

KB4535305 - SQL Server Reporting Services remote code execution vulnerability
A remote code execution vulnerability exists in Microsoft SQL Server Reporting Services when it incorrectly handles page requests. See CVE-2020-0618 for details.
To fix this issue in the products that are listed in “Applies to,” install the following security update, as appropriate:
Description of the security update for SQL Server 2016 SP2 CU11: February 11, 2020
Description of the security update for SQL Server 2016 SP2 GDR: February 11, 2020
Description of the security update for SQL Server 2014 SP3 CU4: February 11, 2020
Description of the security update for SQL Server 2014 SP3 GDR: February 11, 2020
Description of the security update for SQL Server 2012 SP4 GDR: February 11, 2020

Need more help?
Want more options.
Explore subscription benefits, browse training courses, learn how to secure your device, and more.

Microsoft 365 subscription benefits

Microsoft 365 training

Microsoft security

Accessibility center
Communities help you ask and answer questions, give feedback, and hear from experts with rich knowledge.

Ask the Microsoft Community

Microsoft Tech Community

Windows Insiders
Microsoft 365 Insiders
Was this information helpful?
Thank you for your feedback.
Microsoft September 2020 Patch Tuesday fixes 129 vulnerabilities
Lawrence abrams.
- September 8, 2020
Today is Microsoft's September 2020 Patch Tuesday, and your Windows administrators will be scrambling as they install updates and try to resolve bugs caused by them. Be nice!
With the September 2020 Patch Tuesday security updates release, Microsoft has released fixes for 129 vulnerabilities in Microsoft products.
Of these vulnerabilities, 23 are classified as Critical, and 105 are classified as Important, and 1 as moderate.
This release is tied with June 2020 as the largest amount of security fixes released on a Microsoft Patch Tuesday, with the second-largest being 123 fixes in July 2020, and the third having 120 fixes in August 2020.
For information about the non-security Windows updates, you can read about today's Windows 10 Cumulative Updates KB4571756 & KB4574727 Released .
Vulnerabilities of interest
While there were no zero-days this month, there were quite a few vulnerabilities that are interesting and can be exploited remotely.
Below are three of the more interesting security vulnerabilities fixed today:
- CVE-2020-16875 - Microsoft Exchange Memory Corruption Vulnerability can allow a remote attacker to perform remote code execution by simply sending an specially crafted email to an Exchange server.
- CVE-2020-0922 - Microsoft COM for Windows Remote Code Execution Vulnerability can be exploited by luring a user to a site with malicious JavaScript.
- CVE-2020-0908 - Windows Text Service Module Remote Code Execution Vulnerability can be exploit by tricking a user to visiting a site that contains malicious "user-provided content or advertisements."
Recent security updates from other companies
Other vendors who released security updates in September include:
- Adobe released security updates today for Adobe Acrobat, Reader, and Lightstream.
- Apple released security updates in iOS 13.7 on September 1st.
- Google Chrome 85.0.4183.83 was released on August 25th, with twenty security fixes .
- Intel patched 4 vulnerabilities today with their September 2020 Platform Update .
- SAP released their September 2020 security updates today.
The September 2020 Patch Tuesday Security Updates
Below is the full list of resolved vulnerabilities and released advisories in the September 2020 Patch Tuesday updates. To access the full description of each vulnerability and the systems that it affects, you can view the full report here .
| Tag | CVE ID | CVE Title | Severity |
|---|---|---|---|
| Active Directory | Active Directory Remote Code Execution Vulnerability | Important | |
| Active Directory | Active Directory Information Disclosure Vulnerability | Important | |
| Active Directory | Active Directory Remote Code Execution Vulnerability | Important | |
| Active Directory | Active Directory Information Disclosure Vulnerability | Important | |
| Active Directory Federation Services | ADFS Spoofing Vulnerability | Important | |
| ASP.NET | Microsoft ASP.NET Core Security Feature Bypass Vulnerability | Important | |
| Common Log File System Driver | Windows Common Log File System Driver Elevation of Privilege Vulnerability | Important | |
| Internet Explorer | WinINet API Elevation of Privilege Vulnerability | Important | |
| Internet Explorer | Internet Explorer Browser Helper Object (BHO) Memory Corruption Vulnerability | Important | |
| Internet Explorer | Windows Start-Up Application Elevation of Privilege Vulnerability | Important | |
| Microsoft Browsers | Microsoft Browser Memory Corruption Vulnerability | Critical | |
| Microsoft Dynamics | Microsoft Dynamics 365 for Finance and Operations (on-premises) Remote Code Execution Vulnerability | Critical | |
| Microsoft Dynamics | Microsoft Dynamics 365 (On-Premise) Cross Site Scripting Vulnerability | Important | |
| Microsoft Dynamics | Microsoft Dynamics 365 (on-premises) Remote Code Execution Vulnerability | Important | |
| Microsoft Dynamics | Microsoft Dynamics 365 (On-Premise) Cross Site Scripting Vulnerability | Important | |
| Microsoft Dynamics | Microsoft Dynamics 365 (On-Premise) Cross Site Scripting Vulnerability | Important | |
| Microsoft Dynamics | Microsoft Dynamics 365 (On-Premise) Cross Site Scripting Vulnerability | Important | |
| Microsoft Dynamics | Microsoft Dynamics 365 (On-Premise) Cross Site Scripting Vulnerability | Important | |
| Microsoft Dynamics | Microsoft Dynamics 365 (On-Premise) Cross Site Scripting Vulnerability | Important | |
| Microsoft Dynamics | Microsoft Dynamics 365 (on-premises) Remote Code Execution Vulnerability | Critical | |
| Microsoft Dynamics | Microsoft Dynamics 365 (On-Premise) Cross Site Scripting Vulnerability | Important | |
| Microsoft Exchange Server | Microsoft Exchange Memory Corruption Vulnerability | Critical | |
| Microsoft Graphics Component | Microsoft Graphics Component Information Disclosure Vulnerability | Important | |
| Microsoft Graphics Component | Windows Graphics Component Elevation of Privilege Vulnerability | Important | |
| Microsoft Graphics Component | Windows Graphics Component Information Disclosure Vulnerability | Important | |
| Microsoft Graphics Component | Windows Win32k Elevation of Privilege Vulnerability | Important | |
| Microsoft Graphics Component | Windows Graphics Component Information Disclosure Vulnerability | Important | |
| Microsoft Graphics Component | Microsoft Graphics Component Information Disclosure Vulnerability | Important | |
| Microsoft Graphics Component | DirectX Elevation of Privilege Vulnerability | Important | |
| Microsoft Graphics Component | DirectX Elevation of Privilege Vulnerability | Important | |
| Microsoft Graphics Component | Win32k Elevation of Privilege Vulnerability | Important | |
| Microsoft Graphics Component | GDI+ Remote Code Execution Vulnerability | Critical | |
| Microsoft Graphics Component | Windows GDI Information Disclosure Vulnerability | Important | |
| Microsoft Graphics Component | Win32k Information Disclosure Vulnerability | Important | |
| Microsoft JET Database Engine | Jet Database Engine Remote Code Execution Vulnerability | Important | |
| Microsoft JET Database Engine | Jet Database Engine Remote Code Execution Vulnerability | Important | |
| Microsoft NTFS | NTFS Elevation of Privilege Vulnerability | Important | |
| Microsoft Office | Microsoft Excel Remote Code Execution Vulnerability | Important | |
| Microsoft Office | Microsoft Excel Remote Code Execution Vulnerability | Important | |
| Microsoft Office | Microsoft Office Information Disclosure Vulnerability | Important | |
| Microsoft Office | Microsoft Word Remote Code Execution Vulnerability | Important | |
| Microsoft Office | Microsoft Excel Remote Code Execution Vulnerability | Important | |
| Microsoft Office | Microsoft Excel Information Disclosure Vulnerability | Important | |
| Microsoft Office | Microsoft Word Remote Code Execution Vulnerability | Important | |
| Microsoft Office | Microsoft Excel Remote Code Execution Vulnerability | Important | |
| Microsoft Office SharePoint | Microsoft Office SharePoint XSS Vulnerability | Important | |
| Microsoft Office SharePoint | Microsoft SharePoint Spoofing Vulnerability | Important | |
| Microsoft Office SharePoint | Microsoft SharePoint Remote Code Execution Vulnerability | Critical | |
| Microsoft Office SharePoint | Microsoft Office SharePoint XSS Vulnerability | Important | |
| Microsoft Office SharePoint | Microsoft SharePoint Remote Code Execution Vulnerability | Critical | |
| Microsoft Office SharePoint | Microsoft SharePoint Server Tampering Vulnerability | Important | |
| Microsoft Office SharePoint | Microsoft SharePoint Server Tampering Vulnerability | Important | |
| Microsoft Office SharePoint | Microsoft SharePoint Remote Code Execution Vulnerability | Critical | |
| Microsoft Office SharePoint | Microsoft Office SharePoint XSS Vulnerability | Important | |
| Microsoft Office SharePoint | Microsoft Office SharePoint XSS Vulnerability | Important | |
| Microsoft Office SharePoint | Microsoft Office SharePoint XSS Vulnerability | Important | |
| Microsoft Office SharePoint | Microsoft SharePoint Remote Code Execution Vulnerability | Critical | |
| Microsoft Office SharePoint | Microsoft SharePoint Remote Code Execution Vulnerability | Critical | |
| Microsoft Office SharePoint | Microsoft Office SharePoint XSS Vulnerability | Important | |
| Microsoft Office SharePoint | Microsoft SharePoint Remote Code Execution Vulnerability | Critical | |
| Microsoft Office SharePoint | Microsoft SharePoint Server Remote Code Execution Vulnerability | Critical | |
| Microsoft OneDrive | OneDrive for Windows Elevation of Privilege Vulnerability | Important | |
| Microsoft OneDrive | OneDrive for Windows Elevation of Privilege Vulnerability | Important | |
| Microsoft OneDrive | OneDrive for Windows Elevation of Privilege Vulnerability | Important | |
| Microsoft Scripting Engine | Scripting Engine Memory Corruption Vulnerability | Critical | |
| Microsoft Scripting Engine | Scripting Engine Memory Corruption Vulnerability | Important | |
| Microsoft Scripting Engine | Scripting Engine Memory Corruption Vulnerability | Critical | |
| Microsoft Windows | TLS Information Disclosure Vulnerability | Important | |
| Microsoft Windows | Windows Runtime Elevation of Privilege Vulnerability | Important | |
| Microsoft Windows | Windows Media Audio Decoder Remote Code Execution Vulnerability | Critical | |
| Microsoft Windows | Windows Elevation of Privilege Vulnerability | Important | |
| Microsoft Windows | Windows UPnP Service Elevation of Privilege Vulnerability | Important | |
| Microsoft Windows | Microsoft splwow64 Elevation of Privilege Vulnerability | Important | |
| Microsoft Windows | Microsoft COM for Windows Remote Code Execution Vulnerability | Critical | |
| Microsoft Windows | Windows Cryptographic Catalog Services Elevation of Privilege Vulnerability | Important | |
| Microsoft Windows | Windows RSoP Service Application Elevation of Privilege Vulnerability | Important | |
| Microsoft Windows | Microsoft Store Runtime Elevation of Privilege Vulnerability | Important | |
| Microsoft Windows | Connected User Experiences and Telemetry Service Elevation of Privilege Vulnerability | Important | |
| Microsoft Windows | Windows Elevation of Privilege Vulnerability | Important | |
| Microsoft Windows | Windows CloudExperienceHost Elevation of Privilege Vulnerability | Important | |
| Microsoft Windows | Projected Filesystem Information Disclosure Vulnerability | Important | |
| Microsoft Windows | Group Policy Elevation of Privilege Vulnerability | Important | |
| Microsoft Windows | Windows InstallService Elevation of Privilege Vulnerability | Important | |
| Microsoft Windows | Windows Function Discovery Service Elevation of Privilege Vulnerability | Important | |
| Microsoft Windows | Windows Runtime Elevation of Privilege Vulnerability | Important | |
| Microsoft Windows | Windows Remote Code Execution Vulnerability | Critical | |
| Microsoft Windows | Windows Storage Services Elevation of Privilege Vulnerability | Important | |
| Microsoft Windows | Microsoft COM for Windows Elevation of Privilege Vulnerability | Important | |
| Microsoft Windows | Windows Media Audio Decoder Remote Code Execution Vulnerability | Critical | |
| Microsoft Windows | Windows State Repository Service Information Disclosure Vulnerability | Important | |
| Microsoft Windows | Windows Storage Services Elevation of Privilege Vulnerability | Important | |
| Microsoft Windows | Windows Mobile Device Management Diagnostics Information Disclosure Vulnerability | Important | |
| Microsoft Windows | Microsoft splwow64 Information Disclosure Vulnerability | Important | |
| Microsoft Windows | Windows Function Discovery SSDP Provider Elevation of Privilege Vulnerability | Important | |
| Microsoft Windows | Windows Routing Utilities Denial of Service | Important | |
| Microsoft Windows | Windows Text Service Module Remote Code Execution Vulnerability | Critical | |
| Microsoft Windows | Windows Elevation of Privilege Vulnerability | Important | |
| Microsoft Windows | Windows Modules Installer Elevation of Privilege Vulnerability | Important | |
| Microsoft Windows | Projected Filesystem Security Feature Bypass Vulnerability | Important | |
| Microsoft Windows | Windows Information Disclosure Vulnerability | Important | |
| Microsoft Windows | Microsoft Store Runtime Elevation of Privilege Vulnerability | Important | |
| Microsoft Windows | Windows Defender Application Control Security Feature Bypass Vulnerability | Important | |
| Microsoft Windows | Windows Language Pack Installer Elevation of Privilege Vulnerability | Important | |
| Microsoft Windows | Windows Shell Infrastructure Component Elevation of Privilege Vulnerability | Important | |
| Microsoft Windows Codecs Library | Microsoft Windows Codecs Library Remote Code Execution Vulnerability | Critical | |
| Microsoft Windows Codecs Library | Windows Camera Codec Pack Remote Code Execution Vulnerability | Critical | |
| Microsoft Windows Codecs Library | Microsoft Windows Codecs Library Remote Code Execution Vulnerability | Critical | |
| Microsoft Windows DNS | Windows dnsrslvr.dll Elevation of Privilege Vulnerability | Important | |
| Microsoft Windows DNS | Windows DNS Denial of Service Vulnerability | Important | |
| Microsoft Windows DNS | Windows DNS Denial of Service Vulnerability | Important | |
| Open Source Software | Xamarin.Forms Spoofing Vulnerability | Important | |
| SQL Server | SQL Server Reporting Services Security Feature Bypass Vulnerability | Moderate | |
| Visual Studio | Visual Studio Remote Code Execution Vulnerability | Critical | |
| Visual Studio | Visual Studio Remote Code Execution Vulnerability | Important | |
| Visual Studio | Visual Studio JSON Remote Code Execution Vulnerability | Important | |
| Windows DHCP Server | Windows DHCP Server Information Disclosure Vulnerability | Important | |
| Windows Diagnostic Hub | Diagnostics Hub Standard Collector Elevation of Privilege Vulnerability | Important | |
| Windows Diagnostic Hub | Diagnostics Hub Standard Collector Elevation of Privilege Vulnerability | Important | |
| Windows Hyper-V | Windows Hyper-V Denial of Service Vulnerability | Important | |
| Windows Hyper-V | Windows Hyper-V Denial of Service Vulnerability | Important | |
| Windows Kernel | Win32k Information Disclosure Vulnerability | Important | |
| Windows Kernel | Windows Kernel Information Disclosure Vulnerability | Important | |
| Windows Kernel | Windows Kernel Information Disclosure Vulnerability | Important | |
| Windows Kernel | Windows Kernel Elevation of Privilege Vulnerability | Important | |
| Windows Kernel | Windows Kernel Information Disclosure Vulnerability | Important | |
| Windows Kernel | Windows Kernel Information Disclosure Vulnerability | Important | |
| Windows Kernel | Windows Kernel Information Disclosure Vulnerability | Important | |
| Windows Print Spooler Components | Windows Print Spooler Elevation of Privilege Vulnerability | Important | |
| Windows Shell | Shell infrastructure component Elevation of Privilege Vulnerability | Important |
Related Articles:
Windows 10 KB5037768 update released with new features and 20 fixes
Microsoft June 2024 Patch Tuesday fixes 51 flaws, 18 RCEs
Windows 10 KB5039211 update released with new feature, 12 fixes
Microsoft May 2024 Patch Tuesday fixes 3 zero-days, 61 flaws
Windows 11 KB5039212 update released with 37 changes, fixes
- Patch Tuesday
- Security Update
- Vulnerability
- Windows Update
- Previous Article
- Next Article
Post a Comment Community Rules
You need to login in order to post a comment.
Not a member yet? Register Now
You may also like:
Dev rejects CVE severity, makes his GitHub repo read-only
New regreSSHion OpenSSH RCE bug gives root on Linux servers
Help us understand the problem. What is going on with this comment?
- Abusive or Harmful
- Inappropriate content
- Strong language
Read our posting guidelinese to learn what content is prohibited.
Enterprise TruRisk Platform
Everything you need to measure, manage, and reduce your cyber risk in one place
CAPABILITIES
- Asset Management
- Vulnerability & Configuration Management
- Risk Remediation
- Threat Detection & Response
- Cloud Security
PLATFORM APPS
Asset management.
See entire attack surface, continuously maintain your CMDB, and track EOL/EOS software
Gain an attacker’s view of your external internet-facing assets and unauthorized software
Vulnerability & Configuration Management
Discover, assess, prioritize, and patch critical vulnerabilities up to 50% faster
Consolidate & translate security & vulnerability findings from 3rd party tools
Automate scanning in CI/CD environments with shift left DAST testing
Detect, prioritize, and remediate vulnerabilities in your cloud environment
Risk REMEDIATION
Efficiently remediate vulnerabilities and patch systems
Quickly create custom scripts and controls for faster, more automated remediation
Threat Detection and Response
Advanced endpoint threat protection, improved threat context, and alert prioritization
Extend detection and response beyond the endpoint to the enterprise
Reduce risk, and comply with internal policies and external regulations with ease
Reduce alert noise and safeguard files from nefarious actors and cyber threats
Cloud-Native Application Protection Platform (CNAPP) for multi-cloud environment.
Continuously discover, monitor, and analyze your cloud assets for misconfigurations and non-standard deployments.
Detect and remediate security issues within IaC templates
Manage your security posture and risk across your entire SaaS application stack
Continuous real-time protection of the multi-cloud environment against active exploitation, malware, and unknown threats.
Discover, track, and continuously secure containers – from build to runtime
- Endpoint Security
- PCI Compliance
- DORA Compliance
- Application Security
- Threat Protection
- Zero-Trust Security
- Small Business
- Mid-Sized Business
- Resources Library
- Product Tours
- Qualys Stream
- Fundamentals
- Threat Research Unit
- Security Alerts
- Security Advisories
- Support Portal
- Free Training
- Documentation
- Community Discussions
- Knowledgebase
- Release Notes
- Release Notifications
- Best Practices
- Success Stories
- Testimonials
- Partner Program
- VAD Partners
- VAR Resellers
- MSP/MSSP Partners
- Integration Partners
- Partner FAQs
- Find a Partner
- Investor Relations
- US Platform 1
- US Platform 2
- US Platform 3
- US Platform 4
- CA Platform 1
- EU Platform 1
- EU Platform 2
- EU Platform 3
- IN Platform 1
- AE Platform 1
- UK Platform 1
- AU Platform 1
- KSA Platform 1
- PCI Platform
Contact us below to request a quote, or for any product-related questions
- Create Account. It’s Free!
- Try PM for free
- Try VMDR for free
- Try VMDR TruRisk for free
- Try CS for free
- Sign up for TotalCloud
- Sign up for CDR
- Try CSAM for free
- Try PCI for free
- Try DORA for free
- Try Policy Compliance for free
- Try VMDR for Mobile Devices
- Try SaaSDR for free
- Try Multi-Vector EDR for Free
- Try CAR for Free
- Request a Demo
- Cloud Platform - Free Trial
Free Services
- 60-Day Remote Endpoint Protection
- Global AssetView
- Community Edition
- BrowserCheck
- Quick Links
- Resources (guides, whitepapers, etc.)
- Qualys Cloud Apps
- Events calendar
- Qualys Community
- Events Calendar
- Cloud Platform
Platform Apps
- CyberSecurity Asset Management (CSAM)
- External Attack Surface Management (EASM) - New
- Vulnerability Management, Detection & Response (VMDR) – Most Popular
- Enterprise TruRisk Management (ETM) - New
- Web App Scanning (WAS)
- Patch Management (PM)
- Custom Assessment and Remediation (CAR)
- Qualys Endpoint Security
- Context XDR
- Policy Compliance
- File Integrity Monitoring (FIM)
- TotalCloud (CNAPP)
- Cloud Security Posture Management (CSPM)
- Infrastructure as Code Security (IaC)
- SaaS Security Posture Management (SSPM) - New
- Cloud Workload Protection (CWP)
- Cloud Detection & Response (CDR)
- Container Security (CS)
- What's my platform?
- Chat With Us
- Schedule a Demo
- +1 800 745 4355
- Request a Call or Email
- Global Offices and Contacts
Microsoft security alert.
September 8, 2020, advisory overview.
Qualys Vulnerability R&D Lab has released new vulnerability checks in the Enterprise TruRisk Platform to protect organizations against 127 vulnerabilities that were fixed in 12 bulletins announced today by Microsoft. Customers can immediately audit their networks for these and other new vulnerabilities by accessing their Qualys subscription. Visit Qualys Security Blog to prioritize remediation .
Non-Qualys customers can audit their network for these and other vulnerabilities by signing up for a Qualys Free Trial , or by trying Qualys Community Edition .
Vulnerability details
Microsoft has released 12 security bulletins to fix newly discovered flaws in their software. Qualys has released the following checks for these new vulnerabilities:
Microsoft Internet Explorer Security Update for September 2020
Patches: The following are links for downloading patches to fix these vulnerabilities: Microsoft Security Update Guide Windows
Microsoft SharePoint Foundation and SharePoint Server Update September 2020
Patches: The following are links for downloading patches to fix these vulnerabilities: Microsoft SharePoint Foundation and SharePoint Server September 2020
Microsoft Office and Microsoft Office Services and Web Apps Security Update September 2020
Patches: The following are links for downloading patches to fix these vulnerabilities: Microsoft Office and Microsoft Office Services and Web Apps Security Update September 2020
Microsoft Exchange Server Security Update for September 2020
Patches: The following are links for downloading patches to fix these vulnerabilities: Download Security Update For Exchange Server 2016 Cumulative Update 16 (KB4577352) Windows Download Security Update For Exchange Server 2016 Cumulative Update 17 (KB4577352) Windows Download Security Update For Exchange Server 2019 Cumulative Update 5 (KB4577352) Windows Download Security Update For Exchange Server 2019 Cumulative Update 6 (KB4577352) WIndows
Microsoft Dynamics 365 Security Update for September 2020
Patches: The following are links for downloading patches to fix these vulnerabilities: KB4574742 KB4577501
Microsoft SQL Server Reporting Services Update for September 2020
Patches: The following are links for downloading patches to fix these vulnerabilities: SQL Server 2017 Reporting Services Windows SQL Server 2019 Reporting Services Windows
Microsoft Windows Security Update for September 2020
Microsoft visual studio security update for september 2020.
Patches: The following are links for downloading patches to fix these vulnerabilities: CVE-2020-1130 WIndows CVE-2020-1133 WIndows CVE-2020-16856 WIndows CVE-2020-16874 WIndows
Microsoft OneDrive for Windows Elevation of Privilege Vulnerability
Patches: The following are links for downloading patches to fix these vulnerabilities: CVE-2020-16851 WIndows CVE-2020-16852 WIndows CVE-2020-16853 WIndows
Microsoft ASP.NET Core Security Feature Bypass Vulnerability September 2020
Patches: The following are links for downloading patches to fix these vulnerabilities: .Net Core 2.1 .Net Core 3.1
Microsoft Edge Security Update for September 2020
Patches: The following are links for downloading patches to fix these vulnerabilities: CVE-2020-0878 CVE-2020-1057 CVE-2020-1172 CVE-2020-1180
Microsoft Windows Servicing Stack Security Update September 2020
Patches: The following are links for downloading patches to fix these vulnerabilities: ADV990001
These new vulnerability checks are included in Qualys vulnerability signature 2.4.979-3. Each Qualys account is automatically updated with the latest vulnerability signatures as they become available. To view the vulnerability signature version in your account, from the Qualys Help menu, select the About tab.
Selective Scan Instructions Using Qualys
To perform a selective vulnerability scan, configure a scan profile to use the following options:
- Ensure access to TCP ports 135 and 139 are available.
- Enable Windows Authentication (specify Authentication Records).
- If you would like the scan to return the Windows Hostname, also include QID 82044 and ensure access to UDP port 137 is available.
- If you would like to be notified if Qualys is unable to log on to a host (if Authentication fails), also include QID 105015.
In addition, prior to running a scan for these new vulnerabilities, you can estimate your exposure to these new threats by running the Risk Analysis Report, available from the Qualys Vulnerability Management Reports tab.
Access for Qualys Customers
Platforms and Platform Identification
Technical Support
For more information, customers may contact Qualys Technical Support .
About Qualys
The Enterprise TruRisk Platform and its integrated suite of security and compliance applications provides organizations of all sizes with a global view of their security and compliance solutions, while drastically reducing their total cost of ownership. Qualys solutions include: continuous monitoring, vulnerability management, policy compliance, PCI compliance, security assessment questionnaire, web application scanning, web application firewall, malware detection and SECURE Seal for security testing of web sites.
Log4Shell Response

- Basic search
- Lucene search
- Search by product
Security Updates for Microsoft SQL Server Reporting Services (September 2020)
Attack Vector
Attack Complexity
Authentication
Confidentiality Impact
Integrity Impact
Availability Impact
AV:N/AC:L/Au:S/C:N/I:P/A:N
Privileges Required
User Interaction
CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N
The Microsoft SQL Server Reporting Services installation on the remote host is missing a security update. It is, therefore, affected by a security feature bypass vulnerability in SQL Server Reporting Services (SSRS) due to improper validation of uploaded attachments to reports. An authenticated, remote attacker could exploit this issue to upload file types that were disallowed by an administrator. (CVE-2020-1044)
| Vendor | Product | Version | CPE |
|---|---|---|---|
| cpe:/a:microsoft:sql_server_reporting_services |
cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-1044
www.nessus.org/u?5708b76b



How to Update SQL Server Reporting Services (SSRS) 2017 or Later
A common question I usually get from fellow SQL Server community members, is how to update SQL Server Reporting Services (SSRS) 2017?
This is a good question, because since SQL Server 2017 and later, SSRS is no longer part of the SQL Server installation media. To this end, SSRS 2017 and later can be found as standalone installation packages.
Downloading SQL Server Reporting Services (SSRS) 2017 and Later
SQL Server Reporting Services (SSRS) 2017 can be downloaded on this MS download link
SQL Server Reporting Services (SSRS) 2019 can be downloaded on this MS download link .
Updating SQL Server Reporting Services (SSRS) 2017 and Later
So the question remains: how can you update SSRS?
If you try to update SSRS 2017 or later, using a SQL Server service pack media or Cumulative Update (CU), the installer will not be finding any SQL Server components/features to update.
So, in order to update SSRS 2017 or later, you just need to download the latest SSRS installer from Microsoft, and run the installation process on the SSRS server to be updated. Then, after running the installer, you will be asked whether you want to proceed with updating the existing SSRS installation or not.
Check our Master Class “Essential SQL Server Administration Tips”
If you really want to learn sophisticated SQL Server administration techniques, then you should check our on-demand online course titled “ Essential SQL Server Administration Tips ” (special limited-time discount included in link).
Via the course, you will learn essential hands-on SQL Server Administration tips on SQL Server maintenance, security, performance, integration, error handling and more. Many live demonstrations and downloadable resources included!
Featured Online Courses:
- Introduction to Azure Database for MySQL
- Working with Python on Windows and SQL Server Databases
- Boost SQL Server Database Performance with In-Memory OLTP
- Introduction to Azure SQL Database for Beginners
- Essential SQL Server Administration Tips
- SQL Server Fundamentals – SQL Database for Beginners
- Essential SQL Server Development Tips for SQL Developers
- Introduction to Computer Programming for Beginners
- .NET Programming for Beginners – Windows Forms with C#
- Introduction to SQL Server Machine Learning Services
- SQL Server 2019: What’s New – New and Enhanced Features
- Entity Framework: Getting Started – Complete Beginners Guide
- How to Import and Export Data in SQL Server Databases
- Learn How to Install and Start Using SQL Server in 30 Mins
- A Guide on How to Start and Monetize a Successful Blog
Related SQL Server Administration Articles:
- Essential SQL Sever Administration Tips
- How to Patch a Standalone SQL Server Instance
- The SQL Server Browser Service and UDP Port 1434
- The Maximum Number of Concurrent Connections Setting in SQL Server
- Top 10 SQL Server DBA Daily Tasks List
- There is no SQL Server Failover Cluster Available to Join
- Encrypting a SQL Server Database Backup
- How to Resolve: The feature “Scale-out deployment” is not supported in this edition of Reporting Services
- …more
Reference: SQLNetHub.com ( https://www.sqlnethub.com )
© SQLNetHub
Artemakis Artemiou, a distinguished Senior Database and Software Architect, brings over 20 years of expertise to the IT industry. A Certified Database, Cloud, and AI professional, he earned the Microsoft Data Platform MVP title for nine consecutive years (2009-2018). As the founder of SQLNetHub and GnoelixiAI Hub , Artemakis is dedicated to sharing his knowledge and democratizing education on various fields such as: Databases, Cloud, AI, and Software Development. His commitment to simplicity and knowledge sharing defines his impactful presence in the tech community.
Privacy Overview
| Cookie | Duration | Description |
|---|---|---|
| cookielawinfo-checkbox-analytics | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Analytics". |
| cookielawinfo-checkbox-functional | 11 months | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Functional". |
| cookielawinfo-checkbox-necessary | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Necessary". |
| cookielawinfo-checkbox-others | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Other. |
| cookielawinfo-checkbox-performance | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Performance". |
| viewed_cookie_policy | 11 months | The cookie is set by the GDPR Cookie Consent plugin and is used to store whether or not user has consented to the use of cookies. It does not store any personal data. |
SQL Server Reporting Services (SSRS) Versions
Microsoft SQL Server Reporting Services ( SSRS or S.S.R.S. or RS ) is a native server-based reporting platform for creating reports from relational or multidimensional data sources.
A widely used and dynamic tool it provides a comprehensive, server-based reporting solution that allows the authoring, manageability, and delivery of reports in multiple ways and formats, such as on the Web or via e-mail, in Excel, PDF, CSV, XML and Word etc.
SQL Server Reporting Services (SSRS) is a separate install from SQL Server 2017 onwards.
Reporting Services 2022 build numbers:
| Build | Alternative builds | File version | Alternative file version | KB / Description | Release date |
|---|---|---|---|---|---|
| 16.0.1115.96 | 16.0.1115 16.00.1115 16.00.1115.96 | 16.0.8898.18912 | 16.0.8898 16.0.8898.0 | *new | |
| 16.0.1115.92 | 16.0.1115 16.00.1115 16.00.1115.92 | 16.0.8886.1775 | 16.0.8886 16.0.8886.0 | ||
| 16.0.1115.61 | 16.0.1115 16.00.1115 16.00.1115.61 | 16.0.8784.14010 | 16.0.8784 16.0.8784.0 | ||
| 16.0.1114.11 | 16.0.1114 16.00.1114 16.00.1114.11 | 16.0.8564.33454 | 16.0.8564 16.0.8564.0 | ||
| 16.0.1113.11 | 16.0.1113 16.00.1113 16.00.1113.11 | 16.0.8361.39598 | 16.0.8361 16.0.8361.0 | ||
| 16.0.1112.48 | 16.0.1112 16.00.1112 16.00.1112.48 | 16.0.8353.8096 | 16.0.8353 16.0.8353.0 | ||
| 15.0.1111.106 | 15.0.1111 15.00.1111 15.00.1111.106 | 15.0.8264.8408 | 15.0.8264 15.0.8264.0 |
Reporting Services 2019 build numbers:
| Build | Alternative builds | File version | Alternative file version | KB / Description | Release date |
|---|---|---|---|---|---|
| 15.0.1102.1167 | 15.0.1102 15.00.1102 15.00.1102.1167 | 15.0.8863.19101 | 15.0.8863 15.0.8863.0 | *new | |
| 15.0.1102.1166 | 15.0.1102 15.00.1102 15.00.1102.1166 | 15.0.8863.19101 | 15.0.8863 15.0.8863.0 | ||
| 15.0.1102.1140 | 15.0.1102 15.00.1102 15.00.1102.1140 | 15.0.8760.20928 | 15.0.8760 15.0.8760.0 | ||
| 15.0.1102.1129 | 15.0.1102 15.00.1102 15.00.1102.1129 | 15.0.8738.29460 | 15.0.8738 15.0.8738.0 | ||
| 15.0.1102.1084 | 15.0.1102 15.00.1102 15.00.1102.1084 | 15.0.8599.29221 | 15.0.8599 15.0.8599.0 | ||
| 15.0.1102.1075 | 15.0.1102 15.00.1102 15.00.1102.1075 | 15.0.8563.17333 | 15.0.8563 15.0.8563.0 | ||
| 15.0.1102.1047 | 15.0.1102 15.00.1102 15.00.1102.1047 | 15.0.8434.2956 | 15.0.8434 15.0.8434.0 | ||
| 15.0.1102.1002 | 15.0.1102 15.00.1102 15.00.1102.1002 | 15.0.8276.32713 | 15.0.8276 15.0.8276.0 | ||
| 15.0.1102.962 | 15.0.1102 15.00.1102 15.00.1102.962 | 15.0.8115.18148 | 15.0.8115 15.0.8115.0 | ||
| 15.0.1102.932 | 15.0.1102 15.00.1102 15.00.1102.932 | 15.0.7961.31630 | 15.0.7961 15.0.7961.0 | ||
| 15.0.1102.911 | 15.0.1102 15.00.1102 15.00.1102.911 | 15.0.7842.32355 | 15.0.7842 15.0.7842.0 | ||
| 15.0.1102.896 | 15.0.1102 15.00.1102 15.00.1102.896 | 15.0.7765.17516 | 15.0.7765 15.0.7765.0 | ||
| 15.0.1102.861 | 15.0.1102 15.00.1102 15.00.1102.861 | 15.0.7545.4810 | 15.0.7545 15.0.7545.0 | ||
| 15.0.1102.675 | 15.0.1102 15.00.1102 15.00.1102.675 | 15.0.7243.37714 | 15.0.7243 15.0.7243.0 |
Reporting Services 2017 build numbers:
| Build | Alternative builds | File version | Alternative file version | KB / Description | Release date |
|---|---|---|---|---|---|
| 14.0.601.20 | 14.0.601 14.00.601 14.00.601.20 | 14.0.8444.41957 | 14.0.8444 14.0.8444.0 | ||
| 14.0.600.1860 | 14.0.600 14.00.600 14.00.600.1860 | 14.0.8091.35795 | 14.0.8091 14.0.8091.0 | ||
| 14.0.600.1763 | 14.0.600 14.00.600 14.00.600.1763 | 14.0.7844.42503 | 14.0.7844 14.0.7844.0 | ||
| 14.0.600.1669 | 14.0.600 14.00.600 14.00.600.1669 | 14.0.7544.5078 | 14.0.7544 14.0.7544.0 | ||
| 14.0.600.1572 | 14.0.600 14.00.600 14.00.600.1572 | ||||
| 14.0.600.1453 | 14.0.600 14.00.600 14.00.600.1453 | SQL Server Reporting Services 2017 – November 2019 Release 2 | |||
| 14.0.600.1451 | 14.0.600 14.00.600 14.00.600.1451 | ||||
| 14.0.600.1274 | 14.0.600 14.00.600 14.00.600.1274 | ||||
| 14.0.600.1109 | 14.0.600 14.00.600 14.00.600.1109 | ||||
| 14.0.600.906 | 14.0.600 14.00.600 14.00.600.906 | ||||
| 14.0.600.892 | 14.0.600 14.00.600 14.00.600.892 | ||||
| 14.0.600.744 | 14.0.600 14.00.600 14.00.600.744 | ||||
| 14.0.600.689 | 14.0.600 14.00.600 14.00.600.689 | ||||
| 14.0.600.594 | 14.0.600 14.00.600 14.00.600.594 | ||||
| 14.0.600.490 | 14.0.600 14.00.600 14.00.600.490 | ||||
| 14.0.600.451 | 14.0.600 14.00.600 14.00.600.451 |
Reporting Services 2016 build numbers:
| Build | Alternative builds | File version | Alternative file version | KB / Description | Release date |
|---|---|---|---|---|---|
| 13.0.6300.2 | 13.0.6300 13.00.6300 13.00.6300.2 | 2015.132.6300.2 | 2015.132.6300 2015.132.6300.0 2015.130.6300.2 2015.130.6300 2015.130.6300.0 | ||
| 13.0.5888.11 | 13.0.5888 13.00.5888 13.00.5888.11 | 2015.131.5888.11 | 2015.131.5888 2015.131.5888.0 2015.130.5888.11 2015.130.5888 2015.130.5888.0 | ||
| 13.0.5882.1 | 13.0.5882 13.00.5882 13.00.5882.1 | 2015.131.5882.1 | 2015.131.5882 2015.131.5882.0 2015.130.5882.1 2015.130.5882 2015.130.5882.0 | ||
| 13.0.5850.14 | 13.0.5850 13.00.5850 13.00.5850.14 | 2015.131.5850.14 | 2015.131.5850 2015.131.5850.0 2015.130.5850.14 2015.130.5850 2015.130.5850.0 | ||
| 13.0.5830.85 | 13.0.5830 13.00.5830 13.00.5830.85 | 2015.131.5830.85 | 2015.131.5830 2015.131.5830.0 2015.130.5830.85 2015.130.5830 2015.130.5830.0 | ||
| 13.0.5820.21 | 13.0.5820 13.00.5820 13.00.5820.21 | 2015.131.5820.21 | 2015.131.5820 2015.131.5820.0 2015.130.5820.21 2015.130.5820 2015.130.5820.0 | ||
| 13.0.5698.0 | 13.0.5698 13.00.5698 13.00.5698.0 | 2015.131.5698.0 | 2015.131.5698 2015.130.5698.0 2015.130.5698 | ||
| 13.0.5622.0 | 13.0.5622 13.00.5622 13.00.5622.0 | 2015.131.5622.0 | 2015.131.5622 2015.130.5622.0 2015.130.5622 | ||
| 13.0.5598.27 | 13.0.5598 13.00.5598 13.00.5598.27 | 2015.131.5598.27 | 2015.131.5598 2015.131.5598.0 2015.130.5598.27 2015.130.5598 2015.130.5598.0 | ||
| 13.0.5492.2 | 13.0.5492 13.00.5492 13.00.5492.2 | 2015.131.5492.2 | 2015.131.5492 2015.131.5492.0 2015.130.5492.2 2015.130.5492 2015.130.5492.0 | ||
| 13.0.5470.0 | 13.0.5470 13.00.5470 13.00.5470.0 | 2015.131.5470.0 | 2015.131.5470 2015.130.5470.0 2015.130.5470 | ||
| 13.0.5426.0 | 13.0.5426 13.00.5426 13.00.5426.0 | 2015.131.5426.0 | 2015.131.5426 2015.130.5426.0 2015.130.5426 | ||
| 13.0.5366.0 | 13.0.5366 13.00.5366 13.00.5366.0 | 2015.131.5366.0 | 2015.131.5366 2015.130.5366.0 2015.130.5366 | ||
| 13.0.5337.0 | 13.0.5337 13.00.5337 13.00.5337.0 | 2015.131.5337.0 | 2015.131.5337 2015.130.5337.0 2015.130.5337 | ||
| 13.0.5292.0 | 13.0.5292 13.00.5292 13.00.5292.0 | 2015.131.5292.0 | 2015.131.5292 2015.130.5292.0 2015.130.5292 | ||
| 13.0.5264.1 | 13.0.5264 13.00.5264 13.00.5264.1 | 2015.131.5264.1 | 2015.131.5264 2015.131.5264.0 2015.130.5264.1 2015.130.5264 2015.130.5264.0 | ||
| 13.0.5233.0 | 13.0.5233 13.00.5233 13.00.5233.0 | 2015.131.5233.0 | 2015.131.5233 2015.130.5233.0 2015.130.5233 | ||
| 13.0.5216.0 | 13.0.5216 13.00.5216 13.00.5216.0 | 2015.131.5216.0 | 2015.131.5216 2015.130.5216.0 2015.130.5216 | ||
| 13.0.5201.2 | 13.0.5201 13.00.5201 13.00.5201.2 | 2015.131.5201.2 | 2015.131.5201 2015.131.5201.0 2015.130.5201.2 2015.130.5201 2015.130.5201.0 | ||
| 13.0.5153.0 | 13.0.5153 13.00.5153 13.00.5153.0 | 2015.131.5153.0 | 2015.131.5153 2015.130.5153.0 2015.130.5153 | ||
| 13.0.5149.0 | 13.0.5149 13.00.5149 13.00.5149.0 | 2015.131.5149.0 | 2015.131.5149 2015.130.5149.0 2015.130.5149 | ||
| 13.0.5102.14 | 13.0.5102 13.00.5102 13.00.5102.14 | 2015.131.5102.14 | 2015.131.5102 2015.131.5102.0 2015.130.5102.14 2015.130.5102 2015.130.5102.0 | ||
| 13.0.5026.0 | 13.0.5026 13.00.5026 13.00.5026.0 | 2015.131.5026.0 | 2015.131.5026 2015.130.5026.0 2015.130.5026 | ||
| 13.0.5026.0 | 13.0.5026 13.00.5026 13.00.5026.0 | 2015.131.5026.0 | 2015.131.5026 2015.130.5026.0 2015.130.5026 | ||
| 13.0.5026.0 | 13.0.5026 13.00.5026 13.00.5026.0 | 2015.131.5026.0 | 2015.131.5026 2015.130.5026.0 2015.130.5026 | ||
| 13.0.5026.0 | 13.0.5026 13.00.5026 13.00.5026.0 | 2015.131.5026.0 | 2015.131.5026 2015.130.5026.0 2015.130.5026 | ||
| 13.0.4604.0 | 13.0.4604 13.00.4604 13.00.4604.0 | 2015.130.4604.0 | 2015.130.4604 | ||
| 13.0.4574.0 | 13.0.4574 13.00.4574 13.00.4574.0 | 2015.130.4574.0 | 2015.130.4574 | ||
| 13.0.4560.0 | 13.0.4560 13.00.4560 13.00.4560.0 | 2015.130.4560.0 | 2015.130.4560 | ||
| 13.0.4550.1 | 13.0.4550 13.00.4550 13.00.4550.1 | 2015.130.4550.1 | 2015.130.4550 2015.130.4550.0 | ||
| 13.0.4541.0 | 13.0.4541 13.00.4541 13.00.4541.0 | 2015.130.4541.0 | 2015.130.4541 | ||
| 13.0.4528.0 | 13.0.4528 13.00.4528 13.00.4528.0 | 2015.130.4528.0 | 2015.130.4528 | ||
| 13.0.4522.0 | 13.0.4522 13.00.4522 13.00.4522.0 | 2015.130.4522.0 | 2015.130.4522 | ||
| 13.0.4514.0 | 13.0.4514 13.00.4514 13.00.4514.0 | 2015.130.4514.0 | 2015.130.4514 | ||
| 13.0.4502.0 | 13.0.4502 13.00.4502 13.00.4502.0 | 2015.130.4502.0 | 2015.130.4502 | ||
| 13.0.4474.0 | 13.0.4474 13.00.4474 13.00.4474.0 | 2015.130.4474.0 | 2015.130.4474 | ||
| 13.0.4466.4 | 13.0.4466 13.00.4466 13.00.4466.4 | 2015.130.4466.4 | 2015.130.4466 2015.130.4466.0 | ||
| 13.0.4466.4 | 13.0.4466 13.00.4466 13.00.4466.4 | 2015.130.4466.4 | 2015.130.4466 2015.130.4466.0 | ||
| 13.0.4457.0 | 13.0.4457 13.00.4457 13.00.4457.0 | 2015.130.4457.0 | 2015.130.4457 | ||
| 13.0.4451.0 | 13.0.4451 13.00.4451 13.00.4451.0 | 2015.130.4451.0 | 2015.130.4451 | ||
| 13.0.4446.0 | 13.0.4446 13.00.4446 13.00.4446.0 | 2015.130.4446.0 | 2015.130.4446 | ||
| 13.0.4435.0 | 13.0.4435 13.00.4435 13.00.4435.0 | 2015.130.4435.0 | 2015.130.4435 | ||
| 13.0.4422.0 | 13.0.4422 13.00.4422 13.00.4422.0 | 2015.130.4422.0 | 2015.130.4422 | ||
| 13.0.4411.0 | 13.0.4411 13.00.4411 13.00.4411.0 | 2015.130.4411.0 | 2015.130.4411 | ||
| 13.0.4259.0 | 13.0.4259 13.00.4259 13.00.4259.0 | 2015.130.4259.0 | 2015.130.4259 | ||
| 13.0.4224.16 | 13.0.4224 13.00.4224 13.00.4224.16 | 2015.130.4224.16 | 2015.130.4224 2015.130.4224.0 | ||
| 13.0.4210.6 | 13.0.4210 13.00.4210 13.00.4210.6 | 2015.130.4210.6 | 2015.130.4210 2015.130.4210.0 | ||
| 13.0.4001.0 | 13.0.4001 13.00.4001 13.00.4001.0 | 2015.130.4001.0 | 2015.130.4001 | ||
| 13.0.2218.0 | 13.0.2218 13.00.2218 13.00.2218.0 | 2015.130.2218.0 | 2015.130.2218 | ||
| 13.0.2216.0 | 13.0.2216 13.00.2216 13.00.2216.0 | 2015.130.2216.0 | 2015.130.2216 | ||
| 13.0.2213.0 | 13.0.2213 13.00.2213 13.00.2213.0 | 2015.130.2213.0 | 2015.130.2213 | ||
| 13.0.2210.0 | 13.0.2210 13.00.2210 13.00.2210.0 | 2015.130.2210.0 | 2015.130.2210 | ||
| 13.0.2204.0 | 13.0.2204 13.00.2204 13.00.2204.0 | 2015.130.2204.0 | 2015.130.2204 | ||
| 13.0.2197.0 | 13.0.2197 13.00.2197 13.00.2197.0 | 2015.130.2197.0 | 2015.130.2197 | ||
| 13.0.2193.0 | 13.0.2193 13.00.2193 13.00.2193.0 | 2015.130.2193.0 | 2015.130.2193 | ||
| 13.0.2186.6 | 13.0.2186 13.00.2186 13.00.2186.6 | 2015.130.2186.6 | 2015.130.2186 2015.130.2186.0 | ||
| 13.0.2164.0 | 13.0.2164 13.00.2164 13.00.2164.0 | 2015.130.2164.0 | 2015.130.2164 | ||
| 13.0.2149.0 | 13.0.2149 13.00.2149 13.00.2149.0 | 2015.130.2149.0 | 2015.130.2149 | ||
| 13.0.1745.2 | 13.0.1745 13.00.1745 13.00.1745.2 | 2015.130.1745.2 | 2015.130.1745 2015.130.1745.0 | ||
| 13.0.1601.5 | 13.0.1601 13.00.1601 13.00.1601.5 | 2015.130.1601.5 | 2015.130.1601 2015.130.1601.0 | ||
| 13.0.1601.5 | 13.0.1601 13.00.1601 13.00.1601.5 | 2015.130.1601.5 | 2015.130.1601 2015.130.1601.0 | ||
| 13.0.1601.5 | 13.0.1601 13.00.1601 13.00.1601.5 | 2015.130.1601.5 | 2015.130.1601 2015.130.1601.0 | ||
| 13.0.1601.5 | 13.0.1601 13.00.1601 13.00.1601.5 | 2015.130.1601.5 | 2015.130.1601 2015.130.1601.0 | ||
| 13.0.1601.5 | 13.0.1601 13.00.1601 13.00.1601.5 | 2015.130.1601.5 | 2015.130.1601 2015.130.1601.0 | ||
| 13.0.1601.5 | 13.0.1601 13.00.1601 13.00.1601.5 | 2015.130.1601.5 | 2015.130.1601 2015.130.1601.0 | ||
| 13.0.1601.5 | 13.0.1601 13.00.1601 13.00.1601.5 | 2015.130.1601.5 | 2015.130.1601 2015.130.1601.0 | SQL Server Reporting Services 2016 RTM |
Reporting Services 2014 build numbers:
| Build | Alternative builds | File version | Alternative file version | KB / Description | Release date |
|---|---|---|---|---|---|
| 12.0.6433.1 | 12.0.6433 12.00.6433 12.00.6433.1 | 2014.120.6433.1 | 2014.120.6433 2014.120.6433.0 | ||
| 12.0.6372.1 | 12.0.6372 12.00.6372 12.00.6372.1 | 2014.120.6372.1 | 2014.120.6372 2014.120.6372.0 | ||
| 12.0.6329.1 | 12.0.6329 12.00.6329 12.00.6329.1 | 2014.120.6329.1 | 2014.120.6329 2014.120.6329.0 | ||
| 12.0.6293.0 | 12.0.6293 12.00.6293 12.00.6293.0 | 2014.120.6293.0 | 2014.120.6293 | ||
| 12.0.6259.0 | 12.0.6259 12.00.6259 12.00.6259.0 | 2014.120.6259.0 | 2014.120.6259 | ||
| 12.0.6214.1 | 12.0.6214 12.00.6214 12.00.6214.1 | 2014.120.6214.1 | 2014.120.6214 2014.120.6214.0 | ||
| 12.0.6205.1 | 12.0.6205 12.00.6205 12.00.6205.1 | 2014.120.6205.1 | 2014.120.6205 2014.120.6205.0 | ||
| 12.0.6118.4 | 12.0.6118 12.00.6118 12.00.6118.4 | 2014.120.6118.4 | 2014.120.6118 2014.120.6118.0 | ||
| 12.0.6108.1 | 12.0.6108 12.00.6108 12.00.6108.1 | 2014.120.6108.1 | 2014.120.6108 2014.120.6108.0 | ||
| 12.0.5687.1 | 12.0.5687 12.00.5687 12.00.5687.1 | 2014.120.5687.1 | 2014.120.5687 2014.120.5687.0 | ||
| 12.0.5659.1 | 12.0.5659 12.00.5659 12.00.5659.1 | 2014.120.5659.1 | 2014.120.5659 2014.120.5659.0 | ||
| 12.0.5632.1 | 12.0.5632 12.00.5632 12.00.5632.1 | 2014.120.5632.1 | 2014.120.5632 2014.120.5632.0 | ||
| 12.0.5626.1 | 12.0.5626 12.00.5626 12.00.5626.1 | 2014.120.5626.1 | 2014.120.5626 2014.120.5626.0 | ||
| 12.0.5605.1 | 12.0.5605 12.00.5605 12.00.5605.1 | 2014.120.5605.1 | 2014.120.5605 2014.120.5605.0 | ||
| 12.0.5600.1 | 12.0.5600 12.00.5600 12.00.5600.1 | 2014.120.5600.1 | 2014.120.5600 2014.120.5600.0 | ||
| 12.0.5590.1 | 12.0.5590 12.00.5590 12.00.5590.1 | 2014.120.5590.1 | 2014.120.5590 2014.120.5590.0 | ||
| 12.0.5589.7 | 12.0.5589 12.00.5589 12.00.5589.7 | 2014.120.5589.7 | 2014.120.5589 2014.120.5589.0 | ||
| 12.0.5579.0 | 12.0.5579 12.00.5579 12.00.5579.0 | 2014.120.5579.0 | 2014.120.5579 | ||
| 12.0.5571.0 | 12.0.5571 12.00.5571 12.00.5571.0 | 2014.120.5571.0 | 2014.120.5571 | ||
| 12.0.5571.0 | 12.0.5571 12.00.5571 12.00.5571.0 | 2014.120.5571.0 | 2014.120.5571 | ||
| 12.0.5563.0 | 12.0.5563 12.00.5563 12.00.5563.0 | 2014.120.5563.0 | 2014.120.5563 | ||
| 12.0.5557.0 | 12.0.5557 12.00.5557 12.00.5557.0 | 2014.120.5557.0 | 2014.120.5557 | ||
| 12.0.5556.0 | 12.0.5556 12.00.5556 12.00.5556.0 | 2014.120.5556.0 | 2014.120.5556 | ||
| 12.0.5553.0 | 12.0.5553 12.00.5553 12.00.5553.0 | 2014.120.5553.0 | 2014.120.5553 | ||
| 12.0.5546.0 | 12.0.5546 12.00.5546 12.00.5546.0 | 2014.120.5546.0 | 2014.120.5546 | ||
| 12.0.5540.0 | 12.0.5540 12.00.5540 12.00.5540.0 | 2014.120.5540.0 | 2014.120.5540 | ||
| 12.0.5537.0 | 12.0.5537 12.00.5537 12.00.5537.0 | 2014.120.5537.0 | 2014.120.5537 | ||
| 12.0.5522.0 | 12.0.5522 12.00.5522 12.00.5522.0 | 2014.120.5522.0 | 2014.120.5522 | ||
| 12.0.5511.0 | 12.0.5511 12.00.5511 12.00.5511.0 | 2014.120.5511.0 | 2014.120.5511 | ||
| 12.0.5223.6 | 12.0.5223 12.00.5223 12.00.5223.6 | 2014.120.5223.6 | 2014.120.5223 2014.120.5223.0 | ||
| 12.0.5214.6 | 12.0.5214 12.00.5214 12.00.5214.6 | 2014.120.5214.6 | 2014.120.5214 2014.120.5214.0 | ||
| 12.0.4522.0 | 12.0.4522 12.00.4522 12.00.4522.0 | 2014.120.4522.0 | 2014.120.4522 | ||
| 12.0.4511.0 | 12.0.4511 12.00.4511 12.00.4511.0 | 2014.120.4511.0 | 2014.120.4511 | ||
| 12.0.4502.0 | 12.0.4502 12.00.4502 12.00.4502.0 | 2014.120.4502.0 | 2014.120.4502 | ||
| 12.0.4491.0 | 12.0.4491 12.00.4491 12.00.4491.0 | 2014.120.4491.0 | 2014.120.4491 | ||
| 12.0.4474.0 | 12.0.4474 12.00.4474 12.00.4474.0 | 2014.120.4474.0 | 2014.120.4474 | ||
| 12.0.4468.0 | 12.0.4468 12.00.4468 12.00.4468.0 | 2014.120.4468.0 | 2014.120.4468 | ||
| 12.0.4459.0 | 12.0.4459 12.00.4459 12.00.4459.0 | 2014.120.4459.0 | 2014.120.4459 | ||
| 12.0.4457.0 | 12.0.4457 12.00.4457 12.00.4457.0 | 2014.120.4457.0 | 2014.120.4457 | ||
| 12.0.4449.0 | 12.0.4449 12.00.4449 12.00.4449.0 | 2014.120.4449.0 | 2014.120.4449 | ||
| 12.0.4439.1 | 12.0.4439 12.00.4439 12.00.4439.1 | 2014.120.4439.1 | 2014.120.4439 2014.120.4439.0 | ||
| 12.0.4436.0 | 12.0.4436 12.00.4436 12.00.4436.0 | 2014.120.4436.0 | 2014.120.4436 | ||
| 12.0.4427.24 | 12.0.4427 12.00.4427 12.00.4427.24 | 2014.120.4427.24 | 2014.120.4427 2014.120.4427.0 | ||
| 12.0.4422.0 | 12.0.4422 12.00.4422 12.00.4422.0 | 2014.120.4422.0 | 2014.120.4422 | ||
| 12.0.4419.0 | 12.0.4419 12.00.4419 12.00.4419.0 | 2014.120.4419.0 | 2014.120.4419 | ||
| 12.0.4416.0 | 12.0.4416 12.00.4416 12.00.4416.0 | 2014.120.4416.0 | 2014.120.4416 | ||
| 12.0.2569.0 | 12.0.2569 12.00.2569 12.00.2569.0 | 2014.120.2569.0 | 2014.120.2569 | ||
| 12.0.2568.0 | 12.0.2568 12.00.2568 12.00.2568.0 | 2014.120.2568.0 | 2014.120.2568 | ||
| 12.0.2564.0 | 12.0.2564 12.00.2564 12.00.2564.0 | 2014.120.2564.0 | 2014.120.2564 | ||
| 12.0.2560.0 | 12.0.2560 12.00.2560 12.00.2560.0 | 2014.120.2560.0 | 2014.120.2560 | ||
| 12.0.2556.4 | 12.0.2556 12.00.2556 12.00.2556.4 | 2014.120.2556.4 | 2014.120.2556 2014.120.2556.0 | ||
| 12.0.2553.0 | 12.0.2553 12.00.2553 12.00.2553.0 | 2014.120.2553.0 | 2014.120.2553 | ||
| 12.0.2546.0 | 12.0.2546 12.00.2546 12.00.2546.0 | 2014.120.2546.0 | 2014.120.2546 | ||
| 12.0.2495.0 | 12.0.2495 12.00.2495 12.00.2495.0 | 2014.120.2495.0 | 2014.120.2495 | ||
| 12.0.2480.0 | 12.0.2480 12.00.2480 12.00.2480.0 | 2014.120.2480.0 | 2014.120.2480 | ||
| 12.0.2456.0 | 12.0.2456 12.00.2456 12.00.2456.0 | 2014.120.2456.0 | 2014.120.2456 | ||
| 12.0.2430.0 | 12.0.2430 12.00.2430 12.00.2430.0 | 2014.120.2430.0 | 2014.120.2430 | ||
| 12.0.2402.0 | 12.0.2402 12.00.2402 12.00.2402.0 | 2014.120.2402.0 | 2014.120.2402 | ||
| 12.0.2381.0 | 12.0.2381 12.00.2381 12.00.2381.0 | 2014.120.2381.0 | 2014.120.2381 | ||
| 12.0.2370.0 | 12.0.2370 12.00.2370 12.00.2370.0 | 2014.120.2370.0 | 2014.120.2370 | ||
| 12.0.2342.0 | 12.0.2342 12.00.2342 12.00.2342.0 | 2014.120.2342.0 | 2014.120.2342 | ||
| 12.0.2254.0 | 12.0.2254 12.00.2254 12.00.2254.0 | 2014.120.2254.0 | 2014.120.2254 | ||
| 12.0.2000.8 | 12.0.2000 12.00.2000 12.00.2000.8 | 2014.120.2000.8 | 2014.120.2000 2014.120.2000.0 | ||
| 12.0.2000.8 | 12.0.2000 12.00.2000 12.00.2000.8 | 2014.120.2000.8 | 2014.120.2000 2014.120.2000.0 | ||
| 12.0.2000.8 | 12.0.2000 12.00.2000 12.00.2000.8 | 2014.120.2000.8 | 2014.120.2000 2014.120.2000.0 | ||
| 12.0.2000.8 | 12.0.2000 12.00.2000 12.00.2000.8 | 2014.120.2000.8 | 2014.120.2000 2014.120.2000.0 | ||
| 12.0.2000.8 | 12.0.2000 12.00.2000 12.00.2000.8 | 2014.120.2000.8 | 2014.120.2000 2014.120.2000.0 | ||
| 12.0.2000.8 | 12.0.2000 12.00.2000 12.00.2000.8 | 2014.120.2000.8 | 2014.120.2000 2014.120.2000.0 | ||
| 12.0.2000.8 | 12.0.2000 12.00.2000 12.00.2000.8 | 2014.120.2000.8 | 2014.120.2000 2014.120.2000.0 | ||
| 12.0.2000.8 | 12.0.2000 12.00.2000 12.00.2000.8 | 2014.120.2000.8 | 2014.120.2000 2014.120.2000.0 | ||
| 12.0.2000.8 | 12.0.2000 12.00.2000 12.00.2000.8 | 2014.120.2000.8 | 2014.120.2000 2014.120.2000.0 | ||
| 12.0.2000.8 | 12.0.2000 12.00.2000 12.00.2000.8 | 2014.120.2000.8 | 2014.120.2000 2014.120.2000.0 | ||
| 12.0.2000.8 | 12.0.2000 12.00.2000 12.00.2000.8 | 2014.120.2000.8 | 2014.120.2000 2014.120.2000.0 | SQL Server Reporting Services 2014 RTM | |
| 12.0.1736.0 | 12.0.1736 12.00.1736 12.00.1736.0 | 2014.120.1736.0 | 2014.120.1736 |
Reporting Services 2012 build numbers:
| Build | Alternative builds | File version | Alternative file version | KB / Description | Release date |
|---|---|---|---|---|---|
| 11.0.7507.2 | 11.0.7507 11.00.7507 11.00.7507.2 | 2011.110.7507.2 | 2011.110.7507 2011.110.7507.0 | ||
| 11.0.7493.4 | 11.0.7493 11.00.7493 11.00.7493.4 | 2011.110.7493.4 | 2011.110.7493 2011.110.7493.0 | ||
| 11.0.6607.3 | 11.0.6607 11.00.6607 11.00.6607.3 | 2011.110.6607.3 | 2011.110.6607 2011.110.6607.0 | ||
| 11.0.6598.0 | 11.0.6598 11.00.6598 11.00.6598.0 | 2011.110.6598.0 | 2011.110.6598 | ||
| 11.0.6594.0 | 11.0.6594 11.00.6594 11.00.6594.0 | 2011.110.6594.0 | 2011.110.6594 | ||
| 11.0.6579.0 | 11.0.6579 11.00.6579 11.00.6579.0 | 2011.110.6579.0 | 2011.110.6579 | ||
| 11.0.6567.0 | 11.0.6567 11.00.6567 11.00.6567.0 | 2011.110.6567.0 | 2011.110.6567 | ||
| 11.0.6544.0 | 11.0.6544 11.00.6544 11.00.6544.0 | 2011.110.6544.0 | 2011.110.6544 | ||
| 11.0.6540.0 | 11.0.6540 11.00.6540 11.00.6540.0 | 2011.110.6540.0 | 2011.110.6540 | ||
| 11.0.6537.0 | 11.0.6537 11.00.6537 11.00.6537.0 | 2011.110.6537.0 | 2011.110.6537 | ||
| 11.0.6523.0 | 11.0.6523 11.00.6523 11.00.6523.0 | 2011.110.6523.0 | 2011.110.6523 | ||
| 11.0.6518.0 | 11.0.6518 11.00.6518 11.00.6518.0 | 2011.110.6518.0 | 2011.110.6518 | ||
| 11.0.5678.0 | 11.0.5678 11.00.5678 11.00.5678.0 | 2011.110.5678.0 | 2011.110.5678 | ||
| 11.0.5657.0 | 11.0.5657 11.00.5657 11.00.5657.0 | 2011.110.5657.0 | 2011.110.5657 | ||
| 11.0.5655.0 | 11.0.5655 11.00.5655 11.00.5655.0 | 2011.110.5655.0 | 2011.110.5655 | ||
| 11.0.5649.0 | 11.0.5649 11.00.5649 11.00.5649.0 | 2011.110.5649.0 | 2011.110.5649 | ||
| 11.0.5646.0 | 11.0.5646 11.00.5646 11.00.5646.0 | 2011.110.5646.0 | 2011.110.5646 | ||
| 11.0.5644.2 | 11.0.5644 11.00.5644 11.00.5644.2 | 2011.110.5644.2 | 2011.110.5644 2011.110.5644.0 | ||
| 11.0.5641.0 | 11.0.5641 11.00.5641 11.00.5641.0 | 2011.110.5641.0 | 2011.110.5641 | ||
| 11.0.5634.1 | 11.0.5634 11.00.5634 11.00.5634.1 | 2011.110.5634.1 | 2011.110.5634 2011.110.5634.0 | ||
| 11.0.5623.0 | 11.0.5623 11.00.5623 11.00.5623.0 | 2011.110.5623.0 | 2011.110.5623 | ||
| 11.0.5592.0 | 11.0.5592 11.00.5592 11.00.5592.0 | 2011.110.5592.0 | 2011.110.5592 | ||
| 11.0.5582.0 | 11.0.5582 11.00.5582 11.00.5582.0 | 2011.110.5582.0 | 2011.110.5582 | ||
| 11.0.5569.0 | 11.0.5569 11.00.5569 11.00.5569.0 | 2011.110.5569.0 | 2011.110.5569 | ||
| 11.0.5556.0 | 11.0.5556 11.00.5556 11.00.5556.0 | 2011.110.5556.0 | 2011.110.5556 | ||
| 11.0.5548.0 | 11.0.5548 11.00.5548 11.00.5548.0 | 2011.110.5548.0 | 2011.110.5548 | ||
| 11.0.5532.0 | 11.0.5532 11.00.5532 11.00.5532.0 | 2011.110.5532.0 | 2011.110.5532 | ||
| 11.0.3492.0 | 11.0.3492 11.00.3492 11.00.3492.0 | 2011.110.3492.0 | 2011.110.3492 | ||
| 11.0.3487.0 | 11.0.3487 11.00.3487 11.00.3487.0 | 2011.110.3487.0 | 2011.110.3487 | ||
| 11.0.3486.0 | 11.0.3486 11.00.3486 11.00.3486.0 | 2011.110.3486.0 | 2011.110.3486 | ||
| 11.0.3482.0 | 11.0.3482 11.00.3482 11.00.3482.0 | 2011.110.3482.0 | 2011.110.3482 | ||
| 11.0.3470.0 | 11.0.3470 11.00.3470 11.00.3470.0 | 2011.110.3470.0 | 2011.110.3470 | ||
| 11.0.3470.0 | 11.0.3470 11.00.3470 11.00.3470.0 | 2011.110.3470.0 | 2011.110.3470 | ||
| 11.0.3460.0 | 11.0.3460 11.00.3460 11.00.3460.0 | 2011.110.3460.0 | 2011.110.3460 | ||
| 11.0.3449.0 | 11.0.3449 11.00.3449 11.00.3449.0 | 2011.110.3449.0 | 2011.110.3449 | ||
| 11.0.3431.0 | 11.0.3431 11.00.3431 11.00.3431.0 | 2011.110.3431.0 | 2011.110.3431 | ||
| 11.0.3412.0 | 11.0.3412 11.00.3412 11.00.3412.0 | 2011.110.3412.0 | 2011.110.3412 | ||
| 11.0.3401.0 | 11.0.3401 11.00.3401 11.00.3401.0 | 2011.110.3401.0 | 2011.110.3401 | ||
| 11.0.3393.0 | 11.0.3393 11.00.3393 11.00.3393.0 | 2011.110.3393.0 | 2011.110.3393 | ||
| 11.0.3381.0 | 11.0.3381 11.00.3381 11.00.3381.0 | 2011.110.3381.0 | 2011.110.3381 | ||
| 11.0.3368.0 | 11.0.3368 11.00.3368 11.00.3368.0 | 2011.110.3368.0 | 2011.110.3368 | ||
| 11.0.3153.0 | 11.0.3153 11.00.3153 11.00.3153.0 | 2011.110.3153.0 | 2011.110.3153 | ||
| 11.0.3128.0 | 11.0.3128 11.00.3128 11.00.3128.0 | 2011.110.3128.0 | 2011.110.3128 | ||
| 11.0.2832.9 | 11.0.2832 11.00.2832 11.00.2832.9 | 2011.110.2832.9 | 2011.110.2832 2011.110.2832.0 | ||
| 11.0.2832.4 | 11.0.2832 11.00.2832 11.00.2832.4 | 2011.110.2832.4 | 2011.110.2832 2011.110.2832.0 | ||
| 11.0.2832.25 | 11.0.2832 11.00.2832 11.00.2832.25 | 2011.110.2832.25 | 2011.110.2832 2011.110.2832.0 | ||
| 11.0.2832.12 | 11.0.2832 11.00.2832 11.00.2832.12 | 2011.110.2832.12 | 2011.110.2832 2011.110.2832.0 | ||
| 11.0.2830.77 | 11.0.2830 11.00.2830 11.00.2830.77 | 2011.110.2830.77 | 2011.110.2830 2011.110.2830.0 | ||
| 11.0.2830.57 | 11.0.2830 11.00.2830 11.00.2830.57 | 2011.110.2830.57 | 2011.110.2830 2011.110.2830.0 | ||
| 11.0.2830.47 | 11.0.2830 11.00.2830 11.00.2830.47 | 2011.110.2830.47 | 2011.110.2830 2011.110.2830.0 | ||
| 11.0.2830.38 | 11.0.2830 11.00.2830 11.00.2830.38 | 2011.110.2830.38 | 2011.110.2830 2011.110.2830.0 | ||
| 11.0.2830.24 | 11.0.2830 11.00.2830 11.00.2830.24 | 2011.110.2830.24 | 2011.110.2830 2011.110.2830.0 | ||
| 11.0.2814.8 | 11.0.2814 11.00.2814 11.00.2814.8 | 2011.110.2814.8 | 2011.110.2814 2011.110.2814.0 | ||
| 11.0.2814.2 | 11.0.2814 11.00.2814 11.00.2814.2 | 2011.110.2814.2 | 2011.110.2814 2011.110.2814.0 | ||
| 11.0.2809.92 | 11.0.2809 11.00.2809 11.00.2809.92 | 2011.110.2809.92 | 2011.110.2809 2011.110.2809.0 | ||
| 11.0.2424.0 | 11.0.2424 11.00.2424 11.00.2424.0 | 2011.110.2424.0 | 2011.110.2424 | ||
| 11.0.2420.0 | 11.0.2420 11.00.2420 11.00.2420.0 | 2011.110.2420.0 | 2011.110.2420 | ||
| 11.0.2419.0 | 11.0.2419 11.00.2419 11.00.2419.0 | 2011.110.2419.0 | 2011.110.2419 | ||
| 11.0.2376.0 | 11.0.2376 11.00.2376 11.00.2376.0 | 2011.110.2376.0 | 2011.110.2376 | ||
| 11.0.2218.0 | 11.0.2218 11.00.2218 11.00.2218.0 | 2011.110.2218.0 | 2011.110.2218 | ||
| 11.0.2100.60 | 11.0.2100 11.00.2100 11.00.2100.60 | 2011.110.2100.60 | 2011.110.2100 2011.110.2100.0 | SQL Server Reporting Services 2012 RTM |
You can comment here . If you know of a SSRS version that we don't have listed here, please use the comments.
I work on this site continuously and keep the information up to date. If it helps you, you can support me:
© 2007–2024 SqlServerBuilds.blogspot.com · Contact · Privacy policy
Other useful sites › SQL Server Versions List · Firebird Database Versions List · Exchange Server Versions List · SharePoint Servers Version List · Microsoft Knowledge Base Monitoring
This browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
September Security Patch 2020 - SQL Reporting services not running
We encountered issue for MBAM Server, after installing September Security Patch . SQL Reporting Services is in not running status
SQL Server Reporting Services A SQL Server technology that supports the creation, management, and delivery of both traditional, paper-oriented reports and interactive, web-based reports. 2,854 questions Sign in to follow
Windows 10 Security Windows 10: A Microsoft operating system that runs on personal computers and tablets. Security: The precautions taken to guard against crime, attack, sabotage, espionage, or another threat. 2,815 questions Sign in to follow
Windows Server Security Windows Server: A family of Microsoft server operating systems that support enterprise-level management, data storage, applications, and communications. Security: The precautions taken to guard against crime, attack, sabotage, espionage, or another threat. 1,772 questions Sign in to follow
I couldn't fully understand the meaning for "SQL Reporting Services is in not running status".
Have you tried to start the SQL Reporting Services?
Or you mean that you couldn't start the SQL Reporting Services?
If the answer is helpful, please click " Accept Answer " and upvote it.
Note: Please follow the steps in our documentation to enable e-mail notifications if you want to receive the related email notification for this thread.
May I know how's the issue going on now?
Thank you for the time, the client answered back and the services is now up and running
European Microsoft Fabric Community Conference
The ultimate Microsoft Fabric, Power BI, Azure AI, and SQL learning event: Join us in Stockholm, September 24-27, 2024. Save €200 with code MSCUST on top of early bird pricing!
- Power BI forums
- News & Announcements
- Get Help with Power BI
- Report Server
- Power Query
- Mobile Apps
- DAX Commands and Tips
- Custom Visuals Development Discussion
- Health and Life Sciences
- Power BI Spanish forums
- Translated Spanish Desktop
- Training and Consulting
- Instructor Led Training
- Dashboard in a Day for Women, by Women
- Community Connections & How-To Videos
- COVID-19 Data Stories Gallery
- Themes Gallery
- Data Stories Gallery
- R Script Showcase
- Webinars and Video Gallery
- Quick Measures Gallery
- 2021 MSBizAppsSummit Gallery
- 2020 MSBizAppsSummit Gallery
- 2019 MSBizAppsSummit Gallery
- Custom Visuals Ideas
- Upcoming Events
- Community Blog
- Power BI Community Blog
- Custom Visuals Community Blog
- Community Support
- Community Accounts & Registration
- Using the Community
- Community Feedback
Find everything you need to get certified on Fabric—skills challenges, live sessions, exam prep, role guidance, and more. Get started
May 2024 Power BI Report Server issue
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- All forum topics
- Previous Topic
- Mark as New
- Report Inappropriate Content
- pbirs may 2024 udpate
Helpful resources

Europe’s largest Microsoft Fabric Community Conference
Join the community in Stockholm for expert Microsoft Fabric learning including a very exciting keynote from Arun Ulag, Corporate Vice President, Azure Data.

Power BI Monthly Update - June 2024
Check out the June 2024 Power BI update to learn about new features.

Fabric Community Update - June 2024
Get the latest Fabric updates from Build 2024, key Skills Challenge voucher deadlines, top blogs, forum posts, and product ideas.
| User | Count |
|---|---|
| 8 | |
| 4 | |
| 1 | |
| 1 | |
| 1 |
| User | Count |
|---|---|
| 18 | |
| 11 | |
| 8 | |
| 8 | |
| 7 |


Get notified in your email when a new post is published to this blog
Let GitHub Copilot draft of your pull request description

Jessie Houghton
July 1st, 2024 2
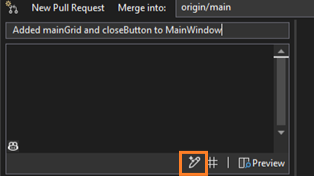
Writing good pull request descriptions is essential for effective code reviews and collaboration. But it’s time-consuming and tedious, especially when you have multiple commits or complex changes. That’s why we’re highlighting a feature that will make your life better with the help of GitHub Copilot: generated pull request descriptions. GitHub Copilot examines your code changes and generates helpful summaries that you can edit and customize. Save your energy for your coding tasks and let GitHub Copilot provide extra context for your reviewers.
Download Visual Studio
Starting with Visual Studio version 17.10 GA, to try these out, you’ll need to have an active GitHub Copilot subscription and the GitHub Copilot component installed and the Git Preview Features enabled in the GitHub Copilot Menu.
Get going faster with generated pull request descriptions
One of the most popular features of GitHub Copilot is the ability to generate Git commit messages based on your code changes. We’ve heard awesome feedback on this feature, so we wanted to continue saving you time and improve your collaborations by enabling GitHub Copilot-powered pull request descriptions. You can now generate a first draft for your pull request and preview the markdown output. You’ll get assistance in providing important context to your colleagues for their reviews and get the added benefit of ensuring you include the right changes in your pull request.
Select “Add AI Generated Pull Request Description” sparkle pen icon within the Create a Pull Request window to see your description.
Help us go further
So far, we’ve heard customers are satisfied with their generated results, sharing that responses are accurate and useful , and inserting suggestions at a rate of 80%! Please share your ideas to improve this future and further power up Version Control with GitHub Copilot.
Take the Survey
We appreciate the time you’ve spent reporting issues/suggestions and hope you continue to give us feedback when using Visual Studio on what you like and what we can improve. Your feedback is critical to help us make Visual Studio the best tool it can be! You can share feedback with us via Developer Community : report any bugs or issues via report a problem and share your suggestions for new features or improvements to existing ones.
Stay connected with the Visual Studio team by following us on YouTube , Twitter , LinkedIn , Twitch and on Microsoft Learn .

Jessie Houghton Program Manager, Version Control Team


On-premises reporting with Power BI Report Server

Dynamics 365 Business Central
On-premises reporting, on-premises reporting today.

Cloud-ready for tomorrow

Create, publish, distribute Power BI reports

Create reports

Publish to Power BI Report Server

Distribute and consume across devices

Plans to suit every need

Get started and learn more

Free trial download

Documentation

Contact Sales

Follow Power Platform
- Chat with sales
Available M-F 6 AM to 3 PM PT.

IMAGES
VIDEO
COMMENTS
IMPORTANT Windows 8.1 and Windows Server 2012 R2 have reached the end of mainstream support and are now in extended support. Starting in July 2020, there will no longer be optional, non-security releases (known as "C" releases) for this operating system. Operating systems in extended support have only cumulative monthly security updates (known as the "B" or Update Tuesday release).
Windows. Windows Server, version 2004 (Server Core installation) 4571756. Security Update. Windows10.-KB4571756-x64.msu. 4566782. Yes. Yes. Provides deployment information for the September 2020 Microsoft security release.
A remote code execution vulnerability exists in Microsoft SQL Server Reporting Services when it incorrectly handles page requests. See CVE-2020-0618 for details. Resolution. To fix this issue in the products that are listed in "Applies to," install the following security update, as appropriate:
Oct 11, 2020, 6:47 PM. We encountered issue for MBAM Server, after installing September Security Patch . SQL Reporting Services is in not running status. SQL Server Reporting Services.
SQL Server 2022 Reporting Services. This release introduces the new SQL Server 2022 (16.x) Reporting Services (SSRS). We continue to innovate, create, and design in a way that gives everyone the ability to achieve more. Designing for inclusivity reflects how people adapt to the world around them. In this new release of SSRS, we've done a lot of ...
Uninstall SQL Server Reporting Services. In a scale-out deployment, repeat for all nodes in the scale-out. For more information, see Uninstall Native Mode. Restore backups of ReportServer database. For more information, see Backup and Restore Operations for Reporting Services. Reinstall the prior update of SQL Server Reporting Services.
Fixed issue where some SQL Server 2022 product keys weren't working with SQL Server 2022 Reporting Services. 16..8353.8096, 2022/11/16 (Product Version: 16..1112.48) Initial release. Major changes from SQL Server 2019 Reporting Services: New portal experience with performance improvements using Angular; Accessibility fixes to many parts of ...
Microsoft SQL Server 2019 Reporting Services. SQL Server Reporting Services is a server-based reporting platform that provides comprehensive reporting functionality. Important! Selecting a language below will dynamically change the complete page content to that language. Download.
Refreshed Portal. In addition to the above updates, the SSRS portal was improved to provide a more inclusive modern graphical interface making it easier to deliver meaningful reporting on your data from a web-based experience. In the portal, you can view reports, KPIs, and navigate through the elements in your report server instance.
Select Install Reporting Services. Choose an edition to install and then select Next. For a free edition, choose either Evaluation or Developer from the drop-down. Otherwise, enter a product key. Find the product key for SQL Server Reporting Services. Read and agree to the license terms and conditions and then select Next.
The September 2020 security release consists of security updates for the following software: Microsoft Windows Microsoft Edge (EdgeHTML-based) Microsoft Edge (Chromium-based) Microsoft ChakraCore Internet Explorer SQL Server Microsoft JET Database Engine Microsoft Office and Microsoft Office Services and Web Apps Microsoft Dynamics Visual ...
This article summarizes various options that can be taken to modernize SQL Server Reporting Services (SSRS) and then provides a detailed step-by-step guide to bringing report server databases to Azure SQL Managed Instance.. Different Options for Modernization. If you run SQL Server Reporting Services for Business Intelligence capabilities on-premises, you may want to draw benefits by ...
Size. Download. Security Update for SQL Server 2014 Service Pack 3 GDR (KB4532095) Microsoft SQL Server 2014. Security Updates. 2/11/2020. n/a. 1049.6 MB. 1100564704.
SQL Server: CVE-2020-1044: SQL Server Reporting Services Security Feature Bypass Vulnerability: Moderate: Visual Studio: CVE-2020-16874: Visual Studio Remote Code Execution Vulnerability: Critical ...
To find the edition of your SQL Server instance, you can use one of the procedures in Method 2 through Method 5 in the Determine which version and edition of SQL Server Database Engine is running section. The version information and edition information are in the same output string. For information about SQL Server Support lifecycle, see SQL ...
Microsoft SQL Server Reporting Services Update for September 2020 Severity Serious 3 Qualys ID 91673 Vendor Reference CVE-2020-1044 CVE Reference ... Microsoft releases the security update for Microsoft Edge September 2020. The KB Articles associated with the update: KB4577032 KB4570333 KB4574727 KB4577041 KB4571756 KB4577049
The Microsoft SQL Server Reporting Services installation on the remote host is missing a security update. It is, therefore, affected by a security feature bypass vulnerability in SQL Server Reporting Services (SSRS) due to improper validation of uploaded attachments to reports.
So, in order to update SSRS 2017 or later, you just need to download the latest SSRS installer from Microsoft, and run the installation process on the SSRS server to be updated. Then, after running the installer, you will be asked whether you want to proceed with updating the existing SSRS installation or not.
Microsoft SQL Server Reporting Services (SSRS or S.S.R.S. or RS) is a native server-based reporting platform for creating reports from relational or multidimensional data sources.. A widely used and dynamic tool it provides a comprehensive, server-based reporting solution that allows the authoring, manageability, and delivery of reports in multiple ways and formats, such as on the Web or via e ...
The Microsoft SQL Server Reporting Services installation on the remote host is missing a security update. It is, therefore, affected by a security feature bypass vulnerability in SQL Server Reporting Services (SSRS) due to improper validation of uploaded attachments to reports. An authenticated, remote attacker could exploit this issue to ...
The September 2020 security release consists of security updates for the following software: Microsoft Windows. Microsoft Edge (EdgeHTML-based) Microsoft Edge (Chromium-based) Microsoft ChakraCore. Internet Explorer. SQL Server. Microsoft JET Database Engine. Microsoft Office and Microsoft Office Services and Web Apps.
Windows Server: A family of Microsoft server operating systems that support enterprise-level management, data storage, applications, and communications. Security: The precautions taken to guard against crime, attack, sabotage, espionage, or another threat. The precautions taken to guard against crime, attack, sabotage, espionage, or another threat.
Security Updates for Microsoft SQL Server Reporting Services (September 2020) medium Nessus Plugin ID 140534. Language: English. Information. Dependencies. Dependents. Changelog. sql_server_reporting_services_installed.nbin.
The ultimate Microsoft Fabric, Power BI, Azure AI, and SQL learning event: Join us in Stockholm, September 24-27, 2024. ... After applying this update I wasn't able to run any reports. They all generated, "Exception of type 'Microsoft.Reporting.Services.ReportProcessing.ReportProcessingException' was thrown. (rsProcessingError).
We appreciate the time you've spent reporting issues/suggestions and hope you continue to give us feedback when using Visual Studio on what you like and what we can improve. Your feedback is critical to help us make Visual Studio the best tool it can be!
Power BI Report Server is the on-premises solution for reporting today, with the flexibility to move to the cloud tomorrow. It's included with Power BI Premium so you have the ability to move to the cloud on your terms. Provide access to rich, interactive reports, and the enterprise reporting ...