
Java, Java, Java: Object-Oriented Problem Solving
(4 reviews)
Ralph Morelli, Trinity College
Ralph Walde, Trinity College
Copyright Year: 2016
Publisher: Ralph Morelli, Ralph Walde
Language: English
Formats Available
Conditions of use.
Learn more about reviews.
Reviewed by Onyeka Emebo, Assistant Professor, Virginia Tech on 12/28/21
The text adequately addresses areas under Object Oriented Programming using Java as a Programming Language for Introduction to Computer Science courses. It gently introduces basic concepts in computer, objects and java using problem solving... read more
Comprehensiveness rating: 5 see less
The text adequately addresses areas under Object Oriented Programming using Java as a Programming Language for Introduction to Computer Science courses. It gently introduces basic concepts in computer, objects and java using problem solving approaches and gradually builds up to more advanced Java technologies in such a simplified manner that can be easily understood. The text also provides a table of content at the beginning and a summary of points for each chapter with exercises.
Content Accuracy rating: 4
The text content is accurate, without errors and unbiased. There is however some links that needs to be updated.
Relevance/Longevity rating: 4
While the field of computer science with particular emphasis to programming as it relates to this text is constantly evolving, the approach taken by this text to teach the essentials is likely to persist. The code, tested in Java 8, should continue to work with new Java releases. Updates to the text can be done easily by the way it has been written.
Clarity rating: 5
The text is written in a clear and easy to understand manner. The objectives, explanations, examples and exercises are clear and easy to follow. The codes are well commented to aid readability.
Consistency rating: 4
The text is highly consistent in both structure and terminology. It starts each chapter with objectives and outline and concludes with summary, exercises and solutions. However, some codes within the chapters are put in figures while others are not, this could be confusing.
Modularity rating: 5
The text is divided in 17 chapters (0 - 16) and 8 appendices (A – H). Each chapter is further divided into sections and subsections. This breakdown makes it easier for instructors to apportion sections to students at different times within the course.
Organization/Structure/Flow rating: 5
The text is organized in a manner that is logical and it flows well from section to section. The structure makes navigation from chapter to chapter easier.
Interface rating: 3
I reviewed the PDF version and it looks good to a large extent. The links in the table of contents are working properly. There are clickable links within the text to different figures, sections, such as appendices, and external websites. However, there are some issues with some figure titles, e.g., figure 12, 1.10, 2.7, 2.10, 2.14, etc. are cut off. Some hyperlinks for some figures missing e.g., figure 2.8 and some figures don’t have titles.
Grammatical Errors rating: 5
The text contains no grammatical errors.
Cultural Relevance rating: 5
The text is culturally neutral. The examples are unbiased in the way it has been presented.
Reviewed by Ghaith Husari, Assistant Professor, East Tennessee State University on 4/17/20
This book covers Object-Oriented Programming under JAVA. It introduces the concepts of object-oriented programming and they are used for problem-solving. This book covers all the relevant areas of Object-Oriented Programming under Java. Also, it... read more
This book covers Object-Oriented Programming under JAVA. It introduces the concepts of object-oriented programming and they are used for problem-solving. This book covers all the relevant areas of Object-Oriented Programming under Java. Also, it covers more advanced topics such as socket programming and algorithms.
Content Accuracy rating: 5
The Object-Oriented concepts and implementation example shown in code samples are accurate and easy to learn as the code samples are aligned with the concept being discussed. Some links and URLs are out-dated but they have little to no impact on student learning. However, I would add a note that says "some of the links and URLs might not up-to-date. However, they can be found using search engines if necessary"
Programming languages get updated regularly to include new and easier functions to use. While it is impossible for a textbook to include every function, this textbook provides a great learning opportunity that allows students to build the muscle to be able to learn more about Java online. When it comes to Object-Oriented concepts, the book is extremely relevant and up-to-date
The textbook is very easy to understand and the code sample is both clear (code readability) and relevant.
Consistency rating: 5
The text and the terms it contains are consistent. Also, the textbook follows a consistent theme.
The textbook chapters are divided into sections and subsections that are shown also in the table of contents which can be used to visit each section.
The textbook consists of seventeen chapters that are organized in a logical manner. The more general concepts such as problem-solving and programing are placed at the beginning, then the chapters introduce the discuss Object-Oriented Programming come after the general chapters. The more advanced topics such as socket programming and data structures and algorithms come towards the end. This made a lot of sense to me.
Interface rating: 5
The textbook is easily accessible online and it can be downloaded to open with Edge or Adobe Reader without any problems.
No grammar issues have been noticed.
This textbook is neutral and unbiased.
Reviewed by Guanyu Tian, Assistant Professor, Fontbonne University on 6/19/18
This textbook covers Object-Oriented Programming with Java programming language pretty well. It starts with the concept of Objects and problem solving skills and then dive into Java programming language syntax. Overall, it appropriately covers all... read more
Comprehensiveness rating: 4 see less
This textbook covers Object-Oriented Programming with Java programming language pretty well. It starts with the concept of Objects and problem solving skills and then dive into Java programming language syntax. Overall, it appropriately covers all areas of the subject including the main principles of Object-Oriented Programming and Java programming language. In the later chapters, this textbook also introduces advanced topics such as concurrent programming, network/socket programming and data structures. The textbook provides table of contents at the beginning and index of terms at the end. Each chapter also provides a list of key words and a list of important concepts and technique terms.
Content Accuracy rating: 3
The content of the textbook is mostly accurate. Many URLs linked to Java documentations and APIs are not up-to-date.
Many URLs to Java references are not up-to-date and many online samples are not accessible. Nonetheless, the concepts of Object-Oriented Programming and Java programming language syntax are mostly current. Any updates to the contents of the textbook can be implemented with minimal effort.
The text is easy to understand. However, some of the texts are not displayed on adobe reader.
Consistency rating: 3
The text is consistent in terms of framework. Each chapter starts with introduction to a problem, and then discussion and design of the solution with UML diagrams; then Java is used to implement the solution(s). However, there is some level of inconsistency in terms of Java code samples. For example, some Java code examples use appropriate indentations and new lines, but some examples do not. This may confuse students.
Each chapter is divided into different sections and subsections. A student can go to each section of a chapter by clicking it in the Table of Contents.
Organization/Structure/Flow rating: 3
The topics in this text book are organized in a reasonable order. It starts with general concepts of computer and program design, then Objects and Java Programming Language, and then advanced topics in computer programming. It would be better if the textbook starts with Java programming language and then principles of Object Oriented programming.
Some of the texts are not displayed in the reviewer's adobe reader. Many diagrams and figures are poorly drawn. Overall, the interface of the book is one area that needs improvement.
No major grammar issues has been noticed.
The text of this textbook is a neutral and unbiased.
Overall, this textbook covers materials of Object-Oriented Programming with Java taught in first or second-year computer science course. However, the contents of Java programming language has not been up-to-date and the interface of the book is very poor compare to similar books the reviewer has used for learning and teaching the same materials. Some sample codes are not well written or inconsistent in terms of the use of indentation and new lines. Many URLs are obsolete and the web pages are not accessible.
Reviewed by Homer Sharafi, Adjunct Faculty Member, Northern Virginia Community College on 6/20/17
The textbook includes the material that is typically covered in a college-level CS1 course. Using an “early objects” approach and Java as the programming language, the authors go over problem-solving techniques based on object-oriented... read more
The textbook includes the material that is typically covered in a college-level CS1 course. Using an “early objects” approach and Java as the programming language, the authors go over problem-solving techniques based on object-oriented programming principles. In addition to an Index of terms towards the end of the text, each chapter summary includes the technical terms used, along with a bulleted-list of important points discussed in that chapter.
The computer science concepts and the accompanying sample code are accurate and error-free; however, the only issue is the fact that the URLs that make references to various aspects of Java, such as API documentation, JDK, and the Java Language Specification, have not been updated to reflect the fact that Sun Microsystems was acquired by Oracle back in 2010.
Like other software systems, Java is updated on a regular basis; nonetheless, the computer science concepts discussed in the textbook are based on standard undergraduate curriculum taught in a CS1 course. Therefore, any updates to the textbook would need to be with regard to the version of Java with minimal effort.
Clarity rating: 4
The authors deliver clear explanations of the computer science concepts and the accompanying Java language features.
There is a consistent theme throughout much of the text: A topic is introduced and discussed within the context of a problem. Its solution is then designed and explained using UML diagrams; finally, Java is used to illustrate how the solution is implemented on the computer.
Each chapter is divided into sections that can easily be identified within the table of contents. Therefore, it’s fairly easy for a student to pick and choose a section in a chapter and work on the other sections later. Throughout each chapter, there are self-study exercises to incrementally test understanding of the covered material. Solutions to those self-study exercises are then provided towards the end of the chapter. In addition, each chapter includes end-of-chapter exercises that can be used to assess one’s understanding of the computer science concepts as well as the various features of Java.
The book consists of seventeen chapters; however, a typical CS1 course would need the material in the first ten chapters only, and those chapters are set up in a logical manner, allowing one to go through the material sequentially. Depending on how fast he first ten chapters are covered during the course of a semester, an instructor may choose from the last seven chapters in the text to introduce more advanced topics in computer science and/or Java.
Interface rating: 1
The textbook can be accessed online or opened using Acrobat Reader with no problem. There are no issues, as long as navigation is done one page after another manually. However, when browsing through the table of contents (TOC) or the Index, the entries are not set up using any live links. That is, you cannot click on a page number associated with an item within the TOC or the Index to go directly to that page.
Grammatical Errors rating: 3
This reviewer did not come across any such issues, while going through the text.
This is a computing textbook, where the contents are presented using technical terms. Culturally, the textbook is completely neutral and unbiased in terms of how the material is presented.
Table of Contents
- 0 Computers, Objects, and Java
- 1 Java Program Design and Development
- 2 Objects: Defining, Creating, and Using
- 3 Methods: Communicating with Objects
- 4 Input/Output: Designing the User Interface
- 5 Java Data and Operators
- 6 Control Structures
- 7 Strings and String Processing
- 8 Inheritance and Polymorphism
- 9 Arrays and Array Processing
- 10 Exceptions: When Things Go Wrong
- 11 Files and Streams
- 12 Recursive Problem Solving
- 13 Graphical User Interfaces
- 14 Threads and Concurrent Programming
- 15 Sockets and Networking
- 16 Data Structures: Lists, Stacks, and Queues
Ancillary Material
- Ralph Morelli, Ralph Walde
About the Book
We have designed this third edition of Java, Java, Java to be suitable for a typical Introduction to Computer Science (CS1) course or for a slightly more advanced Java as a Second Language course. This edition retains the “objects first” approach to programming and problem solving that was characteristic of the first two editions. Throughout the text we emphasize careful coverage of Java language features, introductory programming concepts, and object-oriented design principles.
The third edition retains many of the features of the first two editions, including:
- Early Introduction of Objects
- Emphasis on Object Oriented Design (OOD)
- Unified Modeling Language (UML) Diagrams
- Self-study Exercises with Answers
- Programming, Debugging, and Design Tips.
- From the Java Library Sections
- Object-Oriented Design Sections
- End-of-Chapter Exercises
- Companion Web Site, with Power Points and other Resources
The In the Laboratory sections from the first two editions have been moved onto the book's Companion Web Site. Table 1 shows the Table of Contents for the third edition.
About the Contributors
Ralph Morelli, Professor of Computer Science Emeritus. Morelli has been teaching at Trinity College since 1985, the same year the computer science major was first offered. More recently, he was one of the Principal Investigators (PIs) for the Humanitarian Free and Open Source Software (HFOSS) project, an NSF-funded effort to get undergraduates engaged in building free and open source software that benefits the public. In summer 2011 a team of Trinity HFOSS students and faculty traveled to Haiti to build an open source mobile application that helps manage beneficiaries for a humanitarian aid organization. Currently Morelli is the PI of the Mobile CSP project, an NSF-funded effort to train high school teachers in CT and elsewhere to teach the emerging Advanced Placement CS Principles course that is being created by the College Board. The main goal of this NSF initiative is to increase access to computer science among underrepresented groups, including girls, African Americans, and Hispanic Americans. The Mobile CSP course teaches students to create mobile apps to serve their community. In summer 2014, a group of 20 Mobile CSP students spent their summer building mobile apps for the city of Hartford.
Ralph Walde. Dr. Walde has given Trinity 28 years of distinguished service, first as a Professor of Mathematics and now as a Professor of Computer Science. He was instrumental in helping to establish and nourish computing at Trinity and was one of the founding members of the Computer Science Department.
Contribute to this Page
Advanced Object-Oriented Programming in Java – Full Book
Java is a go-to language for many programmers, and it's a critical skill for any software engineer. After learning Java, picking up other programming languages and advanced concepts becomes much easier.
In this book, I'll cover the practical knowledge you need to move from writing basic Java code to designing and building resilient software systems.
Many top companies rely on Java, so understanding it is essential, not just for tech jobs but also if you're considering starting your own business.
Looking to move up in your career? Contributing to open-source projects can be a smart move. This guide will also help you with the advanced skills you'll need to become an open-source Java developer and get noticed by employers.
And finally, the book will help you stay current with the latest in technology as you learn about the Java behind AI, big data, and cloud computing. You'll learn to create high-performance Java applications that are fast, efficient, and reliable.
Prerequisites
Before diving into the advanced concepts covered in this book, it is essential to have a solid foundation in Java fundamentals and Object-Oriented Programming (OOP).
This guide builds upon the knowledge and skills acquired in my previous book Learn Java Fundamentals – Object-Oriented Programming .
Here are the key prerequisites:
Strong Understanding of Java Basics
- Syntax and Structure : Familiarity with Java syntax and basic programming constructs.
- Basic Programming Concepts : Proficiency in writing and understanding simple Java programs.
Proficiency in Object-Oriented Programming Concepts
- Classes and Objects : Deep understanding of classes, objects, and their interactions.
- Inheritance and Polymorphism : Knowledge of how inheritance and polymorphism are implemented in Java.
- Encapsulation and Abstraction : Ability to encapsulate data and utilize abstraction in program design.
Experience with Java Data Types and Operators
- Primitive and Non-primitive Data Types : Comfort with using various data types in Java.
- Operators : Familiarity with arithmetic, relational, and logical operators.
Control Structures and Error Handling
- Control Flow Statements : Proficiency in using if , else , switch , and loop constructs.
- Exception Handling : Basic understanding of handling exceptions in Java.
Basic Understanding of Java APIs and Libraries
- Familiarity with using standard Java libraries and APIs for common tasks.
This guide assumes that you have already mastered these fundamental concepts and are ready to explore more advanced topics in Java programming.
This book will delve into complex topics that require a strong foundation in basic OOP principles, along with familiarity with Java's core features and functionalities.
How this Book Will Help You:
- Position yourself as a top candidate for senior Java developer roles, ready to tackle high-stakes projects and lead innovative software development initiatives.
- Transform you into an expert in high-demand areas such as concurrency and network programming, making you an invaluable asset to any team.
- Build a portfolio of impressive projects, from dynamic web applications to sophisticated mobile games, showcasing your advanced Java skills to potential employers.
- Learn to write code that's not only functional but exceptionally clean and efficient, adhering to the best practices that define expert-level Java programming.
- Engage with a community of like-minded developers, and by the end of this guide, you’ll not only gain knowledge but also a network of peers to collaborate with on future Java endeavors.
- Equip yourself with advanced problem-solving skills that enable you to dissect and overcome real-world software development challenges with innovative solutions.
- Stay ahead of the curve by mastering the latest Java features and frameworks that will define the future of software development.
- Prepare yourself to achieve Java certification, validating your skills and knowledge in a way that's recognized across the industry.
- Gain the confidence to contribute to open-source projects or even start your own, with the deep understanding of Java that this guide provides.
You're embarking on a journey to master Java Object-Oriented Programming, a skill that paves the way for diverse opportunities in software engineering. This guide will lay a foundation for you to transition from writing code to building robust software systems.
With these advanced skills, you're poised to contribute to open-source projects, qualify for top Java developer roles, and stay ahead in the tech industry. Your path from learning to leading in the Java community starts here. Let's begin.
Table of Contents
Chapter 1: unit testing and debugging.
- Chapter 2. File Handling and Input/Output (I/O)
Chapter 3: Deadlocks and How to Avoid Them
Chapter 4: java design patterns, chapter 5: how to optimize java code for speed and efficiency.
- Chapter 6: Concurrent Data Structures and Algorithms
Chapter 7: Fundamentals of Java Security
Chapter 8: secure communication in java.

In software development, unit testing and debugging play a vital role in ensuring the quality and reliability of your code. These practices provide a reliable means to verify the correctness of your code, allowing you to identify and address errors or bugs that may hinder its intended functionality.
Unit testing allows you to systematically test individual units of your code, such as functions or methods, applying pressure through tests to ensure their proper functioning.
By conducting these tests, you can establish a reliable method to validate the behavior of your code. This not only instills confidence in your work but also allows you to catch and address potential issues early on, making the development process more efficient.
To become an efficient software engineer, it is crucial to prioritize unit testing and debugging as integral parts of your software development workflow. By doing so, you can ensure the stability and effectiveness of your codebase, providing practical advice that will help you deliver high-quality software.
Fundamentals of Unit Testing
Java, with its rich ecosystem and extensive support for testing frameworks, offers a fertile ground for implementing unit testing practices. In this section, you'll learn about Java's testing landscape, highlighting essential tools and frameworks like JUnit.
JUnit is a widely used testing framework that provides a comprehensive set of features and functionalities to facilitate the creation and execution of high-quality unit tests in Java.
By leveraging tools like JUnit, you can confirm the effectiveness and efficiency of your testing efforts, leading to the development of robust and reliable Java applications.
Examples for unit testing include isolation, repeatability, and simplicity. When conducting unit tests, it is important to focus on testing the beginning, middle, and end of your functions.
By separating each key area and stress testing it, you can ensure thorough testing of your code. This approach aligns with the principles of the scientific method, where you aim to test all crucial aspects of your functions to achieve reliable and accurate results.
Unit Testing Examples
To illustrate unit testing in Java using JUnit, let's create some practical examples. We'll focus on a simple Java class and how we can apply unit testing to it, adhering to principles like isolation, repeatability, and simplicity.
Suppose we have a Java class named Calculator with a couple of basic mathematical operations:
Using JUnit, we will write test cases that individually test each method of the Calculator class.
First, include JUnit in your project. If you're using Maven, add the following dependency to your pom.xml :
Now, let's create test cases:
In these test cases, we follow the principles of unit testing:
- Isolation : Each test method ( testAdd and testSubtract ) is independent of others. They test specific functionalities of the Calculator class. This is what you want to do, test each case systematically and separately.
- Repeatability : These tests can be run multiple times, and they will produce the same results, ensuring consistent behavior of the methods being tested.
- Simplicity : The tests are straightforward and focused solely on the method they are meant to test. For instance, testAdd only tests the add method.
How to Write Helpful Unit Tests
When crafting unit tests, it's essential to approach them with a clear and systematic strategy. This involves following certain guidelines and asking pertinent questions to ensure comprehensive and effective testing.
Here’s an outline to guide you through the process:
Create a New Object
Firstly, for each test, create a new instance of the object you're testing. This ensures that each test is independent and unaffected by the state changes caused by other tests. In Java, this typically looks like this:
Use Assertions:
Utilize JUnit's assertion methods like assertEquals , assertTrue , and so on to verify the outcomes of your test. These assertions form the crux of your test, as they validate whether the object's behavior matches expectations. For example:
Initiate Several Objects:
In some cases, it may be necessary to initiate several objects to simulate more complex interactions. This is particularly useful when testing how different components of your application interact with each other. For instance:
Key Guidelines and Questions for Writing Tests
- What is the expected outcome? Clearly define what result you expect from the method you're testing. This guides your assertion statements.
- Are the tests independent? Ensure each test can run independently of the others, without relying on shared states or data.
- Are edge cases covered? Include tests for boundary conditions and edge cases, not just the typical or average scenarios. This is key for creating reliable software.
- Is each test simple and focused? Aim for simplicity. Each test should ideally check one aspect or behavior of your method.
- How does the method behave under different inputs? Test a variety of inputs, including valid, invalid, and edge cases, to ensure your method handles them correctly.
- Is the test repeatable and consistent? Your tests should produce the same results every time they're run, under the same conditions.
- Are the test names descriptive? Name your tests clearly to indicate what they are testing. For example, testEmptyListReturnsZero() is more informative than testList() .
- Are you checking for exceptions? Where applicable, write tests to check that your method throws the expected exceptions under certain conditions.
Following these guidelines ensures that your unit tests are robust, reliable, and provide a comprehensive assessment of your code's functionality.
Practical Unit Testing Scenarios and Case Studies
Here are examples of Java code snippets that demonstrate real-world scenarios and case studies related to array manipulation, along with the corresponding unit tests using JUnit. These examples illustrate common challenges and how to address them through effective unit testing and debugging.
Sort a List of Products
Scenario : A Java method sorts an array of Product objects based on their price.
Product Class:
Sorting Method:
Find the Maximum Value in an Array
Scenario : A method is supposed to find the maximum value in an array, but it's returning incorrect results.
Method with Bug:
Debugging and Fixing:
The issue is in the for-loop, which incorrectly starts from index 1 instead of 0. Correcting the loop to start from index 0 fixes the bug. Corrected Method:
These examples show how unit testing can reveal bugs in real-world scenarios and guide developers in debugging and fixing issues related to array manipulation in Java.
Unit Testing Best Practices
When it comes to writing and maintaining unit tests in Java, there are several best practices that can help ensure the effectiveness and reliability of your tests.
First and foremost, it is crucial to focus on test isolation. Each unit test should be independent of others, meaning that they should test specific functionalities of the code in isolation. This allows for a more systematic and targeted approach to testing, making it easier to identify and fix any issues that may arise.
By keeping tests isolated, you can ensure that changes made to one test do not inadvertently affect the results of other tests.
Another important best practice is to prioritize test repeatability. Tests should be designed in such a way that they can be run multiple times, producing the same results each time.
This ensures consistent behavior and allows for easy identification of any changes or regressions in the code. By making tests repeatable, you can have confidence in the stability and reliability of your codebase.
Simplicity is also key when it comes to writing unit tests. Each test should be focused solely on the method or functionality it is meant to test.
By keeping tests simple and concise, you can improve readability and maintainability. Additionally, simple tests are easier to understand and debug, making it quicker to identify and fix any issues that may arise.
When writing unit tests, it is important to consider edge cases and boundary conditions. These are scenarios that may not be covered by typical or average test cases.
By including tests for edge cases, you can ensure that your code handles these situations correctly and avoid potential bugs or errors. Testing these extreme scenarios is crucial for creating reliable and robust software.
Test names should be descriptive and indicative of what is being tested. This helps improve the readability and understandability of the tests, making it easier for other developers to navigate and interpret them.
Clear and concise test names also serve as documentation for the behavior and functionality being tested.
In addition to these best practices, it is essential to follow a systematic and comprehensive approach to unit testing. This involves asking pertinent questions and following guidelines to ensure comprehensive and effective testing.
Questions such as "What is the expected outcome?" and "Are the tests independent?" help guide the creation of thorough and reliable unit tests.
These practices will help ensure the stability and effectiveness of your codebase, allowing you to deliver high-quality software that meets the highest standards of functionality and reliability.
Hands-On Exercises for Unit Testing in Java
Beginner level: exercise & solution, exercise: testing a sum function.
Create a function sumArray that takes an array of integers and returns the sum of all the elements. Write a unit test to validate that the function correctly sums the array elements.
Solution with Code:
Intermediate Level: Exercise & Solution
Exercise: testing array equality.
Create a function arraysEqual that compares two arrays of integers and returns true if they are equal (same elements in the same order) and false otherwise. Write a unit test to validate the function's behavior for equal and unequal arrays.
Advanced Level: Exercise & Solution
Exercise: testing array rotation.
Create a function rotateArray that takes an array and a positive integer k , and rotates the array to the right by k places. Write a unit test to validate the function's behavior for different values of k .
Each example provides a clear task, solution, and comments to guide the learner through the process of writing and understanding unit tests in Java.
These exercises range from basic array operations to more complex tasks like array rotation, covering different aspects of array manipulation and testing.
Additional Unit Testing Resources
- Java Unit Testing Guide
- What is Debugging?
- How to Debug Java Code
- A Beginner's Guide to Testing

Chapter 2: File Handling and Input/Output (I/O)
File handling in java using filewriter and filereader.
File handling is an essential aspect of programming, especially when it comes to reading from and writing to files.
In Java, file handling is accomplished using various classes and methods provided by the language's standard library. One such set of classes is FileWriter and FileReader , which are specifically designed for handling textual data.
This chapter explores the concepts and techniques involved in file handling using FileWriter and FileReader in Java.
We will discuss the importance of character streams and why choosing the right stream, such as FileWriter and FileReader , is crucial for working with textual data. We'll also delve into the constructors and methods of these classes, explore practical demonstrations, and provide exercises to enhance your understanding and proficiency in Java file handling.
What is FileWriter ?
FileWriter is a class in Java that is used for writing character-based data to a file. It is a subclass of the OutputStream class, which allows for the writing of byte-based data.
FileWriter is specifically designed for handling textual data and provides convenient methods for writing characters, character arrays, and strings to a file.
Constructors of FileWriter :
There are several constructors available in FileWriter for creating instances of the class. These constructors provide flexibility in specifying the file to be written, the character encoding to be used, and the buffer size for efficient writing. The constructors include options for passing a File object, a FileDescriptor, or a String representing the file path.
It is important to choose the appropriate constructor based on the specific use case. For example, using the File constructor allows for easy manipulation of file properties, while the String-based constructor provides a more convenient way to specify the file path. Also, specifying the character encoding and buffer size can greatly impact the performance and behavior of the FileWriter .
Methods of FileWriter :
FileWriter provides various methods for writing data to a file. The key methods include write() , flush() , and close() .
The write() method allows for writing single characters, character arrays, and strings to the file. It provides flexibility in appending data to an existing file or overwriting the content of the file.
The flush() method is used to flush any buffered data to the file. This ensures that all data is written immediately and not held in memory.
The close() method is used to close the FileWriter and release any system resources associated with it. It is important to always close the FileWriter after writing to ensure that all data is properly written and resources are freed.
Enhancing Performance with BufferedWriter:
To improve the performance of writing data to a file, you can use FileWriter in conjunction with BufferedWriter . BufferedWriter is a class that provides buffering capabilities, reducing the number of system calls and improving overall efficiency.
By wrapping the FileWriter with a BufferedWriter , data can be written to a buffer first, and then flushed to the file when necessary. This reduces the overhead of frequent disk writes and can significantly enhance the performance of file writing operations.
What is FileReader ?
FileReader is an important class in Java that specializes in reading character streams from a file. It is a subclass of the InputStreamReader class, which is responsible for converting byte streams into character streams.
FileReader inherits the functionality of InputStreamReader and provides additional methods specifically designed for reading textual data from a file.
Constructors of FileReader
FileReader offers several constructors that allow for different file access scenarios. These constructors provide flexibility in specifying the file to be read, the character encoding to be used, and the buffer size for efficient reading.
You can choose the appropriate constructor depending on your use case. For example, a FileReader instance can be created by passing a File object, a FileDescriptor, or a String representing the file path.
Methods of FileReader
FileReader provides various methods for reading data from a file. The read() method is the primary method used for reading characters from a file. It returns the next character in the file as an integer value, or -1 if the end of the file has been reached.
FileReader also provides a close() method to release any system resources associated with the FileReader instance. It also allows for handling IOExceptions, which are exceptions that may occur during file reading operations.
Java Code to Demonstrate FileWriter
Hands-on exercises and real-world applications, how to write to a file using filewriter.
Task : Create a program to write a list of students' names to a text file.
Exercise : Modify the program to append new students to the existing list without overwriting the current data.
How to Read from a File using FileReader
Task : Create a program to read the contents of the "students.txt" file created above and display them on the console.
Now, let's look at some practical code examples for common pitfalls in file handling using Java's FileWriter and FileReader classes, along with solutions:
File Not Found:
- Pitfall : Attempting to read from or write to a file that doesn't exist.
- Solution : Always check if the file exists before performing read/write operations. Use the File class to create a new file if it does not exist.
Incorrect File Paths:
- Pitfall : Using incorrect file paths leading to FileNotFoundException .
- Solution : Use absolute paths for clarity or ensure the relative path is correct. Pay attention to cross-platform path separators.
Resource Leakage:
- Pitfall : Not closing FileWriter or FileReader properly, which can lead to resource leakage.
- Solution : Use try-with-resources to ensure that file resources are automatically closed.
Overwriting File Content:
- Pitfall : Accidentally overwriting existing file content.
- Solution : Use the FileWriter constructor that allows for appending content ( new FileWriter("filename.txt", true) ).
Character Encoding Issues:
- Pitfall : Issues with character encoding leading to corrupted file data.
- Solution : Be aware of the platform's default charset. Specify charset explicitly if handling non-text files or special character sets.
Buffering for Performance:
- Pitfall : Inefficient file writing/reading operations.
- Solution : Use BufferedWriter or BufferedReader for efficient reading and writing operations.
These examples demonstrate practical solutions to overcome common challenges encountered in file handling in Java.
File handling is a fundamental aspect of programming, and in Java, it can be effectively accomplished using the FileWriter and FileReader classes.
FileWriter is specifically designed for writing character-based data to a file, offering convenient methods for writing characters, character arrays, and strings. On the other hand, FileReader specializes in reading character streams from a file, providing additional methods for reading textual data.
Byte Streams vs Character Streams
In this section, you'll learn about the concept of streams in Java. Streams are an essential part of the Java I/O (Input/Output) model, allowing the transfer of data between a program and an external source or destination.
There are two main types of streams in Java: Byte Streams and Character Streams.
Byte Streams are used for 8-bit byte operations and are commonly employed for reading and writing binary data. They are particularly useful when dealing with files or streams that contain non-textual information, such as images or audio files.
Examples of key Java classes associated with Byte Streams include FileInputStream and FileOutputStream .
On the other hand, Character Streams are designed for 16-bit Unicode operations and are primarily used for reading and writing textual data. They are especially suitable when working with text files or when you need to handle character-based input or output.
Important Java classes for Character Streams include FileReader and FileWriter .
Advantages and Limitations of Byte and Character Streams
To effectively utilize Byte Streams and Character Streams in your Java programs, here are some practical recommendations:
- Choose the appropriate stream type based on the nature of your data. If you are working with binary data or non-textual information, Byte Streams provide efficient operations for handling such data. But if your application primarily deals with textual data, such as log files or user-generated content, Character Streams are the recommended choice.
- Use the appropriate Java classes associated with each stream type. For Byte Streams, use classes like FileInputStream and FileOutputStream for reading from and writing to files. For Character Streams, use classes like FileReader and FileWriter for reading and writing text data.
- Handle exceptions properly and close streams to avoid resource leaks. This ensures smooth data transfer and manipulation, enhancing the overall performance and reliability of your Java applications.
Byte Stream and Character Stream Code Examples
Here's an advanced code example that demonstrates the use of Byte Streams and Character Streams in Java:
In this code example, we have two sections: one demonstrating the use of Byte Streams and another demonstrating the use of Character Streams.
For Byte Streams, we use FileInputStream to read binary data from an input file ( input.txt ). We read the data in chunks using a byte buffer and process the data (in this case, encrypting it). Then, we use FileOutputStream to write the encrypted data to an output file ( output.txt ).
For Character Streams, we use FileReader to read text data from the same input file. We read the data line by line using a BufferedReader , process the data (in this case, converting it to uppercase), and use FileWriter and BufferedWriter to write the processed data to the output file.
These examples showcase the practical use of Byte Streams and Character Streams for handling binary and textual data, respectively.
Remember to handle exceptions properly and close the streams after use to ensure efficient and reliable stream-based operations in your Java programs.
When choosing between Byte Streams and Character Streams in Java, consider the nature of your data and the specific requirements of your application.
For non-textual or binary data, use Byte Streams. For textual data, use Character Streams. Handle exceptions properly and close streams after use.
By understanding the advantages and limitations of each stream type, you can make informed decisions and ensure efficient data processing in your Java applications.
How to Handle Exceptions in I/O
Java exception basics.
In the realm of Java programming, understanding exceptions is crucial for writing reliable and maintainable code. Exceptions in Java refer to conditions that disrupt the normal flow of a program. They are classified based on their nature to handle errors or exceptional situations that arise during runtime.
Java handles exceptions using "try-catch" blocks, allowing programmers to isolate and manage error conditions effectively. This understanding is key to anticipating and addressing potential issues, leading to more robust code.
Familiarity with the wide range of Java exceptions is important for precise error reporting and targeted handling. Best practices in throwing exceptions include adhering to Java’s syntax and guidelines, and judicious use of custom exceptions to improve code clarity and maintainability.
Exception handling extends beyond "try-catch" blocks. The "finally" block is used for cleanup operations, ensuring resource release regardless of exception occurrence. Nested try-catch structures provide fine-grained control over error management.
Anatomy of a Java Exception
In Java, we can use the try-catch blocks to isolate and handle exceptions. Here's an example:
By catching the exception, we can gracefully recover from error conditions and prevent our program from crashing.
Java provides a wide range of exception types to choose from. Let's say we have a method that reads data from a file. We can handle specific exceptions that might occur, such as FileNotFoundException and IOException . Here's an example:
By handling specific exceptions, we can provide more precise error reporting and targeted exception handling.
In addition to try-catch blocks, we can use the finally block for cleanup operations. For example, if we open a file in the try block, we can ensure that the file is properly closed in the finally block, regardless of whether an exception occurs. Here's an example:
Nested try-catch structures provide fine-grained control over error management. We can handle exceptions at different levels, depending on the specific needs of our program. Here's an example:
By understanding these concepts and applying best practices, we can write robust and error-resistant Java code.
Remember to keep code simplicity in mind. By applying practical advice and taking action, reliable and maintainable Java applications can be built.
Throwing Exceptions
When it comes to handling exceptions in Java, it is essential to understand the syntax for throwing exceptions, creating custom exceptions, and following best practices.
To throw an exception in Java, you can use the throw keyword followed by the exception object. This allows you to explicitly indicate that a specific error condition has occurred. For example:
By throwing exceptions, you can provide more detailed and meaningful error messages to assist in troubleshooting and debugging.
Creating custom exceptions in Java enables you to handle specific error scenarios in a more precise and targeted manner. By extending the Exception class or one of its subclasses, you can define your own exception types. For example:
Custom exceptions can be useful for encapsulating complex logic or specific error conditions within your code. They improve code readability and make it easier to identify and handle exceptional situations.
To ensure effective exception handling, it is important to follow best practices. Here are a few recommendations:
- Be specific in exception handling : Catch exceptions at the right level of abstraction to handle them appropriately. Consider the specific exception types that can be thrown and handle them accordingly.
- Provide meaningful error messages : Exception messages should clearly indicate the cause and context of the error. This helps developers understand and resolve issues more efficiently.
- Keep exception handling minimal : Only catch exceptions that you can handle effectively. Rethrowing or propagating exceptions may be necessary in some cases to allow higher-level code to handle them appropriately.
- Clean up resources : Use the finally block to release resources that were acquired within a try block, ensuring proper cleanup regardless of whether an exception occurs.
- Log exceptions : Logging exceptions helps in diagnosing and troubleshooting issues. Include relevant information such as stack traces, input values, and any other contextual details that may assist in resolving the problem.
Here's an advanced code example that demonstrates exception handling in Java:
In this example, the FileProcessor class has a method processFile() that reads lines from a file. It uses a try-with-resources block to automatically close the BufferedReader after processing the file. If the file is not found or an error occurs while reading the file, the corresponding exceptions ( FileNotFoundException and IOException ) are caught and handled. The exceptions are also rethrown to allow the higher-level code (in this case, the main() method) to handle them if needed.
Unchecked Exceptions
Unchecked exceptions are exceptions that do not require explicit handling by the programmer. They are subclasses of the RuntimeException class or its subclasses.
Unchecked exceptions are often caused by programming errors or unexpected conditions that may occur during runtime. Examples of unchecked exceptions include NullPointerException , ArrayIndexOutOfBoundsException , and IllegalArgumentException .
When dealing with unchecked exceptions, it is important to follow best practices to prevent these exceptions from occurring. This includes validating inputs and ensuring proper error handling and defensive programming.
Checked Exceptions
Checked exceptions are exceptions that must be explicitly handled or declared in the method signature using the throws keyword. They are subclasses of the Exception class (excluding subclasses of RuntimeException ).
Checked exceptions are typically used for conditions that are beyond the control of the program, such as I/O errors or network failures. Examples of checked exceptions include IOException , SQLException , and FileNotFoundException .
When handling checked exceptions, it is important to consider the appropriate handling strategy based on the specific situation. This may involve wrapping the checked exception in a custom unchecked exception, logging the exception, or propagating the exception to higher-level code for handling.
Example Code – Unchecked and Checked Exceptions
Here are additional examples that demonstrate the handling of unchecked and checked exceptions:
Unchecked Exception Example:
In this example, the divide method calculates the result of dividing the dividend by the divisor . If the divisor is zero, an unchecked exception of type ArithmeticException is thrown. This ensures that the code explicitly handles the case where division by zero occurs.
Checked Exception Example:
In this example, the readFile method reads the contents of a file specified by the fileName parameter. The method declares that it may throw an IOException (a checked exception) using the throws keyword. This allows the caller of the method to handle the exception or propagate it further up the call stack.
Understanding the differences between unchecked and checked exceptions is essential for effective exception handling in Java. By following best practices, handling exceptions appropriately, and considering the specific needs of your application, you can write robust and reliable Java code.
Remember to continuously improve your exception handling skills and stay up to date with industry best practices to ensure the highest quality in your code.
Real-World Examples of Exception Handling:
Here are some additional code examples for each of the topics we've just discussed:
Practical Applications in Java Applications:
Common scenarios for exception handling:, learning from real-world cases:.
These examples demonstrate various scenarios where exception handling is commonly applied in Java applications. The comments in the code provide explanations and instructions for each scenario.
Remember to adapt the code to your specific needs and handle exceptions according to your application's requirements.
Advanced Exception Handling Techniques
When it comes to advanced exception handling techniques in Java, there are several key aspects to consider.
Utilizing the throws Keyword: The throws keyword is used to indicate that a method may throw a particular exception. By declaring checked exceptions in the method signature, we can ensure that the calling code handles or propagates the exception.
This has a significant impact on code design and maintenance. Proper use of the throws keyword promotes clarity and forces developers to consider exception handling requirements upfront. It also allows for more modular and flexible code, as exceptions can be handled at different levels in the call stack.
Exception Chaining and Cause Analysis: Exception chaining involves linking exceptions together to provide a comprehensive view of the error chain. By utilizing exception chaining, we can identify the root cause of an exception and facilitate effective troubleshooting.
Techniques such as logging stack traces and analyzing exception causes enable us to gain insights into the underlying issues.
Real-world use cases for exception chaining include debugging complex scenarios and providing detailed error reports to aid in issue resolution.
Familiarize yourself with various best practices : Writing robust and error-resistant code involves following best practices for exception handling. It is important to handle exceptions at the appropriate level of abstraction, providing meaningful error messages and logging relevant information.
Avoiding common mistakes, such as catching exceptions unnecessarily or swallowing exceptions, ensures that exceptions are properly addressed.
Logging and Diagnosing Exceptions: Logging exceptions plays a vital role in diagnosing and troubleshooting issues. By integrating logging with exception handling, we can capture valuable information such as stack traces, input values, and contextual details. This facilitates efficient debugging and helps in resolving problems effectively.
Utilizing tools and strategies for effective logging and diagnosis enhances the error analysis process and aids in producing actionable insights.
Advanced Scenarios: By employing techniques such as multi-catch blocks or handling exceptions at different levels, we can effectively manage multiple exceptions.
Resource management in exceptions is another crucial aspect, ensuring that resources are properly released even in the presence of exceptions.
Exception handling in concurrent programming requires careful synchronization and error handling strategies to maintain data integrity and prevent race conditions.
Advanced and Custom Exception Handling Case Studies:
Analyzing real-world examples of exception handling can provide valuable insights. By studying industry cases, we can learn from successful approaches and identify common patterns. Analyzing exception handling patterns allows us to apply proven techniques and adapt them to our specific needs.
By solving complex problems with exception handling, we can develop expertise in handling challenging scenarios and build robust applications.
Remember, when writing code, it is important to keep it simple and concise. Use clear and straightforward examples to illustrate concepts. By applying practical advice and continuously improving your exception handling skills, you can develop reliable and maintainable Java applications.
Here's an example code snippet that demonstrates the use of custom exceptions and exception handling techniques:
In this example, the FileValidator class demonstrates the use of a custom exception, FileValidationException , which is thrown when a file fails validation. The validateFile method catches any IOException that occurs during file validation and rethrows it as a FileValidationException to provide a clear and meaningful error message. The Main class demonstrates the handling of the custom exception, allowing for specific error reporting and appropriate exception handling.
By applying these techniques and principles, you can effectively handle exceptions in Java and develop high-quality code. Remember to always strive for simplicity, clarity, and continuous improvement in your exception handling practices.

Deadlock is a situation in Java multithreading where two or more threads are blocked forever, waiting for each other to release resources. Understanding deadlock is crucial for writing robust concurrent code.
There are four necessary and sufficient conditions for a deadlock to occur: mutual exclusion, hold and wait, no preemption, and circular wait.
- Mutual exclusion means that a resource can only be used by one thread at a time.
- Hold and wait refers to a situation where a thread holds a resource and is waiting to acquire another resource.
- No preemption implies that resources cannot be forcefully taken away from a thread.
- Circular wait occurs when a cycle of threads exists, where each thread is waiting for a resource that is held by another thread in the cycle.
To better illustrate this concept, consider the following code snippet:
In this example, two threads call method1 and method2 concurrently. If one thread acquires resource1 and waits for resource2 , while the other thread acquires resource2 and waits for resource1 , a deadlock occurs.
To avoid deadlocks, it is essential to carefully manage resources and their acquisition order. One practical approach is to ensure a consistent and predefined order for acquiring locks. By avoiding circular wait and ensuring a consistent lock ordering, deadlocks can be prevented.
Remember to always minimize lock contention and unnecessary locks. Additionally, utilize concurrency utilities such as ReentrantLock and Semaphore to manage locks effectively.
Deadlock Example
Complex deadlock scenarios involve intricate situations where multiple threads and resources are entangled, making detection and resolution more challenging. Let's explore an example to better understand this concept in the context of Java programming.
Consider the following code snippet that demonstrates a potential deadlock scenario:
In this example, three threads, let's call them Thread A, Thread B, and Thread C, call method1 and method2 concurrently. If Thread A acquires resource1 and waits for resource2 , Thread B acquires resource2 and waits for resource3 , and Thread C acquires resource3 and waits for resource1 , a complex deadlock occurs. All threads are stuck in a state of indefinite waiting, unable to proceed.
To avoid such complex deadlocks, it becomes even more crucial to carefully manage resources and their acquisition order.
One practical approach is to establish a consistent and predefined order for acquiring locks. By doing so, we can prevent circular wait conditions and ensure a smooth execution of concurrent code.
To solve this issue, you need to ensure that all methods acquire the locks in the same order. Here’s the corrected code:
In this corrected code, both method1 and method2 acquire locks on resource1 , resource2 , and resource3 in the same order, which prevents the deadlock. This strategy is known as lock ordering — a simple yet effective way to prevent deadlocks.
It’s a good practice to always acquire locks in the same order throughout your program. This way, if a thread holds one lock and requests another, you can be sure that no other threads are holding or requesting locks in the opposite order. This eliminates the circular wait condition, and thus, the deadlock.
Remember, the order of releasing the locks doesn’t matter in preventing deadlocks. It’s the order of acquiring locks that’s crucial.
To resolve the potential deadlock in the provided example, we can modify the order of acquiring locks in either method1 or method2 . By consistently acquiring resources in the same order across all methods, we eliminate the possibility of circular wait and mitigate the risk of deadlock.
How to Detect and Analyze Deadlocks
To detect deadlocks in Java, you can analyze thread dumps. Thread dumps provide valuable information about the state of threads, including their locks and waiting conditions. By carefully examining the thread dump, you can identify if any threads are stuck in a deadlock situation.
One useful tool for deadlock detection is the jstack command. This command allows you to generate a thread dump of a Java application. You can then analyze the thread dump to identify any potential deadlocks.
Here's an example of how you can use the jstack command to detect deadlocks in a Java application:
In this command, <pid> represents the process ID of the Java application. By running this command, you will obtain a thread dump that can be analyzed for deadlock situations.
By being proactive in detecting deadlocks and utilizing tools like jstack , you can quickly identify and address potential issues in your Java code.
Remember, when it comes to deadlocks, prevention is key. Be mindful of your resource acquisition order and avoid circular wait conditions. Additionally, consider using concurrency utilities like ReentrantLock and Semaphore to manage locks effectively.
How to Resolve Deadlocks
To resolve deadlocks, there are two main strategies you can employ: breaking the deadlock cycle and refactoring the code to eliminate circular wait conditions.
Breaking the deadlock cycle involves identifying the resources involved in the deadlock and implementing a strategy to break the cycle.
One approach is to define a global ordering of resources and ensure that all threads acquire resources in the same order. By doing so, you eliminate the possibility of circular wait and allow the threads to proceed without deadlock.
Here's an example of how you can break the deadlock cycle:
In this example, we have modified the code to ensure that both method1 and method2 acquire resources in the same order: resource1 followed by resource2 . By maintaining this consistent lock ordering across all methods, we break the deadlock cycle and allow the threads to execute without deadlock.
Another strategy is to refactor the code to eliminate circular wait conditions. This involves restructuring the code to remove the dependency between resources that leads to deadlock. By carefully analyzing the resource dependencies and redesigning the code, you can eliminate the possibility of circular wait and prevent deadlocks.
Here's an example:
In this refactored code, we have removed the nested locks and ensured that each resource is acquired and released independently. By doing so, we eliminate the possibility of circular wait and mitigate the risk of deadlock.
How to Prevent Deadlocks
Avoiding nested locks:.
To prevent deadlock conditions, avoid using nested locks in your code. Nested locks occur when a thread acquires a lock while holding another lock. This can lead to a situation where multiple threads are waiting for each other to release the locks they hold, resulting in a deadlock.
Instead of using nested locks, consider restructuring your code to acquire locks in a more organized and controlled manner. By acquiring locks one at a time and releasing them promptly, you can minimize the chances of deadlocks occurring. Let's take a look at an example:
In this example, the code has been refactored to eliminate nested locks. Each method now acquires and releases a single lock independently. This approach ensures that threads can execute their operations without getting stuck in a deadlock situation.
Lock Ordering:
Consistent ordering of lock acquisition is another effective technique to prevent deadlocks. By establishing a predefined order for acquiring locks across all threads, you eliminate the possibility of circular wait conditions.
When designing your code, carefully analyze the dependencies between resources and determine a logical order for acquiring locks. By consistently following this order, you ensure that threads acquire locks in a predictable manner, minimizing the risk of deadlocks.
Consider the following example:
In this code snippet, both method1 and method2 acquire locks in the same order: first lock1 and then lock2 . By consistently following this lock acquisition order across all methods, you eliminate the possibility of circular wait conditions and ensure a smooth execution of concurrent code.
Timeouts and Try-Lock:
Using timeouts and try-lock mechanisms can help you avoid indefinite waiting, which can potentially lead to deadlocks.
By setting a timeout on lock acquisition attempts or using try-lock methods, you can prevent threads from waiting indefinitely for a lock to become available.
In this revised code, the methods method1 and method2 use a try-lock mechanism to acquire locks. If a lock is not immediately available, the thread does not wait indefinitely but proceeds to perform other operations. This approach helps prevent deadlocks by ensuring that threads do not get stuck waiting for locks indefinitely.
By following these practical techniques, such as avoiding nested locks, establishing consistent lock ordering, and utilizing timeouts and try-lock mechanisms, you can significantly reduce the risk of deadlocks in your Java multithreading code.
Best Practices for Avoiding Deadlocks
To minimize lock contention and avoid unnecessary locks, it is important to follow best practices in Java multithreading. By using these techniques, you can improve the efficiency and performance of your concurrent code.
Minimize the Scope of Locks
One effective practice is to minimize the scope of locks. Only synchronize the critical sections of code that require exclusive access to shared resources. By reducing the number of code blocks that are synchronized, you can minimize the chances of contention and improve the overall throughput.
Use Thread Joins Wisely
Another useful practice is to use thread joins wisely. Thread joining is a mechanism that allows one thread to wait for the completion of another thread.
But it's important to be cautious when using thread joins, as incorrect usage can lead to deadlocks. Make sure to avoid situations where threads are waiting indefinitely for each other to complete, as this can result in a deadlock. Instead, carefully design your code to ensure proper synchronization and coordination between threads.
Use Concurrency Utilities
Java provides several concurrency utilities, such as ReentrantLock , Semaphore , and other synchronization classes, that can help manage locks effectively. These utilities offer more flexibility and control over locking mechanisms compared to traditional synchronized blocks.
For example, ReentrantLock allows for finer-grained locking and enables features like fairness and interruptibility. Similarly, Semaphore provides a convenient way to control access to shared resources by limiting the number of threads allowed to enter a critical section simultaneously.
Here's an example code snippet that demonstrates the use of ReentrantLock :
In this example, the ReentrantLock is used to synchronize the critical section of code. By acquiring the lock before entering the critical section and releasing it afterward, you ensure exclusive access to shared resources.
Advanced Deadlock Topics
Deadlocks can occur not only within a single JVM but also in distributed systems. It is important to broaden our understanding of deadlocks to include their occurrence in distributed environments. In such scenarios, multiple processes or nodes may compete for shared resources, leading to potential deadlocks.
To address deadlocks in distributed systems, it is crucial to carefully design the communication and coordination mechanisms between nodes.
One effective approach is to utilize message-based communication protocols, such as asynchronous messaging or event-driven architectures. These protocols can help minimize the chances of resource contention and reduce the risk of deadlocks.
Also, modern Java features and frameworks offer valuable tools to address deadlock and concurrency issues.
For example, the CompletableFuture class provides a convenient way to handle asynchronous computations and avoid blocking threads. By leveraging CompletableFuture and other similar features, you can ensure efficient and non-blocking execution of concurrent code.
Let's take a look at an example code snippet that demonstrates the use of CompletableFuture :
In this example, the CompletableFuture class is used to perform asynchronous computations. By using the supplyAsync method, you can execute the computations in a separate thread and obtain a CompletableFuture object that represents the result. This approach helps minimize the chances of deadlocks by avoiding the blocking of threads.

Imagine you're an architect tasked with building a variety of houses, from simple one-bedroom homes to complex mansions with intricate designs.
Just like in architecture, where a set of blueprints offers proven solutions for building robust and aesthetically pleasing structures, Java Design Patterns provide software developers with time-tested methodologies and blueprints for crafting efficient and scalable software applications.
Why Java design patterns are still important in Software Development:
- Universal Blueprint for Problem-Solving : Think of design patterns as the Swiss Army knife in a developer's toolkit. They are like those secret recipes that chefs pass down through generations – each pattern is a recipe for solving a specific design problem in a proven way.
- Timeless Relevance : Like the classic principles of art that never go out of style, Java Design Patterns have stood the test of time. They are like the underlying principles of physics that remain constant, irrespective of the evolving technological landscape.
- Enhances Communication : Using design patterns is akin to musicians using sheet music. They provide a universal language for developers. This shared vocabulary cuts through complexity, much like a well-drawn map simplifies navigation in unknown terrain.
- Principles of Good Design Embedded : These patterns are more than just templates – they are a manifestation of wisdom gathered over decades, much like the principles of good governance that stand the test of time in societies.
- Maintenance and Evolution : Imagine building with LEGO blocks. Design patterns allow software to be as adaptable and maintainable as rearranging LEGO structures, ensuring that systems can evolve gracefully as requirements change.
Overview of Java Design Patterns
- Singleton Pattern : Like a unique key to an exclusive club, this pattern ensures that there's only one instance of a class, providing a single point of access to it.
- Factory Method Pattern : Picture a master artisan who creates a template for an artifact. Subsequent artisans follow this template but add their unique touch, much like this pattern allows for creating objects with a common interface.
- Abstract Factory Pattern : This pattern is like a blueprint for a series of factories; each factory creates objects that, while different, share some common traits.
- Builder Pattern : Imagine a kit for building a model airplane. You can choose different parts for different versions of the plane. The Builder pattern lets you construct complex objects step-by-step, like using such a kit.
- Prototype Pattern : This is like having a master copy, and instead of building from scratch, you make duplicates of this master copy as needed.
- Adapter Pattern : Think of this as a travel adapter that lets you charge your phone anywhere in the world; the Adapter pattern allows otherwise incompatible interfaces to work together.
- Composite Pattern : Much like a painter who sees no difference between a single brushstroke and a complex mosaic, this pattern lets you treat individual objects and compositions uniformly.
- Proxy Pattern : Like a gatekeeper who controls access to a VIP, the Proxy pattern acts as an intermediary, controlling access to another object.
- Observer Pattern : It’s like a news alert service; whenever something newsworthy happens, you get notified. This pattern allows objects to notify others about changes in their state.
- Strategy Pattern : Imagine you’re a strategist in a game, constantly changing your tactics based on the situation. The Strategy pattern lets software change its algorithms dynamically, much like a strategist adapts their approach to shifting conditions on the battlefield.
Each of these design patterns is a tool in the software developer's toolbox, ready to be deployed to tackle specific types of problems. By understanding and utilizing these patterns, developers can create software that is not only robust and efficient but also elegant and easy to maintain.
Just like the right tool can make a difficult task easy, the right design pattern can simplify complex coding challenges and lead to more effective and maintainable code.
Let's explore each of these patterns in more detail in the following sections, uncovering the secrets of their enduring power and versatility in the world of software development.
1. Singleton Pattern
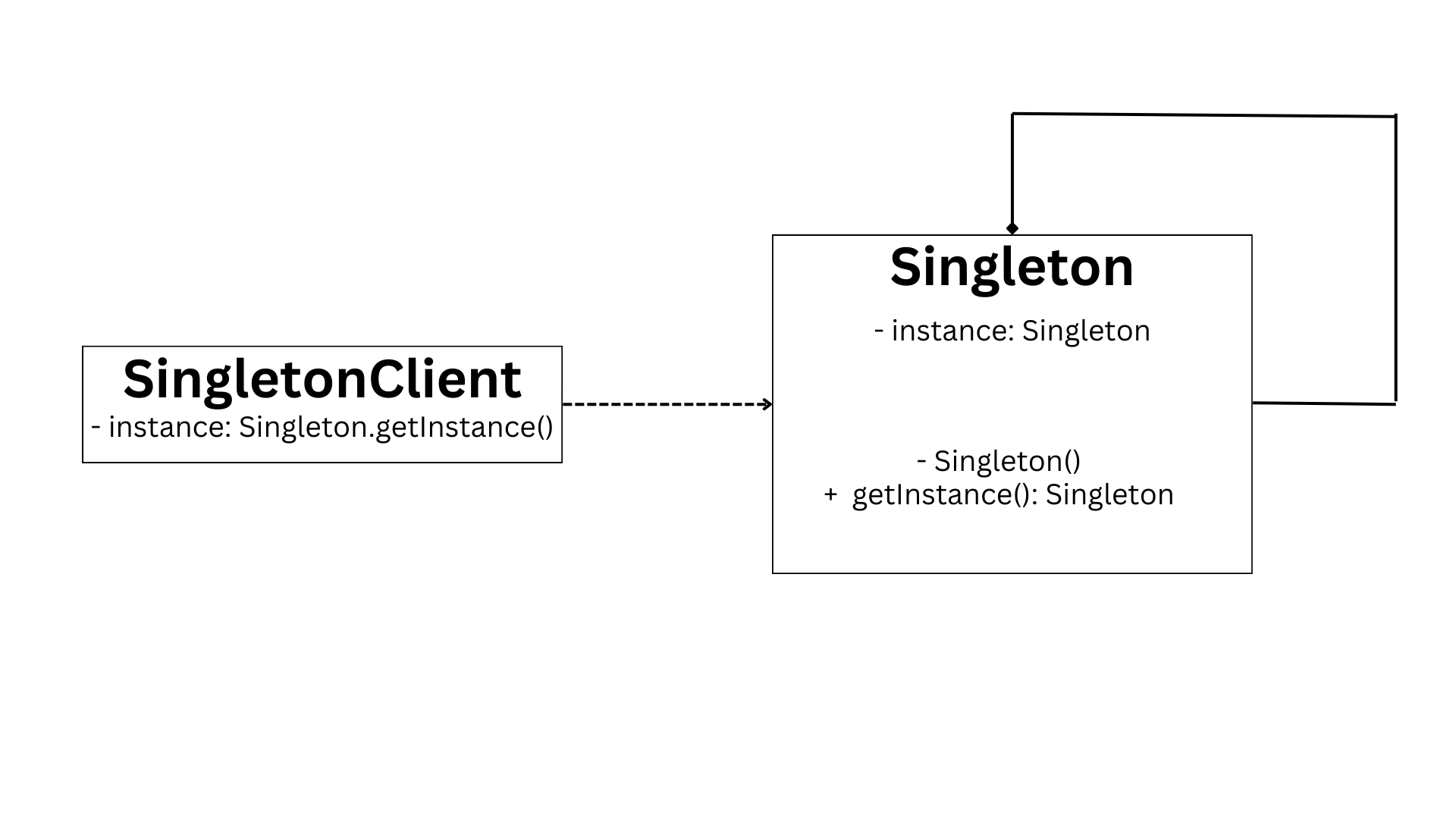
The Singleton pattern addresses the problem of managing access to a resource that should have only one instance, such as a database connection. It ensures that only one instance of a class is created and provides a global access point to that instance. The Singleton pattern restricts object creation for a class to a single instance, which is managed by the class itself.
Singleton pattern is like having a key that unlocks a special treasure room. The key is unique and there can only be one key to access the treasure room. No matter how many people have the key, they all have access to the same treasure room. This ensures that everyone uses the same instance of the treasure room and prevents multiple instances from being created.
In Java, you can implement the Singleton pattern using a private constructor, a static method to return the instance, and a private static field to hold the single instance. Here's an example:
Using the Singleton pattern provides controlled access to the single instance, ensuring that all parts of the system use the same instance. However, it can be challenging to debug due to its global nature.
When using the Singleton pattern, consider its impact on a multi-threaded environment. Synchronization is necessary to make the getInstance() method thread-safe and prevent multiple instances from being created concurrently.
Keep in mind that design patterns are not strict rules to follow, but rather guidelines that can be adapted to fit your needs. Use them wisely and consider the trade-offs they entail in terms of complexity and maintainability.
2. Factory Method Pattern
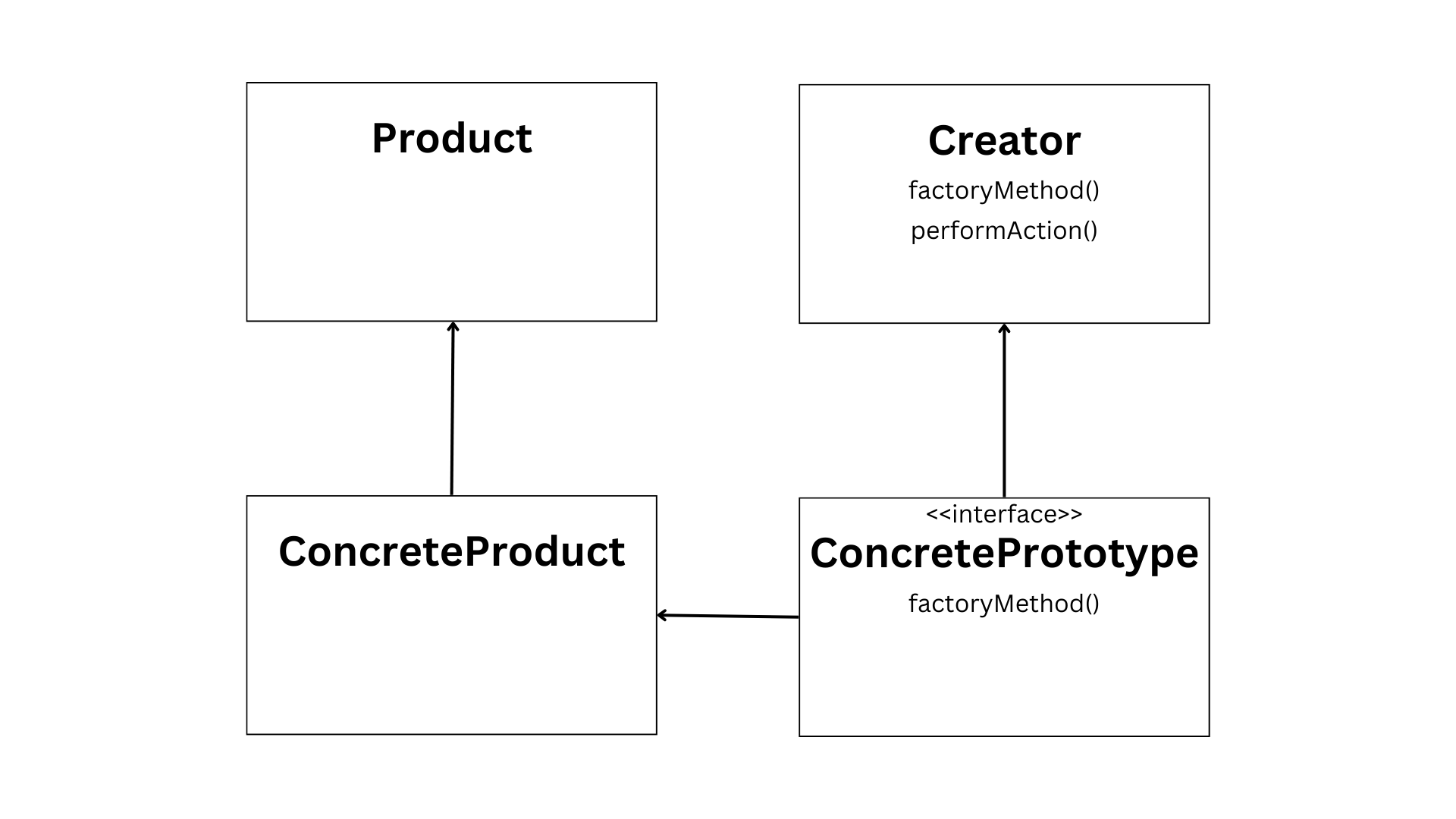
The Factory Method pattern addresses the need for creating objects through an interface while allowing subclasses to determine the specific type of objects to be instantiated. It promotes loose coupling by delegating the responsibility of object creation to subclasses.
Imagine a scenario where different chefs are preparing their own versions of a dish. Each chef represents a subclass in the Factory Method pattern, and the dish represents the object being created. The interface acts as the recipe or guidelines for creating the dish.
Here's an example in Java:
In this example, the Product interface defines the method use() , which represents the behavior of the created objects. The ConcreteProductA and ConcreteProductB classes implement this interface and provide their own implementations of the use() method.
The Creator class is an abstract class that acts as the factory. It declares the createProduct() method, which is responsible for creating the specific type of product. The doSomething() method demonstrates how the factory method is used to create and use the product.
By using the Factory Method pattern, you gain flexibility in object creation. You can easily introduce new subclasses to create different types of products without modifying the existing code. But keep in mind that introducing too many subclasses can introduce complexity and make the code harder to maintain.
An analogy for the Factory Method pattern is like having a restaurant with different chefs specializing in various dishes. The restaurant provides the interface, specifying the general guidelines for creating the dishes. Each chef represents a subclass that creates their unique version of the dish based on the provided guidelines.
Design patterns are not strict rules to follow, but rather guidelines that can be adapted to fit your needs. Use them wisely, considering the trade-offs they entail in terms of complexity and maintainability.
3. Abstract Factory Pattern
The Abstract Factory pattern addresses the problem of creating families of related or dependent objects without specifying their concrete classes. It allows the creation of objects through interfaces, promoting consistency among products while allowing flexibility in their implementation.
Imagine different car factories producing various car models. Each factory represents a concrete factory in the Abstract Factory pattern, and the car models represent the related objects being created. The abstract factory acts as the blueprint or guidelines for creating these car models.
To implement the Abstract Factory pattern in Java, you can define an abstract factory interface that declares methods for creating the related objects. Each concrete factory implements this interface and provides its own implementation of the creation methods. The product interfaces represent the different types of objects that can be created by the factories.
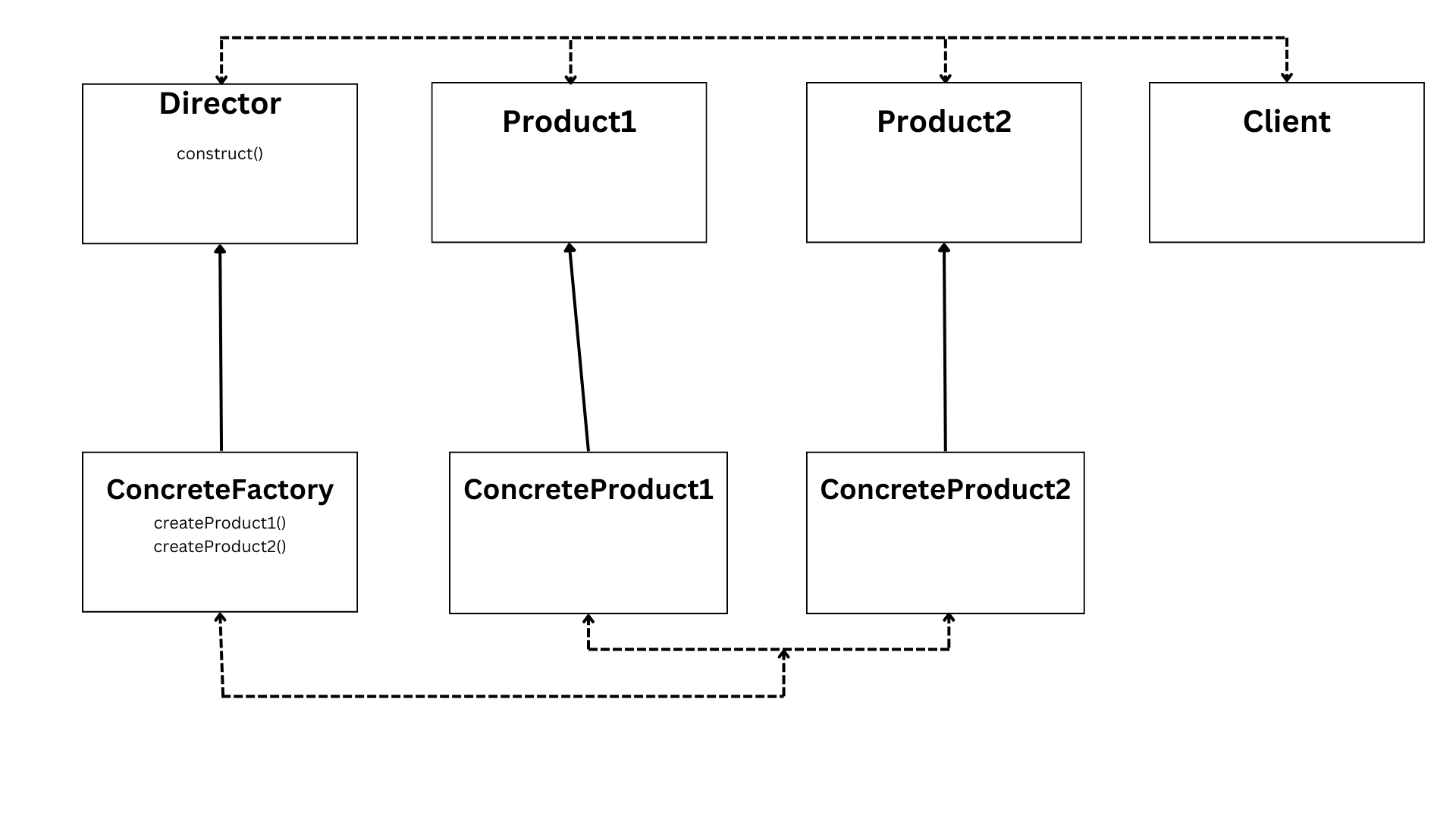
In this example, the AbstractFactory interface declares methods for creating ProductA and ProductB objects. The ConcreteFactory1 and ConcreteFactory2 classes implement this interface and provide their own implementations of the creation methods.
The ProductA and ProductB interfaces represent the different types of objects that can be created by the factories. The ConcreteProductA1 , ConcreteProductA2 , ConcreteProductB1 , and ConcreteProductB2 classes implement these interfaces and provide their own implementations of the behavior.
By using the Abstract Factory pattern, you can create families of related objects without specifying their concrete classes. This promotes consistency among the created objects and allows for easy interchangeability between different implementations. But keep in mind that introducing too many concrete factories and products can increase complexity, so use this pattern judiciously.
4. Builder Pattern
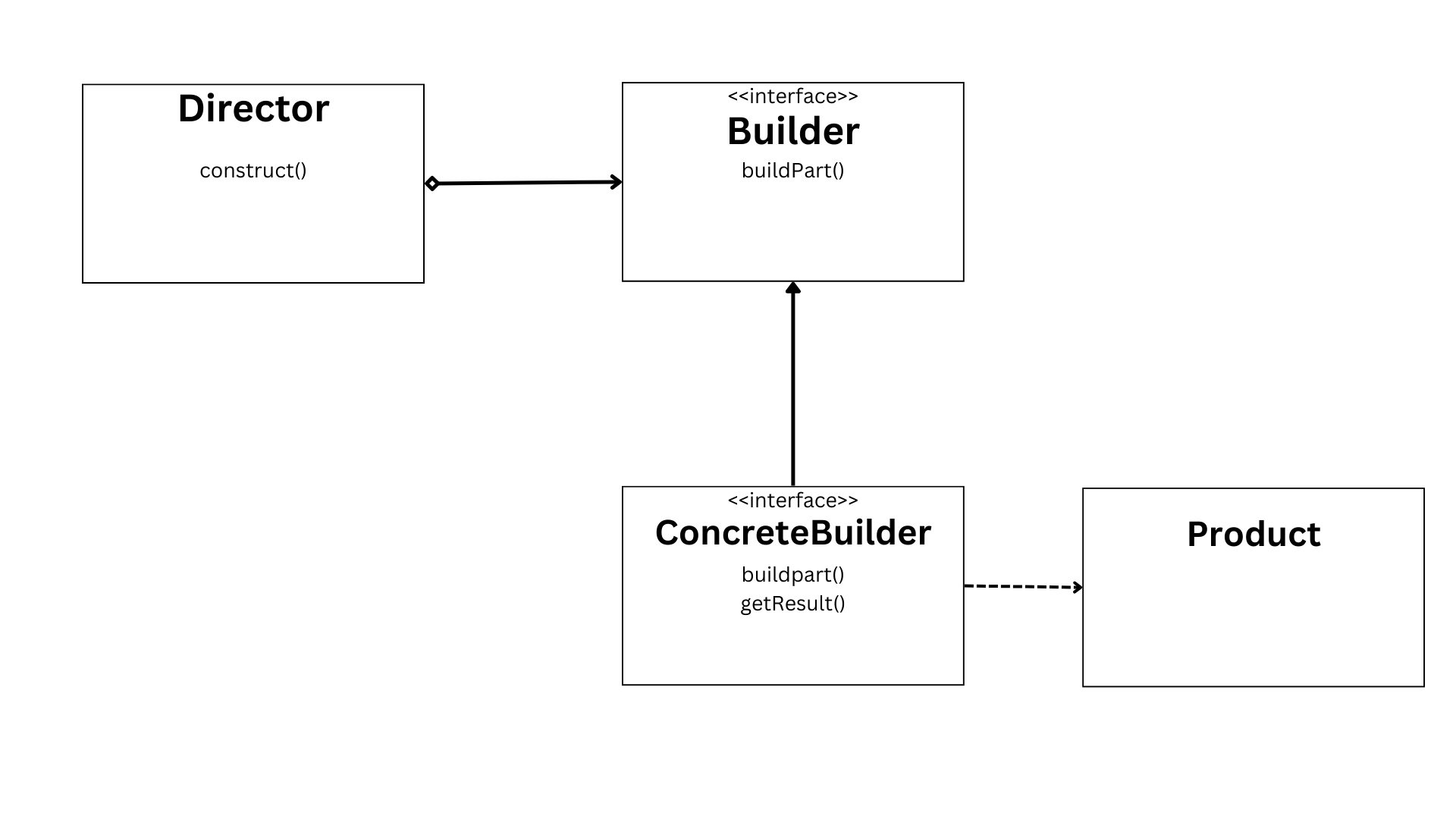
The Builder pattern is a creational design pattern that solves the problem of creating complex objects with multiple parts and configurations. It separates the construction of an object from its representation, allowing step-by-step creation of complex objects.
Imagine building a house with different construction plans. Each plan represents a concrete builder in the Builder pattern, and the house represents the complex object being created. The director acts as the blueprint or guidelines for constructing the house.
To implement the Builder pattern in Java, you can define a builder interface that declares methods for building different parts of the object. Each concrete builder implements this interface and provides its own implementation of the construction methods. The director class coordinates the construction process by invoking the builder's methods.
In this example, the Builder interface declares methods for building different parts of the complex object. The ConcreteBuilder class implements this interface and provides its own implementation of the construction methods. The Director class coordinates the construction process by invoking the builder's methods in a specific order.
By using the Builder pattern, you have more control over the construction of complex objects, allowing you to build them step by step. This pattern is particularly useful when creating objects with many optional or varied parts. However, keep in mind that introducing too many builders can increase complexity, so use this pattern judiciously.
5. Prototype Pattern
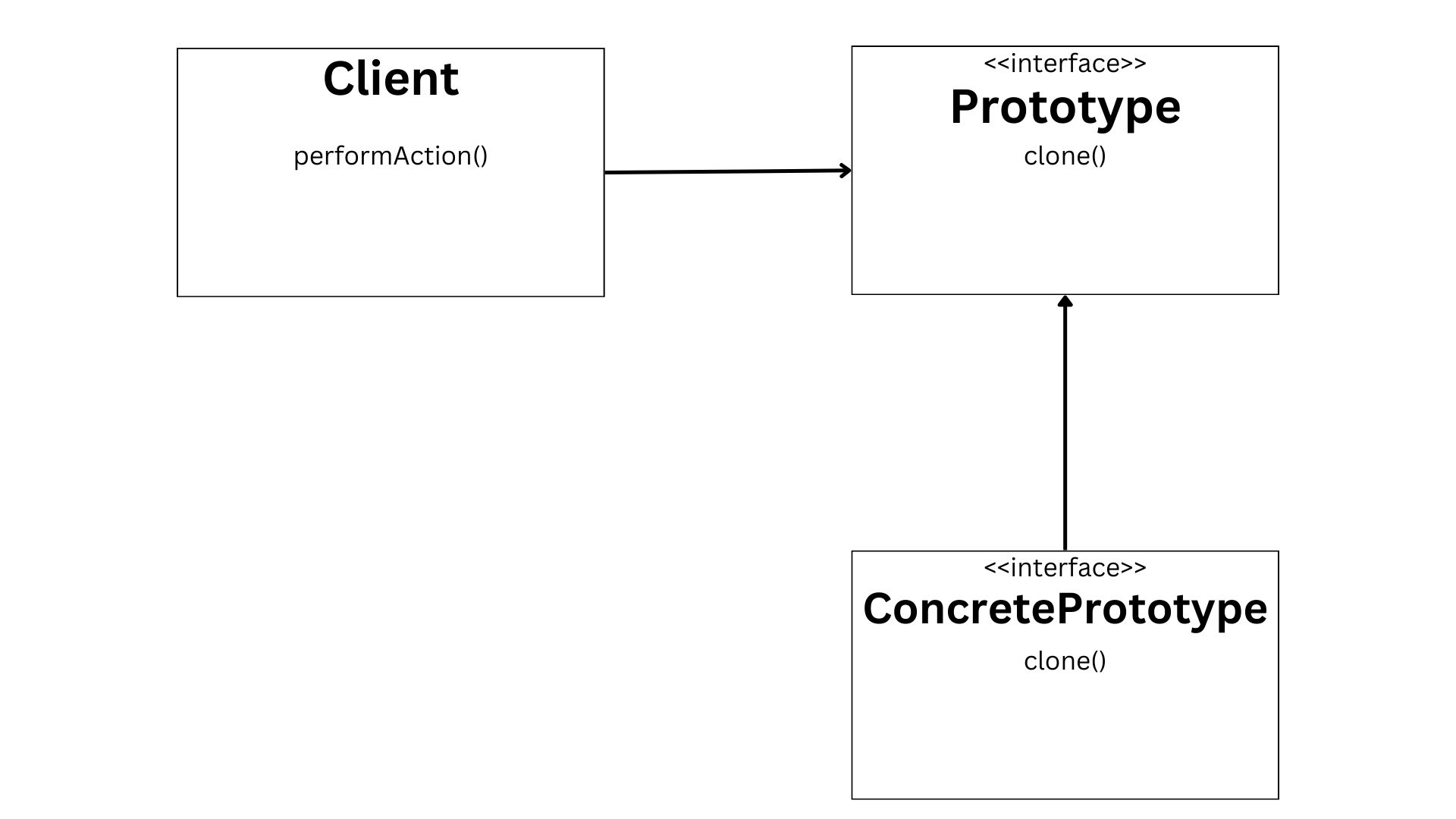
The Prototype pattern addresses the need for copying or cloning objects instead of creating new instances. It allows for the creation of new objects by copying an existing object, utilizing a prototype instance. This pattern consists of a prototype interface and concrete prototypes that implement the interface.
To understand the Prototype pattern, think of it as making photocopies of a document. The original document serves as the prototype, and the copies are created by simply duplicating the original. Similarly, the Prototype pattern allows for efficient cloning of objects by utilizing an existing instance as a blueprint for creating new instances.
In Java, you can implement the Prototype pattern by defining a prototype interface that declares a method for cloning the object. Each concrete prototype class then implements this interface and provides its own implementation of the cloning method. Here's an example:
In this example, the Prototype interface declares the clone() method for cloning the object. The ConcretePrototype class implements this interface and overrides the clone() method to perform a shallow copy of the object. The Main class demonstrates how to use the Prototype pattern by creating a concrete prototype and cloning it to obtain a new instance.
When using the Prototype pattern, keep in mind that the cloning process can become complex when involving deep cloning, where all the object's references are also cloned. It's important to handle any clone exceptions that may occur.
6. Adapter Pattern
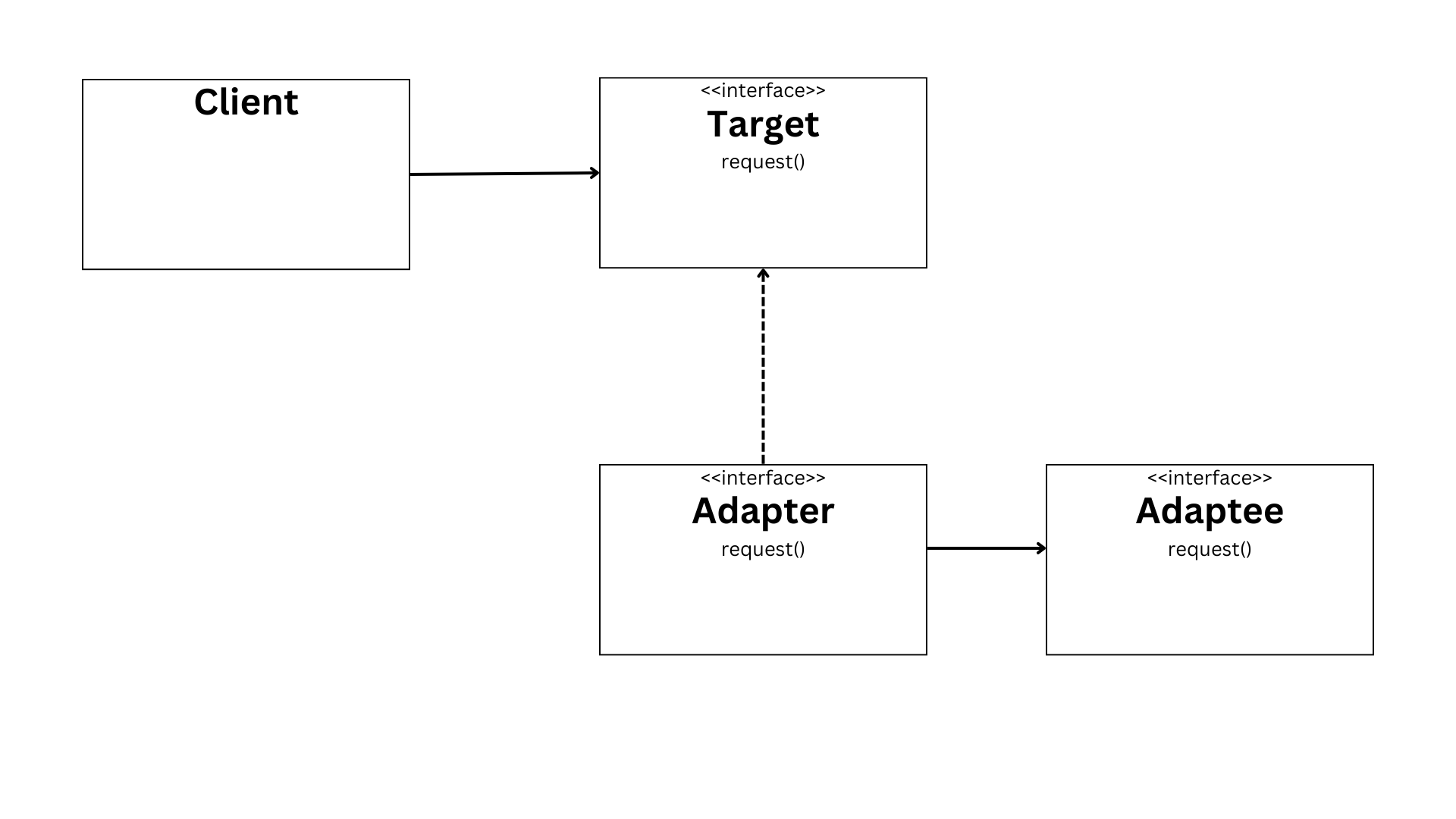
The Adapter pattern solves the problem of incompatible interfaces between classes, allowing them to collaborate effectively. It achieves this by adapting one interface to another using a middle layer called the adapter. The components involved in this pattern are the Adapter, Adaptee, and Target interface.
To understand the Adapter pattern, consider power socket adapters for different country plugs. The adapter serves as a bridge between the incompatible plug and the socket, allowing them to work together.
Similarly, the Adapter pattern enables collaboration between classes with incompatible interfaces by providing a common interface through the adapter.
Here's an example of how the Adapter pattern can be implemented in Java:
In this example, the LegacyCode interface represents the existing code with its own legacy method. The LegacyCodeImpl class implements this interface and provides the implementation of the legacy method.
The NewCode interface represents the desired new interface for the client code. The Adapter class implements this interface and contains a reference to the LegacyCode object. It adapts the new method to the existing legacy code by invoking the legacy method inside the new method.
By using the Adapter pattern, you can integrate legacy code or collaborate with classes that have incompatible interfaces. The adapter acts as a translator, enabling communication between the different components. Remember to choose meaningful names for the classes and interfaces to improve code readability.
When applying the Adapter pattern, consider the trade-offs it entails. While it allows collaboration between incompatible interfaces, it introduces an additional layer of complexity. Use this pattern judiciously and consider the specific needs of your project.
7. Composite Pattern
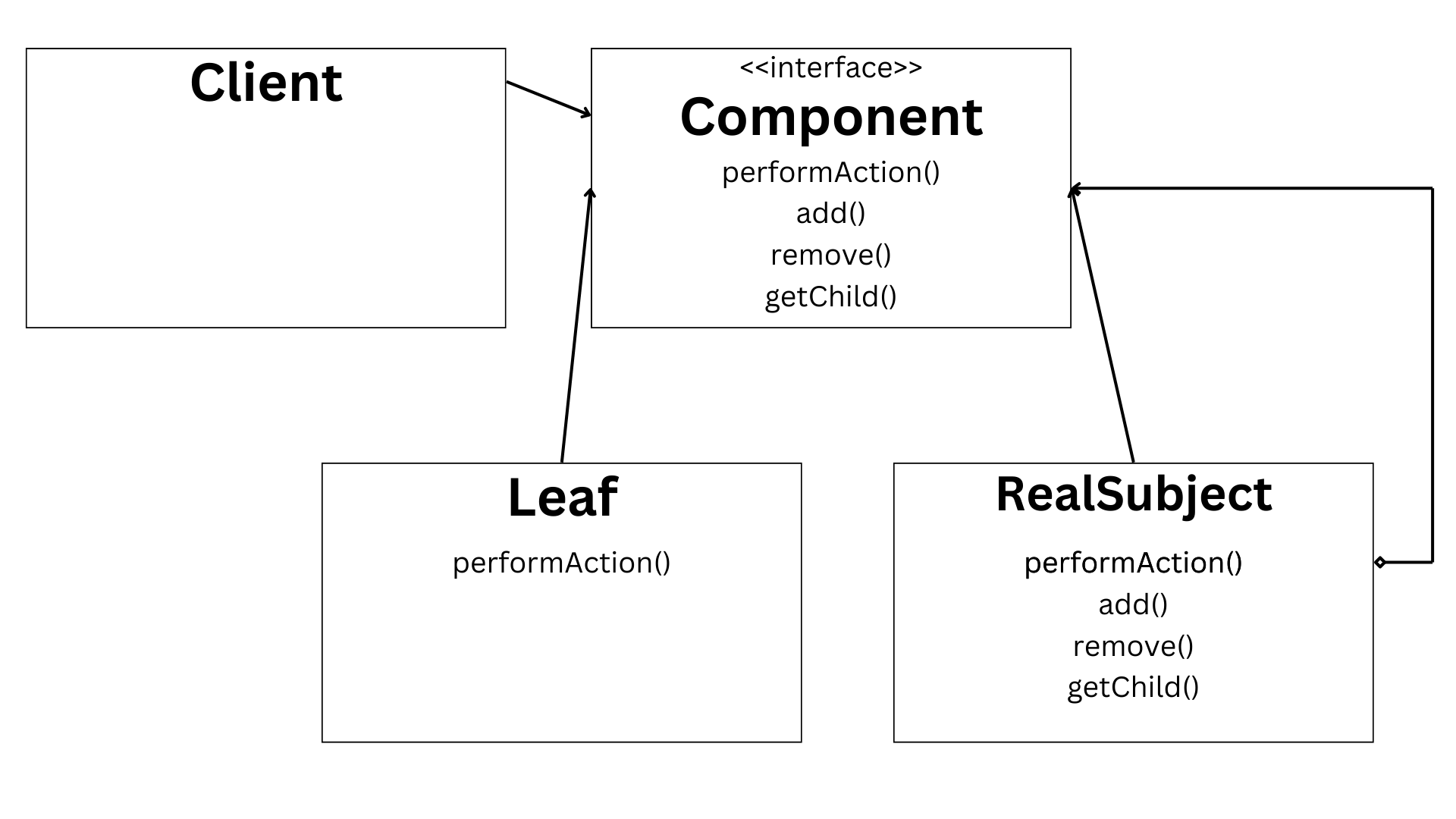
The Composite pattern addresses the problem of treating individual objects and compositions of objects uniformly. It allows us to create tree-like structures to represent part-whole hierarchies.
In this pattern, we have two types of objects: composite objects and leaf objects. Composite objects can contain other objects, including both composite objects and leaf objects. Leaf objects, on the other hand, are the building blocks of the hierarchy and cannot contain other objects.
To understand this pattern, imagine a file system where we have nested folders. The folders represent composite objects, while the files represent leaf objects. By treating folders and files uniformly, we can perform operations on them regardless of their specific type.
Here's an example implementation in Java:
In this example, the Component interface declares the operation() method that represents the operation to be performed on both composite objects and leaf objects. The Composite class implements this interface and contains a list of child components. It provides methods to add and remove child components and overrides the operation() method to perform the operation on itself and its children.
The Leaf class also implements the Component interface and provides its own implementation of the operation() method.
By using the Composite pattern, we can simplify client code by treating individual objects and compositions of objects uniformly. But we should be cautious not to make the design overly general, as it may introduce unnecessary complexity.
8. Proxy Pattern
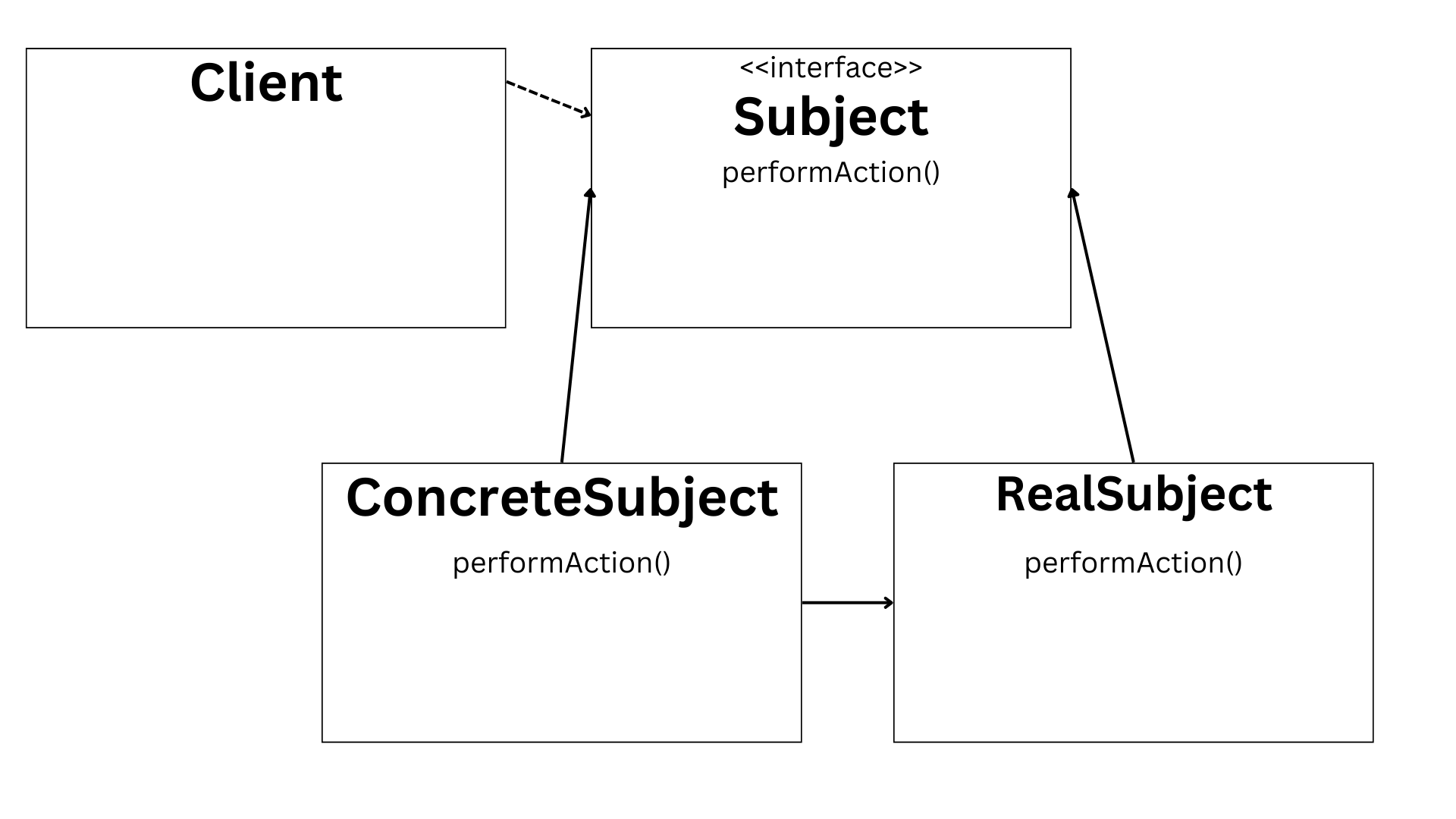
The Proxy pattern is a structural design pattern that provides a placeholder for another object. It is used to control access to an object or delay its instantiation. A common example is a bank teller acting as a proxy for bank account transactions.
To understand the Proxy pattern, let's consider a scenario where we want to access a resource-intensive object, such as a large image or a remote database. Instead of directly accessing the object, we can use a proxy to control the access and provide additional functionality if needed.
In the Proxy pattern, we have three main components: the Proxy, the Subject interface, and the RealSubject. The Proxy class acts as a middleman between the client and the RealSubject. It controls access to the RealSubject and provides any additional logic or checks before delegating the request.
In this example, the Subject interface declares the common method for the request. The RealSubject class implements this interface and provides the actual implementation of the request. The Proxy class also implements the Subject interface and acts as a proxy for the RealSubject.
When the client makes a request through the Proxy, the Proxy checks if the RealSubject has been instantiated. If not, it creates an instance of the RealSubject. The Proxy can also perform additional checks or logic before delegating the request to the RealSubject.
The Proxy pattern provides several advantages, such as controlling access to the real object, delaying the instantiation of the real object until it is actually needed, and providing additional functionality or checks. But it can introduce latency due to the extra layer of indirection.
It's important to note that the Proxy pattern is different from the Adapter pattern, which is used to bridge incompatible interfaces. The Proxy acts as a placeholder or wrapper for the real object, while the Adapter provides a different interface for an existing object.
The Proxy pattern is a powerful tool for controlling access to objects or delaying their instantiation. By using a proxy, you can add extra functionality, perform checks, or provide a simplified interface for the client. Just be cautious of the potential latency introduced by the proxy.
9. Observer Pattern
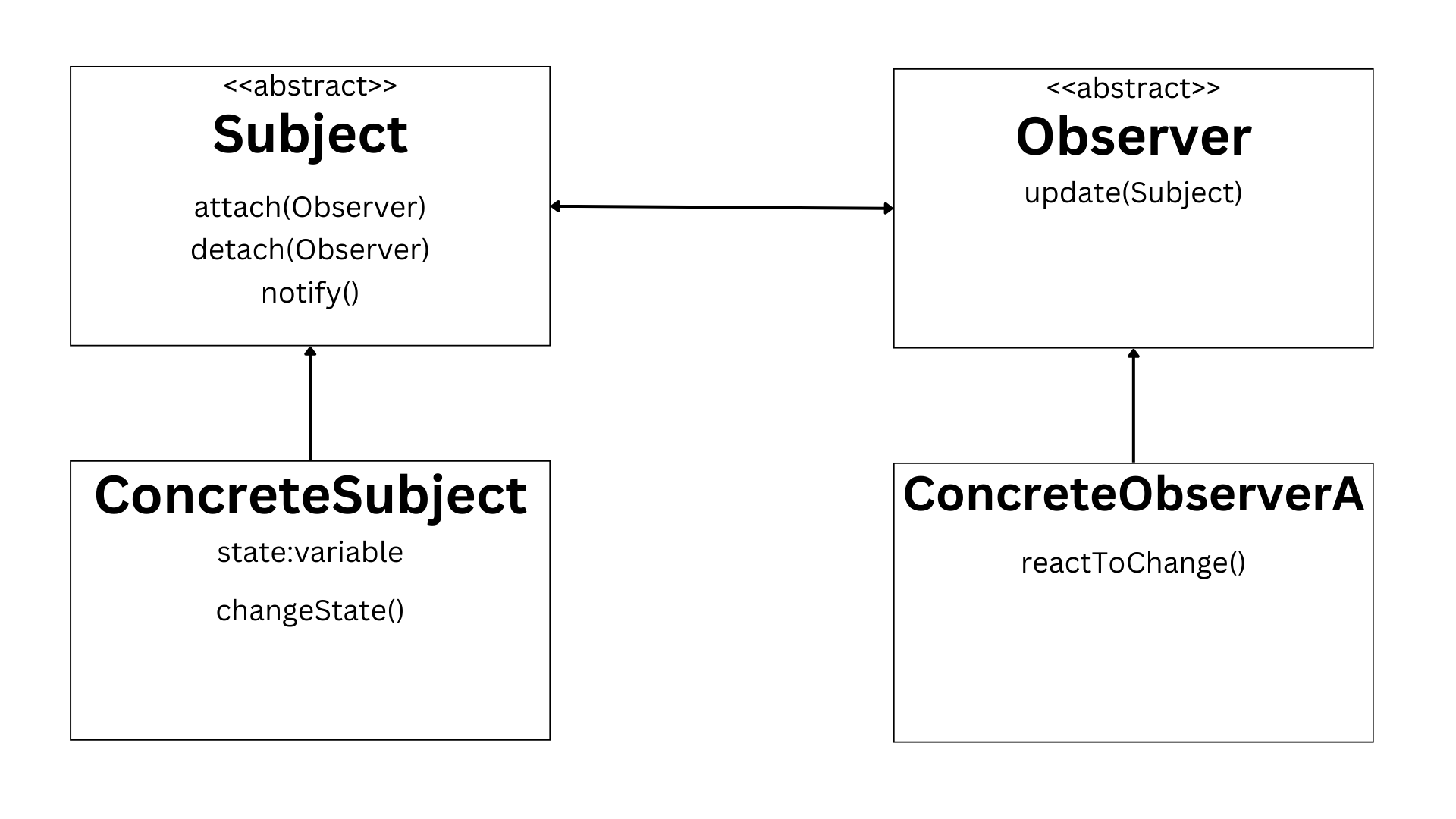
The Composite pattern addresses the need to treat individual objects and compositions of objects uniformly, creating a tree-like structure to represent part-whole hierarchies. This pattern is useful when we want to perform operations on objects regardless of their specific type, such as in a file system where we have folders (composite objects) and files (leaf objects).
To implement the Composite pattern in Java, we can define a Component interface that declares an operation() method. The Composite class represents the composite object and maintains a list of child components. It provides methods to add and remove components, as well as an implementation of the operation() method that calls the operation() method on each child component. The Leaf class represents the leaf object and provides its own implementation of the operation() method.
Here's an example code snippet:
By using the Composite pattern, we can treat individual objects and compositions of objects uniformly, simplifying the code and providing flexibility. But it's important to note that adding too many levels of nesting can make the code more complex and harder to maintain. Therefore, it's important to strike the right balance and use this pattern judiciously.
10. Strategy Pattern
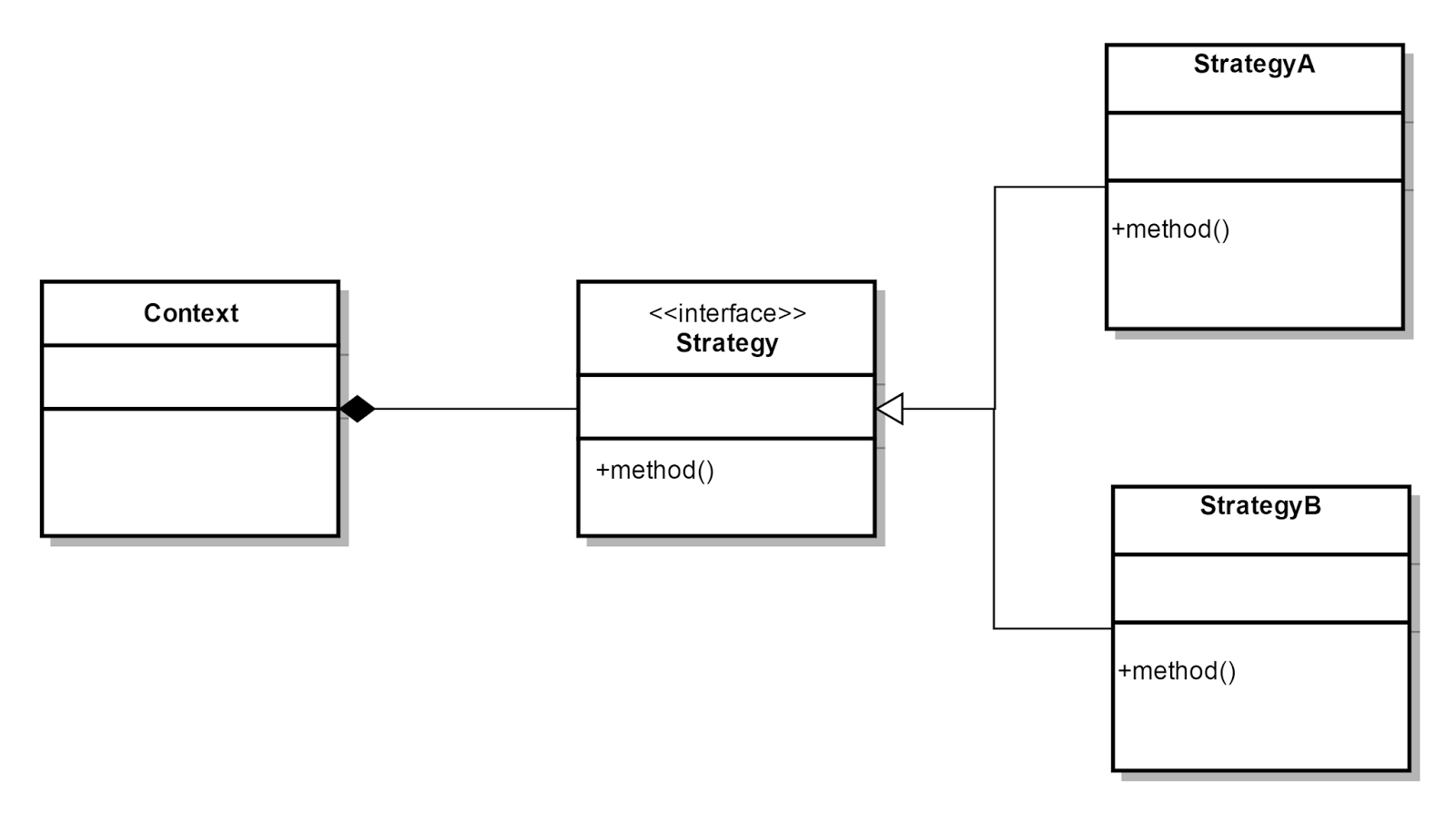
The Strategy pattern is a behavioral design pattern that allows for selecting algorithms or behaviors at runtime. It addresses the need to choose different strategies based on the situation, providing flexibility and interchangeability.
To understand the Strategy pattern, let's consider a real-world example of choosing transportation methods. Depending on the situation, we may need to select a car, a bike, or a bus. Each transportation method represents a strategy, and the situation represents the context.
In Java, we can implement the Strategy pattern by creating a Context class, a Strategy interface, and multiple ConcreteStrategy classes. The Context class encapsulates the algorithms or behaviors and provides a method to change the strategy at runtime. The Strategy interface defines the contract for the different strategies, and the ConcreteStrategy classes implement specific strategies.
In this example, the Strategy interface declares the performAction() method, which represents the behavior of the different strategies. The ConcreteStrategyA and ConcreteStrategyB classes implement this interface and provide their own implementations of the strategies.
The Context class holds a reference to the current strategy and provides methods to set the strategy and execute it. By changing the strategy at runtime, we can easily switch between different behaviors.
When using the Strategy pattern, it's essential to identify the problem and choose the appropriate strategies. Consider the advantages and trade-offs, such as flexibility and potential complexity due to multiple strategy classes.

Java optimization is a crucial aspect of developing high-performance applications. In this guide, we will explore the various techniques and tools that can help improve the speed and efficiency of your Java code.
When it comes to understanding Java performance, it is essential to grasp the basics. You should be familiar with key performance metrics and be able to identify common performance bottlenecks. By analyzing and addressing these bottlenecks, you can significantly enhance the overall performance of your application.
One effective way to optimize your Java code is through computational optimization. This involves using efficient data structures and algorithms to reduce CPU cycle consumption. By carefully selecting the right algorithms and optimizing their implementation, you can achieve significant performance improvements.
Another important aspect of Java optimization is resource conflict optimization. This involves managing multi-threaded environments and implementing synchronization and locking mechanisms appropriately. By ensuring proper coordination among threads, you can avoid conflicts and improve the efficiency of your code.
Additionally, JVM optimization plays a crucial role in enhancing Java performance. By tuning JVM parameters and configuring garbage collectors, you can optimize memory usage and reduce overhead. Understanding the behavior of garbage collection and leveraging profiling and benchmarking techniques can further aid in optimizing your Java code.
To assist you in the optimization process, there are various tools available. Code analysis tools can help identify potential issues and provide suggestions for improvement. Tools for garbage collection analysis, continuous profiling, JIT compilation analysis, benchmarking, and real-time monitoring can also be valuable in identifying performance bottlenecks and optimizing your code.
In order to achieve the best results, it is important to follow best practices in Java optimization. Writing clean and maintainable code, avoiding common pitfalls, and implementing efficient memory management strategies are essential.
Throughout this chapter, we will explore real-world case studies and provide practical advice based on experience. We will also touch upon advanced topics such as optimizing Java in cloud environments and Java performance in microservices architecture.
By applying these techniques and insights, you can optimize your Java code for speed and efficiency, leading to enhanced performance and better user experiences.
Java Optimization Techniques
When it comes to optimizing your Java code, there are several key areas to focus on: computational optimization, resource conflict optimization, algorithm code optimization, and JVM optimization.
Computational optimization
In computational optimization, one effective approach is to utilize efficient data structures and algorithms.
By carefully selecting the right data structures and algorithms for your specific use case, you can significantly reduce CPU cycle consumption and improve the overall performance of your code.
Let's take a look at an example:
Resource conflict optimization
In resource conflict optimization, it is crucial to effectively manage multi-threaded environments and implement synchronization and locking mechanisms.
By ensuring proper coordination among threads, you can avoid conflicts and enhance the efficiency of your code.
Here's an example to illustrate this concept:
Algorithm code optimization
Algorithm code optimization involves selecting the right algorithms and leveraging profiling and benchmarking techniques.
By analyzing the performance characteristics of different algorithms and fine-tuning their implementation, you can achieve significant performance improvements.
JVM Optimization
JVM optimization plays a crucial role in enhancing Java performance. By tuning JVM parameters and configuring garbage collectors, you can optimize memory usage and reduce overhead.
It is essential to understand the behavior of garbage collection and leverage profiling and benchmarking techniques to fine-tune your Java code. Remember, JVM optimization can have a significant impact on the overall performance of your application.
By focusing on these key areas of optimization and applying the techniques discussed, you can greatly improve the speed and efficiency of your Java code.
Java Optimization Tools
When it comes to optimizing your Java code, several key tools deserve your attention. Let's delve into each of them and explore practical advice to improve performance.
Code Analysis Tools like Checkstyle, PMD, and FindBugs (now SpotBugs).
Application: These tools statically analyze your Java code to catch style discrepancies, potential bugs, and anti-patterns.
For instance, Checkstyle can enforce a coding standard by checking for deviations from preset rules. PMD finds common programming flaws like unused variables, empty catch blocks, unnecessary object creation, and so on. SpotBugs scans for instances of bug patterns/potential errors that are likely to lead to runtime errors or incorrect behavior.
Garbage Collection Analysis Tools like VisualVM, GCViewer, and JClarity's Censum.
Application: These tools help in analyzing Java heap dumps and garbage collection logs.
VisualVM can attach to a running JVM and monitor object creation and garbage collection, which helps in tuning the heap size and selecting the appropriate garbage collector. GCViewer can read JVM garbage collection logs to visualize and analyze garbage collection processes. Censum can interpret verbose garbage collection logs to recommend optimizations.
Continuous Profiling Tools like YourKit, JProfiler, and Java Flight Recorder (JFR).
Application: Continuous profiling tools are used to identify performance issues in a running Java application.
YourKit provides powerful on-demand profiling of both CPU and memory usage, as well as extensive analysis capabilities. JProfiler offers a live profiling of a local or remote session, and can track down performance bottlenecks, memory leaks, and threading issues. Java Flight Recorder, part of the JDK, collects detailed runtime information about the JVM which can be analyzed later.
JIT Compilation Analysis Tools like JITWatch, Oracle Solaris Studio Performance Analyzer.
Application: These tools help developers understand the intricacies of the JIT compiler.
JITWatch is a tool that analyzes the Just-In-Time (JIT) compilation process of the HotSpot JVM. It visualizes the compiler optimizations and provides feedback on how the JIT compiler is translating bytecode into machine code. The Performance Analyzer can track the performance of applications and can show how code is being executed, allowing developers to see which methods are being JIT-compiled and how often.
Benchmarking Tools like JMH (Java Microbenchmark Harness), Google Caliper.
Application: Benchmarking tools like JMH are designed for benchmarking code sections (usually methods) to measure their performance.
JMH is specifically tailored for Java and other JVM languages and allows you to define a benchmarking job and measure its performance under different conditions. Google Caliper is another benchmarking framework that's designed to help you record, analyze, and compare the performance of your Java code.
Monitoring Tools like Nagios, Prometheus with JMX exporter, and New Relic.
Application: These tools are used for the real-time monitoring of Java applications.
Nagios can monitor JVM metrics and provide alerts based on thresholds. Prometheus can scrape metrics exposed by JVM using JMX exporter and allows for powerful querying. New Relic provides an APM (Application Performance Management) tool that offers real-time insights into your application's operation, with detailed transaction traces, error tracking, and application topology mapping.
Let's look at how you can use each type of tool to better optimize your Java code.
How to Use Code Analysis Tools
Static code analysis plays a crucial role in identifying potential issues and suggesting improvements in your Java code. By utilizing popular Java code analysis tools, you can gain valuable insights into code quality and ensure adherence to best practices.
Static Code Analysis Example:
How to Use Garbage Collection Analysis Tools
Understanding garbage collection in Java is essential for optimizing memory usage and reducing overhead. By employing tools specifically designed for analyzing garbage collection behavior, you can fine-tune your Java code and optimize memory allocation.
Garbage Collection Analysis Example:
How to Use Continuous Profiling Tools
Continuous profiling enables you to gather real-time performance data and identify performance bottlenecks in your Java application. By using recommended profiling tools, you can gain insights into CPU usage, memory allocation, and method-level performance, allowing you to make targeted optimizations.
Continuous Profiling Example:
How to Use JIT Compilation Analysis Tools
Just-in-time (JIT) compilation is a crucial component of Java performance. Exploring JIT compilation behavior through dedicated tools allows you to understand how your code is optimized at runtime. By analyzing JIT compilation, you can make informed decisions to improve performance.
JIT Compilation Analysis Example:
How to Use Benchmarking Tools
Benchmarking Java applications provides valuable performance data and helps you identify areas for improvement. Effective benchmarking tools allow you to compare different approaches, algorithms, or libraries, enabling you to make informed decisions to enhance performance.
Benchmarking Example:
How to Use Monitoring Tools
Real-time monitoring of Java applications provides crucial insights into system behavior and performance metrics. Top Java monitoring tools enable you to track key performance indicators, detect anomalies, and troubleshoot issues promptly, ensuring optimal performance.
Remember, while utilizing these tools is essential, it's equally important to focus on writing clean and maintainable code, avoiding common pitfalls, and implementing efficient memory management strategies.
Best Practices in Java Optimization
Writing clean and maintainable code is crucial for optimizing Java applications. Adhering to principles of modularity and encapsulation, breaking down code into reusable modules, and encapsulating data and functionality within classes are key practices.
You should also avoid excessive object creation, choose efficient data structures, and employ memory management strategies like lazy initialization and resource cleanup.
Example of clean and maintainable code:
Here's an example code snippet illustrating the importance of clean and maintainable code:
The provided Java code is a good example of clean code for several reasons:
- Single Responsibility Principle : The OrderProcessor class has a single responsibility – to process orders. This makes the class easier to maintain and test.
- Use of meaningful names : The class name OrderProcessor and method name processOrders clearly indicate their purpose. The variable names such as orderRepository and orders are also self-explanatory.
- Dependency Injection : The OrderRepository is passed into the OrderProcessor via its constructor, which is a form of Dependency Injection. This makes the code more flexible and easier to test.
- Code readability : The code is well-structured and easy to read. The use of whitespace and indentation improves readability.
- Error handling : The code checks if an order is valid before processing it, which is a good practice for error handling.
Overall, this code is clean because it is easy to understand, maintain, and extend.

Chapter 6: Concurrent Data Structures and Algorithms for High-Performance Applications
In the fast-paced world of computing, where speed and efficiency are paramount, concurrent data structures and algorithms play a crucial role in achieving high performance.
Concurrency allows multiple tasks to execute simultaneously, maximizing resource utilization and enabling applications to handle complex workloads efficiently.
Understanding the fundamentals of concurrency in computing is essential for developers seeking to optimize their applications. By harnessing the power of parallelism, concurrent data structures and algorithms enable tasks to be executed concurrently, reducing overall execution time and improving responsiveness.
Key Concurrent Data Structures
Lock-based data structures provide a mechanism for ensuring mutual exclusion and data consistency in concurrent applications. They work by acquiring a lock or mutex before accessing shared data, ensuring that only one thread can access the data at a time. Common lock-based structures include locks, mutexes, and semaphores.
Lock-free data structures, on the other hand, offer a way to achieve concurrency without the use of locks. They utilize atomic operations and memory fences to ensure data consistency and avoid the need for explicit locking. Examples of lock-free structures include lock-free queues and lock-free stacks.
Wait-free data structures take concurrency a step further by guaranteeing that every thread makes progress even if other threads are stalled or delayed. They are designed to ensure that no thread is blocked indefinitely, making them suitable for real-time systems and high-performance applications.
We'll see some examples of these in a minute.
Remember, when utilizing lock-based data structures, it is crucial to handle potential issues such as deadlocks and contention. Always aim to strike a balance between concurrency and performance, ensuring efficient utilization of resources.
When working with lock-free and wait-free data structures, it is important to understand their limitations and use them judiciously. These structures can provide significant performance benefits in certain scenarios, but they may also introduce additional complexity and require careful synchronization.
By leveraging the appropriate concurrent data structures and algorithms in your Java applications, you can optimize performance, enhance responsiveness, and achieve efficient resource utilization.

Essential Concurrent Algorithms
In high-performance applications, concurrent data structures and algorithms are essential for achieving optimal speed and efficiency. They enable tasks to be executed simultaneously, maximizing resource utilization and improving responsiveness.
One important aspect of concurrency is task scheduling algorithms. These algorithms play a critical role in managing concurrent tasks. They determine the order in which tasks are executed and ensure efficient utilization of resources.
Here's an example of a round-robin scheduling algorithm implemented in Java:
Synchronization algorithms are crucial for ensuring data consistency in concurrent applications. They prevent data races and conflicts by providing mechanisms for thread synchronization.
Here's an example of using locks for synchronization in Java:
Deadlock detection and resolution are vital for handling potential deadlocks in concurrent applications, as we discussed above. If you remember, deadlocks occur when two or more threads are blocked indefinitely, waiting for each other to release resources.
Here's an example of deadlock prevention using resource ordering in Java:
By leveraging the appropriate concurrent data structures, algorithms, and synchronization techniques, you can optimize the performance of your Java applications. Remember to consider the limitations and complexities of concurrent programming and aim for simplicity and efficiency in your implementation.
Examples of Lock-based, Lock-free, and Wait-free Data Structures
Concurrent data structures and algorithms play a crucial role in achieving high performance in the fast-paced world of computing. By allowing multiple tasks to execute simultaneously, concurrency maximizes resource utilization and enables efficient handling of complex workloads.
Lock-based data structure
Lock-based data structures, such as locks, mutexes, and semaphores, ensure mutual exclusion and data consistency by acquiring locks before accessing shared data.
For example, in Java, you can use a lock-based data structure like the following code snippet:
The lock variable is an instance of the ReentrantLock class from the java.util.concurrent.locks package, which is a reentrant mutual exclusion Lock with the same basic behavior and semantics as the implicit monitor lock accessed using synchronized methods and statements, but with extended capabilities.
The ReentrantLock allows more flexible structuring, may have completely different properties, and may support multiple associated Condition objects.
The use of ReentrantLock helps to ensure that the increment() operation is thread-safe. This is crucial in a multi-threaded environment to prevent race conditions.
Lock-free data structure
On the other hand, lock-free data structures, such as lock-free queues and lock-free stacks, achieve concurrency without the use of locks. They employ atomic operations and memory fences to ensure data consistency.
In this code, AtomicReference is used to ensure that the operations on the top of the stack are atomic. The push and pop methods use a loop with compareAndSet to ensure that the operation is retried if the top was modified by another thread in the meantime.
This is a simple example of a lock-free data structure that achieves concurrency without the use of locks. But it’s important to note that while lock-free data structures can improve performance in multi-threaded environments, they can be more complex to implement correctly and may not always provide the best solution depending on the specific requirements of your application. It’s always important to understand their limitations and use them judiciously.
Wait-free data structure
Wait-free data structures guarantee that every thread makes progress, even if other threads are stalled or delayed. They are suitable for real-time systems and high-performance applications.
In this code, AtomicReference is used to ensure that the operations on the head and tail of the queue are atomic.
The enqueue and dequeue methods use a loop with compareAndSet to ensure that the operation is retried if the head or tail was modified by another thread in the meantime.
This is a simple example of a wait-free data structure that guarantees that every thread makes progress, even if other threads are stalled or delayed. But it’s important to note that while wait-free data structures can improve performance in multi-threaded environments, they can be more complex to implement correctly and may not always provide the best solution depending on the specific requirements of your application. It’s always important to understand their limitations and use them judiciously.
In real-world applications, concurrent structures find applications in scenarios where high-performance and efficient resource utilization are critical. Learning from successful implementations can provide valuable insights and practical advice for optimizing your own applications.

Understanding the importance of Java security is crucial in today's digital landscape. Over the years, Java security has evolved to address emerging threats and provide robust protection for applications and data. Let's delve into these key concepts and explore their practical implications.
When it comes to Java security, you'll want to prioritize the safety of your applications and the sensitive information they handle. By implementing strong security measures, you can safeguard against unauthorized access, data breaches, and malicious attacks.
To illustrate the significance of Java security, consider the following example code snippet:
This Java code sample illustrates the significance of Java security in several ways:
- Hashing Passwords : The hashPassword method uses the MessageDigest class from the java.security package to hash passwords using the SHA-256 algorithm. Hashing passwords is a critical security practice because it means that even if an attacker gains access to the password hash, they cannot easily determine the original password.
- User Authentication : The authenticate method checks if the entered username exists in the userDatabase and if the hashed version of the entered password matches the stored hashed password. This is a basic form of user authentication, which is crucial for protecting user accounts and data.
- User Authorization : The isAuthorized method checks if the authenticated user has the necessary permissions to perform secure operations. This is an example of user authorization, which is important for ensuring that users can only perform actions they are allowed to.
- Exception Handling : The code includes exception handling to deal with potential errors, such as the NoSuchAlgorithmException that might be thrown when getting an instance of MessageDigest . Proper exception handling is important for both security and reliability.
- Secure Operations : The performSecureOperations method is a placeholder for operations that should only be performed by authorized users. Ensuring that only authorized users can perform sensitive operations is a key aspect of application security.
- Logging : The code uses a Logger to record information about authentication and authorization processes. Logging is important for monitoring and troubleshooting security-related events.
These security features are all critical for building secure Java applications. But it’s important to note that this is a simplified example and real-world applications would require additional security measures.
Through regular updates and patches, Java vulnerabilities are addressed, and new features are introduced to mitigate emerging risks. Staying up to date with the latest security practices and incorporating them into your development process is essential for maintaining a secure Java environment.
Let's dive into security principles and best practices in more detail.
What Is Java Security?
Java security refers to the measures and mechanisms in place to safeguard applications and data from unauthorized access, breaches, and malicious attacks. It encompasses a range of practices, including authentication, authorization, encryption, secure coding, and more.
By implementing robust security measures, you can create a secure environment that inspires user confidence and protects valuable information.
Core Principles of Java Security
Java security is built upon several core principles that guide the development and implementation of secure applications:
Authentication
Authentication is a fundamental aspect of cybersecurity. It serves as the first line of defense in securing sensitive resources and functionalities by ensuring that only verified users gain access. In the context of Java, there are several ways to implement authentication, each with its own significance.
Validating usernames and passwords is the most basic form of authentication. It involves checking the entered credentials against a database of registered users.
While simple, this method is susceptible to various attacks such as brute force or dictionary attacks. So it’s crucial to store passwords securely, often as hashed values rather than plain text. Java provides several libraries for secure password hashing, such as Bcrypt.
Example Code:
Multi-factor authentication (MFA) adds an extra layer of security. It requires users to provide two or more verification factors to gain access. These factors could be something the user knows (like a password), something the user has (like a hardware token or phone), or something the user is (like a fingerprint or other biometric trait).
MFA significantly improves security because even if an attacker obtains one factor (like the user’s password), they still need the other factor(s) to gain access.
External authentication systems, such as OAuth2 or OpenID Connect, allow users to authenticate using an external trusted provider (like Google or Facebook). These systems can provide a secure and user-friendly way to handle authentication, as they offload the responsibility of secure credential storage to the external provider. Java has several libraries, like Spring Security, that provide out-of-the-box support for these systems.
Authorization
Access control is a critical aspect of cybersecurity, particularly in Java applications. It involves defining and enforcing policies that determine which users have permissions to access specific resources or perform certain operations within the application.
In a typical Java application, access control can be implemented at various levels. For instance, at the method level, developers can use Java’s built-in access modifiers (public, private, protected, and package-private) to control which other classes can call a particular method. However, for more granular and dynamic access control, developers often turn to frameworks like Spring Security.
Spring Security provides a comprehensive security solution for Java applications. It includes support for both authentication (verifying who a user is) and authorization (controlling what a user can do).
For example, consider a web application where only authenticated users should be able to access certain pages. With Spring Security, developers can annotate controller methods with @PreAuthorize to specify access control rules. Here’s an example:
In this code, the @PreAuthorize annotation ensures that only users with the ‘ADMIN’ role can access the ‘admin’ page. If a user without the ‘ADMIN’ role tries to access this page, Spring Security will block the request.
This is just one example of how access control can be implemented in Java. The key is to carefully define access control policies that align with the application’s requirements and to enforce these policies consistently throughout the application. This helps to ensure that sensitive resources and operations are protected from unauthorized access, thereby enhancing the overall security of the application.
Secure Coding
Secure coding practices are essential in Java cybersecurity. They help eliminate vulnerabilities and prevent common exploits, thereby enhancing the overall security of Java applications.
Input validation is one such practice. It involves checking the data provided by users to ensure it meets specific criteria before processing it.
This is crucial because unvalidated or improperly validated inputs can lead to various types of attacks, such as SQL injection, cross-site scripting (XSS), and command injection.
In Java, you can perform input validation using various methods, such as regular expressions, built-in functions, or third-party libraries.
Here’s an example of basic input validation in Java:
In this code, the isValidUsername method checks if the provided username only contains alphanumeric characters and underscores, which is often a requirement for usernames.
Output encoding is another important secure coding practice. It involves encoding the data before sending it to the client to prevent attacks like XSS, where an attacker injects malicious scripts into content that’s displayed to other users.
Java provides several ways to perform output encoding, such as using the escapeHtml4 method from the Apache Commons Text library to encode HTML content.
Parameterized queries, also known as prepared statements, are used to prevent SQL injection attacks.
SQL injection is a technique where an attacker inserts malicious SQL code into a query, which can then be executed by the database. By using parameterized queries, you ensure that user input is always treated as literal data, not part of the SQL command.
Here’s an example of a parameterized query in Java using JDBC:
In this code, the ? is a placeholder that gets replaced with the username variable. Because the username is automatically escaped by the PreparedStatement , it’s not possible for an attacker to inject malicious SQL code via the username .
Following secure coding practices like input validation, output encoding, and using parameterized queries is crucial for preventing common exploits and enhancing the security of Java applications.
Protecting sensitive data, both at rest and in transit, is a cornerstone of cybersecurity. Encryption plays a vital role in this protection. It involves converting plaintext data into ciphertext using an encryption algorithm, rendering it unreadable to anyone without the decryption key.
In Java, the Java Cryptography Extension (JCE) provides functionalities for encryption and decryption. It supports various encryption algorithms, including AES (Advanced Encryption Standard), which is widely recognized for its strength and efficiency.
Here’s an example of how you might use AES encryption to protect data at rest in Java:
In this code, we first generate a new AES key. We then create a Cipher instance and initialize it for encryption using the generated key. Finally, we encrypt the plaintext data and print the resulting ciphertext.
When it comes to protecting data in transit, secure communication protocols like HTTPS (HTTP over SSL/TLS) are commonly used. These protocols use encryption to protect data as it travels over the network. In Java, you can use the HttpsURLConnection class or libraries like Apache HttpClient to send and receive data over HTTPS.
Managing encryption keys is another critical aspect of data protection. Keys need to be securely generated, stored, and managed. They should be rotated regularly and revoked if compromised. In Java, you can use the Java KeyStore (JKS) to securely store cryptographic keys.
Encryption is a powerful tool for protecting sensitive data in Java applications. By using strong encryption algorithms and properly managing encryption keys, you can significantly enhance the security of your data, both at rest and in transit.
Logging and Monitoring
Implementing comprehensive logging and monitoring systems is a crucial aspect of cybersecurity in Java applications. These systems serve as the eyes and ears of your application, providing visibility into its operations and helping to detect and respond to security incidents effectively.
Logging involves recording events that occur in your application. These events can include user actions, system events, or errors. Logs can provide valuable information for troubleshooting issues, understanding user behavior, and detecting security incidents.
In Java, there are several libraries available for logging, such as Log4j, SLF4J, and java.util.logging.
Here’s an example of how you might use Log4j in a Java application:
In this code, we first create a Logger instance. We then use the info , warn , and error methods to log messages at different levels. These messages will be recorded in the application’s log file, where they can be reviewed later.
Monitoring, on the other hand, involves continuously observing your application to track its performance, identify issues, and detect potential security breaches.
Monitoring can help you identify suspicious activities, such as repeated failed login attempts, unexpected system behavior, or significant changes in traffic patterns, which could indicate a security incident.
Java provides several tools and libraries for monitoring, such as JMX (Java Management Extensions) for monitoring and managing Java applications, and third-party solutions like New Relic or Dynatrace for application performance monitoring.
By adhering to these core principles and incorporating them into the development process, developers can build robust and secure Java applications.
Remember, while these principles provide a solid foundation for Java security, it's essential to stay updated with the latest security practices, frameworks, and libraries. Regularly reviewing and enhancing security measures is crucial to adapt to emerging threats and ensure the ongoing protection of your Java applications.
By focusing on these fundamental aspects of Java security, you can create a secure and reliable environment for your applications and instill confidence in your users.
Here is a final code incorporating all the discussed aspects of Java security:
This code integrates the discussed principles of Java security, such as authentication, authorization, secure coding, encryption, and logging. It provides a foundation for building secure Java applications and protecting sensitive information.
Remember to adapt and enhance the code based on specific application requirements and the latest security practices. Regularly review and update the code to address emerging threats and vulnerabilities, ensuring the ongoing security of your Java applications.
Java Language Features for Security
When it comes to Java security, several key language features play a crucial role in ensuring the safety and protection of applications and data. Let's explore these features and understand their significance in securing Java code.
Static Data Typing: Enforcing Type Safety
One fundamental aspect of Java security is static data typing. By enforcing type safety, Java helps prevent common programming errors and vulnerabilities.
Static typing ensures that variables are declared with specific data types and that only compatible operations can be performed on them. This reduces the risk of type-related security issues, such as type confusion or type casting vulnerabilities.
For example, consider the following code snippet:
In this example, the compiler will detect any attempts to assign an integer value to the userName variable, preventing potential security risks.
Access Modifiers: Controlling Visibility and Accessibility
Access modifiers in Java, such as public , private , and protected , allow developers to control the visibility and accessibility of classes, methods, and variables. This plays a crucial role in ensuring the security of Java code by restricting access to sensitive information or functionalities.
In this example, the sensitiveData variable and the processSensitiveData method are declared as private , ensuring that they can be accessed only within the SecureApplication class.
Automatic Memory Management: Mitigating Memory-Related Vulnerabilities
Java's automatic memory management, enabled by the garbage collector, plays a significant role in enhancing security by mitigating memory-related vulnerabilities.
By automatically deallocating memory that is no longer in use, Java helps prevent issues such as memory leaks and buffer overflows that can lead to security vulnerabilities.
In this example, Java's garbage collector ensures that the memory occupied by the userInput variable is automatically reclaimed after it is no longer needed, reducing the risk of memory-related vulnerabilities.
Bytecode Verification: Ensuring Safe Code Execution
Java's bytecode verification process plays a critical role in ensuring the safe execution of code.
When Java code is compiled, it is transformed into bytecode, which is then executed by the Java Virtual Machine (JVM). Before executing the bytecode, the JVM performs bytecode verification to ensure that it adheres to specific safety requirements.
This process helps prevent common security risks, such as stack overflow or buffer overflow vulnerabilities.
In this example, the JVM verifies the bytecode of the processInput method to ensure that it operates safely, preventing potential security vulnerabilities.
By leveraging these language features, you can enhance the security of your Java code. But it's important to remember that these features alone are not sufficient to guarantee complete security. It is crucial to follow secure coding practices, apply encryption where necessary, and implement other security measures as required by your specific application and environment.
Security Architecture in Java
Overview of java security architecture.
Java security architecture is designed to provide a secure environment for Java applications. It includes various components such as the Java Development Kit (JDK), Java Runtime Environment (JRE), and Java Virtual Machine (JVM).
The architecture ensures the enforcement of security policies, handling of permissions, and management of cryptographic services.
Role of Provider Implementations in Java Security
In Java, a provider refers to a package or a set of packages that supply a concrete implementation of a subset of the cryptography aspects of the Java Cryptography Architecture (JCA) and the Java Cryptography Extension (JCE). They supply the actual program code that implements standard algorithms such as RSA, DSA, and AES.
Provider implementations are indeed crucial in Java security. They provide the necessary cryptographic algorithms and services that are used for various purposes such as generating key pairs, creating secure random numbers, and creating message digests.
Java includes several built-in providers. For instance, SunJCE (Java Cryptography Extension) is a provider that offers a wide range of cryptographic functionalities including support for encryption, key generation and key agreement, and Message Authentication Code (MAC) algorithms.
SunPKCS11 is another provider that offers a wide range of cryptographic functionalities. It provides a bridge from the JCA to native PKCS11 cryptographic tokens. PKCS11 is a standard that defines a platform-independent API to cryptographic tokens, such as hardware security modules (HSM) and smart cards, and names the API itself “Cryptoki”.
While the built-in providers offer a wide range of cryptographic functionalities, Java also allows for custom providers. This means you can implement your own provider to extend the security capabilities of your Java applications.
This is particularly useful when you need to use cryptographic services that are not offered by the built-in providers or when you want to use a device-specific implementation.
Implementing a custom provider involves extending the java.security.Provider class and implementing the required cryptographic services. Once implemented, the provider can be dynamically registered at runtime by calling the Security.addProvider() method.
Understanding Cryptographic Algorithms in Java
Java supports a comprehensive set of cryptographic algorithms for various purposes, including encryption, digital signatures, and hash functions. These algorithms ensure the confidentiality, integrity, and authenticity of data. Some commonly used algorithms include AES, RSA, and SHA-256.
To illustrate the usage of cryptographic algorithms in Java, consider the following example code:
In this example, we generate a key pair using the RSA algorithm, encrypt the data using the public key, and then decrypt it using the private key.
By understanding Java security architecture, provider implementations, and cryptographic algorithms, you can effectively implement secure solutions in your Java applications.
Cryptography in Java
In Java Cryptographic Architecture (JCA), you have access to a wide range of cryptographic functionalities to enhance the security of your Java applications. Let's explore some key concepts and techniques that can be implemented in Java code.
Introduction to Java Cryptographic Architecture (JCA)
To ensure the confidentiality, integrity, and authenticity of data, JCA provides a framework for implementing cryptographic algorithms and services. It includes classes and interfaces that allow you to perform various cryptographic operations, such as encryption, decryption, digital signatures, and message digests.
How to Implement Digital Signatures and Message Digests
Digital signatures provide a way to verify the authenticity and integrity of data. By generating a digital signature, you can ensure that the data has not been tampered with during transmission or storage.
Message digests, on the other hand, create a fixed-size hash value representing the input data. This hash value can be used to verify the integrity of the data.
Here is an example of generating a digital signature and verifying it using Java code:
Symmetric vs. Asymmetric Ciphers
Symmetric ciphers use the same key for both encryption and decryption, while asymmetric ciphers use different keys for these operations.
Symmetric ciphers are generally faster but require a secure method of key exchange. Asymmetric ciphers provide a secure way to exchange keys but are slower than symmetric ciphers.
Here is an example of using symmetric and asymmetric ciphers in Java:
Key Generators and Factories
In Java, you can use key generators and factories to generate and manage cryptographic keys. Key generators provide a way to generate secret keys for symmetric ciphers, while key factories are used to generate public and private keys for asymmetric ciphers.
Here is an example of using key generators and factories in Java:
By understanding and implementing these cryptographic concepts in Java, you can enhance the security of your Java applications and protect sensitive information effectively.
Public Key Infrastructure (PKI) in Java
When it comes to securing your Java applications, understanding the fundamentals of Public Key Infrastructure (PKI) is essential.
PKI provides a framework for managing keys and certificates. These play a crucial role in establishing secure communication and verifying the authenticity of entities in a networked environment.
In Java, you can leverage the KeyStore and CertStore classes to manage keys and certificates effectively.
The KeyStore class allows you to store and retrieve cryptographic keys, while the CertStore class provides a means to access certificates.
By properly managing keys and certificates, you can ensure the integrity and confidentiality of sensitive information.
Here's an example of using the KeyStore class to load a keystore file and retrieve a private key:
In this example, we load a keystore file in JKS format, provide the keystore password, and retrieve a private key using its alias and the associated key password. Once you have the private key, you can use it for various cryptographic operations.
Another important aspect of PKI in Java is the usage of tools such as Keytool and Jarsigner. Keytool is a command-line utility that allows you to manage keys and certificates within a keystore. Jarsigner, on the other hand, is used for digitally signing JAR files, ensuring their integrity and authenticity.
Here's an example of using Keytool to generate a key pair and store it in a keystore:
In this command, we generate a key pair using the RSA algorithm and store it in a keystore named "keystore.jks" with an alias "mykey". Keytool will prompt you for additional details such as the keystore password, key password, and the owner's information.
These tools provide essential functionalities for managing keys and certificates, enabling you to establish a secure environment for your Java applications. By incorporating these practices into your development process, you can enhance the security of your applications and protect sensitive data.
Authentication in Java
When it comes to Java security, understanding authentication mechanisms is crucial. Java provides various authentication mechanisms that can be implemented to ensure the safety and protection of applications and data. Let's explore some of these mechanisms and how they can be implemented in Java code.
Understanding Authentication Mechanisms in Java
In Java, authentication is the process of verifying the identity of a user or entity before granting access to protected resources. Java offers several authentication mechanisms, such as username and password authentication, token-based authentication, and certificate-based authentication.
One common authentication mechanism is username and password authentication. This mechanism involves validating a user's credentials, typically a username and password, to grant access.
To implement username and password authentication in Java, you can use the java.security package and the MessageDigest class to securely hash and compare passwords.
Here's an example code snippet that demonstrates username and password authentication in Java:
In this example, the UserAuthentication class demonstrates username and password authentication. It uses a HashMap to store the user database, where usernames are mapped to their corresponding hashed passwords. The authenticate method checks if the provided username exists in the database and compares the hashed password with the provided password.
Remember, this is a basic example, and in real-world scenarios, you would need to consider additional security measures such as using a salt for password hashing and storing passwords securely.
By implementing these authentication mechanisms in your Java applications, you can ensure the secure verification of user identities and protect sensitive resources.
Pluggable Login Modules: Flexibility and Security
In addition to the username and password authentication mechanism, Java provides a flexible and secure approach to authentication through pluggable login modules. Pluggable login modules allow you to define and implement custom authentication mechanisms based on specific requirements.
To implement pluggable login modules in Java, you can utilize the Java Authentication and Authorization Service (JAAS). JAAS provides a framework for authentication and authorization, allowing you to define and configure login modules to authenticate users.
Here's a simplified example code snippet that demonstrates the use of pluggable login modules in Java:
In this example, the PluggableAuthentication class demonstrates the usage of pluggable login modules. The LoginContext class is responsible for authenticating users using the specified login module, in this case, "SampleLoginModule". Once authenticated, the Subject object can be obtained from the LoginContext to access the authenticated user's information and perform further operations.
By leveraging pluggable login modules, you can customize and extend authentication mechanisms to meet specific security requirements, providing flexibility and enhanced security in your Java applications.
Case Study: How to Implement Username and Password Authentication
To illustrate the implementation of username and password authentication in Java, let's consider a case study. Suppose you are developing a web application that requires user authentication to access certain resources.
To implement username and password authentication in this case, you can utilize Java's Servlet API and the Java Persistence API (JPA). The Servlet API provides functionality for handling HTTP requests and responses, while JPA allows you to interact with a database and store user information securely.
Here's a high-level example code snippet that demonstrates the implementation of username and password authentication in a web application:
In this example, the LoginServlet class handles the HTTP POST request for the login page. It retrieves the username and password entered by the user and delegates the authentication process to the UserService .
If the authentication is successful, a session is created, and the user is redirected to the dashboard page. Otherwise, an error parameter is appended to the URL, indicating an invalid login attempt.
The UserService class encapsulates the authentication logic and interacts with the UserRepository to retrieve user information from the database. It compares the hashed password stored in the User entity with the provided password using the implemented password hashing algorithm.
Remember, this is a simplified example, and in a real-world scenario, you would need to consider additional security measures such as implementing secure session management, protecting against brute force attacks, and using stronger password hashing algorithms.

When it comes to securing client-server communication in Java, there are several protocols and techniques available. Let's explore some of these options:
SSL/TLS Protocols and Java Implementation
To establish a secure connection between a client and a server, the SSL/TLS protocols are commonly used.
In Java, you can utilize the Java Secure Socket Extension (JSSE) to implement SSL/TLS functionality. Here's an example of how to set up a secure connection using JSSE:
In this example, we create an SSLSocketFactory and an SSLSocket to establish a secure connection with the server at example.com on port 443 .
SASL: Securing Client-Server Communication
The Simple Authentication and Security Layer (SASL) is a framework that provides a flexible way to secure client-server communication. It allows clients and servers to negotiate and select authentication mechanisms that suit their requirements.
Here's an example of how to use SASL in Java:
In this example, we create a SaslClient using the PLAIN authentication mechanism for secure communication with the server at example.com .
GSS-API/Kerberos: Advanced Security Protocols
The Generic Security Service Application Program Interface (GSS-API) provides a framework for implementing advanced security protocols, such as Kerberos, in Java. Kerberos is a widely used authentication protocol that enables secure client-server communication.
Here's an example of how to use GSS-API/Kerberos in Java:
In this example, we use the GSS-API to perform a Kerberos login and obtain a Subject that represents the authenticated client.
Access Control in Java
Java provides several key features and tools to enhance security in your applications. Let's explore the role of SecurityManager , implementing permissions for resource access, and policy files.
Role of SecurityManager in Java
The SecurityManager class plays a vital role in Java security by enforcing fine-grained access control policies. It acts as a gatekeeper, preventing untrusted code from accessing sensitive resources or performing unauthorized operations.
By configuring and utilizing the SecurityManager , you can define and enforce security rules specific to your application's requirements.
Example code:
By setting a SecurityManager instance, you enable the enforcement of security policies within your Java application.
Implement Permissions for Resource Access
Java's permission model allows you to grant or deny specific permissions to code based on its origin or identity.
By defining and enforcing permissions, you can control which resources or operations a piece of code can access. This helps mitigate the risk of unauthorized access or misuse of sensitive resources.
In this example, we define a FilePermission to grant read access to a specific file. The SecurityManager 's checkPermission method ensures that the code has the required permission before accessing the file.
Policy Files: Defining and Enforcing Security Policies
Policy files provide a flexible and configurable way to define and enforce security policies in Java applications. They allow you to specify permissions, code sources, and associated permissions, granting or denying access based on defined rules.
By customizing and managing policy files, you can tailor the security policies to the specific needs of your application.
Example policy file (example.policy):
In this example, we grant read permission to the file "/path/to/file.txt". To enforce this policy file, you can specify it when launching your Java application using the -Djava.security.policy system property:
By leveraging policy files, you can define and enforce security policies without modifying your application's code.
Advanced Java Security Topics
Java provides various security features and tools to ensure the safety and protection of your applications. Let's explore some important concepts and techniques you can implement in your Java code.
XML Signature in Java
XML Signature is a crucial aspect of Java security that allows you to digitally sign XML documents to ensure their integrity and authenticity. By using the Java XML Digital Signature API, you can generate and verify XML signatures.
Here's an example code snippet to demonstrate the usage:
Deprecated Security APIs to Avoid
Java has deprecated certain security APIs due to their vulnerabilities or outdated functionality. It is important to avoid using these deprecated APIs and migrate to the recommended alternatives.
Here are a few examples of deprecated security APIs and their recommended replacements:
- java.security.KeyStore : Deprecated in favor of java.security.KeyStore.Builder .
- java.security.SecureRandom : Deprecated in favor of java.security.SecureRandom.getInstanceStrong() or java.security.SecureRandom.getInstance() .
- java.security.KeyPairGenerator : Deprecated in favor of java.security.KeyPairGenerator.getInstance() .
Always refer to the Java documentation for the complete list of deprecated security APIs and their recommended alternatives.
Security Tools and Commands in Java
Java provides various security tools and commands that can assist you in analyzing and enhancing the security of your applications.
Here are a few commonly used tools and commands:
- jarsigner : The jarsigner tool allows you to digitally sign JAR files to ensure their integrity and authenticity.
- keytool : The keytool command-line utility enables you to manage cryptographic keys and certificates in a Java KeyStore.
- javadoc : The javadoc tool generates API documentation, including security-related APIs, from Java source code.
- jps : The jps command-line utility displays information about Java processes running on a system, including their security settings.
- jinfo : The jinfo command-line utility provides configuration information for a running Java process, including security-related properties.
These tools and commands can be valuable in securing your Java applications and ensuring proper configuration and management of security-related components.
Remember to always refer to the official Java documentation and stay updated with the latest security practices and recommendations. Implementing robust security measures and regularly reviewing your code for potential vulnerabilities are essential for maintaining a secure Java environment.
Java Security in Practice
Java security plays a crucial role in today's digital landscape, ensuring the safety and protection of applications and sensitive data. Let's explore some real-world applications where Java security is prominently used and discuss case studies in the banking and e-commerce sectors.
Real-World Applications of Java Security
Java security is extensively utilized in various real-world applications, including banking systems, e-commerce platforms, and government services.
For example, in the banking sector, Java security is crucial for ensuring secure online transactions, protecting customer data, and preventing unauthorized access. Robust authentication mechanisms, encryption algorithms, and secure coding practices are employed to maintain the integrity and confidentiality of financial data.
In e-commerce platforms, Java security plays a vital role in safeguarding sensitive customer information, such as credit card details and personal data. Strict access control, secure communication protocols, and secure coding practices are implemented to prevent data breaches and protect customer privacy.
Let's explore two case studies that illustrate the practical implementation of Java security in the banking and e-commerce sectors.
Case Study: Banking Application
In a banking application, Java security is crucial for protecting customer accounts, preventing fraudulent activities, and ensuring the confidentiality of financial transactions.
To achieve this, the application incorporates several security measures:
- Secure Authentication : The banking application employs strong authentication mechanisms to verify the identity of users. Multi-factor authentication, such as combining passwords with biometric data, adds an extra layer of security.
- Secure Communication : The application uses secure communication protocols, such as HTTPS, to encrypt data transmission between the client and the server. This prevents eavesdropping and ensures the integrity of sensitive information.
- Secure Data Storage : Customer data, including account details and transaction history, is securely stored using encryption techniques. Strong encryption algorithms and proper key management ensure the confidentiality of sensitive data.
Case Study: E-commerce Platform
In an e-commerce platform, Java security is vital for protecting customer data, securing payment transactions, and preventing unauthorized access to user accounts. The platform incorporates various security measures to ensure a safe and trustworthy shopping experience.
- Secure Payment Processing : The e-commerce platform integrates with secure payment gateways, employing encryption and tokenization techniques to protect sensitive payment information. This ensures that customer payment details are securely transmitted and stored.
- Secure User Account Management : The platform enforces strong password policies, implements secure password storage techniques such as hashing and salting, and provides multi-factor authentication options to protect user accounts from unauthorized access.
- Secure Session Management : The e-commerce platform ensures secure session management by generating unique session IDs, implementing session timeouts, and securely storing session data to prevent session hijacking attacks.
By implementing these Java security measures, banking and e-commerce applications can provide a secure and trustworthy environment for their users. Remember to adapt these examples to your specific application requirements and consider additional security measures based on industry standards and best practices.
Java Security for Developers
When it comes to writing secure code in Java, it is important to follow best practices to ensure the safety and protection of your applications. By avoiding common security pitfalls and enhancing your skills through developer security training, you can create robust and secure Java applications. Let's explore these concepts in more detail.
How to Write Secure Code: Best Practices
Writing secure code involves adopting best practices that help mitigate security risks. Here are some key practices to consider:
Input Validation : Always validate and sanitize user input to prevent common vulnerabilities such as SQL injection or cross-site scripting (XSS) attacks. Use built-in Java libraries or frameworks to handle input validation effectively.
Secure Communication : Utilize secure communication protocols, such as HTTPS, to encrypt data transmitted between the client and the server. This ensures the confidentiality and integrity of sensitive information.
Authentication and Authorization : Implement strong authentication mechanisms to verify the identity of users and grant appropriate access privileges. Use secure algorithms for password hashing and consider multi-factor authentication for enhanced security.
Error Handling : Handle errors securely by providing informative error messages to users while avoiding exposing sensitive information that could be exploited by attackers. Log errors appropriately for monitoring and debugging purposes.
Secure Session Management : Implement secure session management techniques, such as using secure tokens or session IDs, to prevent session hijacking or fixation attacks. Set appropriate session timeouts and invalidate sessions after logout.
Common Security Pitfalls and How to Avoid Them
To write secure Java code, it is crucial to be aware of common security pitfalls and take steps to avoid them. Here are some pitfalls to watch out for:
Insecure Direct Object References : Avoid exposing internal object references directly in URLs or hidden fields, as it can lead to unauthorized access to sensitive data. Use indirect references or access control mechanisms to protect confidential information.
Cross-Site Scripting (XSS) Attacks : Prevent XSS attacks by properly encoding user-generated content and validating input. Utilize frameworks or libraries that automatically handle HTML encoding to mitigate this risk.
Insecure Cryptography : Avoid using weak or outdated cryptographic algorithms, as they can be vulnerable to attacks. Utilize the cryptographic functionalities provided by Java, such as AES or RSA, with secure key management practices.
Code Injection : Prevent code injection attacks, such as SQL injection or OS command injection, by utilizing prepared statements or parameterized queries. Avoid constructing queries or commands by concatenating user input.
Here is an example of an insecure code and the solution to it:
Here’s an example of a Java Servlet that has several security issues related to Insecure Cryptography, Cross-Site Scripting (XSS) Attacks, and Insecure Direct Object References:
In this code:
- Insecure Direct Object References : The code constructs an SQL query using the user-supplied username directly, which can lead to SQL Injection attacks if the username is not properly sanitized.
- Insecure Cryptography : The code uses MD5 to hash the password, which is considered insecure due to its vulnerability to collision attacks. A stronger algorithm like bcrypt or scrypt should be used instead.
- Cross-Site Scripting (XSS) Attacks : The code directly outputs the user-supplied username to the response without any sanitization or encoding, which can lead to XSS attacks if the username contains malicious scripts.
Here is the solution to it:
In this revised code, we use a PreparedStatement to prevent SQL Injection attacks. We replace MD5 with bcrypt for password hashing. And we escape the username using StringEscapeUtils.escapeHtml4() from Apache Commons Lang to prevent XSS attacks.
Note that this is a simplified example and real-world applications may have additional complexities and security considerations. Always follow best practices for secure coding to protect your application from these and other security vulnerabilities.
Also, remember to never expose sensitive information like secret keys in your code as done in this example. It’s always recommended to store such information in secure and encrypted environment variables or configuration files.
Developer Security Training: Enhancing Skills
Continuously improving your security skills through developer security training is crucial for writing secure Java code.
Here are some steps you can take to enhance your skills:
- Stay Updated : Keep yourself informed about the latest security threats, vulnerabilities, and best practices by following reputable security resources, attending security conferences, and participating in security-focused communities.
- Training Programs : Explore security training programs and certifications specifically designed for developers. These programs provide in-depth knowledge and practical guidance on secure coding practices, vulnerability assessment, and secure software development.
- Code Reviews : Engage in peer code reviews that include security-focused analysis. Collaborating with experienced developers can help identify potential security weaknesses and learn from their expertise.
- Security Tools : Utilize security analysis tools, such as static code analysis or vulnerability scanners, to identify potential security vulnerabilities in your code. These tools provide automated checks and recommendations for improvement.
By following these practices, avoiding common pitfalls, and continuously enhancing your security skills, you can write secure Java code that protects your applications and user data.
In conclusion, this book has equipped you with advanced Java programming skills crucial for any software engineer.
You've covered key topics ranging from unit testing and debugging to Java security, preparing you to handle real-world software development challenges.
Your journey through these chapters has enhanced your technical expertise, making you adept at creating efficient, secure, and robust software solutions.
Your newfound knowledge opens up a world of opportunities, from advancing in your current role to aspiring for senior developer positions or embarking on your own tech venture. With Java's role in AI, big data, and cloud computing, your skills are more relevant than ever.
As you step forward, remember that mastering Java is about applying these concepts to develop innovative solutions. Continue to grow, adapt to new technologies, and let your passion for programming drive you.
Now, with both the knowledge and confidence, you're ready to make your mark in the world of Java programming. Whether contributing to open-source projects, seeking Java certification, or innovating in your professional endeavors, you are well-prepared for the challenges and opportunities ahead. The path from learning to leading in the Java community awaits.
If you're keen on furthering your Java knowledge, here's a guide to help you conquer Java and launch your coding career . It's perfect for those interested in AI and machine learning, focusing on effective use of data structures in coding. This comprehensive program covers essential data structures, algorithms, and includes mentorship and career support.
Additionally, for more practice in data structures, you can explore these resources:
- Java Data Structures Mastery - Ace the Coding Interview : A free eBook to advance your Java skills, focusing on data structures for enhancing interview and professional skills.
- Foundations of Java Data Structures - Your Coding Catalyst : Another free eBook, diving into Java essentials, object-oriented programming, and AI applications.
Visit LunarTech's website for these resources and more information on the bootcamp .
Connect with Me:
- Follow me on LinkedIn for a ton of Free Resources in CS, ML and AI
- Visit my Personal Website
- Subscribe to my The Data Science and AI Newsletter
About the Author
I'm Vahe Aslanyan, specializing in the world of computer science, data science, and artificial intelligence. Explore my work at vaheaslanyan.com . My expertise encompasses robust full-stack development and the strategic enhancement of AI products, with a focus on inventive problem-solving.
.png)
My experience includes spearheading the launch of a prestigious data science bootcamp, an endeavor that put me at the forefront of industry innovation. I've consistently aimed to revolutionize technical education, striving to set a new, universal standard.
As we close this book, I extend my sincere thanks for your focused engagement. Imparting my professional insights through this book has been a journey of professional reflection. Your participation has been invaluable. I anticipate these shared experiences will significantly contribute to your growth in the dynamic field of technology.
I'm Vahe Aslanyan, dedicated to making AI and data science education inclusive and accessible. I guide developers towards clear tech understanding in software engineering.
If you read this far, thank the author to show them you care. Say Thanks
Learn to code for free. freeCodeCamp's open source curriculum has helped more than 40,000 people get jobs as developers. Get started

DEV Community
Posted on Apr 8
Object-Oriented Programming in Java: A Practical Guide 🚀☕
Object-Oriented Programming (OOP) is a fundamental paradigm that allows developers to create robust, modular, and maintainable software. In this article, we’ll explore the essential concepts of OOP using Java—a versatile language widely used in web development, Android apps, and enterprise solutions.
1. What is OOP?
OOP stands for Object-Oriented Programming . Let’s break down its key components:
Objects: Objects are the building blocks of OOP. They encapsulate both data (attributes or properties) and methods (functions or behaviors). For example, a Car object might have attributes like make, model, and methods like startEngine() and accelerate().
Classes: A class serves as a blueprint for creating objects. It defines the structure and behavior of objects. Think of a class as a template. For instance, you can create multiple Car objects based on the same Car class.
2. Key Concepts in OOP
Let’s delve deeper into essential OOP concepts:
a. Encapsulation:
Encapsulation ensures that an object’s data (attributes) is hidden from external access. You achieve this by defining private fields and providing public methods (getters and setters) to interact with the data.
b. Inheritance:
Inheritance allows you to create a new class (the subclass or derived class) based on an existing class (the superclass or base class). The subclass inherits the attributes and methods of the superclass. For instance, you can create a SportsCar class that inherits from the Car class.
c. Polymorphism:
Polymorphism enables objects of different classes to be treated uniformly. It allows you to define methods with the same name but different implementations in different classes. For example, both Car and Bicycle classes might have a move() method, but their behavior differs.
3. Putting OOP into Practice
Let’s create a simple example:

In this example: We define a Car class with attributes (make and model) and a method (startEngine()). In the Main class, we create a Car object and invoke its startEngine() method.
Remember, OOP is about modeling real-world entities, promoting code reusability, and organizing your code logically. As you explore more complex projects, these OOP principles will guide you toward elegant and efficient solutions. Happy coding! 🌟👩💻
Top comments (0)
Templates let you quickly answer FAQs or store snippets for re-use.
Are you sure you want to hide this comment? It will become hidden in your post, but will still be visible via the comment's permalink .
Hide child comments as well
For further actions, you may consider blocking this person and/or reporting abuse

Saga Pattern in Microservices
Hernani Almeida - Mar 12
Saga Pattern in Microservices - Parte 3

Using LocalStack in your Java Project - Part 1
Gyowanny (Geo) Queiroz - Feb 29

AWS SnapStart - Part 17 Impact of the snapshot tiered cache on the cold starts with Java 21
Vadym Kazulkin - Mar 11

We're a place where coders share, stay up-to-date and grow their careers.

- school Campus Bookshelves
- menu_book Bookshelves
- perm_media Learning Objects
- login Login
- how_to_reg Request Instructor Account
- hub Instructor Commons
- Download Page (PDF)
- Download Full Book (PDF)
- Periodic Table
- Physics Constants
- Scientific Calculator
- Reference & Cite
- Tools expand_more
- Readability
selected template will load here
This action is not available.

Java, Java, Java - Object-Oriented Programming (Morelli and Walde)
- Last updated
- Save as PDF
- Page ID 15048

- Ralph Morelli & Ralph Wade
- Trinity College
\( \newcommand{\vecs}[1]{\overset { \scriptstyle \rightharpoonup} {\mathbf{#1}} } \)
\( \newcommand{\vecd}[1]{\overset{-\!-\!\rightharpoonup}{\vphantom{a}\smash {#1}}} \)
\( \newcommand{\id}{\mathrm{id}}\) \( \newcommand{\Span}{\mathrm{span}}\)
( \newcommand{\kernel}{\mathrm{null}\,}\) \( \newcommand{\range}{\mathrm{range}\,}\)
\( \newcommand{\RealPart}{\mathrm{Re}}\) \( \newcommand{\ImaginaryPart}{\mathrm{Im}}\)
\( \newcommand{\Argument}{\mathrm{Arg}}\) \( \newcommand{\norm}[1]{\| #1 \|}\)
\( \newcommand{\inner}[2]{\langle #1, #2 \rangle}\)
\( \newcommand{\Span}{\mathrm{span}}\)
\( \newcommand{\id}{\mathrm{id}}\)
\( \newcommand{\kernel}{\mathrm{null}\,}\)
\( \newcommand{\range}{\mathrm{range}\,}\)
\( \newcommand{\RealPart}{\mathrm{Re}}\)
\( \newcommand{\ImaginaryPart}{\mathrm{Im}}\)
\( \newcommand{\Argument}{\mathrm{Arg}}\)
\( \newcommand{\norm}[1]{\| #1 \|}\)
\( \newcommand{\Span}{\mathrm{span}}\) \( \newcommand{\AA}{\unicode[.8,0]{x212B}}\)
\( \newcommand{\vectorA}[1]{\vec{#1}} % arrow\)
\( \newcommand{\vectorAt}[1]{\vec{\text{#1}}} % arrow\)
\( \newcommand{\vectorB}[1]{\overset { \scriptstyle \rightharpoonup} {\mathbf{#1}} } \)
\( \newcommand{\vectorC}[1]{\textbf{#1}} \)
\( \newcommand{\vectorD}[1]{\overrightarrow{#1}} \)
\( \newcommand{\vectorDt}[1]{\overrightarrow{\text{#1}}} \)
\( \newcommand{\vectE}[1]{\overset{-\!-\!\rightharpoonup}{\vphantom{a}\smash{\mathbf {#1}}}} \)
We have designed this third edition of Java, Java, Java to be suitable for a typical Introduction to Computer Science (CS1) course or for a slightly more advanced Java as a Second Language course. This edition retains the “objects first” approach to programming and problem solving that was characteristic of the first two editions. Throughout the text we emphasize careful coverage of Java language features, introductory programming concepts, and object-oriented design principles.
- Java Arrays
- Java Strings
- Java Collection
- Java 8 Tutorial
- Java Multithreading
- Java Exception Handling
- Java Programs
- Java Project
- Java Collections Interview
- Java Interview Questions
- Spring Boot
- Java Exercises - Basic to Advanced Java Practice Set with Solutions
1. Write Hello World Program in Java
2. write a program in java to add two numbers., 3. write a program to swap two numbers, 4. write a java program to convert integer numbers and binary numbers..
- 5. Write a Program to Find Factorial of a Number in Java
- 6. Write a Java Program to Add two Complex Numbers
7. Write a Program to Calculate Simple Interest in Java
- 8. Write a Program to Print the Pascal’s Triangle in Java
9. Write a Program to Find Sum of Fibonacci Series Number
10. write a program to print pyramid number pattern in java., 11. write a java program to print pattern., 12. write a java program to print pattern., 13. java program to print patterns., 14. write a java program to compute the sum of array elements., 15. write a java program to find the largest element in array, 16. write java program to find the tranpose of matrix, 17. java array program for array rotation, 18. java array program to remove duplicate elements from an array, 19. java array program to remove all occurrences of an element in an array, 20. java program to check whether a string is a palindrome, 21. java string program to check anagram, 22. java string program to reverse a string, 23. java string program to remove leading zeros, 24. write a java program for linear search., 25. write a binary search program in java., 26. java program for bubble sort..
- 27. Write a Program for Insertion Sort in Java
28. Java Program for Selection Sort.
29. java program for merge sort., 30. java program for quicksort., java exercises – basic to advanced java practice programs with solutions.
Test your Java skills with our topic-wise Java exercises. As we know Java is one of the most popular languages because of its robust and secure nature. But, programmers often find it difficult to find a platform for Java Practice Online. In this article, we have provided Java Practice Programs. That covers various Java Core Topics that can help users with Java Practice.
Take a look at our free Java Exercises to practice and develop your Java programming skills. Our Java programming exercises Practice Questions from all the major topics like loops, object-oriented programming, exception handling, and many more.
List of Java Exercises
Pattern programs in java, array programs in java, string programs in java, java practice problems for searching algorithms, practice problems in java sorting algorithms.
- Practice More Java Problems
-768.webp)
Java Practice Programs
This Java exercise is designed to deepen your understanding and refine your Java coding skills, these programs offer hands-on experience in solving real-world problems, reinforcing key concepts, and mastering Java programming fundamentals. Whether you’re a beginner who looking to build a solid foundation or a professional developer aiming to sharpen your expertise, our Java practice programs provide an invaluable opportunity to sharpen your craft and excel in Java programming language .
The solution to the Problem is mentioned below:
Click Here for the Solution
5. write a program to find factorial of a number in java., 6. write a java program to add two complex numbers., 8. write a program to print the pascal’s triangle in java.
Time Complexity: O(N) Space Complexity: O(N)
Time Complexity: O(logN) Space Complexity: O(N)
Time Complexity: O(N 2 ) Space Complexity: O(1)
27. Write a Program for Insertion Sort in Java.
Time Complexity: O(N logN) Space Complexity: O(N)
Time Complexity: O(N logN) Space Complexity: O(1)
After completing these Java exercises you are a step closer to becoming an advanced Java programmer. We hope these exercises have helped you understand Java better and you can solve beginner to advanced-level questions on Java programming.
Solving these Java programming exercise questions will not only help you master theory concepts but also grasp their practical applications, which is very useful in job interviews.
More Java Practice Exercises
Java Array Exercise Java String Exercise Java Collection Exercise To Practice Java Online please check our Practice Portal. <- Click Here
FAQ in Java Exercise
1. how to do java projects for beginners.
To do Java projects you need to know the fundamentals of Java programming. Then you need to select the desired Java project you want to work on. Plan and execute the code to finish the project. Some beginner-level Java projects include: Reversing a String Number Guessing Game Creating a Calculator Simple Banking Application Basic Android Application
2. Is Java easy for beginners?
As a programming language, Java is considered moderately easy to learn. It is unique from other languages due to its lengthy syntax. As a beginner, you can learn beginner to advanced Java in 6 to 18 months.
3. Why Java is used?
Java provides many advantages and uses, some of which are: Platform-independent Robust and secure Object-oriented Popular & in-demand Vast ecosystem
Please Login to comment...
Similar reads.
- Java-Arrays
- java-basics
- Java-Data Types
- Java-Functions
- Java-Library
- Java-Object Oriented
- Java-Output
- Java-Strings
- Output of Java Program
Improve your Coding Skills with Practice
What kind of Experience do you want to share?

- All Courses
Object Oriented programming (OOP)
Problem solving in object oriented paradigm, introduction:, problem solving methodology in oop:.
The world around us is made up of objects, such as people, automobiles, buildings, streets, and so forth. Each of these objects has the ability to perform certain actions, and each of these actions has some effect on some of the other objects in the world.
OOP is a programming methodology that views a program as similarly consisting of objects that interact with each other by means of actions.
Object-oriented programming has its own specialized terminology. The objects are called, appropriately enough, objects. The actions that an object can take are called methods. Objects of the same kind are said to have the same type or, more often, are said to be in the same class.
For example, in an airport simulation program, all the simulated airplanes might belong to the same class, probably called the Airplane class. All objects within a class have the same methods. Thus, in a simulation program, all airplanes have the same methods (or possible actions), such as taking off, flying to a specific location, landing, and so forth. However, all simulated airplanes are not identical. They can have different characteristics, which are indicated in the program by associating different data (that is, some different information) with each particular airplane object. For example, the data associated with an airplane object might be two numbers for its speed and altitude.
Things that are called procedures, methods, functions, or subprograms in other languages are all called methods in Java. In Java, all methods (and for that matter, any programming constructs whatsoever) are part of a class.
Lab Activities:
Activity 1:.
Consider the concept of a CourseResult. The CourseResult should have data members like the student name, course name and grade obtained in that course.
This concept can be represented in a class as follows:
Public class CourseResult
Public String studentname; Public String coursename; Public String grade;
public void display()
System.out.println(“Student Name is: ― + studentname + “Course Name is: ― + coursename + “Grade is: ― + grade);
Public class CourseResultRun
public static void main(String[]args)
CourseResult c1=new CourseResult (); c1.studentName= ―Ali‖; c1.courseName= ―OOP‖;
c1.grade= ―A‖; c1.display();
CourseResult c2=new CourseResult (); c2.studentName= ―Saba‖; c2.courseName= ―ICP‖;
c2.grade= ―A+‖; c2.display();
Note that both objects; c1 and c2 have three data members, but each object has different values for their data members.
Activity 2:
The example below represents a Date class. As date is composed of three attributes, namely month, year and day; so the class contains three Data Members. Now every date object will have these three attributes, but each object can have different values for these three
public class Date
public String month; public int day;
public int year; //a four digit number.
public void displayDate()
System.out.println(month + ” ” + day + “, ” + year);
public class DateDemo
public static void main(String[] args)
Date date1, date2; date1 = new Date();
date1.month = “December”; date1.day = 31;
date1.year = 2012; System.out.println(“date1:”); date1.display();
Activity 3:
date2 = new Date(); date2.month = “July”; date2.day = 4;
date2.year = 1776; System.out.println(“date2:”); date2.display();
Consider the concept of a Car Part. After analyzing this concept we may consider that it can be described by three data members: modelNumber , partNumber and cost.
The methods should facilitate the user to assign values to these data members and show the values for each object.
importjavax.swing.JOptionPane;
Public class CarPart
private String modelNumber; private String partNumber; private String cost;
public void setparameter(String x, String y,String z)
modelNumber=x; partNumber=y; cost=z;
public static void display()
System.out.println(“Model Number: ―+modelNumber + ―Part Number: ―+partNumber +
―Cost: ― + cost);
Public class CarPartRunner
CarPart car1=new CarPart ();
String x=JOptionPane.showInputDialog(“What is Model Number?” ); String y=JOptionPane.showInputDialog(“What is Part Number?” ); String z=JOptionPane.showInputDialog(“What is Cost?” ); car1.setparameter(x,y,z);
car1.display();
Home Activities:
A Student is an object in a university management System. Analyze the concept and identify the data members that a Student class should have. Also analyze the behavior of student in a university management System and identify the methods that should be included in Student class.
Time is an intangible concept. Analyze the concept and identify the data members and methods that should be included in Time class.
Assignment 1:
Car is an object that helps us in transportation. Analyze the concept and identify the data members and methods that should be included in Car class.
Assignment 2:
Rectangle is an object that represents a specific shape. Analyze the concept and identify the data members and methods that should be included in Rectangle class.
Leave a Reply Cancel reply
You must be logged in to post a comment.

Important Pages
© Copyright Cuitutorial All Rights Reserved
Modal title
- Privacy & Policy
- Terms & Conditions
Java OOP Concepts : Can you solve this real-world problem
Test your Java OOP skills with this real-world challenge! Solve the problem, boost your knowledge, and become a master programmer.
Java, a programming language known for its versatility and reliability, introduces developers to the fascinating world of Object-Oriented Programming (OOP). In this article, we dive deep into the core concepts of Java OOP and present a real-world problem to test your skills.
1. Understanding Java OOP Basics
Object-Oriented Programming (OOP) Demystified
Object-Oriented Programming is a paradigm that revolves around the concept of "objects," encapsulating data and behavior. This fundamental shift in programming design brings forth four key principles: Encapsulation, Inheritance, Polymorphism, and Abstraction.
2. Key OOP Principles Unveiled
Encapsulation: Shielding data within classes, preventing direct access.
Inheritance: Hierarchical organization of classes for code reuse.
2.1 Polymorphism Allowing objects of different types to be treated as objects of a common type.
3. The Real-World Problem
3.1 Dive into the Challenge
Imagine you're tasked with designing a system to manage a library's book inventory. Each book has unique attributes, and the system must support operations like borrowing, returning, and searching. This real-world scenario tests your ability to apply Java OOP concepts in solving a complex problem.
3.2 Importance of Problem-Solving in Programming
Coding is not just about syntax; it's about solving real-world problems. Mastering OOP equips you with the tools to approach challenges systematically, making you a more effective and confident programmer.
4. Breaking Down the Challenge
4.1 Analyzing the Problem Statement
Understanding the problem is the first step. Break down the requirements, identify entities, and define relationships. In our library scenario, consider classes like Book, Library, and User.
4.2 Identifying Potential OOP Solutions
Creating Classes and Objects: Define classes for entities and create instances for each book, library, and user.
4.3 Implementing Inheritance
Establish a hierarchy, perhaps a general Book class and specific subclasses for different genres.
5. Step-by-Step Solution
5.1 Walkthrough of Solving the Problem
Let's embark on a coding journey. Starting with class definitions, we'll guide you through implementing each OOP concept step by step. By the end, you'll have a functional Java program managing a library's book inventory.
5.2 Coding Examples for Each OOP Concept
Explore snippets of Java code showcasing encapsulation, inheritance, polymorphism, and abstraction in action. Learn not just the 'how,' but the 'why' behind each decision.
6. The Joy of Overcoming Challenges
6.1 Celebration of Successful Problem-Solving
Completing the library system is an achievement worth celebrating. The sense of accomplishment reinforces the power of OOP in transforming abstract ideas into practical solutions.
6.2 Reinforcement of Java OOP Concepts
By solving a real-world problem, you solidify your understanding of Java OOP. Theoretical knowledge transforms into a valuable skill set, setting you apart in the competitive world of software development.
7. Real-World Applications
7.1 OOP in the Industry
Discover how major projects, from enterprise-level applications to popular software, rely on OOP principles. Gain insights into the real-world applications that make Java a go-to language for diverse projects.
7.2 Examples of OOP in Java-Based Projects
Explore notable examples of successful Java-based projects where OOP played a pivotal role. From Android app development to web applications, witness the impact of OOP on creating robust and scalable software.
8. Advantages of Mastering Java OOP
8.1 Enhanced Problem-Solving Skills
Mastering Java OOP goes beyond syntax. It enhances your ability to approach and solve complex problems systematically, a skill highly valued in the tech industry.
8.2 Career Benefits in the Tech Industry
Employers seek developers with strong OOP skills . Stand out in job interviews and advance your career by showcasing your proficiency in Java OOP concepts.
9. Challenges Encountered by Developers
9.1 Common Pitfalls in OOP Implementation
Avoiding common mistakes is as important as implementing OOP principles. Learn about pitfalls and gain insights into how to navigate around them effectively.
10. Java OOP Best Practices
10.1 Coding Guidelines for Effective OOP
Follow best practices to ensure your OOP code is clean, readable, and efficient. From naming conventions to structuring classes, adhere to guidelines that make your code a joy to work with.
In this thrilling journey, we explored the fundamentals of Java OOP, tackled a real-world problem, and delved into practical solutions. Remember, mastering OOP is not just about writing code; it's about thinking in objects.
Frequently Asked Questions(FAQs) Q1. How can I practice Java OOP concepts effectively? A1: Engage in coding exercises, work on real-world projects, and participate in online coding communities to apply and reinforce your OOP skills. Q2. Are there any online resources for mastering OOP in Java? A2: Yes, platforms like Codecademy, Coursera, and Udacity offer comprehensive Java OOP courses, providing hands-on learning experiences. Q3. Can I use OOP in languages other than Java? A3: Absolutely! OOP principles are applicable across various programming languages, including Python, C++, and JavaScript.
Perfect elearning i s a tech-enabled education platform that provides it courses with 100% internship and placement support. perfect elearning provides both online classes and offline classes only in faridabad., it provides a wide range of courses in areas such as artificial intelligence, cloud computing, data science, digital marketing, full stack web development, block chain, data analytics, and mobile application development. perfect elearning, with its cutting-edge technology and expert instructors from adobe, microsoft, pwc, google, amazon, flipkart, nestle and infoedge is the perfect place to start your it education., perfect elearning provides the training and support you need to succeed in today's fast-paced and constantly evolving tech industry, whether you're just starting out or looking to expand your skill set., there's something here for everyone. perfect elearning provides the best online courses as well as complete internship and placement assistance., keep learning, keep growing. if you are confused and need guidance over choosing the right programming language or right career in the tech industry, you can schedule a free counselling session with perfect elearning experts., related blogs.

3 Best Backend projects ideas for Beginners in 2023

5 Projects to Help You Become a Front-End Master in 2023
A Beginner's Guide to JavaScript Methods
Advanced Machine Learning Modelling Techniques
Hey it's sneh, what would i call you.
Our counsellor will contact you shortly.

Company Contact
Hello you can contact us on this number +91 88514-12238 Also, you can contact us to this email [email protected] Thanks.
- Become a tutor
Something went wrong!
Some error occured while loading page for you. Please try again.
Challenge Walkthrough
Review the problem statement, choose a language, enter your code, test your code, submit to see results.
- Check your score
Solve a real-world problem using Java

Pixabay. CC0.
As I wrote in the first two articles in this series, I enjoy solving small problems by writing small programs in different languages, so I can compare the different ways they approach the solution. The example I'm using in this series is dividing bulk supplies into hampers of similar value to distribute to struggling neighbors in your community, which you can read about in the first article in this series.
In the first article, I solved this problem using the Groovy programming language , which is like Python in many ways, but syntactically it's more like C and Java. In the second article, I solved it in Python with a very similar design and effort, which demonstrates the resemblance between the languages.
Now I'll try it in Java .
The Java solution
When working in Java, I find myself declaring utility classes to hold tuples of data (the new record feature is going to be great for that), rather than using the language support for maps offered in Groovy and Python. This is because Java encourages creating maps that map one specific type to another specific type, but in Groovy or Python, it's cool to have a map with mixed-type keys and mixed-type values.
The first task is to define these utility classes, and the first is the Unit class:
There's nothing too startling here. I effectively created a class whose instances are immutable since there are no setters for fields item , brand , or price and they are declared private . As a general rule, I don't see value in creating a mutable data structure unless I'm going to mutate it; and in this application, I don't see any value in mutating the Unit class.
While more effort is required to create these utility classes, creating them encourages a bit more design effort than just using a map, which can be a good thing. In this case, I realized that a bulk package is composed of a number of individual units, so I created the Pack class:
More on Java
- What is enterprise Java programming?
- Red Hat build of OpenJDK
- Java cheat sheet
- Free online course: Developing cloud-native applications with microservices architectures
- Fresh Java articles
Similar to the Unit class, the Pack class is immutable. A couple of things worth mentioning here:
- I could have passed a Unit instance into the Pack constructor. I chose not to because the bundled, physical nature of a bulk package encouraged me to think of the "unit-ness" as an internal thing not visible from the outside but that requires unpacking to expose the units. Is this an important decision in this case? Probably not, but to me, at least, it's always good to think through this kind of consideration.
- Which leads to the unpack() method. The Pack class creates the list of Unit instances only when you call this method—that is, the class is lazy . As a general design principle, I've found it's worthwhile to decide whether a class' behavior should be eager or lazy, and when it doesn't seem to matter, I go with lazy. Is this an important decision in this case? Maybe—this lazy design enables a new list of Unit instances to be generated on every call of unpack() , which could prove to be a good thing down the road. In any case, getting in the habit of always thinking about eager vs. lazy behavior is a good habit.
The sharp-eyed reader will note that, unlike in the Groovy and Python examples where I was mostly focused on compact code and spent way less time thinking about design decisions, here, I separated the definition of a Pack from the number of Pack instances purchased. Again, from a design perspective, this seemed like a good idea as the Pack is conceptually quite independent of the number of Pack instances acquired.
Given this, I need one more utility class: the Bought class:
- I decided to pass a Pack into the constructor. Why? Because to my way of thinking, the physical structure of the purchased bulk packages is external, not internal, as in the case of the individual bulk packages. Once again, it may not be important in this application, but I believe it's always good to think about these things. If nothing else, note that I am not married to symmetry!
- Once again the unpack() method demonstrates the lazy design principle. This goes to more effort to generate a list of Unit instances (rather than a list of lists of Unit instances, which would be easier but require flattening further out in the code).
OK! Time to move on and solve the problem. First, declare the purchased packs:
This is pretty nice from a readability perspective: there is one pack of Best Family Rice containing 10 units that cost 5,650 (using those crazy monetary units, like in the other examples). It's straightforward to see that in addition to the one bulk pack of 10 bags of rice, the organization acquired 10 bulk packs of one bag each of spaghetti. The utility classes are doing some work under the covers, but that's not important at this point because of the great design job!
Note the var keyword is used here; it's one of the nice features in recent versions of Java that help make the language a bit less verbose (the principle is called DRY —don't repeat yourself) by letting the compiler infer the variable's data type from the right-side expression's type. This looks kind of similar to the Groovy def keyword, but since Groovy by default is dynamically typed and Java is statically typed, the typing information inferred in Java by var persists throughout the lifetime of that variable.
Finally, it's worth mentioning that packs here is an array and not a List instance. If you were reading this data from a separate file, you would probably prefer to create it as a list.
Next, unpack the bulk packages. Because the unpacking of Pack instances is delegated into lists of Unit instances, you can use that like this:
This uses some of the nice functional programming features introduced in later Java versions. Convert the array packs declared previously to a Java stream, use flatmap() with a lambda to flatten the sublists of units generated by the unpack() method of the Bought class, and collect the resulting stream elements back into a list.
As in the Groovy and Java solutions, the final step is repacking the units into the hampers for distribution. Here's the code—it's not much wordier than the Groovy version (tiresome semicolons aside) nor really all that different:
Some clarification, with numbers in brackets in the comments above (e.g., [1] ) corresponding to the clarifications below:
- 1. Set up the ideal and maximum values to be loaded into any given hamper, initialize Java's random number generator and the hamper number.
- 2.1 Increment the hamper number, get a new empty hamper (a list of Unit instances), and set its value to 0.
- 2.2.1 Get a random number between zero and the number of remaining units minus 1.
- 2.2.2 Assume you can't find more units to add.
- 2.2.3.1 Figure out which unit to look at.
- 2.2.3.2 Add this unit to the hamper if there are only a few left or if the value of the hamper isn't too high once the unit is added and that unit isn't already in the hamper.
- 2.2.3.3 Add the unit to the hamper, increment the hamper value by the unit price, and remove the unit from the available units list.
- 2.2.3.4 As long as there are units left, you can add more, so break out of this loop to keep looking.
- 2.2.4 On exit from this for {} loop, if you inspected every remaining unit and could not find one to add to the hamper, the hamper is complete; otherwise, you found one and can continue looking for more.
- 2.3 Print out the contents of the hamper.
- 2.4 Print out the remaining units info.
When you run this code, the output looks quite similar to the output from the Groovy and Python programs:
The last hamper is abbreviated in contents and value.
Closing thoughts
The similarities in the "working code" with the Groovy original are obvious—the close relationship between Groovy and Java is evident. Groovy and Java diverged in a few ways in things that were added to Java after Groovy was released, such as the var vs. def keywords and the superficial similarities and differences between Groovy closures and Java lambdas. Moreover, the whole Java streams framework adds a great deal of power and expressiveness to the Java platform (full disclosure, in case it's not obvious—I am but a babe in the Java streams woods).
Java's intent to use maps for mapping instances of a single type to instances of another single type pushes you to use utility classes, or tuples, instead of the more inherently flexible intents in Groovy maps (which are basically just Map<Object,Object> plus a lot of syntactic sugar to vanish the kinds of casting and instanceof hassles that you would create in Java) or in Python. The bonus from this is the opportunity to apply some real design effort to these utility classes, which pays off at least insofar as it instills good habits in the programmer.
Aside from the utility classes, there isn't a lot of additional ceremony nor boilerplate in the Java code compared to the Groovy code. Well, except that you need to add a bunch of imports and wrap the "working code" in a class definition, which might look like this:
The same fiddly bits are necessary in Java as they are in Groovy and Python when it comes to grabbing stuff out of the list of Unit instances for the hampers, involving random numbers, loops through remaining units, etc.
Another issue worth mentioning—this isn't a particularly efficient approach. Removing elements from ArrayLists , being careless about repeated expressions, and a few other things make this less suitable for a huge redistribution problem. I've been a bit more careful here to stick with integer data. But at least it's quite quick to execute.
Yes, I'm still using the dreaded while { … } and for { … } . I still haven't thought of a way to use map and reduce style stream processing in conjunction with a random selection of units for repackaging. Can you?
Stay tuned for the next articles in this series, with versions in Julia and Go .

Why I use Java
There are probably better languages than Java, depending on work requirements. But I haven't seen anything yet to pull me away.

Managing a non-profit organization's supply chain with Groovy
Let's use Groovy to solve a charity's distribution problem.

Use Python to solve a charity's business problem
Comparing how different programming languages solve the same problem is fun and instructive. Next up, Python.

Related Content


IMAGES
VIDEO
COMMENTS
Object-oriented programming: Object-oriented programming (OOP) is a programming paradigm based on the concept of "objects", which can contain data and code. The data is in the form of fields (often known as attributes or properties), and the code is in the form of procedures (often known as methods). A Java class file is a file (with the .class ...
EasyJava (Basic)Max Score: 15Success Rate: 98.11%. Solve Challenge. Status. Solved. Unsolved. Skills. Java (Basic) Java (Intermediate) Problem Solving (Intermediate)
This book covers Object-Oriented Programming under JAVA. It introduces the concepts of object-oriented programming and they are used for problem-solving. This book covers all the relevant areas of Object-Oriented Programming under Java. Also, it covers more advanced topics such as socket programming and algorithms. Content Accuracy rating: 5
Hi, folks! Today we are going to talk about object-oriented programming in Java. This article will help give you a thorough understanding of the underlying principles of object-oriented programming and its concepts. Once you understand these concepts, you should have the confidence and ability to develop basic problem-solving applications
This repository is designed to help you sharpen your Java skills with real-world object-oriented programming (OOP) practice problems and solutions. ... Practice solving problems commonly encountered in Java development projects. ... Review the problem statement provided in each exercise file.
You're embarking on a journey to master Java Object-Oriented Programming, a skill that paves the way for diverse opportunities in software engineering. This guide will lay a foundation for you to transition from writing code to building robust software systems. ... Universal Blueprint for Problem-Solving: Think of design patterns as the Swiss ...
OOP stands for Object-Oriented Programming. Let's break down its key components: Objects: Objects are the building blocks of OOP. They encapsulate both data (attributes or properties) and methods (functions or behaviors). For example, a Car object might have attributes like make, model, and methods like startEngine() and accelerate ().
The four fundamental principles of OOP — encapsulation, abstraction, inheritance, and polymorphism — are not just abstract concepts but practical tools that Java offers to solve real-world ...
Problem Solving; Java Programming; Object-Oriented Programming (OOP) Details to know. Shareable certificate. Add to your LinkedIn profile. Specialization - 5 course series. ... You'll learn object-oriented programming principles that will allow you to use Java to its full potential, and you'll implement data structures and algorithms for ...
Use conditionals and loops in a Java program; 3. Use Java API documentation in writing programs. 4. Debug a Java program using the scientific method; 5. Write a Java method to solve a specific problem; 6. Develop a set of test cases as part of developing a program; 7. Create a class with multiple methods that work together to solve a problem ...
Trinity College. We have designed this third edition of Java, Java, Java to be suitable for a typical Introduction to Computer Science (CS1) course or for a slightly more advanced Java as a Second Language course. This edition retains the "objects first" approach to programming and problem solving that was characteristic of the first two ...
Advantages of Object-Oriented Programming. Object-oriented programming has many more advantages over procedural programming: OOP breaks down the problem into the small part, so it is easy to solve ...
There are 5 modules in this course. Learn to code in Java and improve your programming and problem-solving skills. You will learn to design algorithms as well as develop and debug programs. Using custom open-source classes, you will write programs that access and transform images, websites, and other types of data.
That covers various Java Core Topics that can help users with Java Practice. Take a look at our free Java Exercises to practice and develop your Java programming skills. Our Java programming exercises Practice Questions from all the major topics like loops, object-oriented programming, exception handling, and many more.
Object-oriented programming has its own specialized terminology. The objects are called, appropriately enough, objects. The actions that an object can take are called methods. Objects of the same kind are said to have the same type or, more often, are said to be in the same class. For example, in an airport simulation program, all the simulated ...
The best way we learn anything is by practice and exercise questions. Here you have the opportunity to practice the Java programming language concepts by solving the exercises starting from basic to more complex exercises. A sample solution is provided for each exercise. It is recommended to do these exercises by yourself first before checking ...
OO, or Object Oriented, programming refers to a set of activities that lead to a computer program, written in an object-oriented language, that when executed on a computer will solve a problem. Java is an OO language used in CS 180. Other OO languages include C++, C#, Delphi, Modula, Oberon, Objective C, Simula, Smalltalk, and many more!
6.1 Celebration of Successful Problem-Solving. Completing the library system is an achievement worth celebrating. The sense of accomplishment reinforces the power of OOP in transforming abstract ideas into practical solutions. 6.2 Reinforcement of Java OOP Concepts. By solving a real-world problem, you solidify your understanding of Java OOP.
This is difficult to do without OOP. Look into code Design patterns to solve your problem, for instance: factory pattern, builder pattern, state pattern etc. fyi GoF Design Patterns are OOP ways to solve common coding problems. Keep in mind that Design Patterns can be very difficult for a beginner to grasp.
Review the problem statement Each challenge has a problem statement that includes sample inputs and outputs. Some challenges include additional information to help you out. 2 of 6; Choose a language Select the language you wish to use to solve this challenge. 3 of 6; Enter your code
2.1 Increment the hamper number, get a new empty hamper (a list of Unit instances), and set its value to 0. 2.2 This for {} loop will add as many units to the hamper as possible: 2.2.1 Get a random number between zero and the number of remaining units minus 1. 2.2.2 Assume you can't find more units to add.
OOPLab Exercise 1 - practice problems of Object oriented programming in java. Object Oriented Programming 94% (65) 10. 7 OOP Lecture 6 Arrays. Object Oriented Programming 100% (16) 119. LAB Manual pf. Object Oriented Programming 100% (10) 9. LAB Reportt 2 - lab report from lab manual.