt it as a replacement for traditional telephone systems.
Transient Stability Assessment using Neural Networks
Transient stability assessment is a critical part of power system planning and operation. Conventional methods for performing this assessment, such as the direct method and the energy function method, can be time-consuming and computationally intensive. Neural networks offer a promising alternative, as they can learn from data and perform classification and regression tasks with high accuracy. In this seminar, you can discuss the use of neural networks for transient stability assessment, and compare their performance to traditional methods. You can also discuss some of the challenges associated with using neural networks for this application.
Broad Band Over Power Line
Broadband over power line (BPL) is a technology that allows high-speed Internet access using the existing electrical grid. BPL is sometimes also referred to as power line communications (PLC). BPL technology has the potential to provide high-speed Internet access to homes and businesses in rural and suburban areas that do not have access to traditional broadband technologies such as cable or DSL. BPL technology is still in the early stages of development, and there are a number of technical challenges that need to be addressed before it can be widely deployed.
Wardriving is the act of searching for Wi-Fi networks in a moving vehicle, using a laptop or other mobile device. The term comes from the analogy to war driving, in which a battlefield is scanned for enemy activity. Wardriving is commonly used to find open wireless access points for the purpose of free Internet access, or to audit the security of one’s own wireless network. However, it can also be used for malicious purposes, such as stealing confidential information or launching denial-of-service attacks.
Smart Skin for Machine Handling
Smart skin is a type of technology that allows machines to handle objects more gently and safely. This is achieved by using sensors to detect the shape, size, and weight of an object, and then adjust the machine’s grip accordingly. This technology has a wide range of potential applications, from manufacturing to healthcare. It can help reduce workplace injuries, improve efficiency, and enable delicate objects to be handled with care.
Unicode And Multilingual Computing
Unicode is a standard for encoding characters that is used by most computer systems. It allows for the representation of characters from a variety of languages, making it an essential tool for multilingual computing. In this seminar you can cover the basics of Unicode, including its history, how it works, and its applications. In addition, you can also discuss some of the challenges involved in working with Unicode data, as well as some tips and tricks for dealing with these challenges.
3D Human Sensing
3D human sensing is a rapidly growing field with a wide range of potential applications. This technology allows for the capture of three-dimensional images of people, which can then be used for a variety of purposes such as security, biometrics, and even gaming. 3D human sensing is still in its early stages of development, but it has already shown great promise and is sure to have a major impact in the years to come.
Wireless Sensor Networks
A wireless sensor network (WSN) is a type of network that consists of spatially distributed autonomous sensors to monitor physical or environmental conditions, such as temperature, sound, vibration, pressure, motion or pollutants. Wireless sensor networks are often used in industrial and military applications where it would be expensive or impossible to lay down a wired network.
Hyper-Threading technology
Hyper-Threading is a technology used by some Intel processors that allows a single physical processor to appear as two logical processors to the operating system. This can improve the performance of certain types of applications, but it can also lead to stability issues. If you’re considering using Hyper-Threading on your computer, it’s important to understand both the benefits and the risks before making a decision.
Goal-line technology
Goal-line technology is a system used in football to determine whether a shot has crossed the goal line and should be counted as a goal. The technology is typically a sensor-based system that uses cameras or lasers to track the ball’s position and relay the information to a computer, which then determines whether the ball has crossed the line. Goal-line technology is used to supplement the referee’s decision-making, and is not intended to replace the referee.
Smart Textiles
Smart textiles are fabrics that have been designed to incorporate technology into their structure. This can include everything from conductive threads that can be used to create circuits, to sensors that can detect changes in temperature or humidity. Smart textiles are still a relatively new technology, but they have a wide range of potential applications. For example, they could be used in medical garments to monitor patients’ vital signs, or in military clothing to help soldiers stay aware of their surroundings. With the rapid advancement of technology, it is likely that smart textiles will become increasingly common in the years to come.
Nanorobotics
Nanorobotics is the technology of creating robots at the nanometer scale. Nanorobots are robots that are between 1 and 100 nanometers in size. This technology is still in its early stages, but has the potential to revolutionize many industries. Nanorobots could be used in medicine to target specific cells or diseases, in manufacturing to create products with incredible precision, or in environmental cleanup to remove pollutants from water or soil. The potential applications of nanorobotics are vast, and the technology is still being developed.
Design of 2-D Filters using a Parallel Processor Architecture
Design of 2-D Filters using a Parallel Processor Architecture is a technical seminar topic for cse students. This topic covers the design and implementation of 2-D filters using a parallel processor architecture. In this seminar you can cover the theory behind the design of 2-D filters, as well as the practical aspects of implementing them on a parallel processor.
Digital Preservation
Digital preservation is the process of ensuring that digital information and media remain accessible and usable over time. This can be done through a variety of means, such as migration (transferring data to new formats as old ones become obsolete), emulation (recreating an environment in which digital information can be used), and format standardization (ensuring that digital information can be read by different software programs). Digital preservation is an important part of maintaining our cultural heritage and ensuring that future generations can access and use the information and media we create today.
DNA Storage
DNA storage is a new and exciting field of research that holds tremendous potential for the future. By harnessing the power of DNA, we may one day be able to store massive amounts of data in a very small space. This could have a huge impact on the way we store and access information. Additionally, DNA storage is not susceptible to the same problems as traditional methods, such as data loss due to corruption or physical damage. For these reasons, DNA storage is a very promising technology with a bright future.
Network Attached Storage
Network Attached Storage, or NAS, is a type of storage device that connects to a network and provides shared storage for computers on that network. NAS devices are often used in small and medium-sized businesses, as they offer an affordable and easy-to-use solution for storing and sharing data. However, NAS devices can also be used in home networks. In this seminar, you can discuss some of the benefits of using a NAS device, as well as some of the different types of NAS devices available.
Enhancing LAN Using Cryptography and Other Modules
In this technical seminar, you can discuss how to enhance LAN using cryptography and other modules. In this you can cover the following topics:
-What is cryptography and how can it be used to improve LAN security?
-What are some other modules that can be used to enhance LAN security?
-How can these modules be implemented?
Reconfigurable computing
Reconfigurable computing is a rapidly growing field that offers the potential for significant performance gains over traditional CPUs. However, it can be difficult to know where to start when exploring reconfigurable computing. In this seminar you can provide an overview of the basics of reconfigurable computing, including its history, key concepts, and applications.
Thermography
Thermography is a technique that uses infrared radiation to create images of objects. It can be used for a variety of purposes, including detecting leaks in insulation, finding hot spots in electrical equipment, and even seeing through smoke and fog. Thermography is a valuable tool for many industries.
Nano Cars Into The Robotics
The rapid development of nanotechnology is opening up new possibilities for the development of nano cars. Nano cars are cars that are built at the nanometer scale, using nanotechnology. This allows for the creation of cars that are much smaller and more efficient than traditional cars. Nano cars also have the potential to be used in robotics, as they are able to navigate through tight spaces and avoid obstacles. The use of nano cars in robotics is still in its early stages, but the potential applications are exciting.
The DNA chips
DNA chips are a type of microarray that can be used to measure the expression levels of thousands of genes simultaneously. They are often used in genetic studies to identify genes that are differentially expressed in different conditions or diseases. t.
Prototype System Design for Telemedicine
A telemedicine system must be designed to allow a patient to consult with a doctor or other medical professional from a remote location. The system must be able to provide two-way audio and video communication, as well as allow for the exchange of medical data such as test results and X-rays. In addition, the system must be secure to protect the privacy of patient information.
Virtual Smart Phone
Virtual smart phones are an emerging technology that allows users to interact with their phone using a virtual interface. This technology has a number of potential applications, including allowing users to more easily access their phone’s features and providing a more immersive gaming experience. Virtual smart phones are still in the early stages of development, but they have the potential to revolutionize the way we use our phones.
Sandbox (computer security)
A sandbox is a security mechanism for separating running programs. It is often used to execute untested code, or untrusted programs from untrusted sources. A sandbox typically provides a tightly controlled environment where code can be executed. This is done by restricting the resources that code can access, such as file system calls or network access.
Biometrics Based Authentication
Biometrics-based authentication is a method of verifying a user’s identity by using physical or behavioral characteristics that are unique to that individual. This can include things like fingerprints, iris scans, voice recognition, and facial recognition. Biometrics-based authentication is more secure than traditional methods like passwords and PIN numbers, because it is much harder for someone to spoof or fake a biometric characteristic. This makes biometrics-based authentication an ideal solution for high-security applications like military and government use.
Optical Computer
Optical computers use light instead of electricity to process information. They are faster and more efficient than traditional computers, and they generate less heat. Optical computers are still in the early stages of development, but they have the potential to revolutionize computing.
M-Commerce, or mobile commerce, is the buying and selling of goods and services through mobile devices such as smartphones and tablets. M-Commerce has seen explosive growth in recent years, as more and more consumers use their mobile devices to shop online. This trend is only expected to continue, as mobile devices become increasingly omnipresent.
M-Commerce offers many advantages over traditional e-Commerce, including the ability to make purchases anywhere, anytime. For businesses, m-Commerce provides a new avenue for reaching and interacting with customers. As m-Commerce continues to grow, businesses will need to adapt their strategies to take advantage of this new platform.
E-Paper Technology
E-Paper technology is an exciting new development that is revolutionizing the way we read and interact with digital information. This technology allows for a wide range of applications, from e-books and e-newspapers to interactive displays and signage.
E-Paper has many advantages over traditional LCD screens, including better readability in direct sunlight and lower power consumption. E-Paper is also flexible and can be made into a variety of shapes and sizes. This makes it ideal for a wide range of applications, from wearable devices to large-scale public displays.

Web Scraping
Web scraping is a process of extracting data from websites. It can be done manually, but it is often automated using software. Web scraping can be used to collect data for a wide variety of purposes, including market research, price comparison, and data analysis.
Bluetooth Based Smart Sensor Networks
Bluetooth based smart sensor networks are becoming increasingly popular as a way to collect data and monitor activity in a variety of settings. These networks consist of small, wireless sensors that communicate with each other and with a central computer using Bluetooth technology. Smart sensor networks have a wide range of potential applications, including monitoring environmental conditions, tracking the movement of people or objects, and providing security for homes and businesses.
Smart Dustbins for Smart Cities
Smart dustbins are an important part of smart city infrastructure. By collecting and sorting waste, they help to keep cities clean and efficient. Additionally, smart dustbins can provide data that can be used to improve city planning and resource allocation. Technical seminar topics for cse students can include smart dustbin technology and its applications in smart cities.
Modular Computing
Modular computing is a type of computing where components are interchangeable and can be used to create different systems. This type of computing is often used in large organizations where different departments may need different types of systems. For example, a company’s accounting department may need a different type of system than the company’s marketing department. Modular computing allows for this flexibility by allowing companies to mix and match components to create the perfect system for each department.
3d Optical Data Storage
3D optical data storage is a new technology that allows data to be stored on a three-dimensional (3D) surface. This technology has the potential to increase storage capacity by orders of magnitude over existing technologies. 3D optical data storage is still in the early stages of development, but it has already shown promise for applications such as high-definition video and medical imaging.
Robotic Surgery
Robotic surgery is a type of minimally invasive surgery that uses a robot to assist the surgeon. The surgeon controls the robot, which allows for more precise movements and smaller incisions. This results in less pain and scarring for the patient. Robotic surgery is used for a variety of procedures, including heart surgery, cancer surgery, and gynecologic surgery.
Digital Jewelry
Digital jewelry is a type of jewelry that uses digital technology to create or enhance the design. It can be anything from a simple pendant with a photo inside to a complex piece of jewelry with multiple colors and patterns.
The Flexpad is a new type of computer that is flexible and can be used in a variety of ways. It is a great choice for those who want a versatile computer that can be used for a variety of purposes. The Flexpad is also a great choice for those who are looking for a computer that is easy to use and is very user-friendly.
Web Clustering Engines
Web clustering is a process of grouping together web pages that are similar in content. This can be useful for a variety of purposes, such as finding similar pages for a search query or identifying pages that are part of the same topic. There are a number of different algorithms that can be used for web clustering, and each has its own strengths and weaknesses. The choice of algorithm will often depend on the specific application.
Wireless USB
Wireless USB is a technology that allows devices to connect to each other using a wireless connection. This can be useful for a variety of purposes, such as connecting a printer to a computer or connecting a camera to a computer. Wireless USB is a relatively new technology, and it is not yet widely available. However, it has the potential to be very useful for a variety of applications.
Elastic Quotas
Elastic Quotas are a type of quota that allows a user to go over their allotted amount of resources, but are charged for the excess usage. This is different from a traditional quota, which would simply deny the user access to the resource once they reach their limit. Elastic Quotas are often used in cloud computing, where users may not know in advance how much resources they will need.
A bionic eye is an artificial eye that is powered by a battery. It is usually connected to the optic nerve, which sends signals from the eye to the brain. The bionic eye can be used to restore vision to people who are blind or have low vision. There are two types of bionic eyes: retinal implants and corneal implants. Retinal implants are placed under the retina, while corneal implants are placed in front of the retina. Retinal implants are more common and provide better vision than corneal implants.
Zenoss Core
Zenoss Core is a free and open source monitoring tool designed for large-scale enterprise environments. It provides comprehensive monitoring of network, server, and application performance, as well as configuration management and change detection. Zenoss Core is built on a robust and extensible architecture that allows for easy integration with third-party tools and customizations. As a result, it is an ideal solution for organizations looking for a flexible and scalable monitoring solution.
Quadrics Interconnection Network
A quadrics interconnection network is a type of computer network that uses a quadrics mesh to connect nodes. It is a high-performance network that is often used in supercomputing applications. Quadrics networks are designed to be scalable, so they can be used in small networks or large networks with thousands of nodes.
Compute Unified Device Architecture CUDA
CUDA is a parallel computing platform and programming model developed by Nvidia for general computing on its own line of GPUs. CUDA enables developers to speed up compute-intensive applications by harnessing the power of GPUs for the parallelizable part of the computation. The CUDA platform is a software layer that gives direct access to the GPU’s virtual instruction set and memory.
This allows programmers to execute computationally intensive tasks in C, C++, Fortran, and other languages that are supported by Nvidia’s compilers. In addition, CUDA comes with a set of libraries for linear algebra, signal processing, and other common applications.
Quantum Cryptography
Quantum cryptography is a relatively new field of study that uses the principles of quantum mechanics to create more secure methods of communication. This type of cryptography is often used in cases where traditional methods are not secure enough, such as when transmitting sensitive information between two parties. Quantum cryptography is still in the early stages of development, but it has the potential to revolutionize the way we communicate by making it impossible for eavesdroppers to intercept and read our messages.
The Cyborgs
A cyborg, short for “cybernetic organism”, is a being with both organic and artificial parts. The term was coined in 1960 by Manfred Clynes and Nathan S. Kline, who wrote about the potential advantages of creating human-machine hybrids for space exploration. In recent years, the term has come to be associated with the growing trend of humans using technology to enhance their physical and cognitive abilities. This can include everything from wearing fitness tracking devices to using brain implants to improve memory or vision. As technology continues to advance, it is likely that the number of people who identify as cyborgs will only grow.
Crusoe Processor
Crusoe is a type of microprocessor designed by Transmeta Corporation. It was first introduced in 2000. Crusoe processors are designed for low power consumption and are used in a variety of portable devices such as laptops, PDAs, and digital cameras. Crusoe processors are also used in some servers and high-end embedded systems.
Seam Carving for Media Retargeting
Seam carving is a technique for content-aware image resizing. Developed by Shai Avidan and Ariel Shamir, it allows users to remove or add pixels from an image while preserving the overall content. This makes it ideal for media retargeting, as it allows for the removal of unnecessary or unwanted elements from an image. Seam carving is a relatively new technique, but it has already been used in a variety of applications, including video retargeting and 3D model simplification.
Fluorescent Multi-layer Disc
A fluorescent multi-layer disc (FMLD) is a type of optical disc that uses multiple layers of fluorescence to store data.FMLDs are similar to other optical discs, such as CDs and DVDs, but they can store more data because of their multiple layers.FMLDs are often used for storing data backups, as they can store a large amount of data in a small space.
Holograph Technology
Holography is a technique that allows an image to be recorded in three dimensions. This technology has a wide range of applications, from security and authentication to medical imaging and data storage. Holography can be used to create 3D images of objects, which can then be viewed from different angles. This technology has the potential to revolutionize many industries, and it is only now beginning to be explored.
TCPA / Palladium
The Telecommunication Protection and Accessory Palladium Act (TCPA) is a set of regulations enacted by the Federal Communications Commission (FCC) in the United States that govern the use of telephone equipment and services. The TCPA includes provisions that protect consumers from unwanted telemarketing calls, as well as other unsolicited communications. It also requires that telecommunication equipment be accessible to people with disabilities.
Optical Burst Switching
Optical burst switching (OBS) is a type of optical switching in which data is transferred in bursts instead of in a continuous stream. OBS is similar to packet switching, but it uses shorter bursts of data and can therefore achieve higher speeds. OBS is also more efficient than traditional optical switching because it only transfers data when there is a burst of traffic, rather than continuously.
Ubiquitous Networking
Ubiquitous networking is a term used to describe the trend of ever-increasing connectivity. With the proliferation of mobile devices and the internet of things, more and more devices are connected to the internet. This has a number of implications for both individuals and businesses. On an individual level, ubiquitous networking makes it easier to stay connected to friends and family. It also makes it easier to access information and services. For businesses, ubiquitous networking provides new opportunities for marketing and customer engagement. It also creates new challenges in terms of data security and privacy.
NFC and Future
NFC, or Near Field Communication, is a technology that allows devices to communicate with each other when they are close together. NFC can be used for a variety of purposes, including making payments, exchanging data, and connecting to devices. NFC is already being used in many smartphones and is expected to become more widespread in the future. Technical seminar topics for cse students may include NFC and its potential applications.
Cloud Drops
Cloud Drops is a technical seminar topic for computer science students interested in learning about the latest advancements in cloud computing. In this seminar you can cover topics such as cloud architecture, cloud security, and cloud services.
Electronic paper
Electronic paper is a type of paper that can be used in electronic devices such as computers, tablets, and phones. This paper is made from a material that is similar to regular paper, but it is coated with a substance that allows it to be electrically charged. This paper can be used to display information in a variety of colors, making it a versatile tool for both personal and professional use.
Conclusion on seminar topics for computer science
The cse technical seminar topics presented in this article are very useful for students who want to improve their understanding of the subject. These topics will help them gain a better understanding of the concepts and principles involved in cse. Additionally, they can use these topics to prepare for exams and interviews as well.
You may also like to read
Final year projects for computer science
- Question Papers
- Scholarships
100+ Computer Science Presentation Topics (Updated)
This is a list of computer science Presentation Topics for students and professionals. These updated topics can be used for PowerPoint Paper presentation, Poster Presentation, classroom ppt presentation, seminars, seminars, webinars and conferences. etc. These presentation topics will be beneficial for students of Engineering and management courses such as BE Computer science, B Tech IT, MCA, BCA and MBA.
Below is the list of Best Computer Science Presentation Topics.
Artificial intelligence
Advanced Research Projects Agency Network (ARPANET)
AI & critical systems
Quantum Computing
Arithmetic logic unit (ALU)
Accelerated Graphics Port (often shortened to AGP)
ATX (Advanced Technology eXtended)
Sixth Sense Technology: Concept VS. Reality
BASIC – Beginner’s All-purpose Symbolic Instruction Code
Foldable Phones: Future of Mobiles
Basic computer skills
Blu-ray Disc
Cloud computing
CD-ROM (compact disc read-only memory)
Machine Learning
Cellular architecture
Central Processing Unit (CPU)
Cloud Print for Android
Chip (integrated circuit)
Computer multitasking
Cloud computing applications
Cloud computing basics
Cloud Printing for Windows
Computer architectures
Edge Computing
Computer Diagnostic Softwares
Computer form factor
Computer hardware troubleshooting
Cyber Security: New Challenges
Computer Networks
Computer software programs
Computer tracking software
The world of Blockchain
Conventional Binary Numbering System
Conventional PCI (PCI is an initialism formed from Peripheral Component Interconnect
DASD (Direct Access Storage Device)
Internet of Things (IoT)
Desktop Computers
Digital Visual Interface (DVI)
Transparent Display: Concept Vs Reality
DIMM – DIMM which means (dual in-line memory module)
DisplayPort
DNA computers
DVD (Digital Video Disc or Digital Versatile Disc)
Dynamic random-access memory (DRAM)
EEPROM (E2PROM) – Electrically Erasable Programmable Read-Only Memory
Electronic Delay Storage Automatic Calculator (EDSAC)
Embedded computers
Google cloud computing
EPROM – An EPROM (rarely EROM), or erasable programmable read-only Memory
Evolution of Computers
Expansion card (expansion board, adapter card or accessory card)
ExpressCard
FDDI – Fiber Distributed Data Interface
Intelligent Apps
Flash Memory
Graphics processors
Google Glass: Future of Computers!
Hard disk drive (HDD)
Harvard Architecture vs Von Neumann architecture
HDMI (High-Definition Multimedia Interface)
Standardization of web
Image scanner
Input and output devices (collectively termed I/O)
Type C port: The Gamechanger
IOPS (Input/Output Operations Per Second, pronounced eye-ops)
Latest Computer Technologies
Latest Trends in Computer Science
Mainframe computers
Manchester Small-Scale Experimental Machine (SSEM or “Baby”)
Mechanical Analog Computers
Mini-VGA connectors
Motherboard – the central printed circuit board (PCB)
Multiprocessing
Network Topologies
Neural computers
Non-Uniform Memory Access (NUMA) computers
Non-volatile memory
Neuralink: The brain’s magical future
Non-volatile random-access memory
Operating system (OS)
Optical computers
Optical disc drive
Optical disc drive (ODD)
Palmtop computer
Neuralink: Next Big Tech?
PCI Express (Peripheral Component Interconnect Express)
PCI-X, short for PCI-eXtended
Personal Computers (PC)
Personal Digital Assistant (PDA)
Photolithographed semiconductors
Programmable read-only memory (PROM)
Programming language
PSU (power supply unit)
Quantum computer vs Chemical computer
RAID (redundant array of independent disks)
Random-access memory or RAM
Read-only memory or ROM
Register machine vs Stack machine
Remote computer access
Scalar processor vs Vector processor
SIMM, or single in-line memory module
Solid State Drive (SSD)
Spintronics based computer
Static random-access memory (SRAM)
Super Computers
Synchronous dynamic random access memory (SDRAM)
Teleprinter
Ternary computers
Video Graphics Array (VGA) connector
Wearable computer
Virtual Reality
This is all about latest and best presentation topics for computer science and applications studies.
You’ll also like to READ:
Share with friends
404 Not found

51 Latest Seminar Topics for Computer Science Engineering (CSE)
Looking for seminar topics on Computer Science Engineering (CSE)?
This blog will help you identify the most trending and latest seminar topics for CSE.
Computer Science Engineering, among all other engineering courses, is the recent trend among students passing 12th board exams. It is an academic program that encompasses broad topics related to computer application and computer science.
A CSE curriculum comprises many computational subjects, including various programming languages, algorithms, cryptography, computer applications, software designing, etc.
In the uprising of the technological era, the trend for computer-related courses is in high demand. Courses such as BCA (Bachelors of Computer Application), MCA (Masters of Computer Application), Engineering in Computer Science are specifically designed to train students in the field of Computer Science.
Moreover, various online programs have been developed, and seminars are conducted to help students achieve their goals.
Here, you’ll find the list of seminar topics on Computer Science Engineering (CSE) that will help you to be dedicated and engaged with your computer world.
51 Seminar Topics for Computer Science Engineering (CSE)
What is a Seminar?
A seminar is a form of academic/technical education where participants focus on a specific topic or subject in recurring meetings or single meetings. It helps in achieving essential academic skills and develop critical thinking among the participants.
Check out the latest collection of seminar topics for CSE, latest technical CSE MCA IT seminar topics, recent essay topics, speech ideas, dissertation, thesis, IEEE and MCA seminar topics for BTech, MTech, BCA, and MCA Students.
Finger Print Authentication
Fingerprints are the most common means of authenticating biometrics—the distinctive attribute and pattern of a fingerprint consist of lines and spaces.
Big Data Analysis for Customer Behaviour
Big data is a discipline that deals with methods of analyzing, collecting information systematically, or otherwise dealing with collections of data that are too large or too complex for conventional device data processing applications.
Interconnection of Computer Networks
In fixing inter-organizational relationships, networks must be interconnected. A parallel machine interconnection network sends information to every desired destination node from every source node.
Parasitic Computing
Parasite computing is a technique in which a computer may execute complex computations in a standard permitted interface with another program.
IT in Space
For the first time from outside space, the experiments were carried out from discovery flybys to controlled flights. As in most others, spatial analysis has also been carried out with powerful computers in broader simulations.
To ship and control their apps, Pixeom uses containers on edge. Pixeom is cloud-agnostic on the tech side. Pixeom is the first cloud service installed in a package and the first service to connect internationally and create an increasing user network and content.
Wireless Local Loop
Wireless local loops are a common concept in a telecommunications network for a method of connectivity that uses a wireless connection to link customers to the local exchange instead of traditional copper cables.
A smart card is a plastic card with a computer chip that stores and transacts data between users. The card data is transmitted through a computer device reader.
Virtual Reality
“Virtual reality is a way for people to visualize, manipulate, and interact with very complex data and computers.” In the last few years, Virtual Reality has brought a lot of popularity among users, also known as Virtual World (VE).
Random Number Generators
This paper tests the Random Number Generator (RNG) based on the hardware used in encryption applications. The paper simulates an algorithm for the random number generator that is fast and efficient, and the function generates a 50% different value.
HTML HyperText Markup Language
HTML is the Hyper-Text Language Markup, also know as labeling language to design and construct web pages. HTML is a hypertext language mixture of Markup, and the hypertext defines the relation between web pages.
Personal Computer and AutoCAD
AutoCAD is a computer-aided technology that can produce numerous sketches and prototypes for several types of designers. AutoCAD is a double-dimensional and three-dimensional modeling software line, and CAD stands for “Computer-Aided Design.”
A Secure Dynamic Multi-keyword Ranked Search Scheme Over Encrypted Cloud Data
This paper proposes a safe, effective, and interactive search scheme that allows for precise multi-keyword searching and dynamic document elimination.
Rover Mission Using JAVA Technology
Nowadays, Java technology is excellent for general computing and GUIs but not ready for control devices such as the Rover program. The project “Golden Gate” aims at using RTSJ JAVA in real-time.
Wavelet Transforms In Colored Image Steganography
Digital Steganography uses the host data to mask information from a human observer in such a manner that it is imperceptible. This map is translated into Wavelet.
Hamming Cut Matching Algorithm
Hamburg Cut Matching Algorithm reduces the time for comparing the irises to the database so that in the case of large datasets, such as the voting method, we can use iris recognition.
Smart Quill
Smart Quill is a device that users will use to enter information in apps by pressing a button on the pen and punching the information they would like to enter. SmartQuill is considerably larger in size than a common fountain pen.
Implementation of CP
This system is ideal for maintaining product information, upgrading the inventory based on sales details, producing sales receipts, periodic sales, inventory reports, etc.
The Freenet network offers an efficient way to store and retrieve anonymous information. The device keeps knowledge anonymous and accessible by using cooperating nodes while being highly scalable, alongside an effective adaptive routing algorithm.
Silent Sound Technology
‘Silent Sound’ is directed at noticing and translating all the lip gestures into sounds that can support people who are losing voices and can call softly without distracting others.
Data Warehousing
Data Warehousing is the method of designing and utilizing a data storage system. A data warehouse is developed by combining several heterogeneous information sources, enabling analytical reporting, organized or ad hoc inquiries, and decision-making.
Wireless Application Protocol
Wireless Application Protocol (WAP) is a technical standard for handheld wireless network connectivity. A WAP browser is a web browser used as a protocol for smart devices like mobile phones.
Tripwire Intrusion System
Open Source Tripwire is a free software protection and data integrity application to track and alert a variety of applications to unique file changes.
Satrack is essentially an acronym of the GPS, i.e., Global Positioning System transmitting signals to the missile launched in orbit.
Quantum Computing
Quantum computation studies quantum computational processes that use quantum mechanical effects specifically, such as overlaying and interlocking, to perform data transactions.
The Hurd comes from the Mach 3.0 kernel of the CMU and uses the simulated control of the memory of Mach and its message transfer facilities.
Futex Technology
Futex technology suites are also a set of many separate subsystems. They need to interact with each other and often share a similar state despite practical differences between these applications.
IP Telephony
IP Telephony today represents a compelling and cost-efficient medium of communication. IP telephony means voice and communication networks, services, and applications alignment and convergence.
Rover Technology
Rover is a framework that facilitates location-based services as well as time-aware, user-aware, and device-aware services. Location computation includes automatic knowledge and facilities optimized depending on the user’s actual location.
Network Management Protocol
A standard protocol for network management is the Simple Network Management Protocol (SNMP). It gathers information from network devices like servers, scanners, hubs, switches, and IP network routers and configures them.
Steganography
Steganography is the art and science in which the presence of secret contact may be concealed. It is meant to mask/hide information and writing.
ZigBee Technolgy
ZigBee is a wireless technology for control and sensor network applications. It describes a series for low-data short-range wireless networking connectivity protocols.
Asynchronous Transfer Mode
ATM is a telecommunications network switching strategy that utilizes multifunctional asynchronous time parts to encode data through tiny fixed cells.
Wireless USB
The first high-speed personal wireless link is the Wireless USB. Wireless USB builds on wired USB performance and takes USB technology to the future for wireless.
Intrusion Detection Systems
An intrusion detection (IDS) system is a computer or program that detects malicious behaviors or policy breaches on a network or networks. Either an administrator records any observed activity or breach.
Graphics Processing Unit
A GPU is a specially designed microprocessor for 3D graphics processing. The processor is designed with integrated transforming, illumination, triangles, and motors that handle millions of mathematics.
Extreme Programming
Extreme Programming (XP) is also a deliberate and structured software creation strategy. The solution is designed to provide customers with the software as per the requirements.
Human-Computer Interface
The Human-Computer Interface (HCI) addresses the means of communicating between machines and people. The development of GUI software makes devices more comfortable to use.
3-D Password for More Secure Authentication
There are also vulnerabilities in modern authentication schemes. Users use textual codes that do not meet their specifications. In dictionaries, users prefer to use meaningful terms, making word passwords easy to crack and susceptible to a dictionary or brutal attacks.
Synchronization Markup Language
The popularity of mobile devices and computers will rely on their ability to provide users with information when appropriate.
Graph-Based Search Engine
The search engine is a great tool to search the World Wide Web for any details. In the WWV, every attempt is made to identify the most important findings during the vast digital library search.
Peer-to-Peer Systems: The Present and the Future
Today, peer-to-peer (P2P) networks have been a central component of the Internet, with millions of people accessing their mechanisms and utilities. An academic study that joined researchers from networks, networking, and philosophy is pace up by peer-to-peer systems’ popularity.
Big Enterprise Data
There has been an influx of data in our world. Companies collect trillions of bytes of information about their clients, vendors, and activities. Millions of networked sensors in mobile and industrial products, measuring, processing, and exchanging data, are distributed in the real world.
Ambient Intelligence
Ambient Intelligence refers to an exciting modern informatics model where individuals are activated by a digital environment that is responsive and sensitive to their own desires, behaviors, movements, and emotions.
Google Glass
Project Glass is a Google research and development initiative to develop a head-mounted monitor with increased realism (HMD). The goal of the Project Glass products was to view information currently accessible to most mobile users hands-free and to allow for contact with the Internet through natural voice commands.
Cryptography – Advanced Network Security
Since the foray arrived, technology is on the rise. New and creative innovations have been invented in all manner of networks worldwide. Security treatments are more widespread now, leaving the network unstable and insecure with these sophisticated technologies.
Network Media & 3D Internet
3D Internet, a robust digital medium to meet customers, corporate clients, co-workers, partners, and students, are also known as virtual environments. It blends the TV’s instantaneity, the flexible Online material, and the capabilities of social networking platforms such as Facebook.
CORBA Technology
CORBA is the world’s leading middleware solution that enables knowledge sharing, regardless of hardware architectures, language programs, and operating systems. CORBA is basically an Object Request Broker (ORB) interface specification.
Digital Image Processing
We may upgrade digital image processing by incorporating image modification, image scaling cuts, noise reduction, unwanted features, image compression, image fusion, and color adjustments.
Wearable Computing
It refers to computerized equipment or appliances, like garments, watches, lenses, shoes, and similar articles worn by a person are caller wearables. These devices may have unique and special characteristics, such as BP monitoring, heart rate monitoring, etc.
DAROC Technology
DAROC is intended to create an atmosphere for programming that helps undergraduate and graduate students develop an understanding and expertise with distributed programming applications.
General Seminar Topics on Computer Science Engineering (CSE)
- Cellular Digital Packet Data
- Chameleon Chip
- Cisco IOS Firewall.
- Compact peripheral component interconnect
- Computer Clothing.
- Content Management System
- Controller Area Network
- corDECT Wireless in Local Loop System
- Crusoe Processor.
- Delay-Tolerant Networks
- Digital Audio Broadcasting
- Digital Light Processing
- Digital Subscriber Line
- Digital Theatre System
- Digital Watermarking
- Dynamic Distributed Intrusion Detection Systems
- efficeon processor
- E-Intelligence.
- Elastic Quotas
- Electronic Ink
- Embedded System in Automobiles.
- EPICS-Electromechanical Human-machine interaction
- Cluster Computing
- Google Driver Less Car
- Cloud Storage
- Security and Privacy in Social Networks
- Optical Storage Technology
- 3D Optical Storage Technology
- Web Image Re-Ranking Using Query-Specific Semantic Signatures
- Semantic Web
- Big Data To Avoid Weather-related Flight Delays
- Electronic Paper Display
- RFID Based Library Management System
- Solid Waste Management
- Touchless Touchscreen Technology
- i-Twin Limitless Pendrive Technology
- Internet Of Things IOT Based Intelligent Bin for Smart Cities
- Scram Jet Engine for Hypersonic Flight
- Clinical Information System
- Clinic Management System
- Internet Of Things IoT
- Patient Monitoring System
- Patient Monitoring System || Patient Monitoring System Using Zigbee || Patient Monitoring System With SMS || IP Based Patient Monitoring System || GSM Based Patient Monitoring System || Wireless Patient Monitoring System || Remote Patient Monitoring System ||
- Network Security And Cryptography
- Ambient Backscatter
- Buck Boost Converter
The Final Takeaway!
In this article, we’ve listed the best trending and latest seminar topics for Computer Science Engineering (CSE). These are not the only limited topics available; however, the list has been curated based on the computer world’s latest trend.
If you feel like adding anything here or ask any related queries, please let us know in the comment box below.
Cheers to Computer Engineering!
Related Posts
5 best online compilers, list of biggest and popular programming contests, top 5 programming languages that are in demand by employers, top 10 programmers in the world of all time, leave a comment cancel reply.
Your email address will not be published. Required fields are marked *

- Privacy Policy
- Affiliate Disclosure
Exam Success
Latest Technical Seminar Topics For CSE 2023
If you are a computer science engineering student looking for the latest technical seminar topics for CSE? If yes, then you’re in the right place. Here in this post, we have compiled a list of the latest computer science engineering seminar topics for computer science engineering students.
This CSE seminar topics list will help you to choose the right technical seminar topics according to your area of interest in the subject for presentation.
These computer science latest seminar topics include a wide area of technology such as Artificial Intelligence, Data Science , Machine Learning , Programming Languages, Recent trends which are happening in information technology industries, etc.
Here in this post, we have collected a list of the latest 250 computer engineering seminar topics for computer science engineering degree and diploma course students. You can use these topics for seminars and projects in computer science . Do share this list of the latest seminar topics with your friends. Let’s look at this list of seminar topics.
List of Latest Technical Seminar Topics For CSE 2023
- 5G Wireless Technology
- 3d Searching
- 5 Pen PC Technology
- Advanced Queue Management Techniques
- Advanced Encryption Standard
- Advanced Web Development Techniques
- Amoeba: Distributed Operating System
- Artificial Neural Network (Ann)
- Artificial Intelligence In Machines
- Artificial Intelligence For Speech Recognition
- Artificial Passenger: CSE seminar topics
- Artificial Immune System
- Apache – Spam Assassin
- Aqua Communication Using Modem
- Autonomic Computing
- Aspect-Oriented Programming (AOP)
- Augmented Reality
- Automatic Number Plate Recognition
- Bandwidth Recycling
- Biometrics In Secure E-Transaction
- Bimolecular Computers
- Bit Computing
- Biometric Voting System
- Bluejacking
- Bluetooth-Based Smart Sensor Networks
- Broadband Via Satellite To Rural Areas
- Brain Gate Technology
- Cellular Technologies And Security
- Chameleon Chip
- Cluster Computing
- Cloud Computing
- Cognitive Computing Using IBM Watson
- Computational Visual Attention Systems
- Computer Clothing
- Computerized Paper Evaluation Using Neural Network
- Computational Intelligence In Wireless Sensor Networks
- Compute Unified Device Architecture (CUDA)
- Controller Area Network
- Cordect Wireless In Local Loop System
- Connectors In Software Architectures
- Crusoe Processor
- Cryogenic Processor
- Data Mining
- Database Management System (DBMS)
- Datagram Congestion Control Protocol (DCCP)
- Design And Implementation Of A Wireless Remote
- Diamond Chip
- Digital Jewelry – A Wearable Electronic Device
- Distributed Database Management System
- Distributed Operating Systems
- Distributed Interactive Virtual Environment
- Digital Media Broadcasting
- Digital Scent Technology
- Direct Memory Access (DMA)
- Direct Access File System
- Digital Watermarking
- DNA Computing
- DNA Computing In Security
- DNS Security
- Distributed Virtual Disks
- Dynamic Resource Allocation In Grid Computing
- Dynamic TCP Connecting Elapsing
- E Cash Payment Systems
- Electronic Waste (E-Waste)
- E-Paper Technology
- Efficeon Processor: seminar topics for cse
- Emerging Trends In Robotics Using Neural Networks
- E-Mine: A Novel Web Mining Approach
- Encrypted Hard Disks
- Encrypted Text Chat Using Bluetooth
- Ethernet Passive Optical Network
- Ethical Hacking
- Extensible Markup Language (XML)
- Extensible Stylesheet Language
- Eye Movement-Based Human-Computer Interaction Techniques
- Face Detection Technology
- Ferroelectric Ram (Fram)
- Fiber-Distributed Data Interface
- Fingerprint Recognition System By Neural Networks
- Fluorescent Multilayer Optical Data Storage
- Fog Computing
- Free Space Laser Communications
- Generic Access Network
- Generic Visual Perception Processor (GVPP)
- Gi-Fi Technology
- Green Computing
- Gigabit Networking
- Graphical Password Authentication
- Grating Light Valve Display Technology
- Holographic Data Storage
- Human Area Network Technology
- Hi-Fi Technology
- Holographic Versatile Disc (HVD)
- Hyper Transport Technology
- Idma – The Future Of Wireless Technology
- I Mode Technology: seminar topics for computer science
- Iboc Technology
- Intel Centrino Mobile Technology
- Intelligent Ram
- Intelligent Cache System
- Intrusion Detection System (IDS)
- Internet Of Things (IOT)
- Internet Protocol Television
- Internet Protocol Next Generation (IPNG)
- Integrated Services Digital Network (ISDN)
- Integrated Voice And Data Network
- IP Spoofing
- Ipv6-The Next Generation Protocol
- Inverse Multiplexing
- Java Server Pages Standard Tag Library (JSTL)
- Java Management Extensions (JMX)
- JINI Technology
- Jiro Java-Based Technology
- Juxtaposed (JXTA)
- Lamp Technology
- Lightweight Directory Access Protocol (LDAP)
- Li-Fi Technology
- Location-Aware Computing
- Local Multipoint Distribution Service
- Location Dependent Query Processing
- Low Energy Efficient Wireless Communication Network Design
- Magnetoresistive Random Access Memory (M-Ram)
- Machine Learning
- Membrane Computing
- Meteor Burst Communication
- Microsoft Hololens
- Microsoft Transaction Server
- Middleware For Wireless Sensor Networks
- Money Pad The Future Wallet
- Mobile Adhoc Network (Manet)
- Mobile Ad Hoc Network Routing Protocols And Applications
- Mobile Ad-Hoc Networks Extensions To Zone Routing Protocol
- Security Aspects In Mobile Ad Hoc Network (MANET)
- Mobile Agent
- Mobile Jammer: seminar topics for cse
- Mobile Computing Technology
- Mobile Computing Framework
- Mobile Infrastructure Management
- Modular Computing
- Multi-Protocol Label Switching (MPLS)
- Multithreading Microprocessors
- Multilingual Search Engines
- Multiple Domain Orientation
- Nano-Ram: cse seminar topics
- Nano Computing
- Nano Robotics
- Natural Language Processing
- Network Address Translation
- Network Intrusion Detection System
- Network Attached Storage
- Network Custody System
- New Trends In Cryptography
- Next-Generation Secure Computing Base (NGSCB)
- Nvidia Tesla Personal Supercomputer
- Online Analytical Processing (OLAP)
- Online Temperature Monitoring Of Power Distribution Equipment
- Optical Burst Switching
- Optical Data Security
- Optical Computing
- Optical Packet Switching Network
- Optical Free Space Communication
- Open Ran Network
- Open Graphics Library (Open Gl)
- Open Shortest Path First Protocol (OSPF)
- Parallel Computing
- Parallel Computer Architecture
- Parasitic Computing
- Pervasive Computing
- Packet Sniffers
- Parallel Virtual Machine
- Palm Operating System
- Palm Vein Technology
- Personal Digital Assistant
- Performance Of Motes In Wireless Sensor
- Personal Haptic Interface Mechanism (PHANToM)
- Plagiarism Detection Techniques
- Programming Using Mono Software
- Privacy-Preserving Data Mining
- Public Key Infrastructure
- Quantum Computing
- Quantum Cryptography
- Qos For Multimedia In Wireless Networks
- Rapid Prototyping
- Real-Time Task Scheduling
- Resilient Packet Ring Technology
- Rtos Operating System Seminar Topic
- Real-Time Remote Control Architecture Using Mobile Communication
- Recent Advances In Photonic Devices For Optical Computing
- Recent Trends In Information Technology
- Remote Method Invocation (RMI)
- Semantic Web – A New Trend In Data Warehousing
- Security And Privacy In Social Networks
- Security Challenges In Internet Of Things
- Security And Privacy In Wireless LAN
- Security Issues In Mobile Ad Hoc Networks
- Session Initiation Protocol (SIP)
- Secure Socket Layer
- Secure ATM By Image Processing
- Semantic Digital Library
- Simple Object Access Protocol (SOAP)
- Single Photo Emission Computerized Tomography (SPECT)
- Simple Inexpensive Mobile Computer (Simputer)
- Smart Pixel Arrays: seminar topics for cse
- Small Computer System Interface
- Smart Card-Based Prepaid Electricity System
- Smart Client Application Development Using .Net
- Social Impacts Of Information Technology
- Socks – Protocol (Proxy Server)
- Spatial Information System For Emergency
- Specialized Structured Svms In Computer Vision
- Speech Application Language Technology
- Srec – Network Security
- Storage Area Network (SAN)
- Strata Flash Memory
- Survivable Networks Systems
- Synchronous Optical Networking
- Swarm Intelligence And Traffic Safety
- Tactile Interfaces For Small Touch Screen
- Tcpa / Palladium: seminar topics for computer engineering
- The Qnx Real-Time Operating System
- The Tiger SHARC Processor
- Thin Client/Server Computing Model
- Tizen Operating System – One OS For Everything
- Touchless Touchscreen Technology
- Trustworthy Computing
- Transient Stability Assessment Using Neural Networks
- Ubiquitous Computing
- Voice Morphing
- Virtual Keyboard Typing
- Virtual Network Computing
- Virtual Lan Technology
- Virtual Reality Modelling Language (VRML)
- Voice Over Internet Protocol (VOIP)
- Web Technology: CSE seminar topics
- Wibree Technology (Baby Bluetooth)
- Wireless Mark-up Language (WML)
- Wireless Personal Area Network (WPAN)
- Wireless Networked Digital Devices
- Wireless LAN Security
- Worldwide Interoperability For Microwave Access (WIMAX)
- XML Encryption
- Yii Php Framework
- Zettabyte Filesystem
- Zigbee Technology
- Zig Bee Communication Protocol
Final Words
I hope you all like this list of the latest computer engineering seminar topics for computer engineering students. In this way, you can easily select seminar topics from the list as per your interest in the subject.
Also, If you need some latest computer science seminar topics or project topics, then do let us know via the comment below, so I will provide some best computer science seminar topics for you.
Related Posts: –
- Latest Information Technology Seminar Topics [2023]
- 100+ Best Computer Science Projects Topics [2023]
- Top 175+ Software Engineering Project Topics [2023]
Related Posts

1000+ Best General Seminar Topics for Presentation [Updated 2023]
August 25, 2020 September 10, 2023

Latest Agronomy Seminar Topics 2023
August 21, 2020 April 2, 2023

Latest Agriculture Seminar Topics 2023
August 19, 2020 April 2, 2023
Leave a Reply Cancel reply
Your email address will not be published. Required fields are marked *
Save my name, email, and website in this browser for the next time I comment.

- E & C ENGG
- JAVA PROGRAMS
- PHP PROGRAMS
- ARTIFICIAL INTELLIGENCE
- CLOUD COMPUTING
- WIRELESS TECHNOLOGY
Paper Presentation Topics for Computer Science Engineering
- by Ravi Bandakkanavar
- April 14, 2024
We bring you the latest Paper Presentation Topics for Computer Science Engineering. Click on the topic name to read in detail. These topics give an idea of what topic to choose and what information needs to be included as part of a technical paper. Technical papers have been written in a standard format. You can contact us for more details.
- Artificial Intelligence in Machines
- Automatic number plate recognition
- Autonomic Computing
- How to develop Large language models like GPTz, BERT, Gemini
- Blue eyes technology
- Brain-controlled car for the disabled using artificial intelligence
- Braingate technology
- Brain port device
- Brain Computer Interface (BCI)
- 5G Wireless Technology
- Applications of 5G Technology: How can it Revolutionize Industry?
- 5G: Application of Future Information Era
- Cluster computing
- Cloud Computing and cloud services
- Augmented Reality vs Virtual Reality
- Blockchain Technology and its Applications
- Cyber Crime and Security
- Cybersecurity in the Education System
- Cryptography and its Applications
- Distributed and Parallel Computing
- Detection of digital photo image forgery

- Detection of Reviews using sentiment analysis
- Deploying a wireless sensor network on an active volcano
- Digital jewelry
- Data Mining and Predictive Analytics
- Electronic waste (e-waste)
- Electronic nose
- Embedded web server for remote access
- Innovations of Artificial Intelligence in the healthcare sector
- Face detection and recognition technology
- Location-based services through GPS
- How does the Internet work?
- Hadoop Technology
- Internet of Things and its Impact on Society
- Intrusion detection and avoidance system
- Mobile ad hoc network
- Mobile Ad Hoc Network Routing Protocols and Applications
- Nanocomputing
- Nano Ring Memory
- Nanotechnology and applications
- Night Vision Technology
- Open Source Technology
- Anti-satellite weapons (ASAT) Technology
10 Innovative Tech Trends Expected in 2024
- Parasitic computing
- Polymer Memory
- Radio Frequency Identification Technology
- Electronic Document Management System
- Benefits of Continuous Testing
- Humanoid Robots
- Secured web portal for online shopping
- Securing underwater wireless communication networks
- Security requirements in wireless sensor networks
- Security threats on the World Wide Web
- Security aspects in mobile ad hoc networks (MANETs)
- Semantic web
- Sensitive skin
- Snake robot the future of agile motion
- Software-defined radio (SDR)
- Super efficient motors: technical overview
- Surface-conduction Electron-emitter Display (SED)
- Synchronous Optical Networking
- Transient stability assessment using neural networks
- Transient Stability Assessment using Neural Networks
- Trusted Network Connect (TNC) Specifications
- Ubiquitous computing
- Uniprocessor Virtual Memory Without TLBS
- Vertical Cavity Surface Emitting Laser
- Virtual Network Computing
- Virtual Reality
- Watermarking Digital Audio
- Wireless integrated network sensors
- Wearable Computers
- Wearable Biosensors
Artificial Intelligence Topics for Presentation
I have tried to list out some of the trending topics here. I am sure there are hundreds of new technologies evolving every other day. If you come across any new technology, you are most welcome to share it with everyone here.
- Click to share on Twitter (Opens in new window)
- Click to share on Facebook (Opens in new window)
- Click to share on LinkedIn (Opens in new window)
- Click to share on Pinterest (Opens in new window)
- Click to share on Pocket (Opens in new window)
123 thoughts on “Paper Presentation Topics for Computer Science Engineering”
Hi sir I’m computer Engineering 4 sem student I want to do project so suggest me the topic for ppt
plz suggest me unique topics for presentation .
Hi sir I am Rakshata cse 3rd year sit can you suggest me about project
Are you looking for web applications?
Did it help? Would you like to express? Cancel reply
Presentory for Windows
Presentory for mac, presentory online.
Rebrand your approach to conveying ideas.
Differentiate your classroom and engage everyone with the power of AI.
Knowledge Sharing
Create inspiring, fun, and meaningful hybrid learning experiences
Create with AI
- AI Tools Tips
Presentation Ideas
- Presentation Topics
- Presentation Elements
- Presentation Software
- PowerPoint Tips
Presentation Templates
- Template Sites
- Template Themes
- Design Ideas
Use Presentory Better
- Creator Hub
More Details
- Basic Knowledge
- Creative Skills
- Inspirational Ideas
Find More Answers
- LOG IN SIGN UP FOR FREE
- Hot Paper Presentation Topics For CSE
- 10 Unique PowerPoint Design Ideas to Captivate Your Audience
- Mastering Business Presentation Skills for Success (Innovative Business Presentation Ideas Updated)
- Creative 8 New Year Presentation Ideas with PowerPoint Themes
- Crafting an Effective PowerPoint Front Page Design for Maximum Impact
- Mastering PESTEL Analysis with PowerPoint: Guide and Templates
- Highlighting The Important Components of Real Estate PowerPoint and How to Make One
- Designing A Sales Plan Presentation for PowerPoint - An Overview of All Details
- Best Presentation Themes to Engage Your Audience in 2023
- Best Presentation Topics for Engineering Students
- 5 Engaging Presentation Topics for University Students
- 10 Interesting Presentation Topics for Students That Will Help You Shine
- Intriguing Topics for Engaging Computer Science Presentations
- Best 10 Selected Current Topics for Presentation to All Audience
- Elevate Your Skills: Best Topics for Presentation in English
- Top MBA Presentation Ideas To Elevate Your MBA Education
- Full Guide About Best ESL Presentation Topics for Students
- A Complete Guide to Create Company Profile PowerPoint Presentation With Templates
Are you searching for paper presentation topics for CSE ? Computer science and engineering is a rapidly emerging field. The latest developments and up-to-date information gain more attention there. That’s why selecting a hot topic boosts academic and professional growth. Presenting such topics elevates networking opportunities and attracts industry experts. Thus, it results in internships or job opportunities.
Moreover, presenting a hot topic can set you apart from your peers. If you aim to publish your paper, addressing current work trends is essential. Keeping in view the importance of technical paper presentation topics for CSE . In this article, we will explore innovative and creative solutions. This paper will discuss top trending topics and presentation ideas.
In this article
- Trending Topics in CSE Presentation
- Presentation Ideas for CSE Students
- Best Presentation Software – Presentory, Making our CSE Presentation Appealing
Part 1. Trending Topics in CSE Presentation
Imagine having an older smartphone without the latest updates of 2023. It is the same as the CSE field without tech revolutions and transformation. Staying up-to-date is the only secret to success in computer science and engineering. Moreover, students choose a career or a professional trying to be market-competitive. Read further to know some impactful CSE presentation topics .
1. Artificial Intelligence
The current most advancing area of CSE is Artificial Intelligence. It refers to the ability of computer-based systems to perform human-like functions and is designed to work like human cognition. AI programs are based on machine learning and deep learning systems. Thus, make a presentation introducing AI and its application in daily life areas.
Later on, discuss expected advancements in those aspects. So, further plans can be prepared and implemented according to your research information. You can also shed light on the potential use of AI in diagnosis and treatments. Also, explore algorithm trading or fraud detection in finance. Moreover, you can discuss how AI in self-driving vehicles can reduce manual labor and risk management.
2. Edge Computing
Edge computing is a turning computing paradigm that involves networks near users. Edge refers to processing data at high speed and bringing it closer to where it is generated. Some of its possible components include edge devices, on-premises infrastructure, and network edge. You can use this PPT topic for CSE students and discover its useful applications.
For instance, discuss the combination of AI and edge computing for city development and traffic management. Moreover, you can examine its role in IoT (Internet of Things) and highlight intelligent devices. Also, explore its role in optimizing manufacturing and quality controls. Above all, guide students on how 5G networks and edge computing enable low latency services.
3. Quantum Computing
An area of computer science that is based on quantum theory. This technology uses the law of mechanics to solve problems of classic computers. Quantum algorithms use new approaches and create multidimensional computational spaces. For your update, Google and Microsoft are developing their quantum computers. You can discuss their claims and implications.
Moreover, elaborate cloud-based quantum and its accessibility to developers. Also, highlight challenges in quantum error correction code to make it more reliable. Furthermore, you can explain the principles of quantum cryptography, including Quantum Key Distribution (QKD).
4. Robotics
It's a branch of CSE that includes robot design, conception, operation, and manufacture. It contains 3 fundamental parts: software, electrical, and mechanical. According to some predictions, 20 million manufacturing jobs will be lost by 2030. In this regard, robotics plays a vital role and sets an automated future. So, many types of robots can be discussed in the presentation paper.
Moreover, you can incorporate AI-supported robotic systems that include machine learning and deep learning in the CSE presentation topic . You can also introduce the use of robotic drones in crop monitoring and harvesting. Also, discuss potential applications in pollution clean-up and robotics surgeries.
5. Cybersecurity
In simple terms, cybersecurity is concerned with protecting digital and computer-based systems. Professionals usually aim to protect the data of companies and software from threats. Statistics show cybersecurity careers have grown 37% in the recent decade. In your presentation, you can cover password-based authentication and biometric authentication.
Furthermore, it explores implementations of the zero-trust security model. Highlight the impact of ransomware attacks and strategies to recover for organizations. Also, you can address security challenges in voting systems. Plus, it emphasizes the importance of blockchain technology and consensus algorithms. Moreover, it can be strongly used in securing mobile applications.
6. Bioinformatics
Bioinformatics refers to storing, interpreting, and analyzing biological data by computer technology. Computational methods, software tools, and algorithms are used to understand genetic variations. Protein structures and DNA structures are also studied by it. Thus, there are a variety of topics to be discussed under bioinformatics.
Highlight personalized medicine field and genomics data of patients for treatment plans. Moreover, it combines AI and deep learning to detect disease and its biomarkers. However, CSE in bioinformatics involves data mining, sequence alignment, genome assembly, etc.

7. Cloud Computing
It refers to a situation where computing is done on the cloud rather than a desktop or portable device. It includes managing, storing, and accessing data from remote servers. For instance, Google launched App Engines as its cloud computing. There are public, private, and hybrid modes of cloud computing. It has become an integral part of computing that supports applications.
You can explore serverless computing, its development, and its benefits in your presentation. Also, one can discuss multi-cloud management tools and simplify its resources. Moreover, you can convey the cost optimization issues and plan cloud cost monitoring. Cloud services are also closely related to 5G technology. In addition, developers can merge edge computing and IoT to provide mobile services with speed.
8. Secured Web Portal for Online Shopping
Web portals are immensely used for shopping for products. It enables a single platform to core services and content. To ensure the privacy of financial information, secure web portals are essential. However, one can utilize blockchain technology for data integrity. Also, MFA technology can be used, such as OTP and biometrics.
Another factor that can be studied is voice activation, such as Alexa and Google Assistant, to tackle security challenges. Furthermore, developers can focus on AI chatbots to protect customers' data. You can also explore Augmented Reality (AR) to examine how they provide secure shopping experiences.
9. Polymer Memory
Plastic memory refers to polymer memory, an emerging concept in CSE. They are used to store memory in devices by using organic polymers. It can be retained and stored in a flexible and environment-friendly way. So, one can introduce this technology along with its working principles. In addition, explore the types of polymers, such as conductive and ferroelectric, in your technical paper presentation topics for CSE.
Furthermore, current obstacles, research, and industry adaptations can be highlighted. Traditional and polymer memory can also be compared regarding cost and benefits. You can also examine commercialization and eco-friendly aspects of it. Plus, the data accessibility, manufacturing costs, and compatibility with devices can be discussed.
10. Screenless Display
Cutting-edge technology to view digital content without any traditional screen is called Screenless Display. It projects information into surroundings or directly into the human eye. In computer science, this technology is revolutionizing the way we interact. For this purpose, AR glasses like Magic Leap are being used. Additionally, working on a Virtual Reality (VR) Headset is going to enhance the gaming experience.
Moreover, you can discuss the Brain-Computer Interfaces (BCIs), which enable thought-controlled devices. Gesture-based interfaces can also be explored that allow digital interaction through body movements. Also, you can teach the project mapping and light-field displays to the students.

Part 2. Presentation Ideas for CSE Students
Nowadays, CSE students are learning about technologies and embracing shining futures. Presentations can play a crucial role in learning and knowledge sharing. In this regard, you have to select a CSE presentation topic that suits your interests and expertise. Below are some creative ideas to brainstorm according to your requirements.
1. Creativity
Technical topics for PPT presentation for CSE that are creative gain audience engagement and interest. However, choose a topic that unleashes your creativity in the project. Students can combine digital art and programming to enhance art experiences. Moreover, you can introduce humanoid robots programmed to perform creative tasks.
You can also discuss how AI can be used in the image recognition of many objects. Furthermore, creative projects at the hackathon can also be presented. It enables you to highlight challenges and innovative coding solutions. By discussing the creative algorithms, the audience can also obtain knowledge and inspiration.
2. Abstraction
Considering your crowd's expertise level, use the abstraction of concepts. Thus, you can break complex data structures into diagrams, graphs, and tables. Moreover, you can visually present the machine learning systems, including the neural networks or clustering algorithms.
Software Defined Networking (SDN) can also be abstracted in neural networks. Also, layers in cybersecurity, digital threats, and encryption can be abstract. So, these kinds of topics prove beneficial in the case of non-technical audiences.
3. Data and Information
For professionals, paper presentation topics for CSE must contain information to deliver. So, select a topic with a background, an introduction, and specific practical methods. Furthermore, data and information are used in many areas, like agriculture, journalism, and health care. For example, AI and data analytics can combine to manage emergency and relief efforts.
Data analytic sensors can also help in personalizing market strategies. Also, data security can be examined in terms of securing transactions. By mixing data and AI, explore the role of data sets used in machine learning training.
4. Algorithms
Algorithms play a vital role in solving problems in various domains. Some of its aspects include algorithm designs, applications, and analysis. Thus, one can explain algorithms like Grover's and Shor's algorithms. Moreover, you can discuss the algorithms in language processing, like machine translation and sentiment analysis.
Also, highlight concepts of routing, online algorithms, and resource allocation. In blockchain technology, Proof of Stake (PoS) and Poof of Work (PoW) algorithms can be explored. You can also explain algorithms designed for distribution and parallel computing.
5. Programming
The heart of computer science engineering is computer programming. However, one can elaborate on code refactoring and secure coding techniques. In addition, discuss concepts like functional programming and Python programming. Also, you can demonstrate TensorFlow, which is a popular machine learning model.
You can also discuss how to utilize Botpress or Dialogflow to create chatbots and discuss integration possibilities. Furthermore, parallelism and concurrency in programming can also be explored in how they relate to multi-processing and multi-threading programming.
6. Internet
Interconnected networks are known as the Internet. Through the internet, people are connected through intricate web servers and data centers. In your presentation, explore an emerging phenomenon like the Internet of Things (IoT). The dark web is another concern of the internet and an upcoming hot topic of the digital age.
Additionally, the fundamentals of internet protocols can be discussed. In addition, internet technologies can be discovered, like HTTP/3 and IPv6. Above all, one can discuss 5G technology, internet models, and applications.
7. Global Impact
Apart from discussing the latest algorithms and programming. One can work on current issues and come up with digital solutions. Highlight a topic that contains global impact, like sustainability or other advancements. Thus, study market trends or challenges and introduce remote job technologies. In the healthcare section, you can discuss the working on telemedicine for underdeveloped regions.
Moreover, you can explore the development of eco-friendly technologies and present global examples. Also, you can explore renewable energy solutions that are more advanced than existing power grids. In addition, brainstorm ideas for electronic recycling that cause worse impacts on health.
Part 3. Best Presentation Software – Presentory, Making Your CSE Presentation Appealing
Despite selecting the best technical paper presentation topics for CSE , making it appealing is also essential. After getting content, people search for PowerPoint templates because presentation templates save time and effort. So, bring a captivating presentation that visually represents data and inspires. In this regard, AI-powered tools are helpful for students and professionals.
Wondershare Presentory is an AI presentation software. It offers AI features to create presentations that capture the viewer’s attention. For presenting the presentation, you can record, create, or livestream videos. It has a user-friendly interface that requires no prior knowledge or skill. Thus, generate a presentation in seconds and deliver it effectively.
Free Download Free Download Try It Online
Key Features
- Create a stunning presentation with polished and innovative templates. Presenters can use templates that suit their topic. Later on, they can change the background of the slides. You can choose meeting rooms or any other color background from the Background options.
- Animate objects and bring life into your presentation. In this tool, there are many slide transitions and animation options. Thus, add emphasis, appear, and exit motion into any object, text, or picture. In this way, key points will be highlighted that you want to keep noticed.
- Surprisingly, this AI tool can generate content by just entering a topic. It will create a structured outline of the presentation. Afterward, the content gets added to slides precisely. Hence, it saves your efforts of hours.
- With built-in AI, you can record or stream your video along with the presentation slides. It allows you to apply makeup and remove blemishes from your face. Also, it enables you to adjust video quality and brightness levels. Moreover, the video can be converted into different layouts.
- This tool contains a cloud service that protects your data. It allows you to collaborate with freedom. You can save your project in the cloud and edit it anytime. Moreover, you can share presentations on any popular platform.
How to Use Presentory and Create CSE Presentation Efficiently
As we have explained, the unique AI features of this AI-powered presentation maker. It contains a user-friendly interface that allows you to generate projects quickly. Read below to get a detailed step-by-step guide on how to use this tool:
Step1 Explore Create with AI Option
After getting Wondershare Presentory on the system, double tap to access its main interface. Then, find "Create With AI" and select this option to explore it.

Step2 Enter the CSE Topic and Get AI Generated Content
From the Presentory AI window, type your topic in the text box named "Type a topic here." Next, hit the "Continue" option after reviewing the outline generated by its AI. Afterward, select a suitable theme from the displayed themes available. Now, press the "Continue" button and wait a few moments.
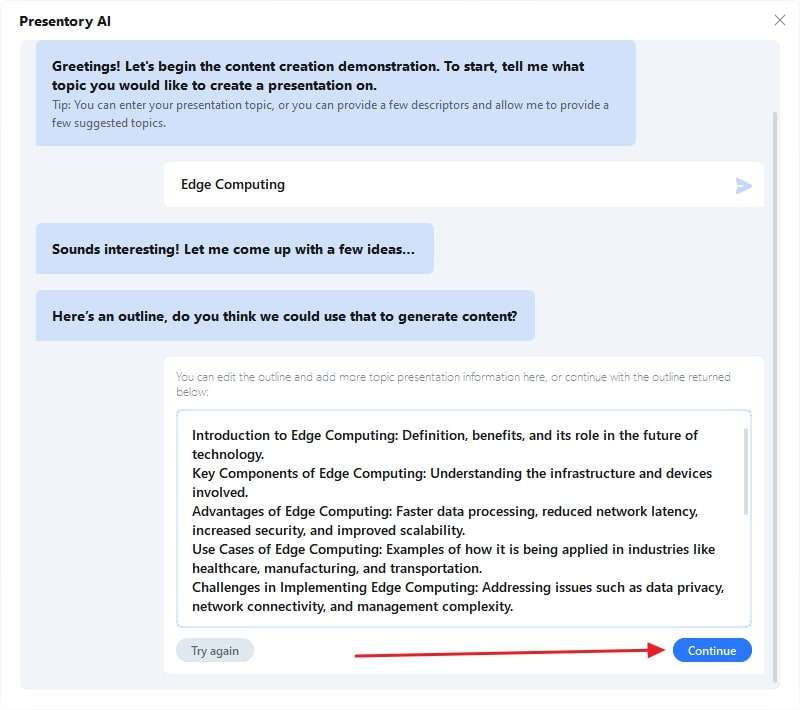
Step3 Insert Animations or Customize as Per Required
With its built-in AI feature, you will get custom-made slides based on your topic and selected theme. To add animations, select the object and tap the "Animation" option at the top-right corner. Select the required animation and set orders of animation in one slide.
From "Resources," choose any sticker or background as needed. After finalizing the presentation, hit the “Project” option in the top bar. There, from the drop-down menu, select “Save Project As”. Then, export the file to your desired location on the device.

Selecting a hot topic for presentation can elevate your growth. CSE students can use topics like computing edge, algorithms, and robotics. Thus, this guide has discussed technical paper presentation topics for CSE . After selecting the topic, getting a tool for impactful presentations is essential.
In this regard, Wondershare Presentory is the most accurate tool for diverse needs. Its AI features can generate content and insert it in attractive templates with one click. Also, you can record videos and change the presentation background. Last but not least, it provides rich resource assets. All in all, it holds all the dynamic features that a presenter looks for.
You May Also Like
- How to Use Slides Changing Remote to Control Presentation from Mobile Devices
Related articles
404 Not found

Top 25 Technical Seminar Topics for CSE and its allied branches with Prepration points
- March 4, 2024

250+ Latest Seminar Topics for CSE 2024
Latest Seminar Topics for CSE (2024) : This page is made for the Engineering students of CSE Branch. It contains a list of Seminar Topics for CSE that are completely of latest technology. These are just the name of Seminar Topics for CSE but it also contains ppt and pdf report so that you can save a lot of your time.
General Topics Non Technical Topics
Mechanical Engineering MCA
Computer Science Electronics
Civil Engineering MBA
Also See: Technical IEEE Seminar Topics for CSE
You can download these Latest Seminar Topics for CSE for free and there is no charge and membership needed to download them.
Latest Seminar Topics for CSE (2024)
Blue brain is project that was found in 2005 and IBM is now working on it to make it possible. The main idea behind this project is that a machine having a same brain like human, that is why is called blue brain or we can say virtual brain. In blue brain, super computers will be used to make an artificial brain. So you will find its complete functionality, need, benefits and advantages disadvantages here.
IP Spoofing
IP Spoofing can be called a method to develop Internet Protocol packets. They equipped with a customized source address either for hiding the sender’s identity or impersonating a different computer system or even both. It is one of the common techniques used for invoking DDoS attacks globally.
Mobile Phone Cloning
Mobile Phone Cloning can be called a process for duplicating the identity of one cell phone to another cell phone. The main purpose behind using this technology is to make fraud calls where the bill is charged from the original cell phone owner.
Bluetooth is called a wireless technology that uses radio waves for transfer data from one device to another. It can be a smartphone, cell phone, tablet, or computer. Nowadays, it is found in millions of products that include speakers, headsets, television, washing machines, and fan among others.
Mobile Computing
Mobile Computing is a technology using which data, voice, and video are transferred from a wireless device without having any fixed connection. The main things that involve in this process are mobile hardware, mobile software, and mobile hardware.
Pill Camera
A pill camera is a tiny camera that designed in the shape of a vitamin pill and used primarily during the endoscopy process. This capsule shape camera takes pictures of the digestive system and sends them to the recorder. It was invented nearly two decades ago during the 1990s by Gavriel Iddan, a popular Israeli inventor.
Human Computer Interface
Human-Computer Interface is a manual interaction performed in designing, executing and assessment processes of a computer system. This type of technology is generally used in all types of disciples where a computer installation is involved. The most well-known platform to perform this process is the Association for Computer Machinery (ACM).
Software Testing
Software Testing is a technology used for tracking the working of a software application. The main motive of this process is to check whether the developed application fulfill the required requirements or not. Also, it finds out the negative issues to ensure the application becomes defect-free.
Phishing is a technique where an attempt to collect personal data is made by using deceptive platforms like websites and emails. Here, the attackers mainly go after login credentials and credit card details. This type of attack has caused devastating results on users in many parts of the world.
Braingate is the technology that defines the connection between computers and the human brain. This system created by Cyber Kinetics in a partnership with the Department of Neuroscience from Brown University. The main component used in this system is computer chip using which brain activity is monitored.
Data Mining
Data Mining is a well-known technique where the user data is extracted from a great sort of raw data. This process consists of data patterns analyzing with the help of software. There are lots of professions where this process is used, including science and research.
3G and WiFi are popular technologies using which people can access the internet. 3G is a third-generation wireless technology, whereas Wi-Fi utilizes the power of radio waves for offering the internet. The biggest difference between these technologies is the range and speed as it stays different for both of them.
Artificial Neural Network can be called a tool that mainly utilized for machine learning. It is basically a brain-inspired system whose main use is to replicate the exact way in which a human body learns. There are both inputs as well as output layers added in this system.
Wireless Sensor Networks (WSN)
Wireless Sensor Network is a self-configured network that doesn’t involve any infrastructure. Despite that, it can effectively monitor tons of physical conditions like vibration, pressure, sound, temperature, and many more. The main component in this network is the sink station that works as an interface between users and the network.
A biochip is basically a cluster of diminished microarrays that are arranged for performing a range of tests simultaneously for boosting speed and throughput. Its surface area is less than a fingernail, but it can perform thousands of biological reactions.
A wireless mesh network is a combination of two or more wireless radios that used together for connecting complete cities using present technology in a cheaper way. It is an emerging technology where the connection is spread across various nodes so that it can be shared across a pretty extended location.
Digital Light Processing
Digital Light Processing is a video technique used in front as well as rear projection units. It is a 3D printing process that is compatible with photopolymers and utilizes conventional light sources. A great advantage of this technique is it creates very accurate components with superior resolution.
Distributed Computing can be defined as a cluster of computer systems that work on a single issue. In this computer approach, the problem is divided into many different components. On top of that, the solution to each part is provided by a variety of computers.
Night Vision Technology
Night Vision is a popular technology that gives a certain vision to the users in complete darkness. It boosts vision in low-light conditions to the users. This type of technology is mainly used in night security, flying, and driving. The main versions of night vision technology are thermal imaging, low-light imaging, and near-infrared illumination.
Wireless Application Protocol
Wireless Application Protocol is defined as a special protocol that created for micro-browsers. The main purpose of this technology is to provide internet in the mobiles. There is a wireless markup language used in this technology instead of HTML.
The 4G Wireless System is the fourth generation technology that provides coverage to a pretty large area with high throughput. It is created to make the system cost-effective along with high spectral efficiency. The main things used in 4G wireless systems are Ultra Wide Radio Band, Millimeter Wireless, and Orthogonal Millimeter Frequency Division Multiplexing.
An Artificial Eye is called a prosthesis that is used for replacing a dead or damaged eye. It was created by scientists for developing a visual prosthesis. That’s why they created a camera that gets interacted with the brain so that the optic nerve can be stimulated.
Asynchronous Chips is the new version of chips providing a great sort of advantage that isn’t possible in the case of synchronous chips. It works at a much higher speed without limiting the chip’s size.
Futex system is used for offering a technique for a program so that userspace code can be enabled in a pretty efficient manner. It let the users synchronize a variety of threads with pretty low involvement of kernel.
Graphics Processing Unit (GPU)
A Graphics Processing Unit can be simply called a single-chip processor whose main job is operating the video and graphics. Its continuous use results in boosting the performance of these two things. The main features of this technology are 3D graphics, digital output, MPEG decoding, YUV color space, rendering polygons, and application support.
Wireless Communication
Wireless Communication is the technology where data or certain information is transferred from one place to another. However, there is no involvement of wires or cables for performing this task. Some major examples of wireless communication are headphones, cellular telephony, wireless home networking, radio receivers, satellite television, and cordless telephones among others.
Agent Oriented Programming
Agent-Oriented Programming can be called a programming paradigm whose main job is to allow the development and programming of intentional agents. The main job of this technology is to offer basic building blocks for creating and implementation intentional agents.
Autonomic Computing
Autonomic Computing is the power of the computer for controlling itself automatically using adaptive systems. It helps the computer users to solve the problems in the system along with other maintenance issues. It is basically a self-managing model that boosts the functioning of computer applications.
GSM (Global System for Mobile Communications)
GSM fully abbreviated as Global System for Mobile Communications is a digital cellular technology using which mobile voice and data services are transmitted. It is one of the most popular and widely accepted standards in the telecommunication world. Nearly 70 % of the globe’s total digital cellular subscribers own GSM technology.
iPhone is one of the world’s most popular smartphones that manufactured by a well-known brand Apple. This device basically combines the features of the digital camera, iPod, computer, and cellular phone with touchscreen ability. According to the latest reports, there are more than 2.5 million apps available to use on this system.
Interferometric Modulator (IMOD)
An Interferometric Modular is a popular technology that consists of subpixels that are miniature Fabry-Perot interferometers in reality. It is mainly used in gaming devices, wrist-worn GPS devices, portable Bluetooth accessories, and cell phone displays.
Microsoft Surface
Microsoft Surface can be called personal computers that come with touchscreen ability and interactive whiteboards. It is created by Microsoft who operates these devices on its windows operating system. It mainly includes 2-in-1 detachable notebooks, hybrid tablets, and interactive whiteboards.
Cryptography and Network Security
Cryptography and Network Security is the analysis of protocols used for preventing hackers from accessing private communication that happens between two people.
Hadoop is an open-source software system that used to store data as well as run applications on different commodity hardware. There is pretty large storage for all types of data along with a great sort of processing power.
5G is a fifth-generation mobile technology whose main motive is to offer a pretty top-level performance when compared with 4G technology. It is the latest evolution of mobile telecommunication that operates with a pretty different approach.
FERROELECTRIC RAM (FRAM)
Ferroelectric RAM can be called a type of random access memory that mixes the quick reading and writing access to dynamic RAM. It is also known with the name of FRAM that mainly competes with Flash technology.
Object Oriented Programming (OOP)
Object-Oriented Programming is a computer language that utilizes the power of objects in programming. The main target of this programming is to apply the real-world entities in the computer world. It binds the data and functions together in such a way that this data doesn’t get accessed by anything other than the function.
Network Topology
Network Topology is describing network arrangement and connection between different nodes schematically. There are lines of connection used in the network topology technology. The main versions of this technology are BUS topology, RING topology, MESH topology, and Star topology.
Project Loon
Project Loon is a project controlled by Google for offering internet solutions in remote areas across the globe. It involved sending hot air balloons to the stratosphere for providing Wi-Fi internet to these parts. It was started in 2011 in California, and since then, it is expanded on a consistent basis.
Storage Area Network (SAN)
A Storage Area Network is a high-speed data transfer technique for giving access to a cluster of servers. It can be simply called a specialized network using which block-level network access can be provided to the storage. It normally includes switches, hosts, storage devices, and storage components.
Hybridoma Technology
Hybridoma is a technology that let the production of MAbs to differentiate fungi species. Apart from that, it discriminates the various components of fungal biomass.
Ribonucleic Acid (RNA)
Ribonucleic Acid is a nucleic acid molecule that looks the same as DNA but comes with ribose instead of deoxyribose. It is created on a DNA template and known mainly with the name of RNA. There is a great role played by this molecule in protein synthesis and other cell activities.
You are at Page 3
PAGE 1 || PAGE 2 || PAGE3 || PAGE4
It was all about Latest Seminar Topics for CSE (2024) . If you liked them then please share them with your friends. Our whole team is always ready to help you if you need seminar of your choice then please comment below. 🙂
58 Comments Already
hadoop ppt nd pdf
Hello Manasa..Your request has been proceeded…we will upload Hadoop ppt and pdf soon 🙂
pdf and ppt for azure service bus(a cloud based messaging system)
we always try to upload the latest seminar including both ppt and pdf….thanks for your cooperation we will get back soon..
i need latest topics for computer science technical seminar.please guide me.
Send me latest ieee based Seminar report and ppt. Thank you
send ppt and report on project loon by google
Can i get some 3d holographic projection seminar topics
Send me a ppt and report on topic femtocells
ppt and pdf on LTE
will i get the ppt n report on wordpress
One of my favorite topic, for sure I will provide you 🙂
ppt and report for child tracking in school bus using gps amd rfid
Hello Bindu, go to this links please https://studymafia.org/global-positioning-system-seminar-pdf-report-and-ppt/
Please provide ppt for ibeacon
pls admin,i need seminar report and ppt on Tablet personal computer
Cool topic bro, will be live soon 🙂
sumit,ppt and report on li-fi
Hello Varun, Go to this link https://studymafia.org/li-fi-technology-seminar-ppt-with-pdf-report/
Sir please i need too 8 th sem latest seminar topic on network please sir immediately send it link please
lovely topics one can consider for workshops
Please Mr Sumit Thakur I need project materials and software on security information system (for national police) asap, please please please
Report for 2G,2.5G and 3g networks
admin please give me any excellent seminar topic for cse and share ppt and report also.
can please someone provide a pdf and ppt on DIGITAL PRESERVATION.plzzzzz
Can you help me to get a seminar topic on SERVICE RELATED APPLICATIONS
can u send me seminar topic on wordpress.
I need too 8 th sem latest seminar topic on network pla send it immediately. new latest seminar easy nd simply seminar
Seminar report on blockchain
thanks for giving us an amazing topic, will surely provide it soon.
Sir, suggest me latest seminar topic 8th sem information science branch
All these topics are for all the semesters.
hello ,pls can u provide some latest seminar topics on latest technology which is not implemented yet,,,,
Then we are not scientists bro 😀
sir please send me link about “Word press” or”Block chain”..
hloo…plz upload ppt and report for mem table
Nothing found on Mem table
sir i want seminar on money pad the future wallet immediately plz with published journal
Hello vic, good topic, will provide it soon to you
please suggest me a latest trending topic on seminar which is also helpful for project. In computer science and systems engineering branch.
please admin, i need a seminar report on (information leakage detection using mobile agent).
please I need seminar material on the roles of computer in career guidance in Nigeria
good day please can i get materials on role of trust management in a distributed network system thanks..
will i get the ppt and report for imap protocol
I WANT PPT FOR BLUE BRAIN & ITWIN
Need ppt and PDF on Bluetooth technology and android . urgent please!!
Hello sir, will I get pdf and report on smart dustbin for smart city.
Can I get ppt n report on “detection and prevention of black holes in MANET” seminar topic
Pls can i get ppt and report on “Quantum cryptography seminar topic
Please i can you add computer securityand Data security
Hi Need Blockchain seminar report Thnx
Hi Can you please upload seminar report on blockchain. If already present please share me the link. Thank you
I need Data-Driven Computing and Caching in 5G Networks: Architecture and Delay Analysis seminar ppt and report. Please send me as early as possible
please send ppt and report on knowledge enabled personalised chatbot for asthma self management
please help me send ppt and pdf seminar topic; Design and computerization of an electronic fund transfer system
Sir please can u help on stock market price prediction based on time series data using arima model sir ?
I Want a ppt for my seminar topic “A Unified Deep Model for Joint Facial Expression Recognition, Face Synthesis, and Face Alignment” ..This is an ieee explore paper..maximum slide is 20..Actually i’m final year engineering student..urgently need ppt for the above topic..can you give me perfect ppt…plzz
i need project topics on cyber security, major on digital forensics
Leave a Reply Cancel reply
Your email address will not be published. Required fields are marked *
This site uses Akismet to reduce spam. Learn how your comment data is processed .
Bits to Bytes, All about Computer Science
Software defined network function.
By decoupling the network functions from the under-laying hardware appliances, NFV provides flexible provisioning of software-based network functionalities on top of an optimally shared physical infrastructure. It addresses the problems of operational costs of managing and controlling these closed and proprietary appliances by leveraging low cost commodity servers.
3D Password
“3D Password” is one of the good seminar topics for computer science technical seminars. Normally the authentication scheme the user undergoes is particularly very lenient or very strict. Throughout the years authentication has been a very interesting approach. With all the means of technology developing, it can be very easy for ‘others’ to fabricate or to steal identity or to hack someone’s password. Therefore many algorithms have come up each with an interesting approach toward calculation of a secret key. The algorithms are such based to pick a random number in the range of 106 and therefore the possibilities of the sane number coming are rare.
An Improved K-means Clustering Algorithm
The traditional K-means algorithm is a widely used clustering algorithm, with a wide range of applications. This ieee seminar paper introduces the idea of the K-means clustering algorithm, analysis the advantages and disadvantages of the traditional K-means clustering algorithm, elaborates the method of improving the K-means clustering algorithm based on improve the initial focal point and determine the K value. Simulation experiments prove that the improved clustering algorithm is not only more stable in clustering process, at the same time, improved clustering algorithm reduces or even avoid the impact of the noise data in the dataset object to ensure that the final clustering result is more accurate and effective.
An atm with an Eye
There is an urgent need for improving security in banking region. With the advent of ATM though banking became a lot easier it even became a lot vulnerable. The chances of misuse of this much hyped ‘insecure’ baby product (ATM) are manifold due to the exponential growth of ‘intelligent’ criminals day by day. ATM systems today use no more than an access card and PIN for identity verification. This situation is unfortunate since tremendous progress has been made in biometric identification techniques, including finger printing, retina scanning, and facial recognition. This IEEE seminar topic proposes the development of a system that integrates facial recognition technology into the identity verification process used in ATMs. The development of such a system would serve to protect consumers and financial institutions alike from fraud and other breaches of security.
“Blue brain” –The name of the world’s first virtual brain. That means a machine that can function as human brain. Today scientists are in research to create an artificial brain that can think, response, take decision, and keep anything in memory. The main aim of this seminar topic is to upload human brain into machine. So that man can think, take decision without any effort. After the death of the body, the virtual brain will act as the man. So, even after the death of a person we will not lose the knowledge, intelligence, personalities, feelings and memories of that man that can be used for the development of the human society. No one has ever understood the complexity of human brain. It is complex than any circuitry in the world. So, question may arise “Is it really possible to create a human brain?” The answer is “Yes”, because whatever man has created today always he has followed the nature. When man does not have a device called computer, it was a big question for all .But today it is possible due to the technology. Technology is growing faster than everything. IBM is now in research to create a virtual brain. It is called “Blue brain “. If possible, this would be the first virtual brain of the world.
Is it possible to create a computer, which can interact with us as we interact each other? For example imagine in a fine morning you walk on to your computer room and switch on your computer, and then it tells you “Hey friend, good morning you seem to be a bad mood today. And then it opens your mail box and shows you some of the mails and tries to cheer you. It seems to be a fiction, but it will be the life lead by “BLUE EYES” in the very near future. The basic idea behind this computer technology is to give the computer the human power. We all have some perceptual abilities. That is we can understand each other’s feelings. For example we can understand ones emotional state by analyzing his facial expression. If we add these perceptual abilities of human to computers would enable computers to work together with human beings as intimate partners. The “BLUE EYES” computer technology aims at creating computational machines that have perceptual and sensory ability like those of human beings.
A captcha is a program that can generate and grade tests that: (A) most humans can pass, but (B) current computer programs can’t pass. Such a program can be used to differentiate humans from computers and has many applications for practical security. This seminar topic
Cloud 9 Technology
“Cloud9” is one of the trending topics for computer science Technical Seminars. This is a new technology in computer science. Cloud9 is a cloud-based testing service that promises to make high-quality testing fast, cheap, and practical. Cloud9 runs on compute utilities like Amazon EC2 [1], and we envision the following three use cases: First, developers can upload their software to Cloud9 and test it swiftly, as part of their development cycle. Second, end users can upload recently downloaded programs or patches and test them before installing, with no upfront cost. Third, Cloud9 can function as a quality certification service, akin to Underwriters Labs [20], by publishing official coverage results for tested applications. In an ideal future, software companies would be required to subject their software to quality validation on such a service, akin to mandatory crash testing of vehicles. In the absence of such certification, software companies could be held liable for damages resulting from bugs. For a software testing service to be viable, it must aim for maximal levels of automation.
Creating enhanced maps
“Creating enhanced maps” is one of the simple topics for computer science Technical Seminars. The concept of enhanced maps (Emaps) was introduced with one main objective: It should characterize roads, first, with more completeness and, second, with more accuracy than standard maps to fulfill the requirements of new challenging road safety applications and advanced driver-assistance systems (ADAS). This technical seminar paper introduces a paradigm for Emap definition and creation on which every road lane is represented and topologically connected to the rest of lanes. Following this approach, a number of Emaps have been created in France, Germany, and Sweden. The experiments carried out in these test sites with the Emaps show the capability of our Emap definition to assist with the determination of the vehicle position at the lane level. Details of the processes of extraction and connection of the road segments are given in the core of this paper, as well as a discussion of the elaboration process and future guidelines in the conclusion.
Silent Sound Technology
‘Silent Sound’ technology aims to notice every movement of the lips and transform them into sounds, which could help people who lose voices to speak, and allow people to make silent calls without bothering others. Rather than making any sounds, your handset would decipher the movements your mouth makes by measuring muscle activity, then convert this into speech that the person on the other end of the call can hear. So, basically, it reads your lips. This new technology will be very helpful whenever a person loses his voice while speaking or allow people to make silent calls without disturbing others, even we can tell our PIN number to a trusted friend or relative without eavesdropping. At the other end, the listener can hear a clear voice. The awesome feature added to this technology is that “it is an instant polyglot” I.E, movements can be immediately transformed into the language of the user’s choice. This translation works for languages like English, French & German. But, for the languages like Chinese, different tones can hold many different meanings. This poses Problem said Wand. He also said that in five or may be in ten years this will Be used in every day’s technology.
SSL and TSL
This subject came into being with the advent of the Internet. There are three basic issues – confidentiality, integrity and availability. When an unauthorized person reads or copies information, it is known as loss of confidentiality. When the information is modified in an irregular manner, it is known as loss of integrity. When the information is erased or becomes inaccessible, it is known as loss of availability. Authentication and authorization are the processes of the Internet security system by which numerous organizations make information available to those who need it and who can be trusted with it. When the means of authentication cannot be refuted later, it is known as non-repudiation. Internet security can be achieved through use of antivirus software, which quarantines or removes malicious software programs. Firewalls can determine which particular websites can be viewed and block deleterious content.
Security and Privacy in Cloud Computing
Recent advances have given rise to the popularity and success of cloud computing. However, when outsourcing the data and business application to a third party causes the security and privacy issues to become a critical concern. Throughout the study at hand, the authors obtain a common goal to provide a comprehensive review of the existing security and privacy issues in cloud environments. We have identified five most representative security and privacy attributes (i.e., confidentiality, integrity, availability, accountability, and privacy-preservability). Beginning with these attributes, we present the relationships among confidentiality, availability and privacy-preservability , the vulnerabilities that may be exploited by attackers, the threat models, as well as existing defense strategies in a cloud scenario. Future research directions are previously determined for each attribute.
E-paper is a revolutionary material that can be used to make next generation; electronic displays. It is portable reusable storage and display medium that look like paper but can be repeatedly written one thousands of times. These displays make the beginning of a new area for battery power information applications such as cell phones, pagers, watches and hand-held computers etc. Two companies are carrying our pioneering works in the field of development of electronic ink and both have developed ingenious methods to produce electronic ink. One is E-ink, a company based at Cambridge, in U.S.A. The other company is Xerox doing research work at the Xerox’s Palo Alto Research Centre. Both technologies being developed commercially for electronically configurable paper like displays rely on microscopic beads that change color in response to the charges on nearby electrodes.
The idea behind EyeOS is that the whole system lives in the web browser. The client must have only a web browser to work with EyeOS and all its applications, including Office and PIM ones. This applies to for both modern and obsolete PC’s An Open Source Platform designed to hold a wide variety of Web Applications. EyeOS was thought of as a new definition of an Operating System, where everything inside it can be accessed from everywhere inside a Network. All you need to do is login into your EyeOS server with a normal Internet Browser, and you have access to your personal desktop, with your applications, documents, music, movies… just like you left it. EyeOS lets you upload your files and work with them no matter where you are. It contains applications like Word Processor, Address Book, PDF reader, and many more developed by the community.
Game Playing in AI
Game playing was one of the first tasks undertaken in Artificial Intelligence. Game theory has its history from 1950, almost from the days when computers became programmable. The very first game that is been tackled in AI is chess. Initiators in the field of game theory in AI were Konard Zuse (the inventor of the first programmable computer and the first programming language), Claude Shannon (the inventor of information theory), Norbert Wiener (the creator of modern control theory), and Alan Turing. Since then, there has been a steady progress in the standard of play, to the point that machines have defeated human champions (although not every time) in chess and backgammon, and are competitive in many other games.
The proposed recognition algorithm classifies the text of a sentence according to the following emotional categories: happiness, sadness, anger, fear, disgust, and surprise. This is one of the trending and new technology in computer science. The proposed algorithm estimates emotional weights for each emotional category (how intense the emotion is) in the form of a numerical vector. The vector is used to determine the dominant emotional type (the emotional type with the highest weight) and the overall emotional valence of a sentence (is the emotion positive, negative, or neutral). If the vector is zero or close to zero, the sentence is considered emotionally neutral. Users of our software may determine their criteria for neutrality. To recognize emotions in sentences, we use a hybrid of a keyword-spotting method and a rule-based method. The keyword-spotting approach is based on the use of a lexicon of words and expressions related to emotions. The main contribution is threefold. First, in order to construct a word lexicon, use of both the power of human judgment and the power of WordNet, a lexical database for English language. Specifically, a survey based word lexicon to automatically search WordNet for all semantic relatives of the initial word set. Second, we take into account “:)”s, “>:O”s, and “ROFL”s through an extensive emoticon lexicon. Third, trying to overcome some of the problems associated with keyword-spotting techniques with several heuristic rules. An argument that the proposed technique is suitable for analyzing fragmented online textual interaction that is abundant in colloquialisms.
Voice Browsers
Browser technology is changing very fast these days and we are moving from the visual paradigm to the voice paradigm. Voice browser is the technology to enter this paradigm. A voice browser is a “device which interprets a (voice) markup language and is capable of generating voice output and/or interpreting voice input, and possibly other input/output modalities. This seminar paper describes the requirements for two forms of character-set grammar, as a matter of preference or implementation; one is more easily read by (most) humans, while the other is geared toward machine generation.
Wireless Body Area Networks
Future communication systems are driven by the concept of being connected any-where at any time. This is not limited to even in medical area. Wireless medical communications assisting peoples work and replacing wires in a hospital are the applying wireless communications in medical healthcare. The increasing use of wireless networks and the constant miniaturization of electrical devices has empowered the development of wireless body area networks(WBANs).In these networks various sensors are attached on clothing or on the body or even implanted under the skin. These devices provide continuous health monitoring and real-time feedback to the user or medical personnel. The wire-less nature of the network and the wide variety of sensors offer numerous new, practical and innovative applications to improve healthcare and the quality of life. The sensor measures certain parameters of human body, either externally or internally. Examples include measuring the heartbeat, body temperature or recording a prolonged electrocardiogram (ECG).
B-Tree File System
The design goal is to work well for a wide variety of workloads, and to maintain performance as the filesystem ages. This is in contrast to storage systems aimed at a particular narrow use case. BTRFS is intended to serve as the default Linux filesystem; it is expected to work well on systems as small as a smartphone, and as large as an enterprise production server. As such, it must work well on a wide range of hardware.
Keyboards Without Keyboards
Input to small devices is becoming an increasingly crucial factor in development for the ever-more powerful embedded market. Speech input promises to become a feasible alternative to tiny keypads, yet its limited reliability, robustness, and flexibility render it unsuitable for certain tasks and/or environments. Various attempts have been made to provide the common keyboard metaphor without the physical keyboard, to build “virtual keyboards”. This promises to leverage our familiarity with the device without incurring the constraints of the bulky physics. This research surveys technologies for alphanumeric input devices and methods with a strong focus on touch-typing. We analyze the characteristics of the keyboard modality and show how they contribute to making it a necessary complement to speech recognition rather than a competitor
A Distributed MAC Design
Wireless USB gives consumers an easy, secure way to connect their PCs, CE, and mobile devices without a cable – without sacrificing speed. Wireless USB enables products from the PC, CE, and mobile industries to connect wirelessly at up to 480 Mbps at 3 meters and 110 Mbps at 10 meters. the requirement of high quality multimedia service in wireless home network environment is more increasing in recent years. WiMedia Alliance has developed the specifications of the PHY, MAC, and convergence layers for UWB (Ultra Wide Band) systems with participation from more than 170 companies.
IMC of Landslide Using LIDAR
Landslide identification and hazard mapping using light detection and ranging (LiDAR) have proven successful in Kentucky and other landslide prone areas of the United States, such as Oregon, Washington, and North Carolina (Burns and Madin, 2009; McKenna and others, 2008; Wooten and others, 2007) . The purpose of this project was to develop a methodology for using LiDAR data to document preexisting landslides in Kenton and Campbell Counties, Kentucky (fig. 1). To do this, potential landslides were mapped and digitized that previously were not visible on existing maps or coarse digital elevation models (DEMs). Field verification of these mapped locations, where possible, also was conducted. Using high-resolution LiDAR to identify potential landslides provides a framework for analyzing landslide data that are crucial to understanding landslide susceptibility and reducing long-term losses.
D-to-D Communications
A common aspect of cellular-assisted and –controlled short-range communications technologies, including the underlay, overlay, or unlicensed spectrum based approaches, is that they rely on the availability and involvement of the cellular infrastructure. By themselves, these technologies do not provide a means for a graceful degradation of connectivity or content access services in case the cellular infrastructure becomes partially or completely damaged or dysfunctional. Ideally, short-range or local communication should be maintained in the absence of infrastructure nodes, but should be able to take advantage of cellular functionality when parts of or the whole infrastructure remains intact.
Deep Learning
In statistical machine learning, a major issue is the selection of an appropriate feature space where input instances have desired properties for solving a particular problem. For example, in the context of supervised learning for binary classification, it is often required that the two classes are separable by a hyper plane. In the case where this property is not directly satisfied in the input space, one is given the possibility to map instances into an intermediate feature space where the classes are linearly separable. This intermediate space cans either be specified explicitly by hand-coded features, be defined implicitly with a so-called kernel function, or be automatically learned. In both of the first cases, it is the user’s responsibility to design the feature space. This can incur a huge cost in terms of computational time or expert knowledge, especially with highly dimensional input spaces, such as when dealing with images.
Graphical Password
The most common computer authentication method is to use alphanumerical usernames and passwords. This method has been shown to have significant drawbacks. For example, users tend to pick passwords that can be easily guessed. On the other hand, if a password is hard to guess, then it is often hard to remember. To address this problem, some researchers have developed authentication methods that use pictures as passwords. Here, we conduct a comprehensive survey of the existing graphical password techniques. We classify these techniques into two categories: recognition-based and recall-based approaches.In this seminar topic we discuss the strengths and limitations of each method and point out the future research directions in this area.
IP Spoofing
IP spoofing is a method of attacking a network in order to gain unauthorised access. The attack is based on the fact that Internet communication between distant computers is routinely handled by routers which find the best route by examining the destination address, but generally ignore the origination address. The origination address is only used by the destination machine when it responds back to the source. In a spoofing attack, the intruder sends messages to a computer indicating that the message has come from a trusted system. To be successful, the intruder must first determine the IP address of a trusted system, and then modify the packet headers to that it appears that the packets are coming from the trusted system.
Mobile WiMax
This is one amongst the latest IEEE seminar topics. This staggering growth of the Internet is driving demand for higher-speed Internet-access services, leading to a parallel growth in broadband adoption. In less than a decade, broadband subscription worldwide has grown from virtually zero to over 200 million. Many industry observers believe so. Before we delve into broadband wireless, let us review the state of broadband access today. Digital subscriber line (DSL) technology, which delivers broadband over twisted-pair telephone wires, and cable modem technology, which delivers over coaxial cable TV plant, is the predominant mass-market broadband access technologies today.
Object Tracking in Video Scenes
Object tracking in video processing follows the segmentation step and is more or less equivalent to the ‘recognition’ step in the image processing. Detection of moving objects in video streams is the first relevant step of information extraction in many computer vision applications, including traffic monitoring, automated remote video surveillance, and people tracking. There are basically three approaches in object tracking. Feature-based methods aim at extracting characteristics such as points, line segments from image sequences, tracking stage is then ensured by a matching procedure at every time instant. Differential methods are based on the optical flow computation, i.e. on the apparent motion in image sequences, under some regularization assumptions. The third class uses the correlation to measure inter-image displacements. Selection of a particular approach largely depends on the domain of the problem.
Optical Computing
Optical computing includes the optical calculation of transforms and optical pattern matching. Emerging technologies also make the optical storage of data a reality. The speed of computers was achieved by miniaturising electronic components to a very small micron-size scale, but they are limited not only by the speed of electrons in matter (Einstein’s principle that signals cannot propagate faster than the speed of light) but also by the increasing density of interconnections necessary to link the electronic gates on microchips. The optical computer comes as a solution of miniaturisation problem. In an optical computer, electrons are replaced by photons, the sub- atomic bits of electromagnetic radiation that make up light..
Optimizing Compiler for CELL Processor
Developed for multimedia and game applications, as well as other numerically intensive workloads, the CELL processor provides support both for highly parallel codes, which have high computation and memory requirements, and for scalar codes, which require fast response time and a full-featured programming environment. This first generation CELL processor implements on a single chip a Power Architecture processor with two levels of cache, and eight attached streaming processors with their own local memories and globally coherent DMA engines. In addition to processor-level parallelism, each processing element has a Single Instruction Multiple Data (SIMD) unit that can process from 2 double precision floating points up to 16 bytes per instruction. This IEEE seminar paper describes, in the context of a research prototype, several compiler techniques that aim at automatically generating high quality codes over a wide range of heterogeneous parallelism available on the CELL processor. Techniques include compiler-supported branch prediction, compiler-assisted instruction fetch, generation of scalar codes on SIMD units, automatic generation of SIMD codes, and data . Results indicate that significant speedup can be achieved with a high level of support from the compiler.
Resource Optimization
“Resource Optimization” is one of the data oriented topics for computer science Technical Seminars. Virtualization addresses IT’s most pressing challenge: the infrastructure sprawl that compels IT departments to channel 70 percent of their budget into maintenance, leaving scant resources for business-building innovation. The difficulty stems from the architecture of today’s X86 computers: they’re designed to run just one operating system and application at a time. As a result, even small data centers have to deploy many servers, each operating at just five percent to 15 percent of capacity—highly inefficient by any standard. Virtualization software solves the problem by enabling several operating systems and applications to run on one physical server or “host.” Each self-contained “virtual machine” is isolated from the others, and uses as much of the host’s computing resources as it requires.
Over the last several years, a loosely defined collection of computer software known as “Spyware” has become the subject of growing public alarm. Computer users are increasingly finding programs on their computers that they did not know were installed and that they cannot uninstall, that create privacy problems and open security holes that can hurt the performance and stability of their systems, and that can lead them to mistakenly believe that these problems are the fault of another application or their Internet provider. The term “spyware” has been applied to everything from keystroke loggers, to advertising applications that track users’ web browsing, to web cookies, to programs designed to help provide security patches directly to users. More recently, there has been particular attention paid to a variety of applications that piggyback on peer-to-peer file-sharing software and other free downloads as a way to gain access to people’s computers. This report focuses primarily on these so-called “adware” and other similar applications, which have increasingly been the focus of legislative and regulatory proposals.
Securing SDN
Software Defined Networking (SDN) is an architectural approach that optimizes and simplifies network operations by more closely binding the interaction (i.e., provisioning, messaging, and alarming) among applications and network services and devices, whether they be real or virtualized. It often is achieved by employing a point of logically centralized network control—which is often realized as an SDN controller—which then orchestrates, mediates, and facilitates communication between applications wishing to interact with network elements and network elements wishing to convey information to those applications. The controller then exposes and abstracts network functions and operations via modern, application-friendly and bidirectional programmatic interfaces.
Digital Mapping
Emerging requirements associated with digital mapping pose a broad set of challenging problems in image understanding research. Currently several leading research centers are pursuing the development of new techniques for automated feature extraction; for example, road tracking, urban scene generation, and edge-based stereo compilation. Concepts for map-guided scene analysis are being defined which will lead to further work in automated techniques for spatial database validation, revision and intensification. This seeks to describe on-going activity in this field and suggest areas for future research. Research problems range from the organization of large-scale digital image/map databases for tasks such as screening and assessment, to structuring spatial knowledge for image analysis tasks, and the development of specialized “expert” analysis components and their integration into automated systems. Significantly, prototype image analysis workstations have been configured for both film-based and digital image exploitation which interface conventional image analysts and extracted spatial data in computer assisted systems. However, the state-of-the-art research capabilities are fragile, and successful concept demonstrations require thoughtful analysis from both the mapping and image understanding communities.
Exterminator
Programs written in C and C++ are susceptible to memory errors,including buffer overflows and dangling pointers. These errors,which can lead to crashes, erroneous execution, and security vulnerabilities, are notoriously costly to repair. Tracking down their location in the source code is difficult, even when the full memory state of the program is available. Once the errors are finally found, fixing them remains challenging: even for critical security-sensitive bugs, the average time between initial reports and the issuance of a patch is nearly one month. We present Exterminator, a system that automatically corrects heap-based memory errors without programmer intervention. Exterminator exploits randomization to pinpoint errors with high precision. From this information, Exterminator derives runtime patches that fix these errors both in current and subsequent executions. In addition, Exterminator enables collaborative bug correction by merging patches generated by multiple users. We present analytical and empirical results that demonstrate Exterminator’s effectiveness at detecting and correcting both injected and real faults.
Fake Access Point Detector
Wireless access points are today popularly used for the convenience of internet use. The growing acceptance of wireless local area networks (WLAN) presented different risks of wireless security attacks. The presence of fake access points is one of the most challenging network security concerns for network administrators. Fake access points, if undetected, can steal sensitive information on the network. Most of the current solutions to detect fake access points are not automated and are dependent on a specific wireless technology. Fake access point is one of the serious threats in wireless local area network. Here we have presented our propose solution to detect fake access point & related risk assessment is analysed .Most of the current approaches to detecting fake access point are rudimentary and easily evaded by hacker. In our solution there is no need of acquire new RF devices for detecting fake access point our solution is designed to work with current infrastructure. Our solution is effective and reliable. It is designed to detect inside attacks in organisation.
Gi-Fi will helps to push wireless communications to faster drive. For many years cables ruled the world. Optical fibers played a dominant role for its higher bit rates and faster transmission. But the installation of cables caused a greater difficulty and thus led to wireless access. The foremost of this is Bluetooth which can cover 9-10mts. Wi-Fi followed it having coverage area of 91mts. No doubt, introduction of Wi-Fi wireless networks has proved a revolutionary solution to “last mile” problem. However, the standard’s original limitations for data exchange rate and range, number of channels, high cost of the infrastructure have not yet made it possible for Wi-Fi to become a total threat to cellular networks on the one hand, and hard-wire networks, on the other. But the man’s continuous quest for even better technology despite the substantial advantages of present technologies led to the introduction of new, more up-to-date standards for data exchange rate i.e., Gi-Fi.
Teradata is an open system, compliant with ANSI standards. It is currently available on UNIX MP-RAS and Windows 2000 operating systems. Teradata is a large database server that accommodates multiple client applications making inquiries against it concurrently. Various client platforms access the database through a TCP-IP connection across an IBM mainframe channel connection. The ability to manage large amounts of data is accomplished using the concept of parallelism, wherein many individual processors perform smaller tasks concurrently to accomplish an operation against a huge repository of data. To date, only parallel architectures can handle databases of this size.
Data transmission, digital transmission or digital communications is the physical transfer of data (a digital bit stream) over a point-to-point or point-to-multipoint communication channel. Examples of such channels are copper wires, optical fibers, wireless communication channels, and storage media. The data is represented as an electromagnetic signal, such as an electrical voltage, radio wave, microwave or infrared signal. For high rate of data transmission we commonly use optical fibers. Optical fibers are widely used in fiber-optic communications, which permits transmission over longer distances and at higher bandwidths (data rates) than other forms of communication. Fibers are used instead of metal wires because signals travel along them with less loss and are also immune to electromagnetic interference. Fibers are also used for illumination, and are wrapped in bundles so they can be used to carry images, thus allowing viewing in tight spaces. But this technology also have many disadvantages such as price, fragility etc.
Xmax is one of the latest seminar topics. Wireless operators today are facing a dilemma. Customers are demanding more and more data applications to be delivered on the go. However, the operator is using scarce expensive licensed spectrum that is overburdened with delivering core voice services. Support for voice, data, location awareness, chat and other applications are required for customers that are very mobile. The operator is facing a choice of acquiring more licensed spectrum (if any is available) or losing customers due to demand for advanced services. xG Technology has a solution to this dilemma of overwhelming demand for advanced applications versus lack of spectrum.
Road characterization of Digital Maps
Here, implementation a novel system to detect, maintain and warn the forthcoming road inconsistencies. In hilly, fog affected and unmaintained areas, vehicles/ motorists are more prone to accidents which have been proved to be fatal in the past. There is insufficient knowledge about the location and type of these inconsistencies as well. Hence, this system provides a two-step solution by eventually warning the motorist about the inconsistency. This is also a self-learning and recursive system which requires less human involvement. The availability of the technologies in the present automobiles is sufficient to create a warning system. But the integration of these technologies inspired the paper to develop the system.
Biometric Electronic Wallet
Bitcoin is an experimental, decentralized digital currency that enables instant payments to anyone, anywhere in the world. Bitcoin uses peer-to-peer technology to operate with no central authority. Wallet is the place where Bitcoins are stored. Once Bitcoin wallet is installed on a computer or mobile phone, it will generate initial Bitcoin address and then the user can create an address for each transaction. Wallet first generates a private key and next it will converts private key to Bitcoin address. Wallet keeps track of private keys, usually by storing them in an encrypted wallet file, either on hard drive, on a server on the Internet, or elsewhere.
HGI with 3D-Environment
Virtual Environment (VE) system offers a natural and intelligent user interface. Hand gesture recognition is more efficient and easier interaction in VE than human-computer interface (HCI) devices like keyboards and mouse. We propose a hand gesture recognition interface that generates commands to control objects directly in a game. Our novel hand gesture recognition system utilizes both Bag-of features and Support Vector Machine (SVM) to realize user-friendly interaction between human and computers. The HCI based on hand gesture recognition interacts with objects in a 3D virtual environment. With this interface, the user can control and direct a helicopter by a set of hand gesture commands controlling the movements of the helicopter. Our system shows the hand gesture recognition interface can attain an enhanced and more intuitive and flexible interaction for the user than other HCI devices.
MAS to Windows Azure Cloud
Schema migration involves the migration of application schema to clouds. Presently various script generation techniques are there which are used for schema migration, which also sometimes require the application architecture to be changed to make it compatible with cloud platform. This paper shows an approach using user templates for capturing the schema structure and access control mechanism for migration of application schema without using script generation tools. Further it gives the necessary algorithm to show the feasibility of its implementation.
In today’s world the Internet has become essential requirement for everyone, everyone wants to remain connected with the world. Many organizations use Wi-Fi to provide access signals to internet and intranet enabling the flexible workforce. In the field of communications, Banking, industry. The users are most frequently using the internet and information transmitted by the users is broadcasted through the air. Every user within the range of Wi-Fi signal can be easily connect the network and sniffed the information using fake access point. Fake AP is an unauthorized access point plugged into a corporate network, posing a serious security threat. In our project we propose the detection of Fake AP and analyzing related risk assessment. Also provide secure and effective communication. WLAN Security technology has major use in many fields. Wireless LAN has a wide range of applications due to its flexibility and easy access. The use of public Wi-Fi has reached at a level that is difficult to avoid. According to the poll conducted by Kaspersky’s global Facebook pages 32 percent of the more than 1600 respondents said that they are using public Wi-Fi regardless of the security concerned.
For more IEEE Technical Seminar topics fill the leave a message form.

- Futuristic seminar ideas
- technical seminar
- technical seminar topics
- technical seminar topics for cse
- Technical Topics
- technology topics for presentation
- Trending Technologies
30+ Technical Seminar Topics for Presentation: Latest Tech Trends
- Share to Facebook
- Share to Twitter

Best Technical Seminar Topics for Presentation: Latest technology trends
Here are 30 emerging technical seminar topics you should consider selecting and adding to your skill set. The links for the PPT presentation for each technical seminar topic are given for your study and reference. You can download them and accordingly draft your own seminar presentation.
1. Cloud Computing
2. Massively Online Open Courses (MOOCs)
3. Software-Defined Networks
4. Quantum Computing
5. Sustainable Materials Management (SMM)
6. Natural User Interfaces
7. Metaverse
8. Information Security
9. 3D Integrated Circuits
10. Artificial Intelligence
11. Universal Memory
12. Blockchain (Cryptocurrency)
13. Computational Biology and Bioinformatics
14. The Internet of Things (IoT)
15. Extended Reality (XR)
16. 5G network
17. Smart Home
18. Distributed Computing
19. Data Mining
20. 3D Printing
21. Medical Robotics
22. Computer Vision and Pattern Recognition
23. Gesture Recognition Technology
24. Machine Learning and Intelligent Systems
25. Big Data and Analytics
26. High-Performance Computing
27. Photonics
28. Sports Technology
29. Nanoelectronics
30. E-Waste
31. Data Security and Privacy
That was all about the latest and most sought-after technical seminar topics that are expected to trend in the year 2024. Hope this comprehensive article provides valuable insights and information that could help you stay up-to-date with the latest technological advancements and innovations.
Also, check out:
- 20 Best Seminar Topics for Computer Science (Updated)
- Seminar Topics on Top 10 Technology Trends for Next Decade
- Latest Mechanical Engineering Seminar Topics (Updated)
- Civil Engineering Seminar Topics
- Electronics and Communication Seminar Topics
- Electrical Engineering Seminar Topics
Share this Article
Subscribe via email, related post.
- Like on Facebook
- Follow on Twitter
- Follow on Slideshare
- Follow on Pinterest
- Subscribe on Youtube
Trending Seminar Topics
- 100+ Seminar Topics for Youth, Teenagers, College Students Young people are on a never-ending quest for transcendence, which drives them to want to improve the environment, countries, communities,...
- 30+ Technical Seminar Topics for Presentation: Latest Tech Trends Technology is rapidly evolving today, allowing for faster change and progress and accelerating the rate of change. However, it is not just t...
- 100 PowerPoint Presentation Topics in Hindi (Download PPT) विद्यार्थियों के लिए प्रेजेंटेशन का महत्व प्रेजेंटेशन (presentation) देना शैक्षणिक पाठ्यक्रम का एक महत्वपूर्ण व्यावहारिक पाठ्यक्रम है, ...
- 100+ Interesting Biology Presentation Topics with PPT Biology Topics for Presentation & Research Biology is a topic that every school student studies and university student who does major in...
- 100 Interesting Fun Topics for Presentations Fun Topics for Presentations We have prepared for you a fantastic collection of fun topics for presentation with relevant links to the artic...
Recent Seminar Topics
Seminar topics.
- 💻 Seminar Topics for CSE Computer Science Engineering
- ⚙️ Seminar Topics for Mechanical Engineering ME
- 📡 Seminar Topics for ECE Electronics and Communication
- ⚡️ Seminar Topics for Electrical Engineering EEE
- 👷🏻 Seminar Topics for Civil Engineering
- 🏭 Seminar Topics for Production Engineering
- 💡 Physics Seminar Topics
- 🌎 Seminar Topics for Environment
- ⚗️ Chemistry Seminar Topics
- 📈 Business Seminar Topics
- 👦🏻 Seminar Topics for Youth
Investigatory Projects Topics
- 👨🏻🔬 Chemistry Investigatory Projects Topics
- 📧 Contact Us For Seminar Topics
- 👉🏼Follow us in Slideshare
Presentation Topics
- 🌍 Environment Related Presentation Topics
- ⚗️ Inorganic Chemistry Presentation Topics
- 👨🏻🎓 General Presentation Topics
- 🦚 Hindi Presentation Topics
- 🪐 Physics Presentation Topics
- 🧪 Chemistry: Interesting Presentation Topics
- 🌿 Biology Presentation Topics
- 🧬 Organic Chemistry Presentation Topics
Speech Topics and Ideas
- 🦁 Informative and Persuasive Speech Topics on Animals
- 🚗 Informative and Persuasive Speech Topics on Automotives
- 💡 Ideas to Choose Right Informative Speech
- 👩🏻🎓 Informative Speech Topics For College Students
- 🔬 Informative Speech Topics on Science and Technology

IMAGES
VIDEO
COMMENTS
Technical Seminar Topics for CSE with Abstract. 3D Printing. 3D Printing is the process to develop a 3D printed object with the help of additive processes. Here, there are three-dimensional objects created by a 3D printer using depositing materials as per the digital model available on the system. 4G Technology.
600+ Popular Seminar Topics for CSE 2023. Latest Seminar Topics for CSE 2023. Mobile Computing and its Applications. Rover Mission Using JAVA Technology. Pill Camera in Medicine. Postulates of Human-Computer Interface. Software Testing. IT In Space. Interconnection of Computer Networks.
This list contains a collection of new technical topics with abstracts ranging from various technical topics accompanied by reports for Computer Science and Engineering (CSE), Information Technology (IT), BCA and MCA.We have carefully selected these topics based on the latest technology trends in Computer Science, Cloud Computing, Software Engineering, AI, Chat GPT, Data Mining, and Data Science.
Technical IEEE Seminar Topics for CSE with PPT and PDF Report (2024) Google Chrome OS. Google Chrome OS is a well-known operating system specially created for netbooks and tablets. It was released by Google about a decade ago in 2009 and created on the top of a Linux Kernel. It runs perfectly on the ARM and Intel X86 chips.
Tempest and Echelon. Tempest and Echelon are two of the most popular technical seminar topics for cse students. Tempest is a software engineering tool that automates the process of creating software prototypes. It is used to create high-fidelity prototypes of software applications.
These presentation topics will be beneficial for students of Engineering and management courses such as BE Computer science, B Tech IT, MCA, BCA and MBA. Below is the list of Best Computer Science Presentation Topics. Artificial intelligence. Advanced Research Projects Agency Network (ARPANET) AI & critical systems. Quantum Computing.
Conference Topics for CSE (Computer Science) at ppt: Studies Mutiny team provides your list of latter the best technical Seminar Topics for CSE Schnell Memory Access (DMA ) Direct Memory Zugang is a computing technique used for the transfers for data from RAM in a computers to a different area in the system without CPU processing.
Computer Science Engineering abbreviated as CSE is one of the most popular courses among engineering aspirants.CSE is an academic program at universities around the globe that mainly integrates computer engineering and computer science. The seminar is an essential technical session for the students dedicated to current and emerging topics across domains. . The seminars enhance the essential ...
Check out the latest collection of seminar topics for CSE, latest technical CSE MCA IT seminar topics, recent essay topics, speech ideas, dissertation, thesis, IEEE and MCA seminar topics for BTech, MTech, BCA, and MCA Students. Finger Print Authentication. Fingerprints are the most common means of authenticating biometrics—the distinctive ...
A list of Top 20 technical seminar topics for computer science engineering (CSE) you should choose for seminars and presentations in 2019. The list also contains related seminar topics on the emerging technologies in computer science, IT, Networking, software branch. To download PDF, PPT Seminar Reports check the links.
List of Latest Technical Seminar Topics For CSE 2023. 5G Wireless Technology. 3d Searching. 5 Pen PC Technology. Advanced Queue Management Techniques. Advanced Encryption Standard. Advanced Web Development Techniques. Amoeba: Distributed Operating System. Artificial Neural Network (Ann)
April 14, 2024. We bring you the latest Paper Presentation Topics for Computer Science Engineering. Click on the topic name to read in detail. These topics give an idea of what topic to choose and what information needs to be included as part of a technical paper. Technical papers have been written in a standard format.
On this page, we have listed the Best 20 technical seminar topics for computer engineering students which should be selected for the year 2023.The seminar topics for the latest technology in computer science are further classified into more subtopics.The seminar topics we have enlisted on the basis of the new technologies that would revolutionize the coming decade.
CSE students can use topics like computing edge, algorithms, and robotics. Thus, this guide has discussed technical paper presentation topics for CSE. After selecting the topic, getting a tool for impactful presentations is essential. In this regard, Wondershare Presentory is the most accurate tool for diverse needs.
Here is a list of the latest CSE Seminar topics; for the abstract, search topic title in Collegelib. If you are looking for more CSE seminar topics with abstracts, please refer to 499 Seminar topics for Computer Science - CSE. Leap Motion, sensor motion detector technology Wolfram Alpha full seminar report and abstract Ambient intelligence
Seminar Key available CSE (Computer Science) with ppt: Study Mafia staff makes thou list of latest and best technical Workshop Topics for CSE Disseminated denial-of-service attacks (DDoS) Widely Disclaimer regarding Maintenance (DDoS) is a DOS attack that includes an variety of impacted business.
Top 25 Technical Seminar Topics for CSE and its allied branches with Prepration points. TIE. March 4, 2024. Articles. Find the top 25 trendy Technical Seminar topics with prepration points to help you prepare for maximum marks from college point of view..
Types of CSE Paper Presentation Topics. If you study computer science and engineering in a college or a university, you most likely face assignments such as presentations in the area of numerical computing, discrete algorithms, modeling and simulation, computational data analysis, big data, cloud computing and machine learning, high-performance computing, etc.
It contains a list of Seminar Topics for CSE that are completely of latest technology. These are just the name of Seminar Topics for CSE but it also contains ppt and pdf report so that you can save a lot of your time. General Topics Non Technical Topics. Mechanical Engineering MCA. Computer Science Electronics.
WiFiber. XMax. Road characterization of Digital Maps. Biometric Electronic Wallet. HGI with 3D-Environment. MAS to Windows Azure Cloud. Fake Access Point Detector. Technical Seminars for engineering students available for free!! Download these CSE Technical Seminars along with their reports before it's too late!!
The latest technical seminar topics are based on tech trends that students and professionals should select for presentation and add to their skillset. Topics For Seminar Discover the best seminar topics, speech topics, and debate topics with downloadable presentations, seminar reports and journals.